In today’s interconnected society, the specter of cybersecurity threats looms larger than ever, with ransomware emerging as one of the most formidable challenges. LockBit 3.0, also known as LockBit Black, is at the forefront of this digital onslaught, exploiting weaknesses with a sophistication that alarms even seasoned experts.
This article dives deep into the workings of LockBit 3.0, shedding light on its infiltration methods, the complexity of its attacks, and the viable steps you can take to defend against this pervasive menace. Equipped with insights and actionable strategies, you’ll gain the knowledge needed to fortify your digital defenses and safeguard your valuable data against the ever-present threat of ransomware.

Lockbit 3.0 Virus Details
| Name | LockBit virus. |
| Type | Ransomware, Cryptovirus |
| Ransom Demanding Note | ooxlOmJxX.README.txt |
| Removal Time | 5 Minutes |
| Detection Tool |
Check if your Mac has been affected by LockBit 3.0
Download
Malware Removal Tool
|
Understanding LockBit 3.0 Ransomware: What You Need to Know
In recent years, the digital world has been plagued by a variety of cybersecurity threats, among which ransomware stands out as particularly vicious. LockBit 3.0, also known as LockBit Black, represents the latest evolution in a series of malware that has been terrorizing organizations worldwide since 2019. This advanced ransomware variant not only encrypts files but also uses unique methods to evade detection and ensure its persistence on infected systems.
Why is LockBit 3.0 Considered a Threatening Malware?
LockBit 3.0 has gained infamy in the cybersecurity community for several reasons. First, its adoption of the Ransomware as a Service (RaaS) model allows it to spread its reach far and wide. By leveraging this model, the creators of LockBit 3.0 can enlist affiliates to distribute the malware, thereby increasing the number of infections.
Furthermore, LockBit 3.0 exhibits advanced capabilities such as disabling REMOVED and deleting Volume Shadow Copy Service, making recovery efforts more challenging for victims. Its method of operation, which includes targeting and encrypting critical infrastructure and organizational data, underscores the high level of threat it poses.
Another aspect that amplifies the threat level of LockBit 3.0 is its continuous development. Since its inception, LockBit has evolved to incorporate more sophisticated infection and evasion techniques.
This adaptability ensures that the ransomware stays one step ahead of cybersecurity defenses, complicating the efforts of researchers and security professionals to provide protective measures against it.
Decoding the LockBit 3.0 Attack Process
The LockBit 3.0 ransomware carries out its attack through a well-structured process:
- Initial Access: LockBit 3.0 typically gains entry into a system through exposed RDP ports or by exploiting unpatched server vulnerabilities. This initial foothold is crucial for the next stages of the attack.
- Execution: Once inside, the ransomware decrypts its source code using a unique access token before executing on the victim’s machine. This step is designed to evade basic detection mechanisms that might identify and block malicious activities.
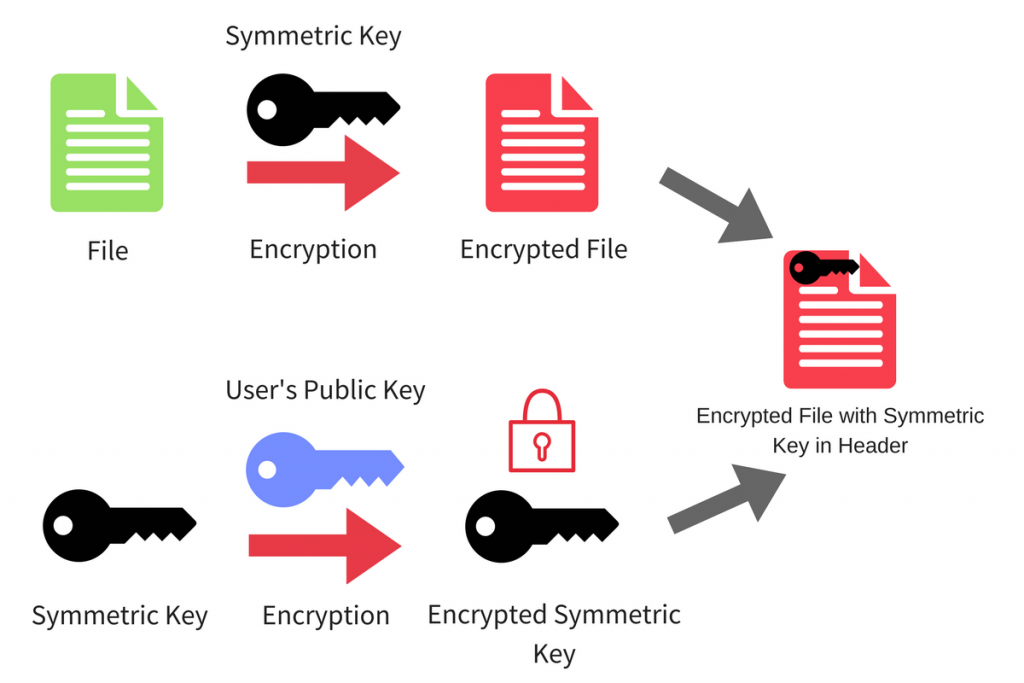
- File Encryption: LockBit 3.0 then identifies and encrypts files across the system, appending them with a random string as an extension. This marks the files as inaccessible without the corresponding decryption key.
