A newly discovered malware has captured the interest of both security experts and computer hackers. It is called the Ovidiy Stealer and it is being sold on underground hacker markets for a price as low as 7 US Dollars. It is of Russian origin and even includes several advanced features. Continue reading to learn more about it.
Russian Ovidiy Stealer Spotted on Hacker Marketplaces
Computer security researchers recently discovered a new malware threat that is rapidly growing in popularity. It is called Ovidiy Stealer and appears to be of Russian origin. It is primarily distributed on the Russian-speaking underground hacker communities for a fee. The malware is associated with one of the lowest prices – reports indicate that some of the builds are sold for 450 Rubles which is the equivalent of 7 US dollars. Depending on the configuration the provided Ovidiy Stealer may also feature stealth protection features that prevent detection by certain anti-virus products. Once the malware has infiltrated a local or company network it can propagate across the accessible devices.
Similar threats are frequently being developed and used by individual hackers and criminal collectives to launch attacks using infected hosts, botnets and other sources. The fact that the Ovidiy stealer is being distributed on Russian forums does not mean that the majority of the attacks are originating from that country. One of the largest hacker underground communities and exchanges use Russian and we assume that hackers from all over the world are going to take advantage of the malicious code.
The Ovidiy Stealer was found on to be on sale on a Russian domain that has since been shutdown. The paying customers of the malware had the ability to access a web panel that provides an easy-to-use graphical interface for managing the infected hosts. Some of the notable features include the following options:
- Template-based Web Panel – The developers of the Ovidiy Stealer have incorporated a web panel configuration module that resembles those of Spora and other famous ransomware families.
- Detailed Log Files Collection – The malware controllers are able to view a detailed list of all collected log files originating from the compromised hosts.
- Additional Modules Purchase – The developers of the tool allow their customers to pay for additional modules and features using a well-developed payment system. It uses a service called “RoboKassa” that supports payment card transactions and other services. The seller name is listed as “Ovidiy” without disclosing any further information revealing the identity of the creator(s).
- Ongoing Development – The developers behind the malware regularly post statistics and information about future updates to showcase that paying for the threat can be attributed as a type of investment.
- Comments System – A functional comments and feedback system is implemented that allows customers of the Ovidiy Stealer to share their feedback about the system.
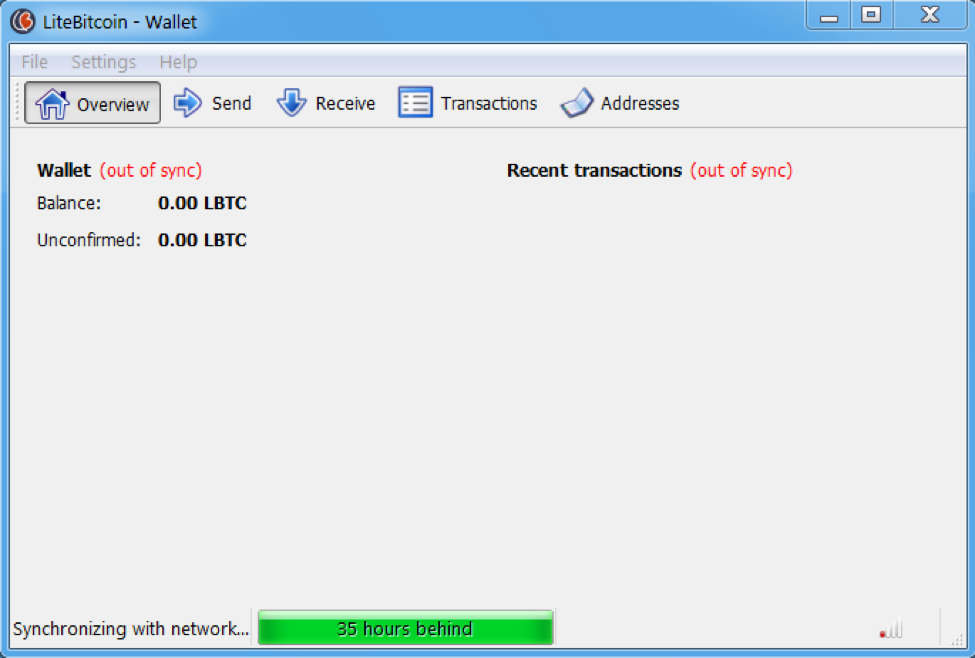
Ovidiy Stealer Poses as a Litecoin Wallet
Ready-made Ovidiy Stealer malware strains have been associated with some of the most widely used spread tactics. The hackers who have purchased the malware kit utilize different methods in order to infect the intended targets. The reported malware instances were identified as being distributed using the following means:
- E-mail Spam Campaigns – The criminals can utilize social engineering tricks to confuse the computer users into infecting themselves. This is done by attaching malicious files or linking them in the body contents.
