Researchers at TrendMicro have discovered MalumPoS – an attack tool designed to breach any PoS (Point of Sale) system. Presently, the PoS RAM scraper is set to harvest data from PoS systems running on Oracle® MICROS®. The platform is commonly used in the hospitality, food and beverage, and retail business sectors. According to Oracle, MICROS is applied to more than 330,000 customer sites, most of them being based in the US. The attack tool has put several big American companies at risk, as well as their clients.
What Exactly Is a PoS RAM Scraper?
Basically, Point-of-Sale RAM scrapers such as MalumPoS are developed to scrape off credit card information from the RAM of the infected system. In other words, each time the credit card is swiped, the PoS data scraper can collect the owner’s credentials. 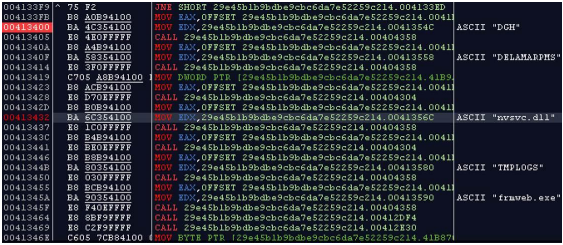
Then, stolen credit card data can be used to:
- Clone credit cards.
- Execute forged transactions such as online purchases.
MalumPos, in particular, has been designed to be configurable, meaning that the attack tool can later be altered by adding other processes or targets. The attackers can include or exclude types of PoS systems, resulting in more companies being attacked, and more credit data compromised.
The Features of MalumPoS
Besides being configurable, MalumPoS has an NVIDIA disguise.
Users may wonder what an NVIDIA disguise is. Once installed on a system, the RAM scraper camouflages itself as the NVIDIA Display Driver. It can also appear as an “NVIDIA Display Driv3r”. The reason for the disguise is that the popularity of NVIDIA components among users can make the malware look harmless.
The Targeted Systems
As already mentioned, the MalumPoS RAM scraper targets the Oracle Micro systems. Other affected systems may include:
- Oracle Forms.
- Systems accessed via Internet Explorer.
Credit Cards at Risk of MalumPos
MalumPoS is written in such a way that it selectively collects data from:
→Visa, MasterCard, AmericanExpress, Discover, Diner’s Club.
MalumPoS Detection Rates and Removal Options
As noted by TrendMicro researchers in their vast report, threat actors can configure future variants of binary codes, according to their targets. There are several endpoint monitoring software tools that detect the components of the PoS RAM scraper. Innovative strategies to deal with threats of the scale are awaited by both average users and enterprises.
Spy Hunter scanner will only detect the threat. If you want the threat to be automatically removed, you need to purchase the full version of the anti-malware tool.Find Out More About SpyHunter Anti-Malware Tool / How to Uninstall SpyHunter