- Ransom Note: A ransom note is dropped in multiple locations, informing the victim of the encryption and the demands of the attackers. Instructions for payment are typically included to facilitate the transaction.
- Disabling Defenses: To ensure its activities go uninterrupted, LockBit 3.0 disables key system defenses, Event Log services, and Volume Shadow Copy, which are often used in data recovery attempts.
The ransom note of the virus has the following message directed towards victims:
~~~ LockBit 3.0 the world’s fastest and most stable ransomware from 2019~~~
>>>>> Your data is stolen and encrypted.
If you don’t pay the ransom, the data will be published on our TOR darknet sites. Keep in mind that once your data appears on our leak site, it could be bought by your competitors at any second, so don’t hesitate for a long time. The sooner you pay the ransom, the sooner your company will be safe.Tor Browser Links:
http://lockbitapt2d73krlbewgv27tquljgxr33xbwwsp6rkyieto7u4ncead.onion
http://lockbitapt2yfbt7lchxejug47kmqvqqxvvjpqkmevv4l3azl3gy6pyd.onion
http://lockbitapt34kvrip6xojylohhxrwsvpzdffgs5z4pbbsywnzsbdguqd.onion
http://lockbitapt5x4zkjbcqmz6frdhecqqgadevyiwqxukksspnlidyvd7qd.onion
http://lockbitapt6vx57t3eeqjofwgcglmutr3a35nygvokja5uuccip4ykyd.onion
http://lockbitapt72iw55njgnqpymggskg5yp75ry7rirtdg4m7i42artsbqd.onion
http://lockbitaptawjl6udhpd323uehekiyatj6ftcxmkwe5sezs4fqgpjpid.onion
http://lockbitaptbdiajqtplcrigzgdjprwugkkut63nbvy2d5r4w2agyekqd.onion
http://lockbitaptc2iq4atewz2ise62q63wfktyrl4qtwuk5qax262kgtzjqd.onionLinks for normal browser:
http://lockbitapt2d73krlbewgv27tquljgxr33xbwwsp6rkyieto7u4ncead.onion.ly
http://lockbitapt2yfbt7lchxejug47kmqvqqxvvjpqkmevv4l3azl3gy6pyd.onion.ly
http://lockbitapt34kvrip6xojylohhxrwsvpzdffgs5z4pbbsywnzsbdguqd.onion.ly
http://lockbitapt5x4zkjbcqmz6frdhecqqgadevyiwqxukksspnlidyvd7qd.onion.ly
http://lockbitapt6vx57t3eeqjofwgcglmutr3a35nygvokja5uuccip4ykyd.onion.ly
http://lockbitapt72iw55njgnqpymggskg5yp75ry7rirtdg4m7i42artsbqd.onion.ly
http://lockbitaptawjl6udhpd323uehekiyatj6ftcxmkwe5sezs4fqgpjpid.onion.ly
http://lockbitaptbdiajqtplcrigzgdjprwugkkut63nbvy2d5r4w2agyekqd.onion.ly
http://lockbitaptc2iq4atewz2ise62q63wfktyrl4qtwuk5qax262kgtzjqd.onion.ly>>>>> What guarantee is there that we won’t cheat you?
We are the oldest ransomware affiliate program on the planet, nothing is more important than our reputation. We are not a politically motivated group and we want nothing more than money. If you pay, we will provide you with decryption software and destroy the stolen data. After you pay the ransom, you will quickly make even more money. Treat this situation simply as a paid training for your system administrators, because it is due to your corporate network not being properly configured that we were able to attack you. Our pentest services should be paid just like you pay the salaries of your system administrators. Get over it and pay for it. If we don’t give you a decryptor or delete your data after you pay, no one will pay us in the future. You can get more information about us on Ilon Musk’s Twitter https://twitter.com/hashtag/lockbit?f=live>>>>> You need to contact us and decrypt one file for free on TOR darknet sites with your personal ID
Download and install Tor Browser https://www.torproject.org/
Write to the chat room and wait for an answer, we’ll guarantee a response from you. If you need a unique ID for correspondence with us that no one will know about, tell it in the chat, we will generate a secret chat for you and give you his ID via private one-time memos service, no one can find out this ID but you. Sometimes you will have to wait some time for our reply, this is because we have a lot of work and we attack hundreds of companies around the world.Tor Browser personal link available only to you (available during a ddos attack):
http://lockbitsupuhswh4izvoucoxsbnotkmgq6durg7kficg6u33zfvq3oyd.onionTor Browser Links for chat (sometimes unavailable due to ddos attacks):
http://lockbitsupa7e3b4pkn4mgkgojrl5iqgx24clbzc4xm7i6jeetsia3qd.onion
http://lockbitsupdwon76nzykzblcplixwts4n4zoecugz2bxabtapqvmzqqd.onion
http://lockbitsupn2h6be2cnqpvncyhj4rgmnwn44633hnzzmtxdvjoqlp7yd.onion
http://lockbitsupo7vv5vcl3jxpsdviopwvasljqcstym6efhh6oze7c6xjad.onion
http://lockbitsupq3g62dni2f36snrdb4n5qzqvovbtkt5xffw3draxk6gwqd.onion
http://lockbitsupqfyacidr6upt6nhhyipujvaablubuevxj6xy3frthvr3yd.onion
http://lockbitsupt7nr3fa6e7xyb73lk6bw6rcneqhoyblniiabj4uwvzapqd.onion
http://lockbitsupuhswh4izvoucoxsbnotkmgq6durg7kficg6u33zfvq3oyd.onion
http://lockbitsupxcjntihbmat4rrh7ktowips2qzywh6zer5r3xafhviyhqd.onion>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>
>>>>> Your personal ID: B51C595D54036891C97A343D13B59749 <<<<< >>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>> Warning! Do not delete or modify encrypted files, it will lead to problems with decryption of files!
