What Is Proxy Virus Process [Windows]
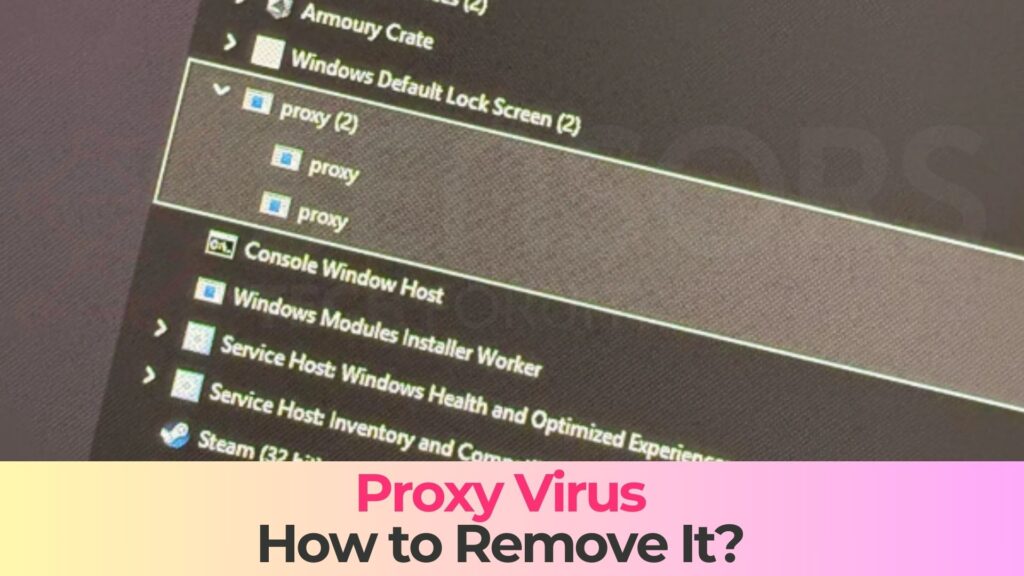
If you have noticed a suspicious process named proxy.exe running in Windows Task Manager and consuming system resources, you should read this article to find out what it really is, how it may have entered your system, and why it represents a serious security risk. The Proxy Virus Process [Windows] is not a legitimate system component and is commonly associated with trojanized applications, malicious loaders, or covert proxy malware used by cybercriminals to abuse infected machines.
The term “Proxy Virus” is used to describe a malicious process that masquerades as a legitimate proxy-related executable while performing hidden operations in the background. In many documented cases, the proxy.exe virus is part of a larger malware infection chain that enables attackers to route traffic through the victim’s device, harvest sensitive information, or establish persistent remote access.
Because proxy.exe may appear generic and technically plausible, many users overlook it, assuming it belongs to legitimate software. This false sense of trust is exactly what attackers rely on. Once active, the Proxy Virus Process can undermine system security, privacy, and network integrity without obvious symptoms.
Proxy Virus Details
| Type | Trojan, Malware, Backdoor |
| Removal Time | Around 5 Minutes |
| Removal Tool |
See If Your System Has Been Affected by malware
Download
Malware Removal Tool
|
How Did I Get Proxy Virus Process [Windows]
The Proxy Virus Process [Windows] typically infiltrates systems through deceptive and indirect distribution methods. Unlike traditional viruses that rely on visible user interaction, this threat often arrives bundled with other software or delivered silently through exploit-based attacks.
Common infection vectors associated with proxy.exe malware include:
- Bundled installers from freeware or pirated software packages
- Cracked applications and illegal license activators
- Malicious attachment email files disguised as invoices or documents
- Fake software updates or bogus system optimization tools
- Exploit kits targeting unpatched Windows vulnerabilities
Once the user executes the trojanized installer or opens a malicious file, the Proxy Virus Process may be dropped into system directories and configured to launch automatically. In many cases, the malware uses misleading file names and metadata to blend in with legitimate Windows services.
Another common scenario involves drive-by downloads, where visiting a compromised or malicious website triggers the download and execution of proxy.exe without explicit user consent. Systems lacking updated security patches or real-time protection are especially vulnerable to this method.
What Does Proxy Virus Process [Windows] Do
After successful infiltration, the Proxy Virus Process begins executing its malicious payload. Its primary purpose is to transform the infected Windows system into a controllable proxy node that attackers can exploit for a wide range of cybercriminal activities.
One of the core behaviors of proxy.exe malware is traffic hijacking. The process may intercept, redirect, or reroute network traffic through the infected machine, effectively turning it into a relay for anonymous browsing, spam campaigns, or illegal operations. This not only compromises privacy but may also expose the victim to legal and reputational risks.
Additional malicious activities commonly associated with the Proxy Virus Process include:
- Establishing persistent communication with remote C&C server infrastructure
- Collecting IP address, geolocation, and system fingerprint data
- Injecting malicious scripts into browser sessions
- Downloading and executing secondary malware components
- Disabling security software and Windows defenses
In advanced variants, proxy.exe may function as a backdoor trojan, allowing attackers to execute commands remotely, modify system settings, or deploy additional payloads such as spyware, ransomware, or cryptominers. This modular behavior makes the threat especially dangerous, as its impact can escalate over time.
From a performance standpoint, infected systems often exhibit symptoms such as slow internet connectivity, unexplained CPU or RAM spikes, frequent application crashes, and abnormal network activity even when the system is idle. These issues stem from the malware’s continuous background operations and unauthorized data transmission.
How to Remove Proxy Virus Process [Windows]
Removing the Proxy Virus Process [Windows] requires careful attention, as the malware may employ persistence mechanisms designed to resist manual removal. Simply ending the proxy.exe process in Task Manager is usually ineffective, since the malicious executable may restart automatically through registry key entries, scheduled tasks, or startup services.
The Proxy Virus Process may embed itself deep within the operating system by modifying critical Windows components. This includes adding registry keys for automatic execution, altering firewall rules, and installing hidden files in system directories. In some cases, it may also inject code into legitimate processes to evade detection.
Because of these advanced techniques, improper removal attempts can leave remnants behind, allowing the malware to regenerate or continue operating covertly. Additionally, incomplete cleanup may expose the system to reinfection or leave security vulnerabilities unaddressed.
A comprehensive removal approach focuses on identifying all malicious components associated with proxy.exe, restoring compromised system settings, and ensuring that no backdoors or secondary payloads remain active. This process should be followed by a full system security audit to verify system integrity.
What should you do?
If you believe your Windows system has been affected by the Proxy Virus Process, you should act immediately. Leaving proxy.exe active allows attackers to exploit your device, compromise your personal data, and misuse your network connection for malicious purposes.
We strongly recommend following the removal guide below to eliminate the Proxy Virus Process completely and secure your system against future threats. Taking prompt action will help restore system performance, protect your privacy, and prevent further damage caused by this dangerous malware.
Preparation before removing Proxy Virus.
Before starting the actual removal process, we recommend that you do the following preparation steps.
- Make sure you have these instructions always open and in front of your eyes.
- Do a backup of all of your files, even if they could be damaged. You should back up your data with a cloud backup solution and insure your files against any type of loss, even from the most severe threats.
- Be patient as this could take a while.
- Scan for Malware
- Fix Registries
- Remove Virus Files
Step 1: Scan for Proxy Virus with SpyHunter Anti-Malware Tool



