 What is Mal/Phish-A on Mac? How to remove Mal/Phish-A redirects? How to remove Mal/Phish-A virus completely from your Mac?
What is Mal/Phish-A on Mac? How to remove Mal/Phish-A redirects? How to remove Mal/Phish-A virus completely from your Mac?
Mal/Phish-A is the name of a virus that affects Mac computers and besides performing a wide range of virus activities, its primary purpose seems to be to display all sorts of phishing web pages, directed at victims. These pages may be the fake login places of Gmail, Facebook, Twitter and other sites and they all aim to extract your user name and password. There may even be PayPal and other fake financial information pages, that may request your financial credentials. This is the main reason why you should read this article and learn how to remove Mal/Phish-A from your Mac.

Threat Summary
| Name | Mal/Phish-A |
| Type | Malware for Mac OS |
| Short Description | Aims to take control over the internet connection of affected users and display phishing pages. |
| Symptoms | The main symptoms are problems with the internet connection and fake web pages begin to appear. |
| Distribution Method | May use malspam or fake apps to enter your Mac. |
| Detection Tool |
See If Your System Has Been Affected by malware
Download
Combo Cleaner
|
User Experience | Join Our Forum to Discuss Mal/Phish-A. |

Mal/Phish-A – How Did I Get It and What Does It Do?
Mal/Phish-A could be spread via multiple different methods, the main ones of which are believed to be via sending e-mails with virus attachements that pretend to be leigitimate documents or even uploading fake apps on download sites, that turn out to be the virus itself.
Either way, when Mal/Phish-A infects your Mac, it may begin to perform the following virus activities:
- Download and run files.
- Obtain your private information.
- Cause browser redirects on Safari, Chrome and Firefox browsers.
- Take screenshots.
- Run a keylogger that aims to log the keystrokes you type on your machine.
You should be aware of fake web pages as they are the main giveaway of an infection with Mal/Phish-A Mac virus. This is because those infections tend to detect if you visit an important site and replace its login page with a fake one. If the following sites ask you to re-sign in, then this is one strong indicator for Mal/Phish-A infection:
- Twitter.
- PayPal.
- Amazon.
- eBay.
- Ray-Ban.
- Gmail.
- Facebook.
- Instagram.
- LinkedIn.
- Your bank.
You should watch for the fake web pages by checking their address bar. If the address bar is not HTTPS (The icon with the green padlock next to the address), then you most likely are not visiting the original version of the site and everything you type in it, including your credit card details could be sent directly to the hackers who are behind Mal/Phish-A.

How to Detect and Remove Mal/Phish-A from Your Mac
If you want Mal/Phish-A gone from your Mac, then we strongly recommend that you follow the instructions underneath. They have been created with the main idea to help you get rid of the virus from your computer effecitvely step by step. If you want to automatically detect and remove Mal/Phish-A from your Mac, then we strongly recommend that you download and run a scan with an advanced malware cleaner software. This software’s main purpose is to automatically detect and remove Mal/Phish-A from your Mac by detecting its files and objects and eliminating them.
Steps to Prepare Before Removal:
