SPOILERS ALERT!
Have you been impatiently looking forward to Mr. Robot’s second season? Do you always have questions about the hacks that take place during the show? Are you often pausing to have a closer look at what’s written on that PC screen? Stay tuned! We’re also hooked on Mr. Robot and we’ll be looking for answers ourselves on an episode-basis.
Even though eps2.2init1.asec starts off with a flashback, the flashback falls right into place with this season’s atmosphere. Season 2 is gradually filling in the gaps from season 1, in a subtle and yet very convincing way. But before we proceed, the tradition commands us to decode the episode’s title, eps2.2_init1.asec.
On the tech side: In Linux, Init is the parent of all processes. Its fundamental role is to create processes from a script stored in the file /etc/inittab. Init also controls autonomous processes required by a system. Init1 takes the system into single user mode. Typically this means services such as sshd will be terminated, and in fact, may terminate all networking on some systems.
On Mr. Robot’s side: Init1 literally depicts the “battle” Elliot is about to have with Mr. Robot. Well, it’s a chess game which eventually turns out to be impossible to win. This alone slowly begins to formulate the answer to the question Elliot has been facing. How to help everybody he cares about, and save himself from the arduous inner-ism that has isolated him from the world. Because no one can win, someone has to retreat. Is Mr. Robot the one to take control of Elliot and the situation, or is it the other way around?
To take the init1 interpretation further, we also see Angela come to some strong conclusions in terms of why she’s at Evil Corp, and what she has to do. Perhaps her innuendo will unravel and deliver results in the episodes to follow? This time she was owned.
Overall, eps2.2_init1.asec, unearths a very cinematic experience, fortified by the musical score (Gustav Holst’s The Planets drives us through the first flashback scenes). It’s a more character-driven episode with less hacking. Nonetheless, it’s a rather important piece of the puzzle called Mr. Robot, as we literally witness his (Mr. Robot’s) birth. Darlene had a lot to do with it.
Darlene, the Flashbacks and the Mask
Speaking of Darlene, the episode is basically focused on her and showcases her relationship with Elliot before he took the job at Allsafe and forgot Darlene was his sister. The insight on Darlene’s personality, like the fact that she suffers from panic attacks and barely remembers their dad, helps us understand why she is the way she is. Also, it becomes evident that she is quite the hacker herself, as she’s in charge of this episode’s most impressive hacking gimmick. The trick she executes is both creative and advanced (scroll down for more details). Go, Darlene!
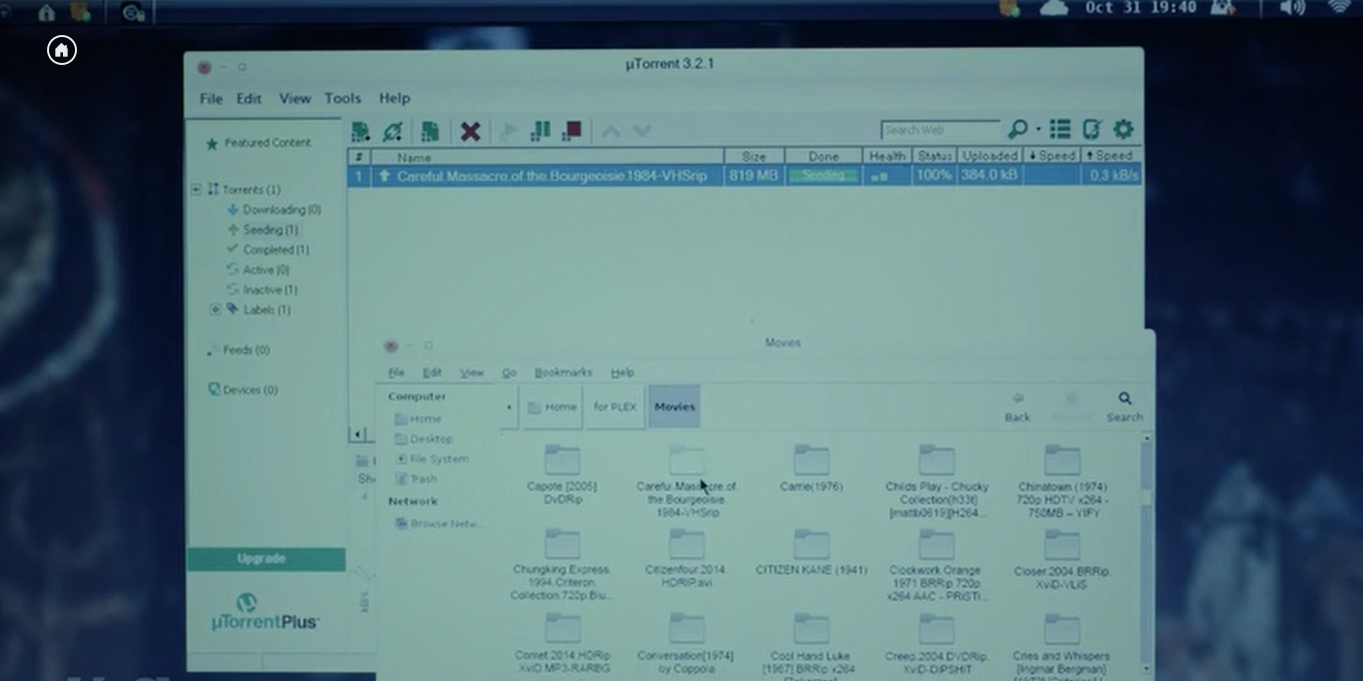
The story brings us back to one Halloween evening, when she shows up at Elliot’s door and tells him she needs him. She’s also bringing a special treat – a torrent version (Careful.Massacre.of.the.Bourgeoisie.1984-VHSrip) of their favorite VHS horror The Careful Massacre of the Bourgeoisie. It’s a made-up ‘80’s flick created by Sam Esmail specifically to serve Mr. Robot’s story… Well, almost made-up, since USA already released the movie online as a sub-10 minute film! It’s just another proof of Esmail’s dedication to detail and to delivering a full-length experience with no story loopholes, whatsoever.
