What Is Shlayer Mac Trojan?
This article has been created in order to give you insight on how to quickly remove the Shlayer Mac Trojan from your Mac effectively.
The Shlayer Mac Trojan is a very dangerous threat to all Mac computers as it can install itself silently and lead to data theft. Active infections can be made without any apparent symptoms and depending on the specific hacker instructions different actions can take place. This is the reason why affected users should remove it immediately.

Shlayer Mac Trojan
| Name | Shlayer Mac Trojan |
| Type | Mac OS Adware |
| Short Description | The Shlayer Mac Trojan installs various malware on the target computers. |
| Symptoms | The victims may not experience any apparent signs of infection. |
| Distribution Method | Emails, infected software installers and other methods. |
| Detection Tool |
See If Your System Has Been Affected by malware
Download
Malware Removal Tool
|
According to the available, information the majority of infections are located in the United States and India. The distribution of the threat has been done via a sophisticated network of sites that include scripts and redirects to the threat. Two distinct strategies have been used:
- Legitimate Site Infections — The hackers have been found to load malicious ads on legitimate sites, as well as various scripts that will deliver the Shlayer Mac Trojan. This is often done by using fake or stolen profiles and posting comments, public and private messages via social networks, chat rooms, forums and other community sites.
- Virus Delivery Web Tactics — The hackers can “push” the Shlayer Mac Trojan by creating numerous fake company, service and product landing pages. They can be hosted on similar sounding domain names to legitimate and well-known sites and can be designed to include rich contents and design. By including self-signed or stolen security certificates and other elements many visitors may not be able to differentiate them from the real and safe domains.
The malvertising campaigns are done by using several sophisticated tactics — they include the insertion of illicit ads onto different platforms. The security analyses which are posted by several vendors shows that infections are also possible by the deployment of browser hijackers. They are dangerous extensions made for the most popular web browsers which are frequently used by desktop users. The dangerous plugins are uploaded both to the official repositories and various hacker-controlled pages, download portals and other places where the users can acquire the infection. To manipulate the prospective victims into downloading them the hijackers the criminals will post elaborate descriptions that promise new feature additions, optimizations and other benefits.
A recent virus campaign statistics of the Mac malware shows that the Shlayer Mac Trojan is responsible for a large part of infections for the past few years. This particular Trojan accounts for about 30% of the total threats for Apple’s operating system according to one of the reports. Ever since the first versions were released in February 2018. Several hacking groups are possibly behind the different attack campaigns which have been against individual users and company networks. This is one of the viruses that have many distinct variants — there are more than 32,000 different configuration types which have been collected so far. All of them are are controlled by special hacker-controlled servers — more than 140 ones have been used for this purpose.
The Trojan engine is capable of mostly running Bash (command line) commands as instructed by the hackers. It can hide itself from some security systems and also deploy other malware across popular types — hijackers, ransomware, common viruses and etc.
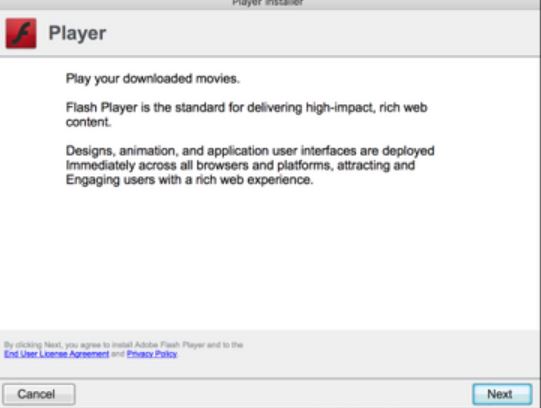
A new update of the Shlayer Mac Trojan has been recently discovered by security updates. The new version of the threat is being spread across the Internet using multiple methods however one of the most frequent ones is an installer or updater for the Adobe Flash Plugin. Links to it and download code are found on hijacker sites, hacked pages and email phishing messages.
It has been confirmed that the new Shlayer Mac Trojan affects all versions from 10.10.5 to 10.14.3. It can be really hard to detect using an anti-virus or anti-malware program as the threats employ multiple layers of obfuscation. The code analysis also reveals that it contains the functionality to detect and bypass active security software.