>>>>> Don’t go to the police or the FBI for help and don’t tell anyone that we attacked you.
They won’t help and will only make things worse for you. In 3 years not a single member of our group has been caught by the police, we are top notch hackers and we never leave a trail of crime. The police will try to prohibit you from paying the ransom in any way. The first thing they will tell you is that there is no guarantee to decrypt your files and remove stolen files, this is not true, we can do a test decryption before paying and your data will be guaranteed to be removed because it is a matter of our reputation, we make hundreds of millions of dollars and are not going to lose our revenue because of your files. It is very beneficial for the police and FBI to let everyone on the planet know about your data leak because then your state will get the fines budgeted for you due to GDPR and other similar laws. The fines will be used to fund the police and the FBI, they will eat more sweet coffee donuts and get fatter and fatter. The police and the FBI don’t care what losses you suffer as a result of our attack, and we will help you get rid of all your problems for a modest sum of money. Along with this you should know that it is not necessarily your company that has to pay the ransom and not necessarily from your bank account, it can be done by an unidentified person, such as any philanthropist who loves your company, for example, Elon Musk, so the police will not do anything to you if someone pays the ransom for you. If you’re worried that someone will trace your bank transfers, you can easily buy cryptocurrency for cash, thus leaving no digital trail that someone from your company paid our ransom. The police and FBI will not be able to stop lawsuits from your customers for leaking personal and private information. The police and FBI will not protect you from repeated attacks. Paying the ransom to us is much cheaper and more profitable than paying fines and legal fees.>>>>> What are the dangers of leaking your company’s data.
First of all, you will receive fines from the government such as the GDRP and many others, you can be sued by customers of your firm for leaking information that was confidential. Your leaked data will be used by all the hackers on the planet for various unpleasant things. For example, social engineering, your employees’ personal data can be used to re-infiltrate your company. Bank details and passports can be used to create bank accounts and online wallets through which criminal money will be laundered. On another vacation trip, you will have to explain to the FBI where you got millions of dollars worth of stolen cryptocurrency transferred through your accounts on cryptocurrency exchanges. Your personal information could be used to make loans or buy appliances. You would later have to prove in court that it wasn’t you who took out the loan and pay off someone else’s loan. Your competitors may use the stolen information to steal technology or to improve their processes, your working methods, suppliers, investors, sponsors, employees, it will all be in the public domain. You won’t be happy if your competitors lure your employees to other firms offering better wages, will you? Your competitors will use your information against you. For example, look for tax violations in the financial documents or any other violations, so you have to close your firm. According to statistics, two thirds of small and medium-sized companies close within half a year after a data breach. You will have to find and fix the vulnerabilities in your network, work with the customers affected by data leaks. All of these are very costly procedures that can exceed the cost of a ransomware buyout by a factor of hundreds. It’s much easier, cheaper and faster to pay us the ransom. Well and most importantly, you will suffer a reputational loss, you have been building your company for many years, and now your reputation will be destroyed.Read more about the GDRP legislation::
https://en.wikipedia.org/wiki/General_Data_Protection_Regulation
https://gdpr.eu/what-is-gdpr/
https://gdpr-info.eu/>>>>> Don’t go to recovery companies, they are essentially just middlemen who will make money off you and cheat you.
We are well aware of cases where recovery companies tell you that the ransom price is 5 million dollars, but in fact they secretly negotiate with us for 1 million dollars, so they earn 4 million dollars from you. If you approached us directly without intermediaries you would pay 5 times less, that is 1 million dollars.>>>> Very important! For those who have cyber insurance against ransomware attacks.
Insurance companies require you to keep your insurance information secret, this is to never pay the maximum amount specified in the contract or to pay nothing at all, disrupting negotiations. The insurance company will try to derail negotiations in any way they can so that they can later argue that you will be denied coverage because your insurance does not cover the ransom amount. For example your company is insured for 10 million dollars, while negotiating with your insurance agent about the ransom he will offer us the lowest possible amount, for example 100 thousand dollars, we will refuse the paltry amount and ask for example the amount of 15 million dollars, the insurance agent will never offer us the top threshold of your insurance of 10 million dollars. He will do anything to derail negotiations and refuse to pay us out completely and leave you alone with your problem. If you told us anonymously that your company was insured for $10 million and other important details regarding insurance coverage, we would not demand more than $10 million in correspondence with the insurance agent. That way you would have avoided a leak and decrypted your information. But since the sneaky insurance agent purposely negotiates so as not to pay for the insurance claim, only the insurance company wins in this situation. To avoid all this and get the money on the insurance, be sure to inform us anonymously about the availability and terms of insurance coverage, it benefits both you and us, but it does not benefit the insurance company. Poor multimillionaire insurers will not starve and will not become poorer from the payment of the maximum amount specified in the contract, because everyone knows that the contract is more expensive than money, so let them fulfill the conditions prescribed in your insurance contract, thanks to our interaction.>>>>> If you do not pay the ransom, we will attack your company again in the future.
