Have you ever wondered about the inner workings of your computer and the files that keep things running smoothly? One such file, msedgewebview2.exe, may not be widely known but plays a pivotal role in enhancing the Microsoft Edge browser’s functionality. This comprehensive guide dives into what msedgewebview2.exe is, its importance for integrating web content within applications, and its security implications.
Msedgewebview2.exe is a process, associated with the Microsoft Edge browser. However, there are reports that malware can exploit the process by masquerading itself as “Msedgewebview2.exe” virus. This is especially true in cases when the file is located in the C:\Windows or C:\Windows\System32 folder. If you see this process running on your Windows machine and you suspect that it is harming your computer, we recommend scanning it with a reputable anti-malware program.
Msedgewebview2.exe Details
| Name | Msedgewebview2.exe |
| Type | Infostealer, Malware, Trojan |
| Short Description | A dangerous malware which can steal sensitive information from infected systems. |
| Symptoms | Infected users may not notice any particular symptoms, as the infostealer is installed silently. |
| Distribution Method | Phishing emails, Exploit kits, Bundled with legitimate software |
| Detection Tool |
See If Your System Has Been Affected by malware
Download
Malware Removal Tool
|
Deciphering msedgewebview2.exe: A Comprehensive Guide
What Is msedgewebview2.exe and Its Purpose?
Msedgewebview2.exe is an executable file that plays a crucial role in enhancing the functionality of the Microsoft Edge browser through what’s known as the Microsoft Edge WebView2 Runtime. In essence, it’s a component that provides the tech infrastructure for embedding web content within native applications. This capability is especially beneficial for developers looking to create hybrid apps that blend web and native elements for a seamless user experience. By leveraging the Chromium open-source project, msedgewebview2.exe offers a robust environment for HTML, CSS, and JavaScript, allowing for high-performance and customizable web content integration within apps. Its development by Microsoft aims to streamline and enrich the developer’s toolkit for more sophisticated and effective application development.
Is msedgewebview2.exe Considered Safe or a Security Threat?
In general, msedgewebview2.exe is safe, as it is a legitimate component of the Microsoft Edge browser, digitally signed and developed by Microsoft. It usually resides in the Microsoft Edge WebView Application directory and is essential for certain applications that require web content embedding. However, the safety of the msedgewebview2.exe process can come into question when malware exploits its name to disguise itself within your system. Malicious programs occasionally mimic legitimate file names like msedgewebview2.exe to avoid detection, often residing in unusual directories such as C:\Windows or C:\Windows\System32, which can be a red flag.
To determine whether the msedgewebview2.exe on your system is safe or possibly a malware in disguise, checking its publisher via the file’s properties can offer clarity. Legitimate instances of the file should be signed by Microsoft Corporation. An absence of a digital signature or discovery of the file in unexpected locations within your system could indicate a compromise. In such scenarios, it’s not just about removing a suspicious file – it’s about ensuring your system’s overall security isn’t breached.
For anyone suspecting that msedgewebview2.exe could be maliciously replicated on their device, conducting a malware scan with a reputable anti-malware tool is advisable. In this context, SpyHunter comes highly recommended. It’s tailored for detecting and removing malware, including masquerading processes like fake msedgewebview2.exe files. By ensuring your system is scanned regularly with sophisticated anti-malware software like SpyHunter, you stand a better chance at maintaining a clean, efficient, and secure computing environment.
In brief, while msedgewebview2.exe is fundamentally a safe and useful component of the Microsoft Edge environment, vigilance is crucial to identifying and mitigating potential threats that might exploit its identity. Making informed checks on the file’s legitimacy and employing security solutions are essential steps towards safeguarding your digital space.
Identifying the Role of msedgewebview2.exe in Windows 10/11
The msedgewebview2.exe process plays a crucial role within the Windows 10 and Windows 11 operating systems. It’s a part of Microsoft Edge WebView2, which enables applications to provide web-based features. By leveraging HTML, CSS, and JavaScript, applications can offer rich content and interactive experiences, thanks to this component. Whether it’s a simple app requiring web content display or a complex application integrating advanced web technologies, msedgewebview2.exe is instrumental in bridging the web and native desktop environments.