As soon as the intrusion is started the built-in malware code will start. Depending on the local conditions or hacker-instructions various actions will take place. One of the most common ones is the acessing of sensitive data including personal information about the users. The new version of the Shlayer Mac Trojan will also generate an unique ID for each infected host.
This is followed a privilege escalation which will deliver a secondary payload. This means that the Trojan can be used both to install other threats to the already compromised hosts and also to spy on the victims in real-time. Other names that the malware is also known include the following:
- Trojan.Mac.Shlayer.f
- Trojan.OSX.Shlayer-2
- Trojan Mac Shlayer
- OSX/Shlayer
Shlayer Mac Trojan — How Did I Get It
The Shlayer Mac Trojan is delivered through a complex campaign known as malicious advertising. The security analysis reveals that the detected samples are distributed via advanced malvertising payloads.
In this particular case the culprit is a malicious browser extension which is hosted on hacker-controlled sites. The dangerous code is disguised as an Adobe Flash Player installer. This type of attack behavior can be embedded in several different sources of infection besides the malicious sites:
- Email Messages — The criminals can additionally use phishing tactics that impersonate legitimate companies and services that the users might be using. By falling victim to their body contents or any attached files the fake Adobe Flash Player file will be downloaded and started onto their computers.
- File Sharing Networks — The payload files can be shared on networks like BitTorrent where such programs are frequently uploaded.
- Malicious Documents — The Adobe Flash Player installer can be embedded in documents made by the criminals. All of the popular file formats can be affected: text files, presentations, databases and spreadsheets. The built-in contents can link to the dangerous files. The other technique is the automatic start of the file by inserting the required scripts into them. When the document files are opened a prompt will be launched asking the users to enable them. The reason quoted will be to correctly view the document.
Not only is the Adobe Flash Player install a malicious carrier, but also an image that conceals the steganography malware — the virus code will be started as soon as it is opened in the browser window. As the campaign is deemed very large it is estimated that as many as 5MM visitors may have been targeted with it.
The malvertising campaign will deliver the payload carrier which starts the hidden code leading to the Shlayer Mac Trojan installation.
Following the malicious sites and script redirects the victims can also be directed to several ad campaign landing pages. They will deliver another set of malicious application installers, depending on the campaigns. Some of the examples include the following malware copies:
- Update Flash Now!
- Windows 10 PC Repair
Shlayer Mac Trojan — What Does It Do?
Upon launching the Shlayer Mac Trojan code the first part of the infection will commence — a shell script decrypting a file found in the Application Resources directory. This malicious file is deployed there in order to hide its appearance from common user locations such as their home folder.
This will start a sequence of a several stage delivery Trojan, including the unpacking of a password-protected ZIP archive containing further malware scripts. The Shlayer Mac Trojan at the moment is configured to lead to other infections. However given its complex modular design it can easily be used for other malicious purposes, including the following:
- Information Harvesting — The engine can be used to harvest data that can be configured to extract both machine metrics and user information. The first category is used to generate an unique ID that is assigned to each individual machine. This is done via an algorithm that uses list of installed hardware components, user settings and other operating system metrics. It can also directly expose the identity of the victims by looking out for strings that can reveal their name, address, phone number, location and any stored account credentials.
- System Changes — To facilitate further infections the payload code can make various changes to the compromised machines — configuration files, operating system environment values and user settings.
- Boot Options Modifications — By accessing the Mac OS computers settings the Shlayer Trojan can set itself or the other deployed payloads to automatically start when the computer is powered on.
- Additional Payload Delivery — It can be used to deliver other threats to the computers such as miners and ransomware.
Future updates to the Shlayer Mac Trojan can deploy all kinds of other modules.
Remove Shlayer Mac Trojan
To fully remove all traces and files of the Shlayer trojan, we recommend following the removal instructions below. They represent two approaches – manual and automatic. For maximum efficiency, it is best to combine them. Consider that a full system scan will detect and remove all trojan files and keep your system safe in the future.
Steps to Prepare Before Removal:
Before starting to follow the steps below, be advised that you should first do the following preparations:
- Backup your files in case the worst happens.
- Make sure to have a device with these instructions on standy.
