Forthcoming versions of the Google Chrome browser will block the installation of extensions outside of the Chrome Web Store. This was announced by the company in an official blog post yesterday. The step is being made in order to protect users from malicious strains that are found on counterfeit download sites.
Google Chrome Will Counter Third Party Extension Installations
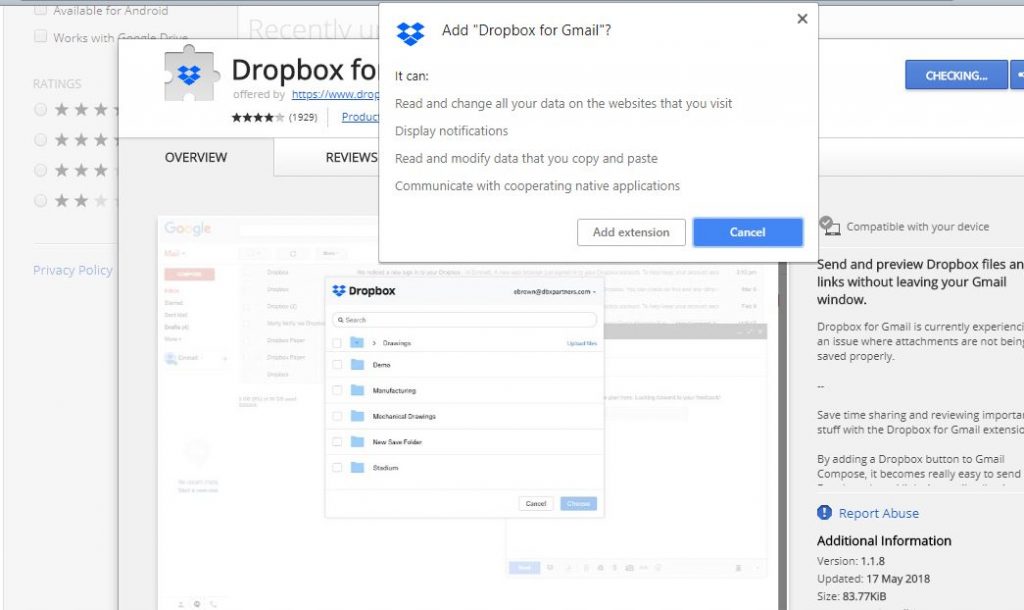
To this date extension installations for the Google Chrome web browser were allowed both through the associated Chrome Web Store which served as the official repository and other third-party sites as well. Ever since they have been devised by the developers computer criminals have used them as payload delivery methods for spreading all kinds of virus threats.
The blog post that carries the announcement reads that by the end of the year users will be able to install plugins only from Google’s official repository. The developers are planning to do this as a transitional change by following a devised plan in three steps:
- Newly published extensions will no longer feature an inline installation option. This means that upon interaction the users will be redirected to the associated Chrome Web Store entry in a new tab. There they will be able to complete the installation.
- From September 2018 onwards the inline installations will be disabled for all existing extensions. All of them will redirect to the Chrome Web Store.
- In December 2018 the inline installation API will be completely removed in the planned version of the browser. It will carry the identifier Google Chrome version 71.
Extension developers are advised to update their web sites with the relevant links. It is also suggested that the developers create a high quality store listing so that they can continue attracting users to them.
What Are The Dangers of Third-Party Google Chrome Extension Installations
The primary reason for taking these measures is to protect users from browser hijackers that are often distributed using such extensions. If the security analysts detect that a certain entry in the Chrome Web Store is malicious they can alert Google to take it down. Third-party sites that feature extensions cannot be taken down as they are usually hosted by the hacker operators themselves.
Most malicious extensions follow a typical behaviour pattern that can execute the following commands:
- Manipulation of Default Settings — The hacker-created extensions can manipulate the default home page, search engine and new tabs page to redirect the victims to a hacker-controlled page.
- Data Hijacking — They can include malicious engines that can retrieve sensitive information about the victims. They can be used to expose the victim’s identity.
- Additional Malware Delivery — The dangerous extensions can be used to deploy additional threats to the compromised computers.
- Trojan Code — Advanced strains of browser hijackers can include a hybrid Trojan engine that can report the infections to a hacker-controlled server. It can be used to spy on the victims or overtake control of their machines.
This step cannot effectively eliminated browser hijackers. It is expected that the hacker operators behind them will shift tactics and focus on another delivery strategy.




Google wants total control over user ! Time to ditch Chrome ! Google is nr.1 www spy and no one seems to see it !