The Significance of msedgewebview2.exe in System Operations
Understanding the significance of msedgewebview2.exe sheds light on its importance in system operations. This executable is not just another process; it’s a backbone for applications needing embedded web technologies. By using Microsoft Edge WebView2 Runtime, it ensures that developers have the tools to create more robust and interactive applications. This, in turn, enhances the user experience by allowing native applications to seamlessly incorporate web content and functionalities. Consequently, msedgewebview2.exe underlines the evolving nature of software, where web and desktop applications converge to offer users a cohesive experience across different platforms.
Common Misconceptions About msedgewebview2.exe
- It’s a Virus or Malware: One of the most common misconceptions about msedgewebview2.exe is that it’s a virus or malware. While it’s true that malware can impersonate legitimate processes, msedgewebview2.exe itself, when part of the Windows operating system and located in its default directory, is entirely safe. Misidentification often arises due to lack of information or the presence of actual malware mimicking this process’s name.
- It’s Non-Essential and Can Be Removed: Another notion is that msedgewebview2.exe is non-essential and can be removed without consequences. This file is pivotal for applications relying on web content, and its removal could disrupt their functionality. It serves a specific purpose and, unless it’s causing issues or identified as malware, should ideally remain untouched.
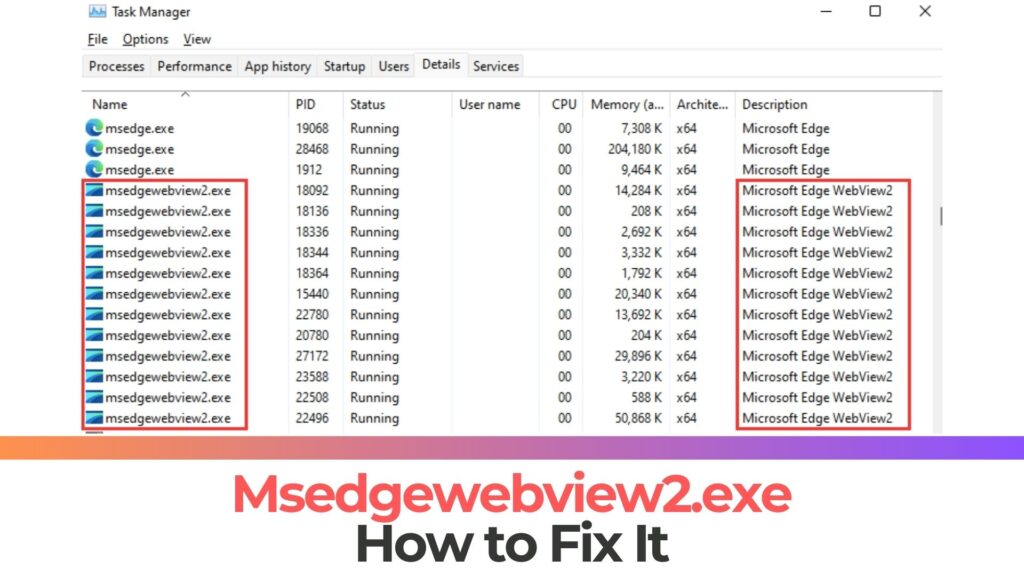
- It Uses Excessive Computer Resources (CPU): Some users believe that msedgewebview2.exe consumes an excessive amount of system resources. While any process can potentially use significant resources due to bugs or inefficient coding, under normal circumstances, msedgewebview2.exe is designed to operate efficiently. If resource consumption is high, it warrants a check for potential underlying issues, such as the presence of malware masquerading as this process.
In addressing these misconceptions, it’s crucial to perform regular system checks and consult reliable sources before taking action based on assumptions. For concerns regarding potential malware disguised as msedgewebview2.exe, utilizing reputable security software, such as SpyHunter, can help in identifying and mitigating threats, ensuring your system’s integrity and performance.