- Arm yourself with patience.
- 1. Scan for Mac Malware
- 2. Uninstall Risky Apps
- 3. Clean Your Browsers
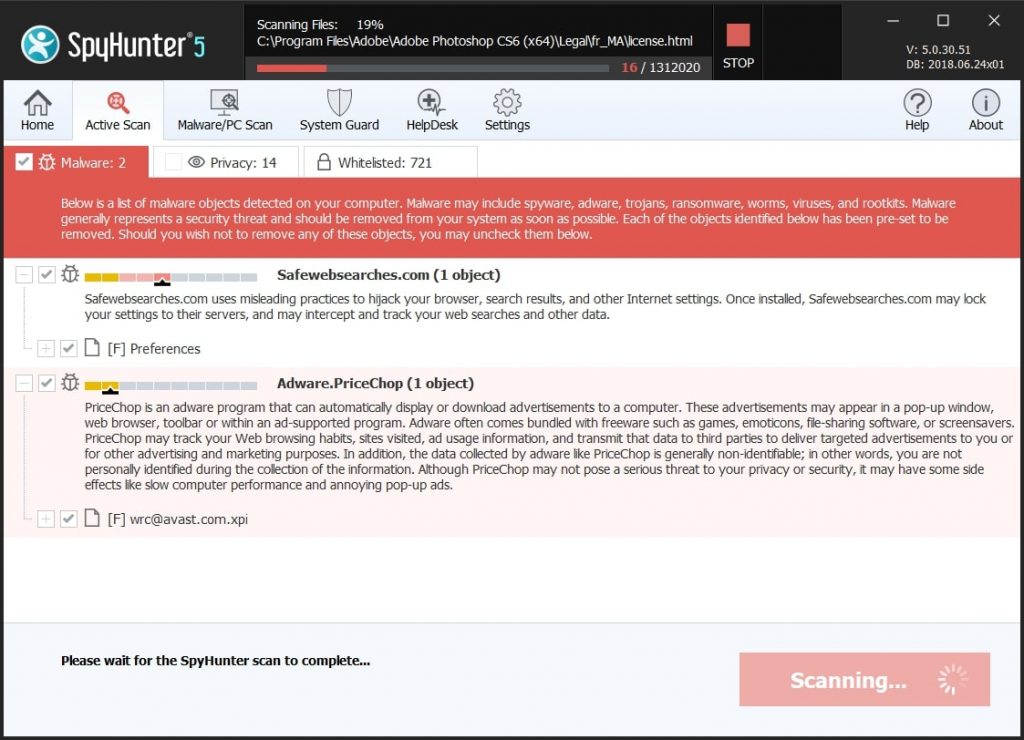
Step 1: Scan for and remove Shlayer Mac Trojan files from your Mac
When you are facing problems on your Mac as a result of unwanted scripts and programs such as Shlayer Mac Trojan, the recommended way of eliminating the threat is by using an anti-malware program. SpyHunter for Mac offers advanced security features along with other modules that will improve your Mac’s security and protect it in the future.
Quick and Easy Mac Malware Video Removal Guide
Bonus Step: How to Make Your Mac Run Faster?
Mac machines maintain probably the fastest operating system out there. Still, Macs do become slow and sluggish sometimes. The video guide below examines all of the possible problems that may lead to your Mac being slower than usual as well as all of the steps that can help you to speed up your Mac.
