Security researchers at Elastic Security Labs have released an in-depth analysis of a long-running Linux malware campaign known as Outlaw. Despite its unsophisticated code and crude attack methods, Outlaw remains remarkably persistent. This malware is a great example of how basic tactics, when combined with clever automation, can power a global botnet operation.
Outlaw Malware: A Persistent Threat Hiding in Plain Sight
First observed several years ago, the Outlaw malware campaign has continued to evolve while relying on brute-force and coinmining tactics to propagate. It targets Linux servers by scanning for weak SSH credentials, infecting them, and then using those systems to spread further.
Unlike advanced malware, Outlaw does not use stealthy evasion techniques. Instead, it succeeds by being simple, adaptable, and automated. Researchers observed it using modified open-source tools like XMRig for crypto mining and IRC ShellBots for command and control, without much effort to hide its activities.
How Outlaw Infects and Expands
Step 1: Initial Access via SSH Brute-Forcing
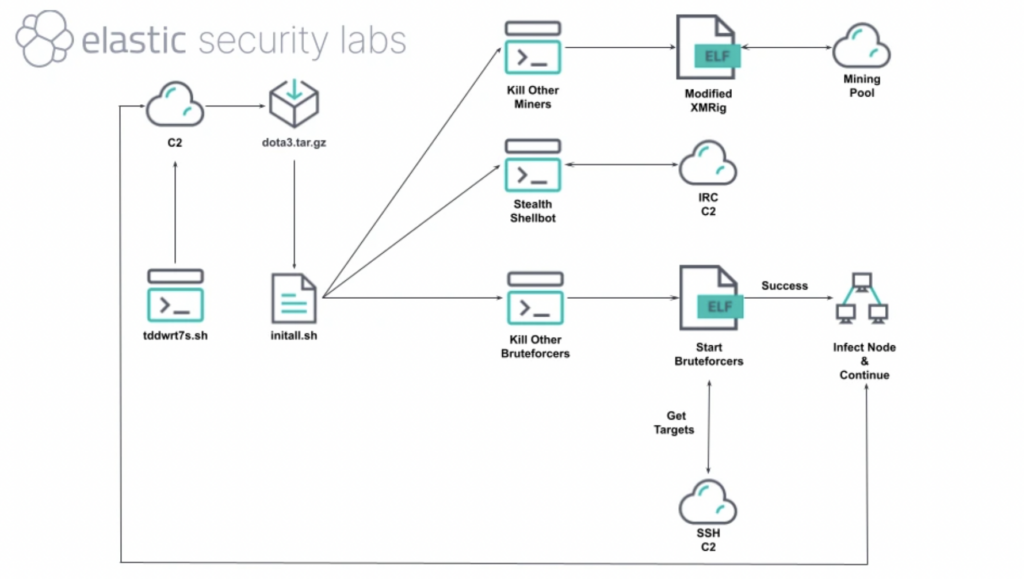
The malware gains entry through high-volume brute-force attacks using its built-in module, blitz. It pulls target IPs from its command-and-control servers and attempts to log in using common or default credentials. Once access is gained, the malware installs itself and initiates the infection cycle.
Step 2: Payload Deployment and Cron-Based Persistence
Outlaw downloads a tarball file containing multiple payloads and executes an initialization script (`initall.sh`). The script sets up hidden directories (like ~/.configrc6) to store malicious binaries, and installs multiple cron jobs to restart its components regularly and on reboot.
Step 3: Mining and Remote Control
The malware installs a customized version of XMRig to mine cryptocurrency using the infected server’s resources. It also connects to IRC-based C2 channels to receive remote commands via ShellBot variants.
Step 4: Worm-Like Propagation
Infected servers are then used to scan local subnets and external IPs, repeating the SSH brute-force attack pattern. This enables the malware to grow its botnet in a worm-like manner with little manual effort from its operators.
What Makes Outlaw So Effective?
Outlaw’s effectiveness lies in a combination of factors that, while unsophisticated, are surprisingly powerful. Its simplicity is key, as it relies on well-known, reliable attack methods without the need for zero-day exploits or privilege escalation techniques. Once deployed, it thrives through automation, operating with little to no human intervention as it spreads and maintains itself.
The malware also demonstrates strong resilience, using cron jobs and built-in kill-switch logic to restart if terminated and even remove other malware that might compete for system resources. Perhaps most notably, Outlaw exhibits a broad attack surface, touching nearly every stage of the MITRE ATT&CK framework. This presents both a challenge for defenders and an opportunity for threat hunters to identify its activity across multiple vectors.
Human Involvement Behind the Malware
Elastic’s honeypot research revealed signs of real-time human interaction. Operators were seen typing commands manually, correcting typos, and modifying script behavior on-the-fly—evidence that even simple botnets like Outlaw may be managed by live threat actors with evolving tactics.
Why This Malware Matters
Outlaw isn’t flashy. It doesn’t use zero-days or advanced exploits. But its long life and operational success prove that basic tactics, if well-executed and automated, can be a real threat especially to poorly secured Linux systems.
This malware’s silent evolution is a wake-up call for system administrators: don’t underestimate low-complexity threats. Poor password hygiene and a lack of system monitoring can open the door to threats like Outlaw that quietly hijack resources and linger undetected.
Defensive Recommendations against Outlaw
- Use strong, unique SSH credentials and disable password authentication where possible.
- Monitor for unexpected cron jobs or hidden directories like
~/.configrc6. - Scan systems for known variants of XMRig or ShellBot malware.
- Segment network traffic and restrict outbound IRC and mining pool communications.
Conclusion
The Outlaw Linux malware is a powerful reminder that cybercrime doesn’t always require sophisticated tools. Sometimes, persistence, automation, and widespread scanning are all a threat actor needs. Organizations relying on Linux infrastructure should take steps now to harden systems and monitor for indicators of compromise. Simply because simple threats like Outlaw are often the hardest to detect… Until it’s too late.