Before starting to follow the steps below, be advised that you should first do the following preparations:
- Backup your files in case the worst happens.
- Make sure to have a device with these instructions on standy.
- Arm yourself with patience.
- 1. Scan for Mac Malware
- 2. Uninstall Risky Apps
- 3. Clean Your Browsers
Step 1: Scan for and remove Mal/Phish-A files from your Mac
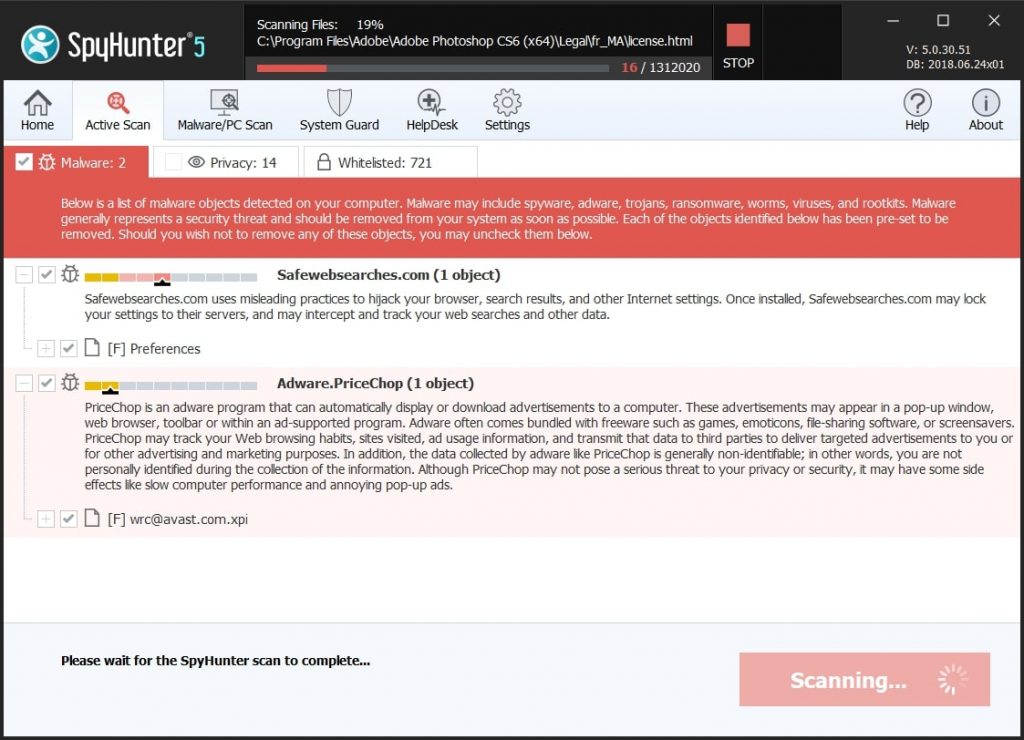
When you are facing problems on your Mac as a result of unwanted scripts and programs such as Mal/Phish-A, the recommended way of eliminating the threat is by using an anti-malware program. SpyHunter for Mac offers advanced security features along with other modules that will improve your Mac’s security and protect it in the future.
Quick and Easy Mac Malware Video Removal Guide
Bonus Step: How to Make Your Mac Run Faster?
Mac machines maintain probably the fastest operating system out there. Still, Macs do become slow and sluggish sometimes. The video guide below examines all of the possible problems that may lead to your Mac being slower than usual as well as all of the steps that can help you to speed up your Mac.
Step 2: Uninstall Mal/Phish-A and remove related files and objects
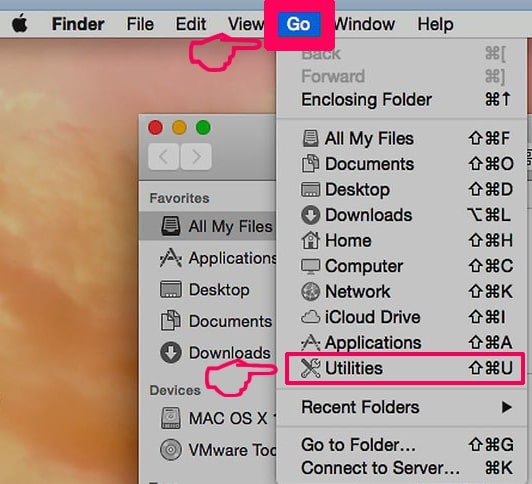
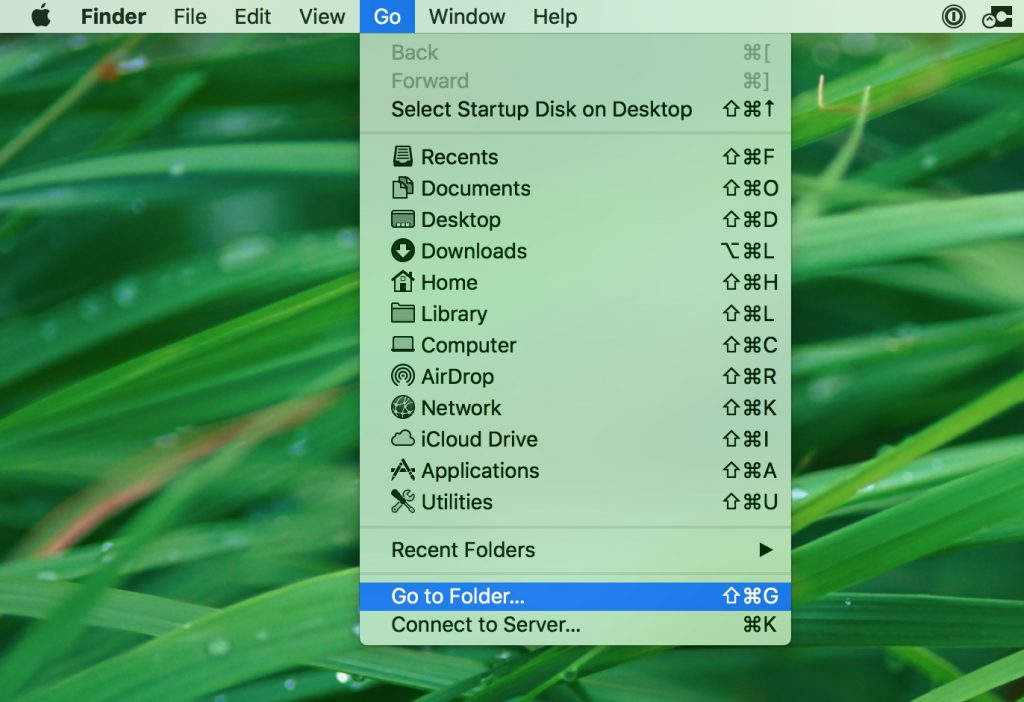
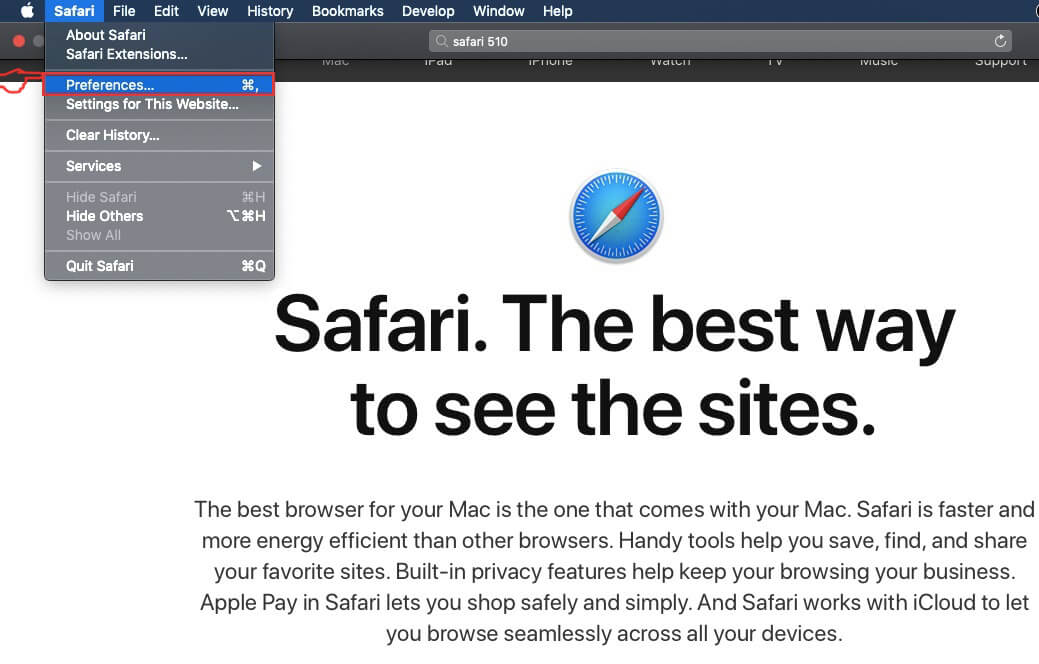
1. Hit the ⇧+⌘+U keys to open Utilities. Another way is to click on “Go” and then click “Utilities”, like the image below shows:
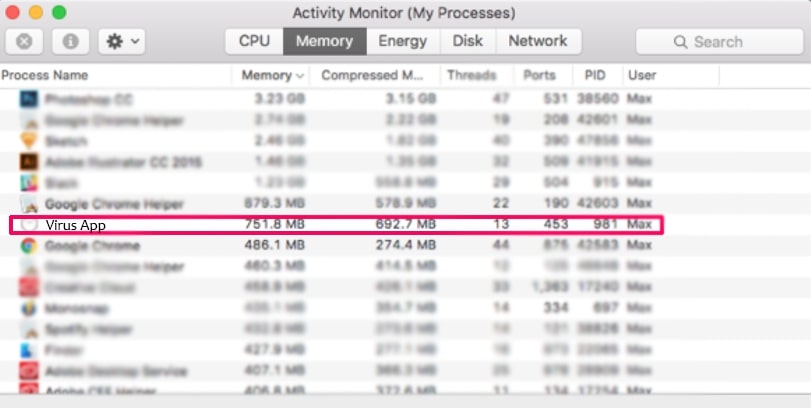
2. Find Activity Monitor and double-click it:

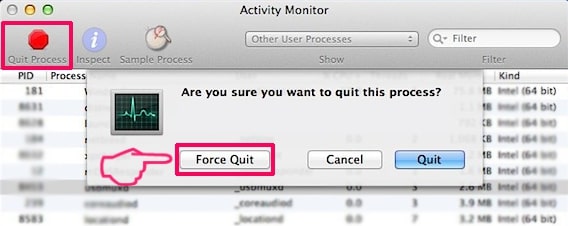
3. In the Activity Monitor look for any suspicious processes, belonging or related to Mal/Phish-A:
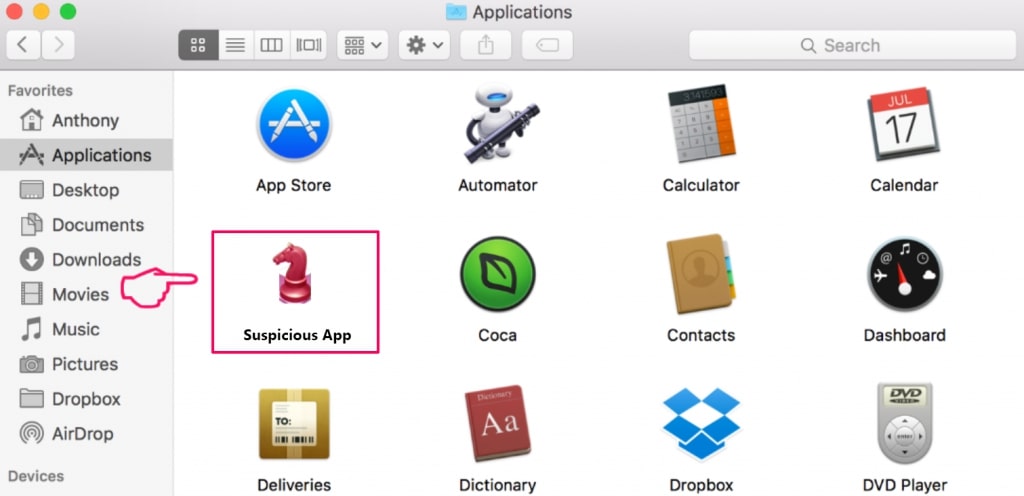