Step 2: Uninstall Shlayer Mac Trojan and remove related files and objects
1. Hit the ⇧+⌘+U keys to open Utilities. Another way is to click on “Go” and then click “Utilities”, like the image below shows:
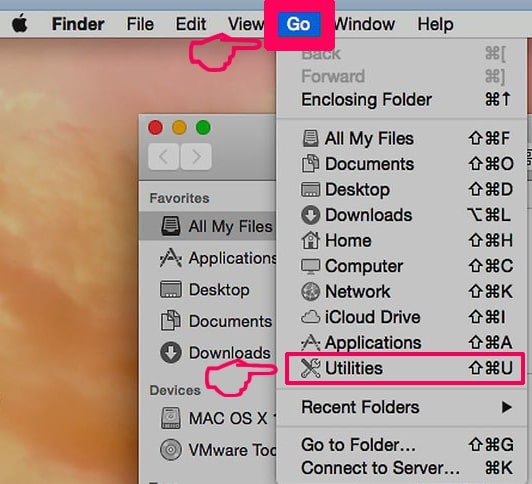
2. Find Activity Monitor and double-click it:

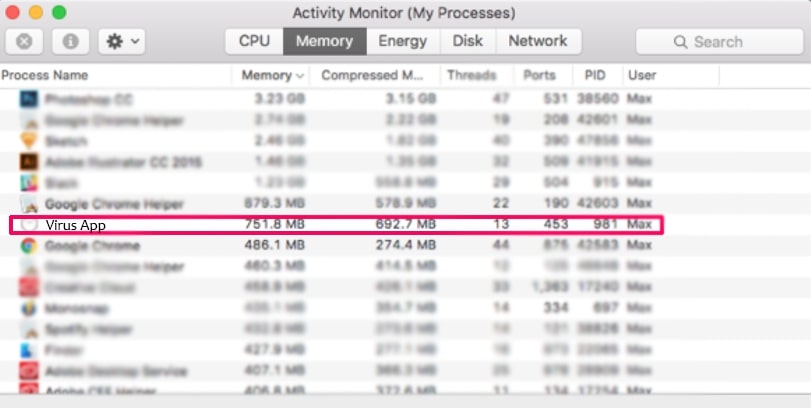
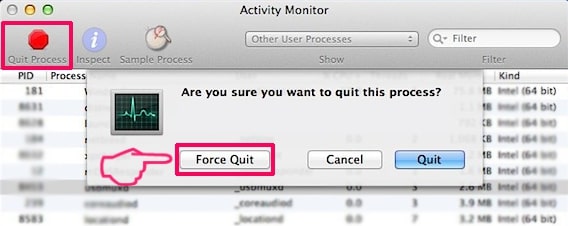
3. In the Activity Monitor look for any suspicious processes, belonging or related to Shlayer Mac Trojan:
4. Click on the "Go" button again, but this time select Applications. Another way is with the ⇧+⌘+A buttons.
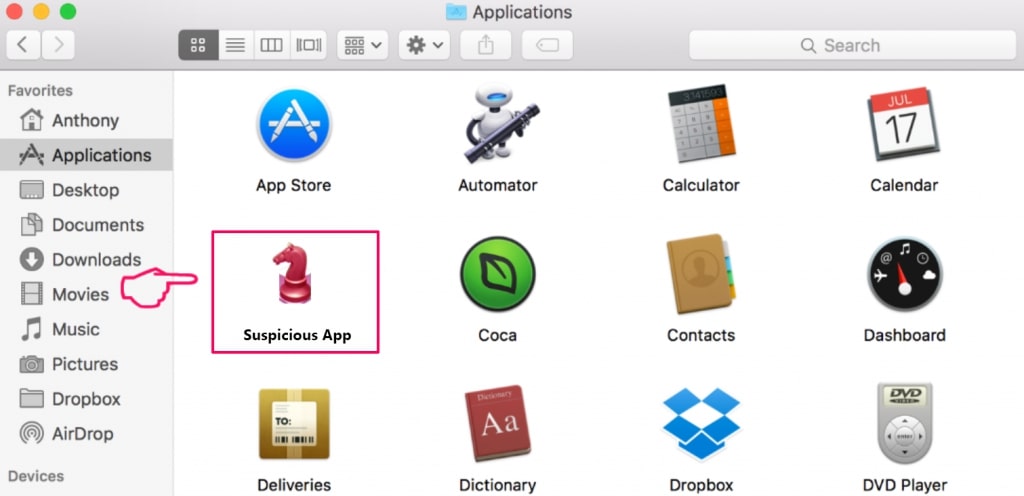
5. In the Applications menu, look for any suspicious app or an app with a name, similar or identical to Shlayer Mac Trojan. If you find it, right-click on the app and select “Move to Trash”.
6. Select Accounts, after which click on the Login Items preference. Your Mac will then show you a list of items that start automatically when you log in. Look for any suspicious apps identical or similar to Shlayer Mac Trojan. Check the app you want to stop from running automatically and then select on the Minus (“-“) icon to hide it.
