Due to its global dominance on the market, Windows has always been the most targeted operating system out there. However, Microsoft has been struggling to secure its product which has led to a (not that) surprising outcome. It turns out that the more secure Windows goes the more prone to attacks macOS and Linux become. Even though it may appear these events are not directly related, it is indeed true that the latter operating systems have seen more attacks than ever before.
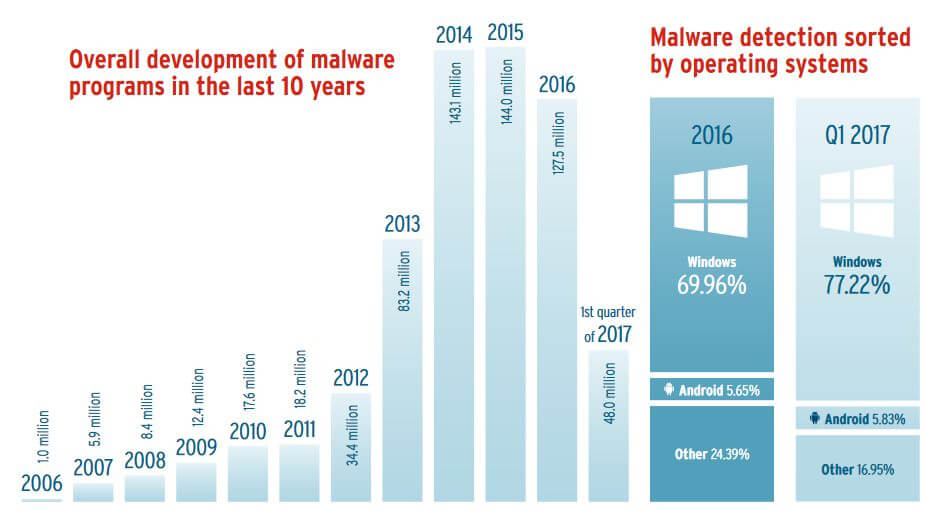
According to AV-TEST security report for 2016/2017, Apple systems have seen three times more attacks compared to past years. As for Windows, the malware targeting Microsoft’s OS has increased by the insignificant 10%. Moreover, the quantity of malware specifically crafted for Windows have even decreased by 13%.
“It remains positive to note that the declining malware trend in 2016 provided some relief, at least quantitatively. Thus, compared to 2015, detection systems were required to seek out and defend against 14% fewer malware samples,” the report reads. “In total, this amounted to precisely 11,725,292 fewer newly developed malware programs than in the previous year.”
However, it is unfortunate that the volume of newly developed malware in 2016 is still the second-highest since the very first time AV-TEST started measuring the numbers, researchers say.
Most Popular Windows, Linux and Apple Malware
Even though Windows still is the most targeted OS out there, Apple and Linux machines have recorded three times more attacks.
According to the institute’s measurements, the most popular Windows malware in 2016 was Allaple, a threat that has been active since 2006 or even earlier. Next on the popular list are Virut, Ramnit, and Virlock. Interestingly, even though ransomware attacks were quite prevalent last year and continued to be so in 2017 (WannaCry, NotPetya) , ransomware accounts for less than 1% of all Windows malware. Viruses and worms continue to top the list with respectively 37.60% and 25.44%.
The number of malware samples in 2016 declined by 15% compared to previous year. However, the fever curve rose again by 7% in the first quarter of 2017. At the time this report was concluded at the end of June 2017, there were already 600 million malware programs detected by AV-TEST targeting the frequently used operating system from Redmond.
macOS, on the other hand, has seen plenty of Trojans – the type of malware that prevailed in 2016 in 85.59%. Ransomware represents 0.07% of all attacks.
With an increase rate of over 370% compared to the previous year, it is no exaggeration to speak of explosive growth. However, it is also important to keep an eye on the overall number of malware programs with which criminals try to cheat Mac users: Whereas in 2015 there were a moderate 819 different malware threats targeting macOS, Apple users in 2016 already had to protect their devices from 3033 malware samples.
As for the most popular Mac malware in 2016 – the top three names are Flashback, MacControl, and Keranger.
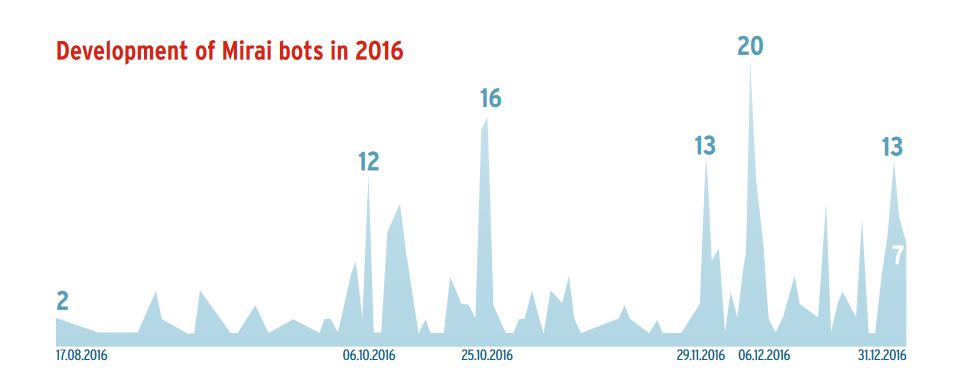
The report also pays attention to the Mirai botnet. “Due to programming errors and the public-oriented attack variant, DDoS, the malware programs of this type were relatively easy to locate”, researchers note. What is quite unfortunately and in the same time troublesome is that most of the IoT devices failed to offer any effective protection against the Mirai infections.
IoT Malware – Nothing New
What about other Linux malware? For example, the Tsunami backdoor has been active for many years and can be easily modified to target IoT devices. AV-TEST first detected the threat in 2003, and even though there was no IoT malware back then, the backdoor was sufficient enough to offer functions that would work even today. Old malware can indeed be used in IoT-related DDoS attacks.
Tsunami is not the only old malware that can be shifted towards IoT devices. The Darlloz worm, known since 2013, together with many other Linux and Unix malware, have similar attack patterns. This only means that IoT malware is nothing new, and the ever-growing number of connected devices will continue to make things worse each year.