4. Click on the "Go" button again, but this time select Applications. Another way is with the ⇧+⌘+A buttons.
5. In the Applications menu, look for any suspicious app or an app with a name, similar or identical to Mal/Phish-A. If you find it, right-click on the app and select “Move to Trash”.
6. Select Accounts, after which click on the Login Items preference. Your Mac will then show you a list of items that start automatically when you log in. Look for any suspicious apps identical or similar to Mal/Phish-A. Check the app you want to stop from running automatically and then select on the Minus (“-“) icon to hide it.
7. Remove any leftover files that might be related to this threat manually by following the sub-steps below:
- Go to Finder.
- In the search bar type the name of the app that you want to remove.
- Above the search bar change the two drop down menus to “System Files” and “Are Included” so that you can see all of the files associated with the application you want to remove. Bear in mind that some of the files may not be related to the app so be very careful which files you delete.
- If all of the files are related, hold the ⌘+A buttons to select them and then drive them to “Trash”.
In case you cannot remove Mal/Phish-A via Step 1 above:
In case you cannot find the virus files and objects in your Applications or other places we have shown above, you can manually look for them in the Libraries of your Mac. But before doing this, please read the disclaimer below:
1. Click on "Go" and Then "Go to Folder" as shown underneath:
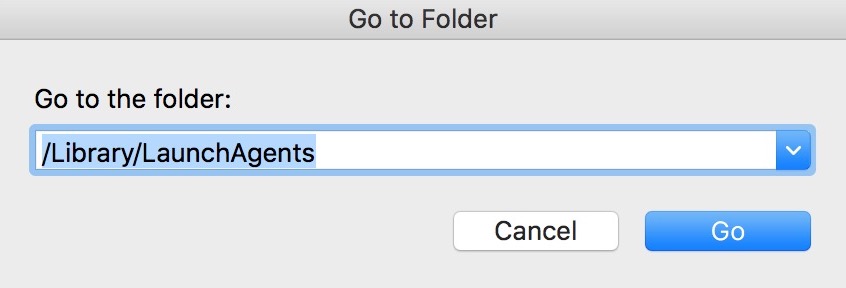
2. Type in "/Library/LauchAgents/" and click Ok:
3. Delete all of the virus files that have similar or the same name as Mal/Phish-A. If you believe there is no such file, do not delete anything.