- Hosted on Download Sites and P2P Sites – Infected payloads and Ovidiy Stealer malware instances are usually found on hacker-controlled download portals. The malware is also frequently uploaded to P2P networks like BitTorrent where pirate content is found.
- Infected Payloads – Ovidiy Stealer malware can be bundled in office documents and software installers. The criminals frequently modify legitimate installers that include the malware in themselves. Depending on the configuration the users may disable the infection by unchecking a checklist or clicking “I disagree” in a notification message.
One of the reasons why the ongoing attacks are considered very dangerous is the fact that Ovidiy Stealer has infected many computer users through a compromised LiteBitcoin wallet software. The app poses as a legitimate application that is used to hold and protect digital currencies. The security researchers discovered that one of the popular mechanisms is the use of archives – the collected samples showcase a “litebitcoin-qt.zip” file. This is probably used to reflect a QT-based version of the application.
Other detected instances include the following infected software bundles:
HideMiner.zip, VkHackTool.zip (a fake hacking tool that allegedly suppports the VKontakte social network), WORLD OF TANKS 2017.txt.exe (installer for the popular “World of Tanks” games),
dice_bot.exe, cheat v5.4.3 2017.exe and Vk.com BulliTl.exe.
Ovidiy Stealer Mechanism of Infection
Several version of the Ovidiy Stealer have been identified, presumably all of them are based on the same engine and code. It is possible that only slight modifications of the original source have produced numerous variants. The malware itself is written using the .NET framework which makes it compatible with all contemporary versions of Microsoft Windows.
The malware follows a preconfigured behavior pattern as directed by the different hackers and collectives. The initial security analysis shows that all captured samples associated with the threat use follow typical browser hijacker commands.
Ovidiy Stealer affects the most commonly Internet-related applications: Opera, the Filezilla FTP client, Google Chrome, Opera and etc. As the is based on a modular approach the hackers can buy additional modules to the malware engine to add support for further programs. The Ovidiy Stealer malware can change essential settings on the installed clients and services as well as steal the stored account credentials, form data, history, bookmarks and monitor all user interaction.
The Ovidiy Stealer engine automatically reports the infected hosts to a hacker-controlled command and control (C&C) server. The researchers reported that this is followed by a data session that sends important information about the infected computers. The malware engine includes a powerful information gathering function that relays the following data to the hackers:
- Compromised Applications – All infected applications and compromised utilities, as well as committed changes are reported to the hackers. The data allows the remote criminals to have an overview of the victims and their usage of different programs.
- Harvested Data – Ovidiy Stealer can extract and forward all saved form data on the compromised machines as instructed. This may include sensitive account credentials and passwords. Using this function the hacker operators are able to conduct identity theft crimes.
- System Data – Comprehensive hardware information is extracted from the infected victims. The collected data can be used by the hackers to generate statistics on the most vulnerable hosts and it helps them to coordinate further attacks.
Each compromised computer is assigned a unique infection ID that is calculated using the values collected during the hardware scan. The analysis of the captured samples showcase some signs of usage of open-source tools namely the LitehTTP bot that can be used to initiate control of the infected hosts. If any application credentials are found from the affected applications a network session is initiated that reports the sensitive information to the remote hacker-controlled servers.
Has your system been infected by malware such as Ovidiy? Check now.
Spy Hunter scanner will only detect the threat. If you want the threat to be automatically removed, you need to purchase the full version of the anti-malware tool.Find Out More About SpyHunter Anti-Malware Tool / How to Uninstall SpyHunter



