The largest traffic distribution system (TDS) known as EITest was just taken down by security researchers from Abuse.ch, BrilliantIT, and Proofpoint. The expert group sinkholed the command and control infrastructure behind the network of hacked servers that had been used to deliver malware through redirects, exploit kits and tech support scams.
The traffic distribution system was previously analyzed by an anonymous author on Malware Don’t Need Coffee:
EITest is one of the longest malicious delivery campaigns that has continued to evolve. In the spring of 2017, it started redirecting Internet Explorer users to tech support scams in addition to the existing redirections with the fake Chrome fonts.
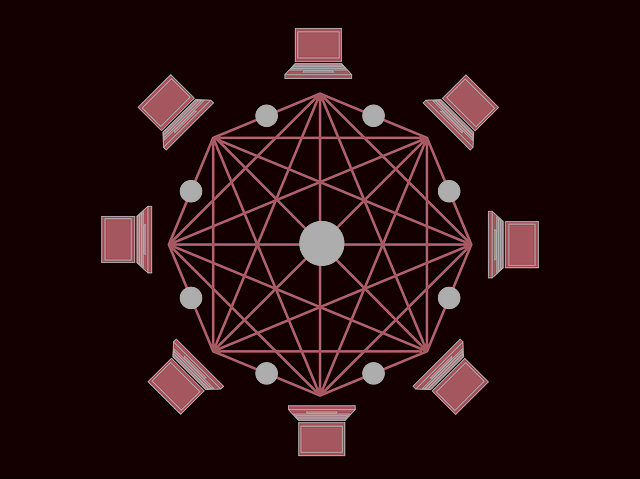
EITest Traffic Distribution System Described
EITest was first detected several years ago, in 2011. However, it became a traffic distribution system available for rent in July 2014. Back then, the TDS was deployed in malicious campaigns distributing the Zaccess Trojan. The attackers were using an exploit kit known as Glazunov.
According to Proofpoint researchers, “EITest is likely one of the oldest of its kind and has been involved in the delivery of a variety of ransomware, information stealers, and other malware, with clear evidence of its use dating back to 2011”.
From the moment EITest could be rented, security researchers have been struggling to cease its operations. Analysis indicates that the EITest team was selling hijacked traffic obtained from hacked sites for $20 USD per a thousand users. Traffic blocks of a minimum of 50,000 users were being sold on a daily basis.
EITest was used in the distribution of a variety of malware and ransomware families. It has been redirecting large amounts of traffic towards the in-famous Angler and RIG exploit kits. The more recent operations involved malicious sites deployed for social engineering like browser lockers, tech supports scams, fake updates and what not.
EITest Operation Sinkholed
Fortunately, Proofpoint together with BrilliantIT and Abuse.ch, successfully sinkholed EITest. Currently, the traffic distribution system’s infection chain is inefficient and thus, nearly two million malicious redirects a day have been prevented from happening.
The researchers succeeded by seizing one particular domain (stat-dns.com) which led to the seizing of the whole operation. More specifically, that server has been pointing to a sinkhole since March 15, 2018:
We analyzed data from the sinkhole operation from March 15 to April 4, 2018. During that period, the sinkhole received almost 44 million requests from roughly 52,000 servers. Decoding the requests we were able to obtain a list of compromised domains as well as IP addresses and user agents of the users who had browsed to the compromised servers.
Of all the compromised websites, Proofpoint researchers observed multiple content management systems, but the vast majority appeared to be using WordPress. We recently wrote about another fake update campaign that was leveraging WordPress and other CMS-based sites to deliver the Chtonic banking malware, a variant of ZeusVM as well as NetSupport RAT.
Since EITest was sinkholed, no attempts of restoring its activities have been observed.
Proofpoint researchers have been following another traffic distribution system as well. Dubbed BlackTDS, the TDS is deployed in the distribution of various pieces of malware. Security researchers have been observing BlackTDS infection chains in the wild, delivering malware through social engineering tricks and fake software updates.
What is worth mentioning is that even though the identification of BlackTDS sites was not that hard for the researchers, associating the traffic with known threat actors was quite challenging or even difficult.