Security Concerns: Assessing the Risks of msedgewebview2.exe
When it comes to the security of our digital devices, vigilance is paramount, especially regarding the processes and applications running on our systems. Msedgewebview2.exe, primarily associated with the Microsoft Edge browser, serves as a background process for web content rendering. Despite its legitimate use, the versatility of this executable has caught the attention of malicious actors. It’s crucial to distinguish between the benign and potentially harmful versions of msedgewebview2.exe to protect your digital environment.
How to Verify the Authenticity of msedgewebview2.exe File?
Verifying the authenticity of msedgewebview2.exe is a straightforward process that can save you from potential security threats. Start by locating the file on your computer, typically found in the Program Files (x86) directory under the Microsoft Edge folder. Right-click on the file, select Properties, and navigate to the Digital Signatures tab. A legitimate msedgewebview2.exe file should list Microsoft Corporation as the signer. Furthermore, checking the details of the digital certificate for validity dates and the signature algorithm can offer additional assurance of the file’s authenticity.
Telltale Signs That msedgewebview2.exe May Be Malicious
The presence of msedgewebview2.exe on your system is not inherently alarming. However, certain indicators should raise red flags:
- Unusual Location: As noted, the legitimate file is usually stored within a specific folder path (
Program Files (x86)\Microsoft\EdgeWebView). If you find msedgewebview2.exe in other locations, especially within system folders likeWindowsorSystem32, this could signify a malicious version. - Excessive Resource Use: While some resource use by msedgewebview2.exe is expected, abnormally high CPU or memory usage can indicate that the process is being exploited for other purposes, such as mining cryptocurrencies or performing unauthorized tasks in the background.
- Pop-Ups and Other Anomalies: Experiencing unexpected pop-ups, system slowdowns, or other erratic behaviors while msedgewebview2.exe is running could suggest the process has been compromised.
Identifying and responding to the risks associated with msedgewebview2.exe requires a mix of awareness and action. Regularly scanning your system with security software, like SpyHunter, ensures that even the most subtle signs of compromise are detected and addressed, safeguarding your system’s integrity.
Given the sophistication of modern cyber threats, it’s crucial to equip your system with robust security tools. SpyHunter’s advanced scanning technology is designed to identify and eliminate malware masquerading as legitimate files, like msedgewebview2.exe, ensuring your digital safety remains uncompromised. Regular scans and staying informed about potential threats are your best defense against the ever-evolving landscape of digital security risks.
Effective Strategies for Managing msedgewebview2.exe
Keeping your computer safe and running smoothly often requires attention to the seemingly small details, such as managing executable files like msedgewebview2.exe. This file, integral to the Microsoft Edge browser, sometimes becomes a target for malware. Understanding how to manage and troubleshoot issues with msedgewebview2.exe is crucial for maintaining system integrity and personal security. Here, we explore effective strategies ranging from preventive measures to the nuanced differences between manual and automatic file removal, ensuring your system remains robust against potential threats.
Preventive Measures to Ensure msedgewebview2.exe Security
Prevention is always the first line of defense in cybersecurity. To secure the msedgewebview2.exe process, start by ensuring your computer is regularly updated. Windows Update is a tool that can automate most of this process, safeguarding your system against vulnerabilities that could be exploited by malware masquerading as legitimate files.
- Regular scans for malware: Utilize reputable anti-malware software to detect and remove any malicious software. Regular scans can help catch threats that might disguise themselves as legitimate processes.
- Clean your hard drive: Tools like Disk Cleanup and System File Checker (sfc /scannow) help keep your system free of unnecessary files that could slow down your computer or harbor malware.
- Uninstall unnecessary applications: Removing programs you no longer need can minimize the number of vulnerabilities on your system.
- Monitor autostart programs: Use system configuration (msconfig) to manage startup programs. Limiting these can help speed up your system and reduce the risk of malicious programs running unnoticed.