This process not only demonstrates the sophistication of LockBit 3.0 but also highlights the importance of proactive and comprehensive cybersecurity measures.
To defend against such threats, it is crucial to maintain updated and robust security solutions. In this context, SpyHunter, with its advanced malware detection and removal capabilities, represents a strategic defense tool capable of identifying and mitigating threats like LockBit 3.0.
Understanding the operation and impact of LockBit 3.0 is the first step in enhancing our defenses against this formidable threat. By staying informed and prepared, organizations can better protect themselves from the devastating effects of ransomware attacks.
How Do Systems Get Infected with LockBit 3.0?
The infiltration of LockBit 3.0 into systems can occur through various means, many of which exploit simple human errors or system vulnerabilities.
Understanding these methods is crucial for prevention. This Ransomware, notorious for its stealth and efficiency, can lock and steal data, causing significant damage to individuals and organizations alike.
Common Methods Hackers Use to Deploy LockBit 3.0
The methods employed by hackers to distribute LockBit 3.0 are diverse, each taking advantage of different weak points within a system or its users. The most common methods include:
- Email Phishing: Using deceitful emails that persuade users to click on malicious links or download infected attachments.
- Pirate Software: Distributing the ransomware through illegal software downloads, cracks, or keygens.
- Exploiting Vulnerabilities: Taking advantage of outdated software or unpatched systems to forcefully gain entry.
- Remote Desktop Protocol (RDP) Exploits: Accessing systems through weak or stolen RDP credentials to inject malicious software.
Prevention involves a combination of vigilance, proper system maintenance, and the use of trusted security solutions like SpyHunter, which can detect and remove threats such as LockBit 3.0.
The Role of Email Phishing in Spreading LockBit 3.0
Email phishing is a prevalent method used by cybercriminals to spread LockBit 3.0. It tricks the recipient into opening a harmful link or downloading an attachment that contains the ransomware.
These emails often mimic legitimate communications from well-known companies or contacts, making them harder to suspect. Highlighting the dangers and signs of phishing emails is essential for educating users on how to avoid falling victim to such scams.
Key tips for identifying and avoiding phishing attempts include:
- Checking the sender’s email address for legitimacy.
- Looking for misspellings or grammatical errors in the body of the email.
- Avoiding downloading attachments from unknown or unsolicited emails.
- Not clicking on links in emails that request sensitive information or seem suspicious.
Employing a secure email service that filters out potentially dangerous emails can further reduce the risk of infection. Ultimately, staying informed about the tactics used by cybercriminals and relying on comprehensive security solutions like SpyHunter can offer strong protection against threats such as LockBit 3.0.
Step-by-Step Guide to Removing LockBit 3.0 Ransomware
Dealing with a ransomware infection like LockBit 3.0 can be stressful, but following a structured approach can help you manage the situation more effectively. This guide outlines a step-by-step process to identify and eliminate this threat from your device.
Initial Safety Measures: Disconnecting from the Network
The first crucial step in dealing with a ransomware attack is to isolate your infected device by disconnecting it from the internet. This prevents the ransomware from transmitting any further data to the attacker’s server, safeguarding your personal information from additional compromise.
Turn off your Wi-Fi and unplug any Ethernet cables. If you’re dealing with a network of computers, ensure each potentially affected device is also isolated to prevent the spread of the infection.
Utilize SpyHunter to Detect and Remove LockBit 3.0 Malicious Files
After isolating your device, employing a reliable malware removal tool like SpyHunter is essential in detecting and removing LockBit 3.0 ransomware components.
SpyHunter’s effectiveness in identifying nefarious files and its user-friendly interface makes it a suitable choice for users of various proficiency levels. Upon download, conduct a full system scan. SpyHunter will meticulously search for and eliminate LockBit 3.0 files, effectively disrupting the malware’s hold on your system.
Manual Removal vs. Professional Tools: What’s More Effective?
While manual removal of ransomware might seem like a cost-saving measure, it’s a complex process requiring specific technical skills.
Attempting to manually delete malicious files can result in accidental loss of crucial system files, leading to further system instability.
Professional malware removal tools, such as SpyHunter, offer a more practical solution.
They are explicitly designed to identify and neutralize threats with precision, significantly reducing the risk of collateral damage to your system files. These tools are constantly updated to tackle the latest ransomware variants, ensuring your device remains safeguarded against new threats.
In conclusion, the safety and security of your digital life are paramount. By following these guided steps and utilizing professional tools like SpyHunter for malware detection and removal, you can effectively mitigate the risks posed by ransomware attacks.