Step 2: Clean any registries, created by Proxy Virus on your computer.
The usually targeted registries of Windows machines are the following:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
You can access them by opening the Windows registry editor and deleting any values, created by Proxy Virus there. This can happen by following the steps underneath:


 Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.Step 3: Find virus files created by Proxy Virus on your PC.
1.For Windows 8, 8.1 and 10.
For Newer Windows Operating Systems
1: On your keyboard press + R and write explorer.exe in the Run text box and then click on the Ok button.

2: Click on your PC from the quick access bar. This is usually an icon with a monitor and its name is either “My Computer”, “My PC” or “This PC” or whatever you have named it.

3: Navigate to the search box in the top-right of your PC's screen and type “fileextension:” and after which type the file extension. If you are looking for malicious executables, an example may be "fileextension:exe". After doing that, leave a space and type the file name you believe the malware has created. Here is how it may appear if your file has been found:

N.B. We recommend to wait for the green loading bar in the navigation box to fill up in case the PC is looking for the file and hasn't found it yet.
2.For Windows XP, Vista, and 7.
For Older Windows Operating Systems
In older Windows OS's the conventional approach should be the effective one:
1: Click on the Start Menu icon (usually on your bottom-left) and then choose the Search preference.

2: After the search window appears, choose More Advanced Options from the search assistant box. Another way is by clicking on All Files and Folders.

3: After that type the name of the file you are looking for and click on the Search button. This might take some time after which results will appear. If you have found the malicious file, you may copy or open its location by right-clicking on it.
Now you should be able to discover any file on Windows as long as it is on your hard drive and is not concealed via special software.
Proxy Virus FAQ
What Does Proxy Virus Trojan Do?
The Proxy Virus Trojan is a malicious computer program designed to disrupt, damage, or gain unauthorized access to a computer system. It can be used to steal sensitive data, gain control over a system, or launch other malicious activities.
Can Trojans Steal Passwords?
Yes, Trojans, like Proxy Virus, can steal passwords. These malicious programs are designed to gain access to a user's computer, spy on victims and steal sensitive information such as banking details and passwords.
Can Proxy Virus Trojan Hide Itself?
Yes, it can. A Trojan can use various techniques to mask itself, including rootkits, encryption, and obfuscation, to hide from security scanners and evade detection.
Can a Trojan be Removed by Factory Reset?
Yes, a Trojan can be removed by factory resetting your device. This is because it will restore the device to its original state, eliminating any malicious software that may have been installed. Bear in mind that there are more sophisticated Trojans that leave backdoors and reinfect even after a factory reset.
Can Proxy Virus Trojan Infect WiFi?
Yes, it is possible for a Trojan to infect WiFi networks. When a user connects to the infected network, the Trojan can spread to other connected devices and can access sensitive information on the network.
Can Trojans Be Deleted?
Yes, Trojans can be deleted. This is typically done by running a powerful anti-virus or anti-malware program that is designed to detect and remove malicious files. In some cases, manual deletion of the Trojan may also be necessary.
Can Trojans Steal Files?
Yes, Trojans can steal files if they are installed on a computer. This is done by allowing the malware author or user to gain access to the computer and then steal the files stored on it.
Which Anti-Malware Can Remove Trojans?
Anti-malware programs such as SpyHunter are capable of scanning for and removing Trojans from your computer. It is important to keep your anti-malware up to date and regularly scan your system for any malicious software.
Can Trojans Infect USB?
Yes, Trojans can infect USB devices. USB Trojans typically spread through malicious files downloaded from the internet or shared via email, allowing the hacker to gain access to a user's confidential data.
About the Proxy Virus Research
The content we publish on SensorsTechForum.com, this Proxy Virus how-to removal guide included, is the outcome of extensive research, hard work and our team’s devotion to help you remove the specific trojan problem.
How did we conduct the research on Proxy Virus?
Please note that our research is based on an independent investigation. We are in contact with independent security researchers, thanks to which we receive daily updates on the latest malware definitions, including the various types of trojans (backdoor, downloader, infostealer, ransom, etc.)
Furthermore, the research behind the Proxy Virus threat is backed with VirusTotal.
To better understand the threat posed by trojans, please refer to the following articles which provide knowledgeable details.