- Enable automatic updates: Keeping your operating system and software up to date is crucial for patching security vulnerabilities.
By adopting these preventive measures, you can significantly reduce the likelihood of encountering issues with the msedgewebview2.exe file and maintain a secure, efficient computing environment.
Manual vs. Automatic Removal of Suspicious msedgewebview2.exe Files
When it comes to handling a suspicious msedgewebview2.exe file, you have two primary strategies: manual removal and automatic removal using security software. Each approach has its advantages and considerations.
Manual Removal: This method involves the user directly locating and deleting the suspect file. It’s advisable for users who are familiar with Windows file systems and feel comfortable discerning safe files from malicious ones. Key steps include:
- Backing up important files to prevent data loss.
- Using Task Manager to end any suspicious processes.
- Navigating to the file location and deleting it if it displays irregularities, such as an unusual location or creation date.
Manual removal offers direct control over the process but requires a certain level of expertise to avoid mistakenly deleting crucial system files.
Automatic Removal: This strategy leverages anti-malware tools like SpyHunter to scan, identify, and remove threats. It’s suited for all users, regardless of technical expertise, and provides a safer alternative to manual removal. Benefits include:
- Comprehensive scanning: Automatically detects malware that might be missed during a manual review.
- User-friendly: Offers an intuitive interface that guides users through the detection and removal process.
- Efficiency: Saves time and reduces the risk of human error by automating the threat detection and removal process.
Choosing between manual and automatic removal should be based on your familiarity with the Windows operating system, the level of potential threat, and the importance of ensuring a malware-free environment. For those seeking a straightforward and reliable method, automatic removal using reputable software like SpyHunter often represents the best blend of safety and ease of use.
Navigating Troubles Caused by msedgewebview2.exe
Microsoft Edge WebView2, denoted by the process msedgewebview2.exe, plays a crucial role in enabling web technologies within native applications. Despite its importance, users may occasionally face issues that can hinder the optimal performance of their computers. Addressing these challenges requires a careful approach, combining proactive maintenance with targeted troubleshooting techniques.
Solutions for Common msedgewebview2.exe Errors and Issues
Encountering errors with msedgewebview2.exe can be frustrating. The following steps can significantly mitigate or resolve such issues:
- Regular System Scans: Schedule thorough malware scans to detect and remove any malicious software that might be masquerading as or targeting msedgewebview2.exe.
- Clean and Optimize Storage: Utilize built-in utilities like Cleanmgr and sfc /scannow to free up disk space and repair corrupted system files, enhancing overall performance and stability.
- Review and Adjust Autostart Programs: Monitor and manage startup programs through msconfig to prevent unnecessary applications from consuming system resources at boot time.
Keep the System Updated: Enable automatic updates for Windows to ensure that your system and its components, including msedgewebview2.exe, are up to date with the latest security patches and performance improvements.- Backup and Restore Points: Regularly back up important data and set system restore points. This precaution allows you to revert to a previous state in case of major issues.
When specific problems arise, recalling the last action performed before the error can provide valuable clues for troubleshooting. If necessary, you can resort to commands like resmon to identify resource-hungry processes or use DISM.exe to repair your Windows installation without losing data.
When Should You Consider Disabling msedgewebdrawer2.exe?
Despite its utility, there are circumstances where disabling or removing msedgewebview2.exe might be warranted:
- Performance Issues: If the process is consistently using an excessive amount of system resources, causing slowdowns or instability.
- Suspected Malware: In instances where the file’s location or behavior raises concerns about its legitimacy, verifying its authenticity is crucial. Tools like Security Task Manager can help discern if msedgewebview2.exe is genuine or a threat.
- Unnecessary for User’s Needs: Users who do not require the specific functionalities provided by Microsoft Edge WebView2 may opt to disable the process to streamline their system’s operation.