Remember, proactive measures and timely action can make all the difference in protecting your data and devices from harm.
Decrypting Your Files: Is It Possible After a LockBit 3.0 Attack?
Victims of the LockBit 3.0 ransomware attack often find themselves facing a difficult predicament: how to recover their encrypted files. The encryption used by this ransomware is particularly strong, requiring a unique key that only the attackers possess.
Despite this, there are a few avenues to explore for file recovery. Firstly, look for any official decryption tools available.
Organizations like Europol and the FBI occasionally release decryptors for certain ransomware strains. It’s vital to verify the source of any decryption tool to avoid further harm.
Additionally, it’s worth consulting a professional who specializes in data recovery. Though they might not guarantee file recovery against LockBit 3.0, they can offer advice tailored to your situation. Remember, paying the ransom is risky and doesn’t ensure file recovery.
Instead, focus on professional solutions and the potential use of decryption tools made available through reputable sources.
Free Decryption Tools vs. Paying the Ransom: Weighing the Pros and Cons
Considering the use of free decryption tools offers a glimmer of hope in what may seem like a desperate situation. These tools, when available, are developed by cybersecurity experts and are designed to decrypt files without compensating the attackers.
It’s a safer avenue that underlines the importance of not funding ransomware operations. However, their availability is limited and dependent on the specific ransomware variant.
Paying the ransom, on the other hand, is fraught with risks. There’s no guarantee that the attackers will provide the decryption key post-payment.
Furthermore, it encourages the continuation of criminal activities. Financial transactions with cybercriminals could also expose one to additional fraud.
Thus, seeking out free decryption tools, despite their limitations, is the recommended course of action over making ransom payments.
Restoring Files from Backups: A Safe Recovery Method
One of the most reliable methods to recover from a ransomware attack like LockBit 3.0 is restoring your files from backups. This method ensures that your data remains intact, providing a peace of mind that is unmatched by any decryption tool.
Regularly backing up your files on separate physical or cloud-based platforms ensures that you have uncontaminated copies available in case of an infection.
Before restoring from backups, it is critical to remove the ransomware from your system to prevent additional encryption. Using trusted security software like SpyHunter helps ensure the ransomware is completely eradicated from your system.
Once safe, you can proceed to restore your files from backups, minimizing data loss and getting back to routine operations much quicker.
It is essential not just to rely on a single backup solution but to have multiple backups in various locations. This diversifies risk and further protects your data from ransomware attacks and other forms of data loss.
Regularly updating these backups ensures that you have the latest versions of your files securely stored away, ready to be restored whenever necessary..
Preventative Measures to Secure Your Data Against Lock 3.0
In the fight against LockBit 3.0, a notorious ransomware threat, adopting preventative security measures is not just advisable but critical.
The first step in outsmarting such digital predators involves a synergy of robust passwords, multi-factor authentication, and the discipline of regular software updates.
Ensuring the use of strong, unique passwords is a foundational defense that cannot be overstated. Complementing this with multifactor authentication adds a vital layer of security, making unauthorized access significantly more difficult for cybercriminals.
Beyond passwords, the practice of regularly reassessing user account permissions to curb excessive access rights can notably diminish potential security breaches.
Moreover, decluttering your digital landscape by removing outdated or unused accounts and ensuring that your system’s configuration aligns with the latest security protocols are crucial steps towards safeguarding your digital assets against LockBit 3.0 threats.
Perhaps the most pivotal strategy in ransomware prevention involves the installation and update of a comprehensive enterprise cybersecurity solution.
Software like SpyHunter, renowned for its effectiveness against malware, can offer real-time protection and detection capabilities, essential for thwarting ransomware attacks before they infiltrate your systems.
Why Regular System Backups Can Save You from Ransomware Miseries
Regular system backups represent an indispensable safeguard in the contemporary digital environment, acting as a fail-safe against the potentially devastating impacts of ransomware attacks.
The essence of this strategy lies in maintaining current backups of critical data, stored independently from your main network. This approach ensures that, in the event of a ransomware infection, you can restore your systems without succumbing to the demands of cyber extortioners.
To optimize the effectiveness of your backup strategy, consider implementing a rotation system with multiple backup points, allowing you to choose the most recent clean data for restoration.
Furthermore, the integration of offline backup copies adds an extra layer of security, protecting your data from being compromised by online threats.
Implementing Strong Security Practices to Deter Future Attacks
Implementing strong security practices is a continuous process that demands attention and updates to stay ahead of cyber threats like LockBit 3.0.
A multi-layered approach to security, encompassing both technological measures and human vigilance, is paramount. Regular training sessions for employees on the latest cyber threats and best security practices can significantly reduce the risk of successful phishing attacks, a common entry point for ransomware.
Moreover, limiting administrative privileges and enforcing the principle of least privilege can greatly minimize the risk of internal threats and unauthorized access.
Network segmentation is another key practice that, by isolating critical parts of your network, can prevent the spread of ransomware across your entire system.
Finally, ensuring that all software is kept up to date, with the latest patches and updates applied, closes vulnerabilities that could be exploited by ransomware.
Organizations seeking to strengthen their defense against these relentless threats may find a reliable ally in security solutions like SpyHunter, designed to provide comprehensive protection and peace of mind.