7. Remove any leftover files that might be related to this threat manually by following the sub-steps below:
- Go to Finder.
- In the search bar type the name of the app that you want to remove.
- Above the search bar change the two drop down menus to “System Files” and “Are Included” so that you can see all of the files associated with the application you want to remove. Bear in mind that some of the files may not be related to the app so be very careful which files you delete.
- If all of the files are related, hold the ⌘+A buttons to select them and then drive them to “Trash”.
In case you cannot remove Shlayer Mac Trojan via Step 1 above:
In case you cannot find the virus files and objects in your Applications or other places we have shown above, you can manually look for them in the Libraries of your Mac. But before doing this, please read the disclaimer below:
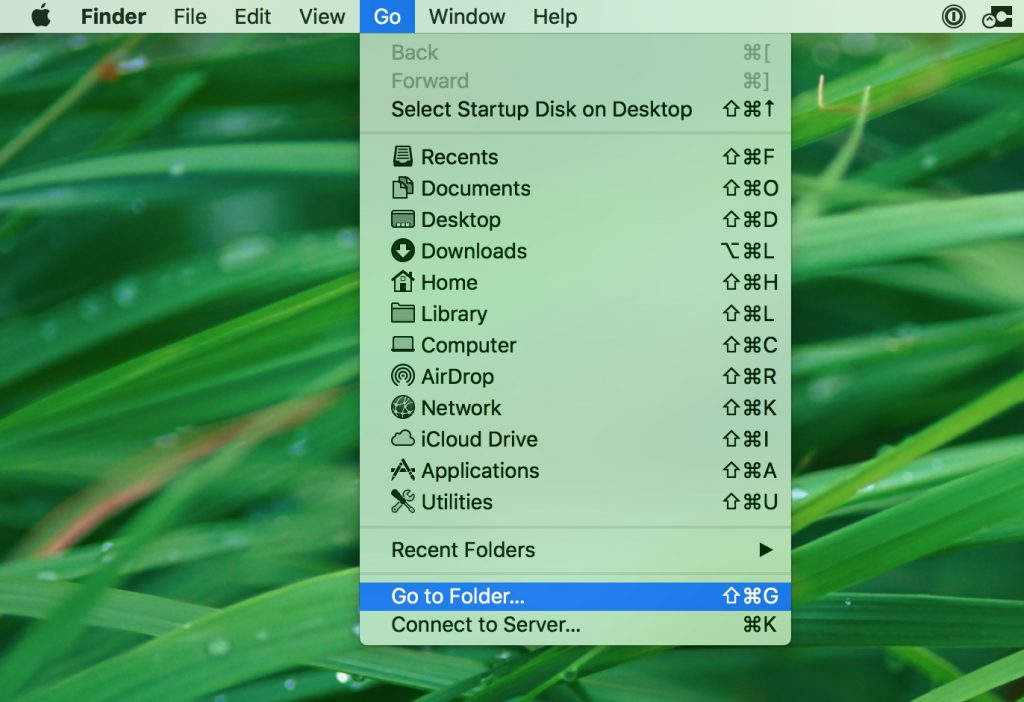
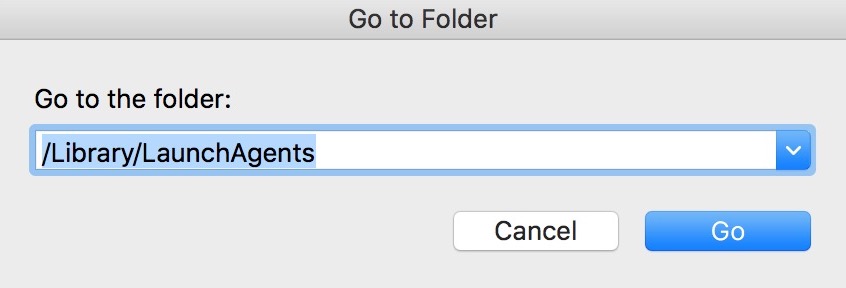
1. Click on "Go" and Then "Go to Folder" as shown underneath:
2. Type in "/Library/LauchAgents/" and click Ok:
3. Delete all of the virus files that have similar or the same name as Shlayer Mac Trojan. If you believe there is no such file, do not delete anything.