However, it’s important to proceed with caution. Before taking action, assess whether the file is causing genuine issues or if its functionality is essential for your applications. Should you decide to remove or disable msedgewebview2.exe but are concerned about potential malware, utilizing a reliable anti-malware software like SpyHunter ensures a thorough investigation and clean-up of any threats, keeping your system secure and functional.
Expert Recommendations for msedgewebview2.exe Issues
When it comes to dealing with msedgewebview2.exe issues, it’s pivotal to adopt a proactive and informed approach. Keeping your computer clean, secure, and up-to-date is fundamental. This involves scanning for malware, optimizing your hard drive, managing installed programs, and ensuring your operating system is current. Regularly back up important data and set restore points to safeguard against unexpected problems. If issues arise, remember the last changes you made as they can be pivotal clues. For deeper system concerns, tools like DISM can repair without data loss.
Choosing the Right Tools to Detect and Remove Malware
Selecting effective tools for malware detection and removal is critical in maintaining a secure system. A quality anti-malware solution offers comprehensive protection against a wide range of threats, including those that may disguise themselves as legitimate processes like msedgewebview2.exe. Security software should offer real-time protection, frequent updates, and detailed scan options. In addition, consider tools that provide system optimization features to further maintain your computer’s health.
How SpyHunter Can Help Secure Your System Against msedgewebview2.exe Threats
SpyHunter offers robust protection against malware that could pose as msedgewebview2.exe or exploit its processes. It scans your system in-depth, identifying hidden threats and removing them with precision. With regular updates to tackle the latest malware variants and a user-friendly interface, SpyHunter is designed to offer both top-notch security and ease of use. In dealing with sophisticated threats that leverage msedgewebview2.exe, SpyHunter’s advanced mechanisms can provide a crucial shield for your computer, ensuring peace of mind through comprehensive digital security.
Final Thoughts on msedgewebview2.exe
Ensuring the safety and security of your computer environment is crucial in an age where threats can appear in many forms. The msedgewebview2.exe process, generally associated with Microsoft Edge, underscores the need for vigilance, as this seemingly benign process can sometimes be masqueraded by malicious software aiming to compromise your system.
To maintain a secure digital space, understanding and following best practices for detecting and resolving issues related to msedgewebview2.exe is essential. Start by verifying the legitimacy of this process through the examination of its publisher information. A digital signature from a recognized entity suggests safety, but the absence of such a signature should raise concerns.
Keep your computer clean and organized. Regularly scan for malware with reliable tools and keep your system updated. Should you find the integrity of msedgewebview2.exe questionable, employing a reputable security solution like SpyHunter not only helps in identification but also in the effective removal of any malicious software disguised under this process name.
Maintaining a habit of periodic system scans, coupled with careful monitoring of software installations and automatic startup programs, forms a foundational strategy in preempting potential issues. In addition, leveraging utilities like ‘cleanmgr’, ‘sfc /scannow’, and others aid in fortifying your system’s resistance to threats.
In conclusion, the security of your computing environment hinges on proactive measures and informed choices. While msedgewebview2.exe might be a legitimate component of your Windows operating system, it’s vital to stay aware that it could also serve as a cover for malicious activities.
Preparation before removing Msedgewebview2.exe.
Before starting the actual removal process, we recommend that you do the following preparation steps.
- Make sure you have these instructions always open and in front of your eyes.
- Do a backup of all of your files, even if they could be damaged. You should back up your data with a cloud backup solution and insure your files against any type of loss, even from the most severe threats.
- Be patient as this could take a while.
- Scan for Malware
- Fix Registries
- Remove Virus Files
Step 1: Scan for Msedgewebview2.exe with SpyHunter Anti-Malware Tool



Step 2: Clean any registries, created by Msedgewebview2.exe on your computer.
The usually targeted registries of Windows machines are the following:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
You can access them by opening the Windows registry editor and deleting any values, created by Msedgewebview2.exe there. This can happen by following the steps underneath:


 Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.Step 3: Find virus files created by Msedgewebview2.exe on your PC.
1.For Windows 8, 8.1 and 10.