In the heat of their conversation, Elliot puts on his father’s jacket, and Darlene hands him the mask she brought as a compliment to the movie they’re about to see. Yes, this is fsociety’s infamous face which in fact Darlene “borrowed” from the movie! This scene is perhaps the very first time Elliot snaps out of his own personality and transforms into another person for just a glimpse of a moment.
“I guess it’s official… I’m crazy!”, Elliot mumbles. He’s telling Darlene that he got fired. He’s now beginning to consider going for the job at Allsafe Angela has been telling him about.
“Maybe I should take the job, be a Trojan horse and take them down [Evil Corp]”, Elliot says. In case you have forgotten, one of Allsafe’s top clients is (was) Evil Corp. Elliot sees a way in.
Tyrell Wellick?
Tyrell is still… away. His wife, however, is here and she’s paying off Kareem, the parking lot attendant who we met in the season one’s finale. Back then, Kareem told Elliot that Wellick’s car was only paid for 3 days. Why is Joanna paying him and what does she know? There’s something rotten here, I can smell it!
What about the Hacks in eps2.2_init1.asec?
Darlene’s Hack: “I hacked the Postmates proxy that supports the APN for my boyfriend’s cell carrier. Now it does a URL rewrite and sends every postmates.com request to my affiliate link—meaning, I get $10 coupons each time a sucker orders anything.”
Is the hack realistic? Yes, it is, and it’s exploited quite often by real crooks, who are after quick cash. Obviously, this scheme involves affiliate links…
An affiliate link is a specific URL that contains the affiliate’s ID or username. In affiliate programs, advertisers use affiliate links to record the traffic that is sent to the advertiser’s website. This action is all part of an affiliate program.
…and affiliate tags. Here’s one definition of affiliate tagging given by marketer Missy Ward:
Similar to tagging content or friends on a social marketing platform, […] Tag System allows merchants to categorize affiliates with unlimited amounts of tags and unlimited rules-based options, allows merchants to alter how commissions are paid based on those tags and other information.
Websites add affiliate tags to make money without the means of advertising. There are even plugins that can do that automatically!
The whole system works as a coded message between websites and retailers and most users won’t even notice the presence of such tags. It’s a network of invisible signals, each one corresponding to a small sum.
If you can replace those signals in transit, that money becomes yours. It’s an extremely common way for hackers to cash out. It could be a simple hack, like a scammy Chrome extension that modifies links for a quick buck, or it could be much more complex.
Since hacking affiliate links is not that hard at all, the more interesting part is that Darlene is successfully and continuously doing this to a single, specific device.
Darlene is able to insert those affiliate tags because she has direct access to all of the requests coming out of her boyfriend’s phone. By altering his Access Point Name settings (also known as APN), he’s arranged to forward his mobile data through a proxy. But Darlene hacked into that proxy, so now it intercepts each Postmates link and adds her own affiliate link.
Elliot’s Migration for Ray: Elliot finally agrees to help Ray but he has his own agenda. He needs access to a computer to talk to Darlene via an old-school IRC chat. Darlene tells him over the phone that they’re owned (pwned?) and Elliot immediately needs to do something about it.
What should we be looking forward to in next episode?
A zoom on:
- Whiterose’s relationship with Phillip Price
- The Ecoin strategy
- Dark Army’s operation Berenstain (here’s one crazy theory)
- Joanna’s connection to Elliot’s three missing days
- Tyrell!
Or perhaps we should just expect the unexpected?