8,800 Command and Control Servers Discovered in ASEAN, Interpol Says
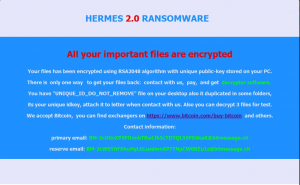
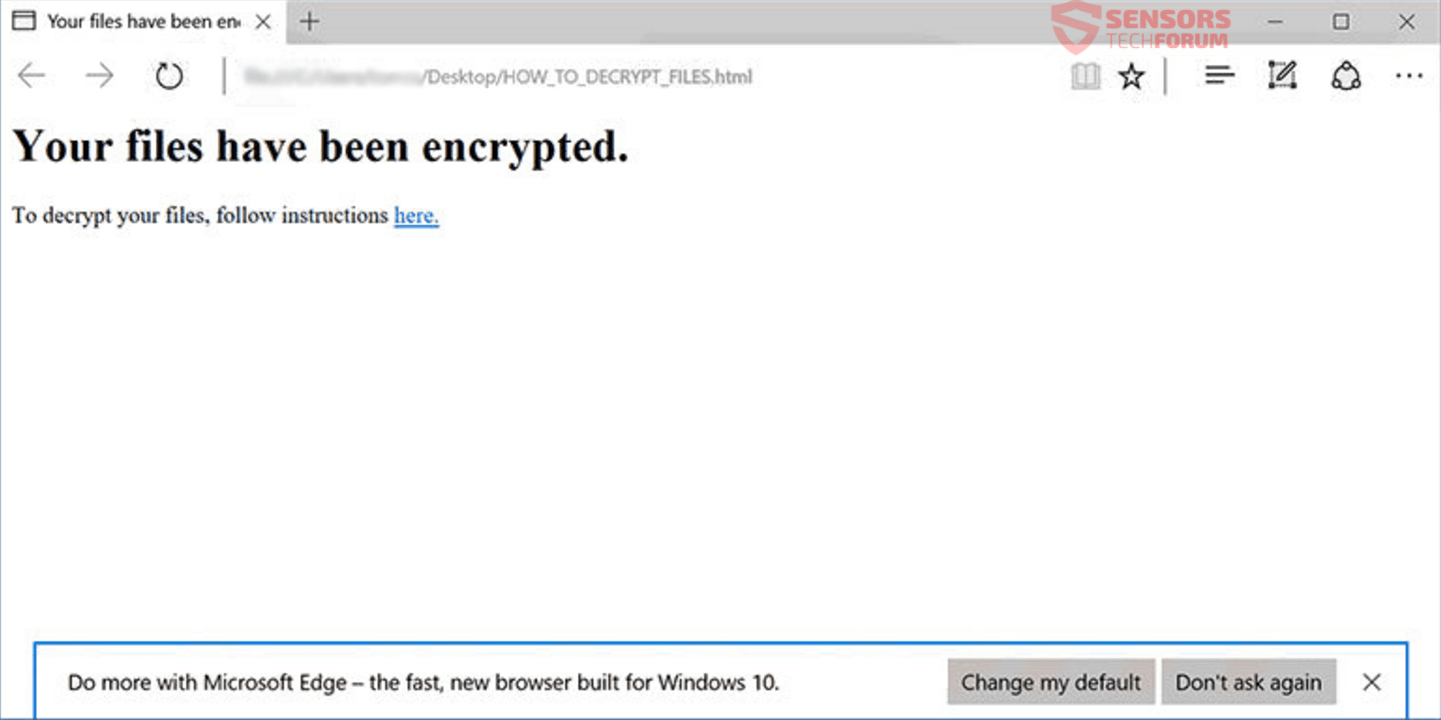
According to the Interpol, thousands of compromised systems have been uncovered in ASEAN (Association of Southeast Asian Nations. The systems included Command and Control servers that were infected with malware. An Interpol-led operation targeting cybercrime across the ASEAN region has…