For Newer Windows Operating Systems
1: On your keyboard press + R and write explorer.exe in the Run text box and then click on the Ok button.

2: Click on your PC from the quick access bar. This is usually an icon with a monitor and its name is either “My Computer”, “My PC” or “This PC” or whatever you have named it.

3: Navigate to the search box in the top-right of your PC's screen and type “fileextension:” and after which type the file extension. If you are looking for malicious executables, an example may be "fileextension:exe". After doing that, leave a space and type the file name you believe the malware has created. Here is how it may appear if your file has been found:

N.B. We recommend to wait for the green loading bar in the navigation box to fill up in case the PC is looking for the file and hasn't found it yet.
2.For Windows XP, Vista, and 7.
For Older Windows Operating Systems
In older Windows OS's the conventional approach should be the effective one:
1: Click on the Start Menu icon (usually on your bottom-left) and then choose the Search preference.

2: After the search window appears, choose More Advanced Options from the search assistant box. Another way is by clicking on All Files and Folders.

3: After that type the name of the file you are looking for and click on the Search button. This might take some time after which results will appear. If you have found the malicious file, you may copy or open its location by right-clicking on it.
Now you should be able to discover any file on Windows as long as it is on your hard drive and is not concealed via special software.
Msedgewebview2.exe FAQ
What Does Msedgewebview2.exe Trojan Do?
The Msedgewebview2.exe Trojan is a malicious computer program designed to disrupt, damage, or gain unauthorized access to a computer system. It can be used to steal sensitive data, gain control over a system, or launch other malicious activities.
Can Trojans Steal Passwords?
Yes, Trojans, like Msedgewebview2.exe, can steal passwords. These malicious programs are designed to gain access to a user's computer, spy on victims and steal sensitive information such as banking details and passwords.
Can Msedgewebview2.exe Trojan Hide Itself?
Yes, it can. A Trojan can use various techniques to mask itself, including rootkits, encryption, and obfuscation, to hide from security scanners and evade detection.
Can a Trojan be Removed by Factory Reset?
Yes, a Trojan can be removed by factory resetting your device. This is because it will restore the device to its original state, eliminating any malicious software that may have been installed. Bear in mind that there are more sophisticated Trojans that leave backdoors and reinfect even after a factory reset.
Can Msedgewebview2.exe Trojan Infect WiFi?
Yes, it is possible for a Trojan to infect WiFi networks. When a user connects to the infected network, the Trojan can spread to other connected devices and can access sensitive information on the network.
Can Trojans Be Deleted?
Yes, Trojans can be deleted. This is typically done by running a powerful anti-virus or anti-malware program that is designed to detect and remove malicious files. In some cases, manual deletion of the Trojan may also be necessary.
Can Trojans Steal Files?
Yes, Trojans can steal files if they are installed on a computer. This is done by allowing the malware author or user to gain access to the computer and then steal the files stored on it.
Which Anti-Malware Can Remove Trojans?
Anti-malware programs such as SpyHunter are capable of scanning for and removing Trojans from your computer. It is important to keep your anti-malware up to date and regularly scan your system for any malicious software.
Can Trojans Infect USB?
Yes, Trojans can infect USB devices. USB Trojans typically spread through malicious files downloaded from the internet or shared via email, allowing the hacker to gain access to a user's confidential data.
About the Msedgewebview2.exe Research
The content we publish on SensorsTechForum.com, this Msedgewebview2.exe how-to removal guide included, is the outcome of extensive research, hard work and our team’s devotion to help you remove the specific trojan problem.
How did we conduct the research on Msedgewebview2.exe?
Please note that our research is based on an independent investigation. We are in contact with independent security researchers, thanks to which we receive daily updates on the latest malware definitions, including the various types of trojans (backdoor, downloader, infostealer, ransom, etc.)
Furthermore, the research behind the Msedgewebview2.exe threat is backed with VirusTotal.
To better understand the threat posed by trojans, please refer to the following articles which provide knowledgeable details.