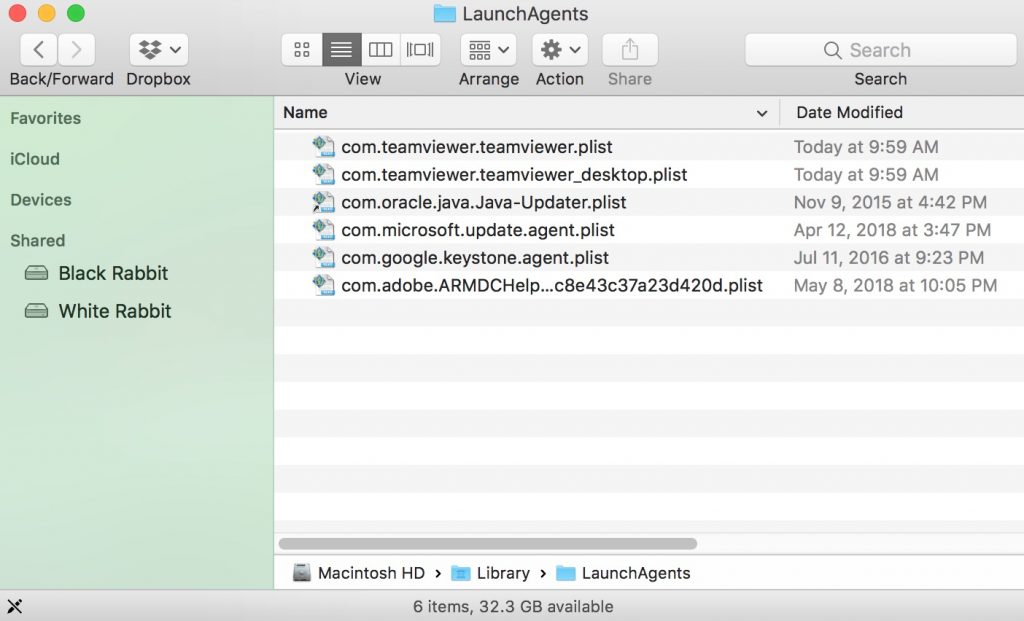
You can repeat the same procedure with the following other Library directories:
→ ~/Library/LaunchAgents
/Library/LaunchDaemons