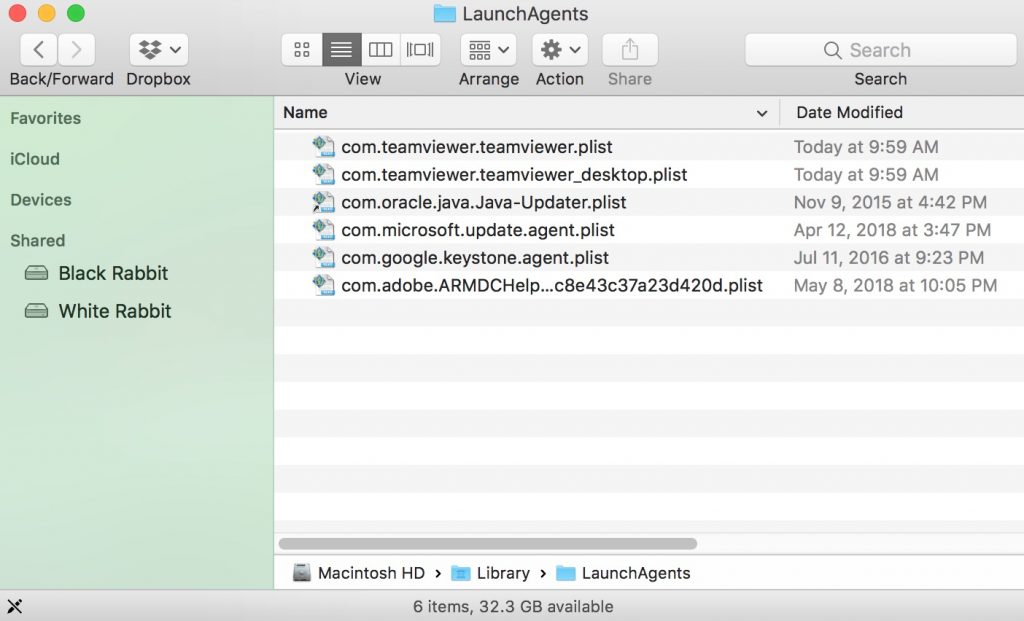
You can repeat the same procedure with the following other Library directories:
→ ~/Library/LaunchAgents
/Library/LaunchDaemons
Tip: ~ is there on purpose, because it leads to more LaunchAgents.
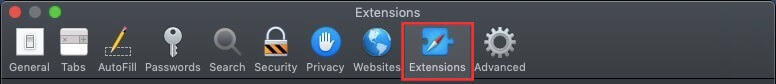
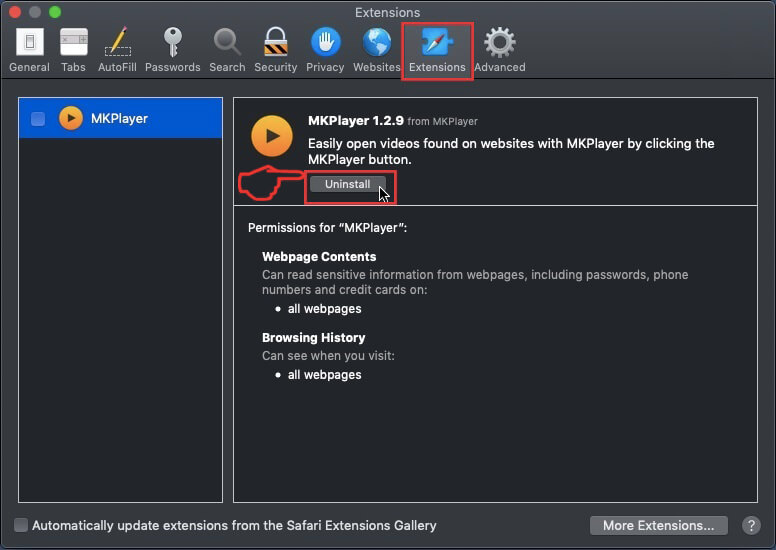
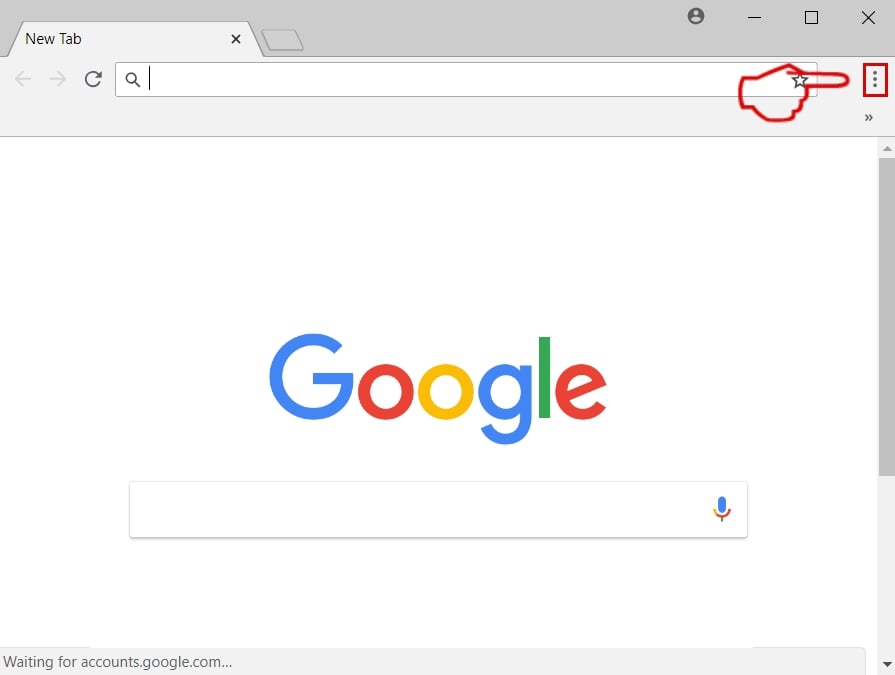
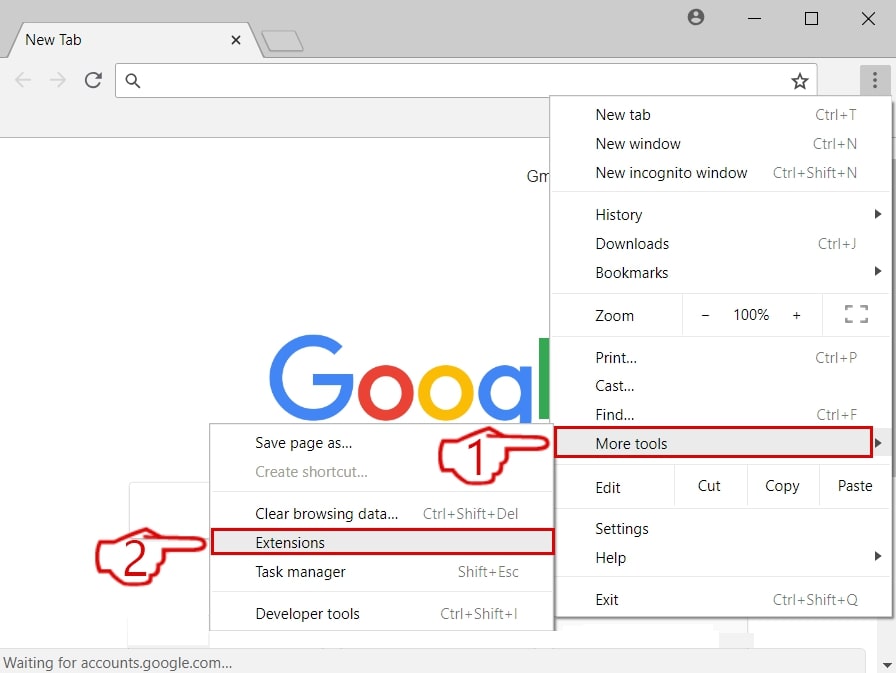
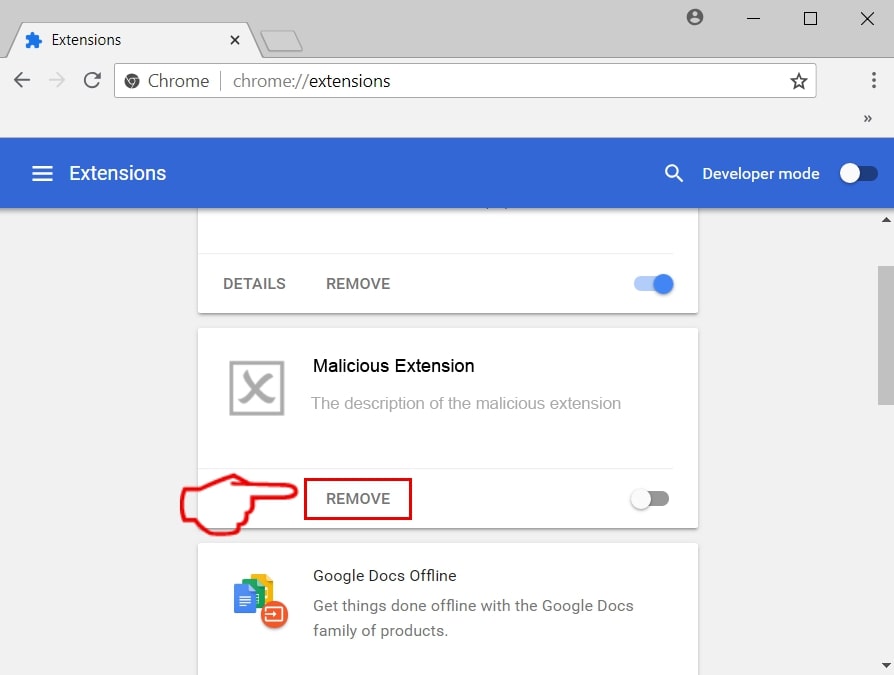
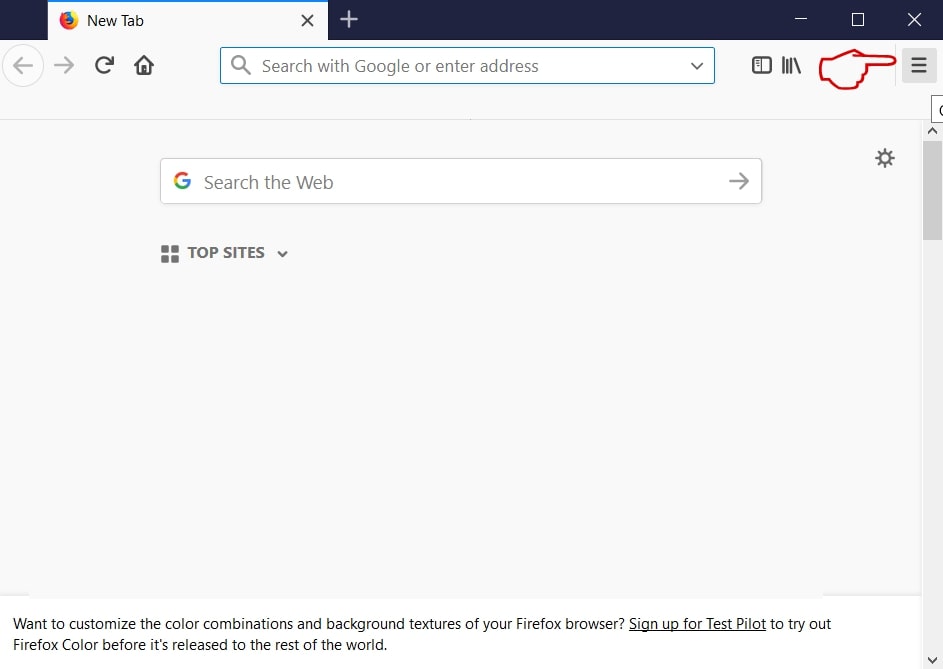
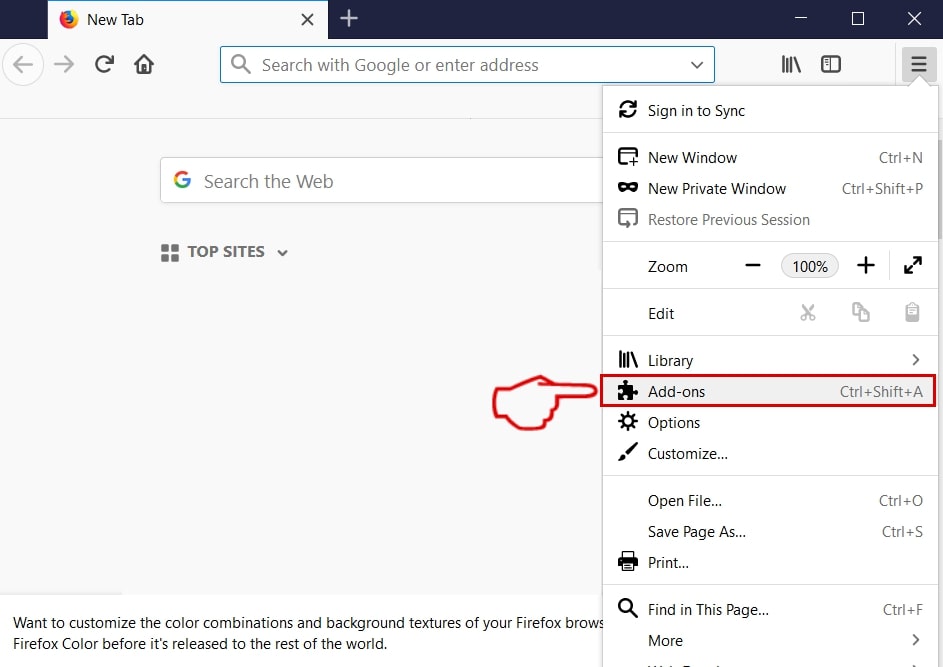
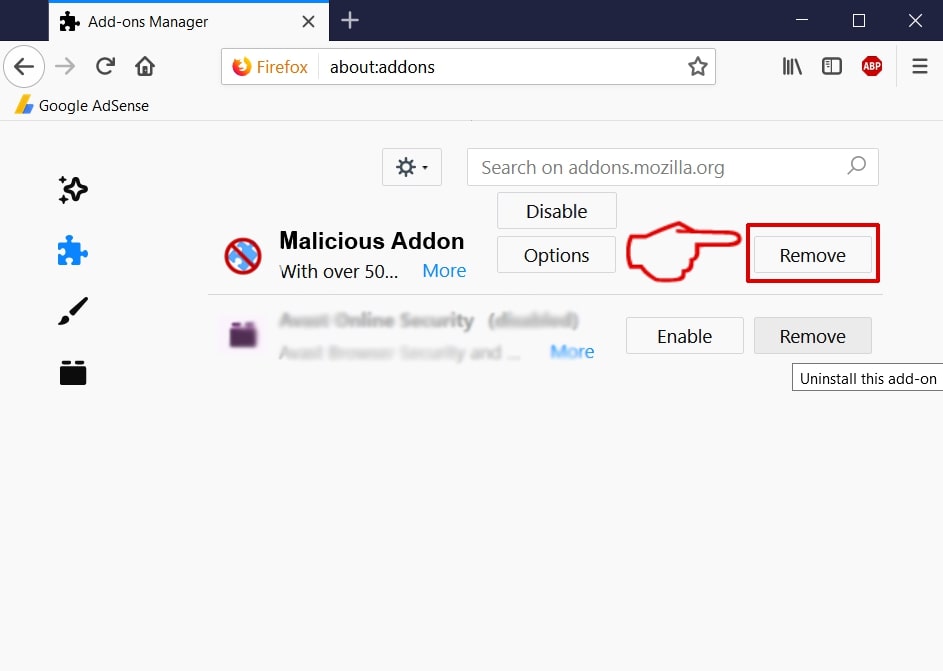
Step 3: Remove Mal/Phish-A – related extensions from Safari / Chrome / Firefox
Mal/Phish-A-FAQ
What is Mal/Phish-A on your Mac?
The Mal/Phish-A threat is probably a potentially unwanted app. There is also a chance it could be related to Mac malware. If so, such apps tend to slow your Mac down significantly and display advertisements. They could also use cookies and other trackers to obtain browsing information from the installed web browsers on your Mac.
Can Macs Get Viruses?