The Importance of Keeping Software and Systems Updated
One of the simplest yet most effective strategies to protect against ransomware like LockBit 3.0 is to keep all software and operating systems up to date.
Cybercriminals frequently target known vulnerabilities in outdated software to deploy ransomware. Timely updates and patches are developed to fix these vulnerabilities, thereby providing an essential defensive tool against potential attacks.
This protective measure extends beyond just the operating system or commonly targeted software; it applies to all digital tools and platforms in use within an organization.
By fostering a culture of cybersecurity awareness and prioritizing regular updates, businesses can shield themselves from the ever-present threat posed by ransomware attacks.
In conclusion, securing your data against threats like LockBit 3.0 demands a proactive and comprehensive approach to cybersecurity.
From strengthening your first line of defense with robust passwords and multifactor authentication to the crucial practice of regular system backups, each step plays a vital role in building a resilient defense against ransomware attacks.
When coupled with ongoing vigilance and the latest in cybersecurity software, such as SpyHunter, organizations can navigate the digital landscape with confidence, knowing they are well-protected against the evolving threats of the digital age.
Must-Know Tips for Enhancing Your Cybersecurity Posture
Improving your cybersecurity posture is crucial in today’s interconnected world. With cyber threats becoming more sophisticated, it is important to arm yourself with knowledge and tools to protect your digital life.
Here, we delve into practical tips and strategic advice to bolster your defenses against cyber threats.
Cyber Hygiene: Everyday Practices to Keep Your Data Safe
Cyber hygiene refers to the routine, fundamental actions that users should take to maintain the health and security of their data. Just like personal hygiene keeps you healthy, cyber hygiene helps keep your digital life secure.
Here are essential practices to include in your daily online routine:
- Regularly update all software: Always download the latest versions of your operating system, applications, and firmware. Developers frequently release updates that fix vulnerabilities that could be exploited by hackers.
- Use strong, unique passwords: Each of your accounts should have a different password. Use a mix of letters, numbers, and symbols to create complex passwords, and consider using a password manager to keep track of them.
- Enable two-factor authentication (2FA): Wherever possible, add an extra layer of security by using 2FA. This requires not only your password but also something you have (like a code sent to your phone) to log in.
- Be cautious about what you click: Avoid clicking on links or downloading attachments from unknown sources, as they could be phishing attempts or contain malware.
- Back up your data regularly: Regular backups can be a lifesaver in many scenarios, such as ransomware attacks or hardware failure. Use external drives or cloud-based services to keep your important data safe.
By incorporating these habits into your daily online activities, you’ll significantly reduce your vulnerability to cyber threats.
Choosing the Right Cybersecurity Software: How SpyHunter Can Help
When it comes to safeguarding your digital environment, selecting the right cybersecurity software is a pivotal decision. SpyHunter is a highly effective malware remediation tool that stands out for its comprehensive protection against the latest malware threats, including ransomware, worms, trojans, and other malicious software.
SpyHunter is designed for the evolving digital landscape, offering intuitive protection that adapts to emerging threats. It provides real-time system guard features that block malware before it can do harm, as well as customized fixes for specific malware problems that might plague your computer.
- Active Malware Scanning: SpyHunter’s advanced malware scanner is updated regularly to detect and remove malware efficiently.
- Ransomware Protection: It provides robust defense mechanisms against ransomware attacks, safeguarding your data from being encrypted and held hostage.
- User-Friendly Interface: SpyHunter is designed with a straightforward interface, making it accessible for both tech-savvy users and those new to cybersecurity software.
- Customized Remediation: Unlike one-size-fits-all solutions, SpyHunter offers customized malware fixes to address unique threats to your system.
- Customer Support: With SpyHunter, you get access to excellent customer service, including a HelpDesk for personalized support.
Choosing SpyHunter not only provides you with effective defense against cyber threats but also peace of mind, knowing that you have a reliable tool at your disposal. For those seeking robust and adaptive cybersecurity software, SpyHunter is an excellent choice that meets a wide array of security needs.
Understanding the Legal and Ethical Implications of Ransomware Payments
In the face of a ransomware attack, the decision whether to pay the ransom demands a thorough analysis of both legal and ethical implications.
While the immediate response might lean towards making payments in hopes of data retrieval, it’s crucial to understand the broader ramifications. Engaging in ransom payments not only involves legal risks but also raises ethical concerns.
Legally, paying ransoms to groups recognized as terrorist organizations by any government can lead to severe legal consequences. Ethically, it contributes to the funding and encouragement of criminal activities, perpetuating a cycle of attacks not just against the payer but also against other potential targets.
From a legal standpoint, various jurisdictions have regulations and guidelines that discourage ransom payments. These regulations are in place not only to prevent financial support to criminal entities but also to deter the expansion of ransomware campaigns. Moreover, the lack of guarantee in data recovery post-payment adds to the complexity of the decision-making process.
Ethically, companies must consider their societal responsibilities. Paying ransom demands arguably fuels the ransomware economy. It supports a business model that hinges on exploitation and criminality, leading to more sophisticated and widespread attacks.