Tip: ~ is there on purpose, because it leads to more LaunchAgents.
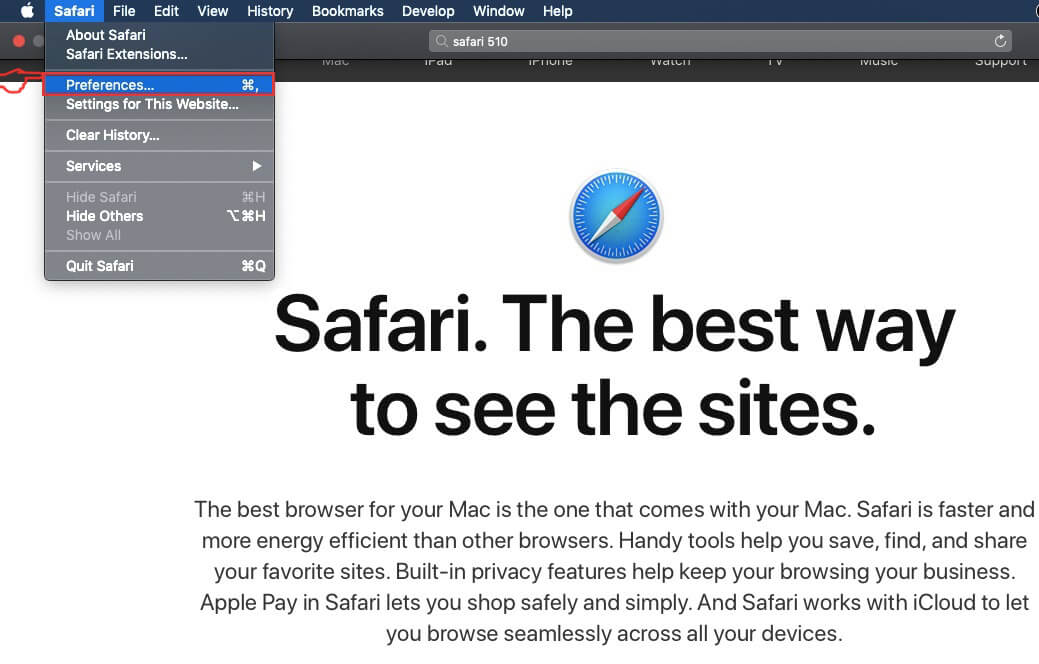
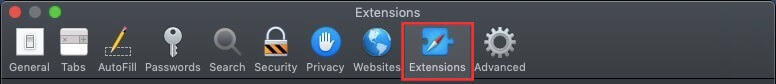