Yes. As much as any other device, Apple computers do get malware. Apple devices may not be a frequent target by malware authors, but rest assured that almost all of the Apple devices can become infected with a threat.
What Types of Mac Threats Are There?
According to most malware researchers and cyber-security experts, the types of threats that can currently infect your Mac can be rogue antivirus programs, adware or hijackers (PUPs), Trojan horses, ransomware and crypto-miner malware.
What To Do If I Have a Mac Virus, Like Mal/Phish-A?
Do not panic! You can easily get rid of most Mac threats by firstly isolating them and then removing them. One recommended way to do that is by using a reputable malware removal software that can take care of the removal automatically for you.
There are many Mac anti-malware apps out there that you can choose from. SpyHunter for Mac is one of the reccomended Mac anti-malware apps, that can scan for free and detect any viruses. This saves time for manual removal that you would otherwise have to do.
How to Secure My Data from Mal/Phish-A?
With few simple actions. First and foremost, it is imperative that you follow these steps:
Step 1: Find a safe computer and connect it to another network, not the one that your Mac was infected in.
Step 2: Change all of your passwords, starting from your e-mail passwords.
Step 3: Enable two-factor authentication for protection of your important accounts.
Step 4: Call your bank to change your credit card details (secret code, etc.) if you have saved your credit card for online shopping or have done online activiites with your card.
Step 5: Make sure to call your ISP (Internet provider or carrier) and ask them to change your IP address.
Step 6: Change your Wi-Fi password.
Step 7: (Optional): Make sure to scan all of the devices connected to your network for viruses and repeat these steps for them if they are affected.
Step 8: Install anti-malware software with real-time protection on every device you have.
Step 9: Try not to download software from sites you know nothing about and stay away from low-reputation websites in general.
If you follow these reccomendations, your network and Apple devices will become significantly more safe against any threats or information invasive software and be virus free and protected in the future too.
More tips you can find on our MacOS Virus section, where you can also ask any questions and comment about your Mac problems.
About the Mal/Phish-A Research
The content we publish on SensorsTechForum.com, this Mal/Phish-A how-to removal guide included, is the outcome of extensive research, hard work and our team’s devotion to help you remove the specific macOS issue.
How did we conduct the research on Mal/Phish-A?
Please note that our research is based on an independent investigation. We are in contact with independent security researchers, thanks to which we receive daily updates on the latest malware definitions, including the various types of Mac threats, especially adware and potentially unwanted apps (PUAs).
Furthermore, the research behind the Mal/Phish-A threat is backed with VirusTotal.
To better understand the threat posed by Mac malware, please refer to the following articles which provide knowledgeable details.