Therefore, organizations are encouraged to evaluate alternative recovery methods and strengthen their cybersecurity defenses to mitigate the risk of future attacks.
To Pay or Not to Pay? The Debate Around Ransomware Ransoms
The dilemma of paying a ransomware demand revolves around a critical debate: the immediate need for data recovery versus the long-term implications of supporting a criminal ecosystem.
On one side, businesses faced with halted operations and the potential loss of critical data might see payment as a necessary evil.
On the other side, the cybersecurity community and law enforcement agencies caution against payments, citing the lack of assurance that data will be decrypted and the risk of marking the payer as a future target.
Additionally, succumbing to ransom demands does not address the root cause of the breach. It leaves the door open for future attacks, emphasizing the importance of robust cybersecurity measures.
Investments in preventative technologies, employee training, and regular data backup practices present a more sustainable approach to safeguarding against ransomware threats.
Negotiating with Hackers: Is It Ever a Good Idea?
Negotiating with hackers presents a complex challenge. While some argue that negotiation might reduce ransom demands, it inherently acknowledges the hacker’s control over the situation.
Engaging in dialogue can unintentionally provide attackers with insights into the organization’s willingness to pay, potentially leading to increased demands or additional attacks.
Instead of negotiation, the focus should be on prevention, detection, and incident response. Emphasizing a proactive cybersecurity posture reduces the risk of becoming a victim in the first place.
Implementing security measures such as using reputable security software like SpyHunter can help detect and remove ransomware threats before they encrypt data. SpyHunter’s advanced algorithms are designed to provide real-time protection, offering a critical layer of defense against ransomware and other types of malware.
Ultimately, the decision to negotiate with hackers is fraught with risks. Organizations should weigh the potential short-term benefits against the long-term consequences.
Building resilience through strong cybersecurity practices and engaging with law enforcement can provide a more effective strategy in combating ransomware attacks.
- Step 1
- Step 2
- Step 3
- Step 4
- Step 5
Step 1: Scan for LockBit 3.0 with SpyHunter Anti-Malware Tool



Ransomware Automatic Removal - Video Guide
Step 2: Uninstall LockBit 3.0 and related malware from Windows
Here is a method in few easy steps that should be able to uninstall most programs. No matter if you are using Windows 10, 8, 7, Vista or XP, those steps will get the job done. Dragging the program or its folder to the recycle bin can be a very bad decision. If you do that, bits and pieces of the program are left behind, and that can lead to unstable work of your PC, errors with the file type associations and other unpleasant activities. The proper way to get a program off your computer is to Uninstall it. To do that:


 Follow the instructions above and you will successfully delete most unwanted and malicious programs.
Follow the instructions above and you will successfully delete most unwanted and malicious programs.
Step 3: Clean any registries, created by LockBit 3.0 on your computer.
The usually targeted registries of Windows machines are the following:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
You can access them by opening the Windows registry editor and deleting any values, created by LockBit 3.0 there. This can happen by following the steps underneath:


 Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Before starting "Step 4", please boot back into Normal mode, in case you are currently in Safe Mode.
This will enable you to install and use SpyHunter 5 successfully.
Step 4: Boot Your PC In Safe Mode to isolate and remove LockBit 3.0





Step 5: Try to Restore Files Encrypted by LockBit 3.0.
Method 1: Use STOP Decrypter by Emsisoft.
Not all variants of this ransomware can be decrypted for free, but we have added the decryptor used by researchers that is often updated with the variants which become eventually decrypted. You can try and decrypt your files using the instructions below, but if they do not work, then unfortunately your variant of the ransomware virus is not decryptable.
Follow the instructions below to use the Emsisoft decrypter and decrypt your files for free. You can download the Emsisoft decryption tool linked here and then follow the steps provided below:
1 Right-click on the decrypter and click on Run as Administrator as shown below:

2. Agree with the license terms:

3. Click on "Add Folder" and then add the folders where you want files decrypted as shown underneath:

4. Click on "Decrypt" and wait for your files to be decoded.

Note: Credit for the decryptor goes to Emsisoft researchers who have made the breakthrough with this virus.
Method 2: Use data recovery software
Ransomware infections and LockBit 3.0 aim to encrypt your files using an encryption algorithm which may be very difficult to decrypt. This is why we have suggested a data recovery method that may help you go around direct decryption and try to restore your files. Bear in mind that this method may not be 100% effective but may also help you a little or a lot in different situations.
Simply click on the link and on the website menus on the top, choose Data Recovery - Data Recovery Wizard for Windows or Mac (depending on your OS), and then download and run the tool.
LockBit 3.0-FAQ
What is LockBit 3.0 Ransomware?
LockBit 3.0 is a ransomware infection - the malicious software that enters your computer silently and blocks either access to the computer itself or encrypt your files.
Many ransomware viruses use sophisticated encryption algorithms to make your files inaccessible. The goal of ransomware infections is to demand that you pay a ransom payment to get access to your files back.
What Does LockBit 3.0 Ransomware Do?
Ransomware in general is a malicious software that is designed to block access to your computer or files until a ransom is paid.
Ransomware viruses can also damage your system, corrupt data and delete files, resulting in the permanent loss of important files.
How Does LockBit 3.0 Infect?
Via several ways.LockBit 3.0 Ransomware infects computers by being sent via phishing emails, containing virus attachment. This attachment is usually masked as an important document, like an invoice, bank document or even a plane ticket and it looks very convincing to users.
Another way you may become a victim of LockBit 3.0 is if you download a fake installer, crack or patch from a low reputation website or if you click on a virus link. Many users report getting a ransomware infection by downloading torrents.
How to Open .LockBit 3.0 files?
You can't without a decryptor. At this point, the .LockBit 3.0 files are encrypted. You can only open them once they are decrypted using a specific decryption key for the particular algorithm.
What to Do If a Decryptor Does Not Work?
Do not panic, and backup the files. If a decryptor did not decrypt your .LockBit 3.0 files successfully, then do not despair, because this virus is still new.
Can I Restore ".LockBit 3.0" Files?
Yes, sometimes files can be restored. We have suggested several file recovery methods that could work if you want to restore .LockBit 3.0 files.
These methods are in no way 100% guaranteed that you will be able to get your files back. But if you have a backup, your chances of success are much greater.
How To Get Rid of LockBit 3.0 Virus?
The safest way and the most efficient one for the removal of this ransomware infection is the use a professional anti-malware program.
It will scan for and locate LockBit 3.0 ransomware and then remove it without causing any additional harm to your important .LockBit 3.0 files.
Can I Report Ransomware to Authorities?
In case your computer got infected with a ransomware infection, you can report it to the local Police departments. It can help authorities worldwide track and determine the perpetrators behind the virus that has infected your computer.
Below, we have prepared a list with government websites, where you can file a report in case you are a victim of a cybercrime:
Cyber-security authorities, responsible for handling ransomware attack reports in different regions all over the world:
Germany - Offizielles Portal der deutschen Polizei
United States - IC3 Internet Crime Complaint Centre
United Kingdom - Action Fraud Police
France - Ministère de l'Intérieur
Italy - Polizia Di Stato
Spain - Policía Nacional
Netherlands - Politie
Poland - Policja
Portugal - Polícia Judiciária
Greece - Cyber Crime Unit (Hellenic Police)
India - Mumbai Police - CyberCrime Investigation Cell
Australia - Australian High Tech Crime Center
Reports may be responded to in different timeframes, depending on your local authorities.
Can You Stop Ransomware from Encrypting Your Files?
Yes, you can prevent ransomware. The best way to do this is to ensure your computer system is updated with the latest security patches, use a reputable anti-malware program and firewall, backup your important files frequently, and avoid clicking on malicious links or downloading unknown files.
Can LockBit 3.0 Ransomware Steal Your Data?
Yes, in most cases ransomware will steal your information. It is a form of malware that steals data from a user's computer, encrypts it, and then demands a ransom in order to decrypt it.
In many cases, the malware authors or attackers will threaten to delete the data or publish it online unless the ransom is paid.
Can Ransomware Infect WiFi?
Yes, ransomware can infect WiFi networks, as malicious actors can use it to gain control of the network, steal confidential data, and lock out users. If a ransomware attack is successful, it could lead to a loss of service and/or data, and in some cases, financial losses.
Should I Pay Ransomware?
No, you should not pay ransomware extortionists. Paying them only encourages criminals and does not guarantee that the files or data will be restored. The better approach is to have a secure backup of important data and be vigilant about security in the first place.
What Happens If I Don't Pay Ransom?
If you don't pay the ransom, the hackers may still have access to your computer, data, or files and may continue to threaten to expose or delete them, or even use them to commit cybercrimes. In some cases, they may even continue to demand additional ransom payments.
Can a Ransomware Attack Be Detected?
Yes, ransomware can be detected. Anti-malware software and other advanced security tools can detect ransomware and alert the user when it is present on a machine.
It is important to stay up-to-date on the latest security measures and to keep security software updated to ensure ransomware can be detected and prevented.
Do Ransomware Criminals Get Caught?
Yes, ransomware criminals do get caught. Law enforcement agencies, such as the FBI, Interpol and others have been successful in tracking down and prosecuting ransomware criminals in the US and other countries. As ransomware threats continue to increase, so does the enforcement activity.
About the LockBit 3.0 Research
The content we publish on SensorsTechForum.com, this LockBit 3.0 how-to removal guide included, is the outcome of extensive research, hard work and our team’s devotion to help you remove the specific malware and restore your encrypted files.
How did we conduct the research on this ransomware?
Our research is based on an independent investigation. We are in contact with independent security researchers, and as such, we receive daily updates on the latest malware and ransomware definitions.
Furthermore, the research behind the LockBit 3.0 ransomware threat is backed with VirusTotal and the NoMoreRansom project.
To better understand the ransomware threat, please refer to the following articles which provide knowledgeable details.
As a site that has been dedicated to providing free removal instructions for ransomware and malware since 2014, SensorsTechForum’s recommendation is to only pay attention to trustworthy sources.
How to recognize trustworthy sources:
- Always check "About Us" web page.
- Profile of the content creator.
- Make sure that real people are behind the site and not fake names and profiles.
- Verify Facebook, LinkedIn and Twitter personal profiles.