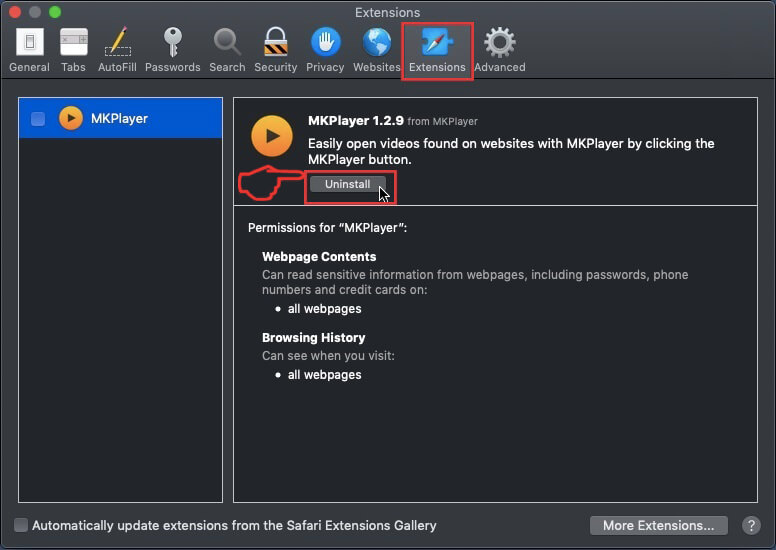
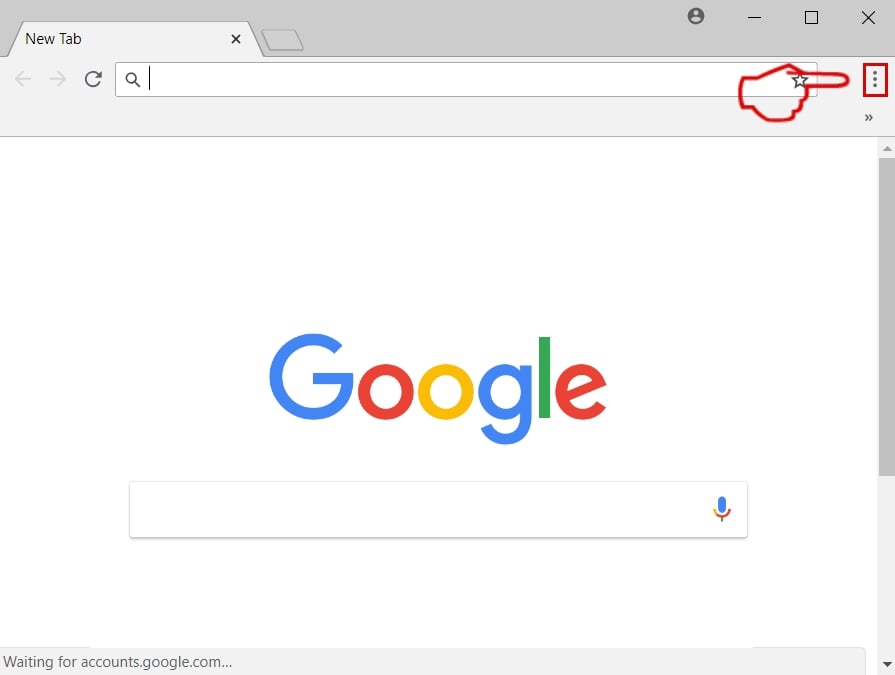
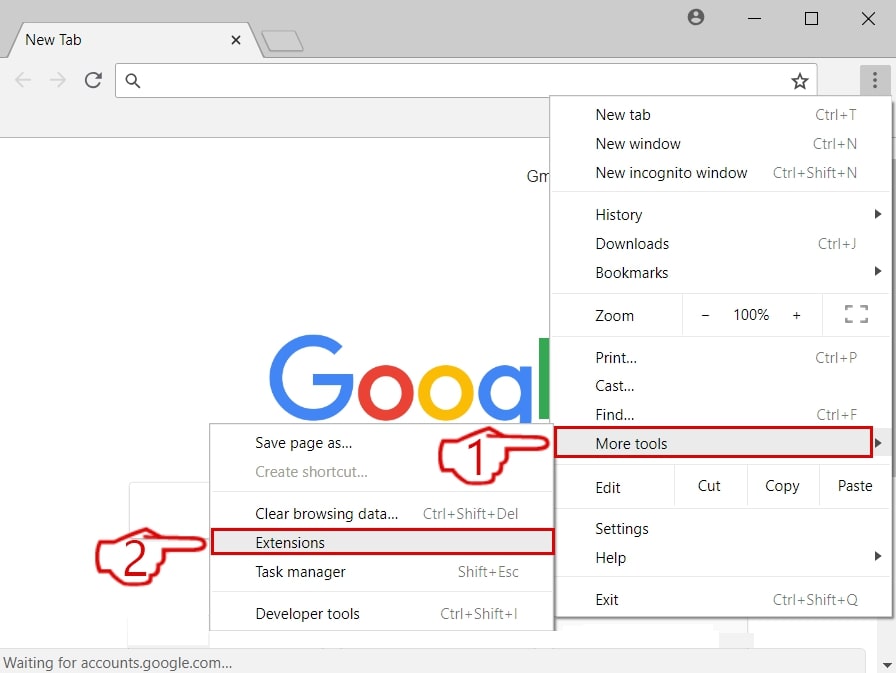
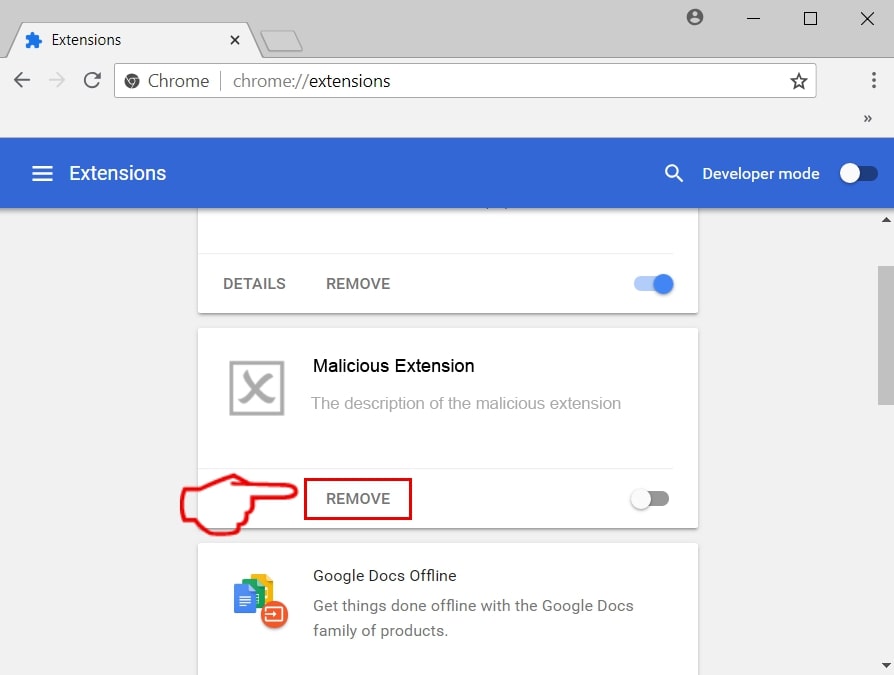
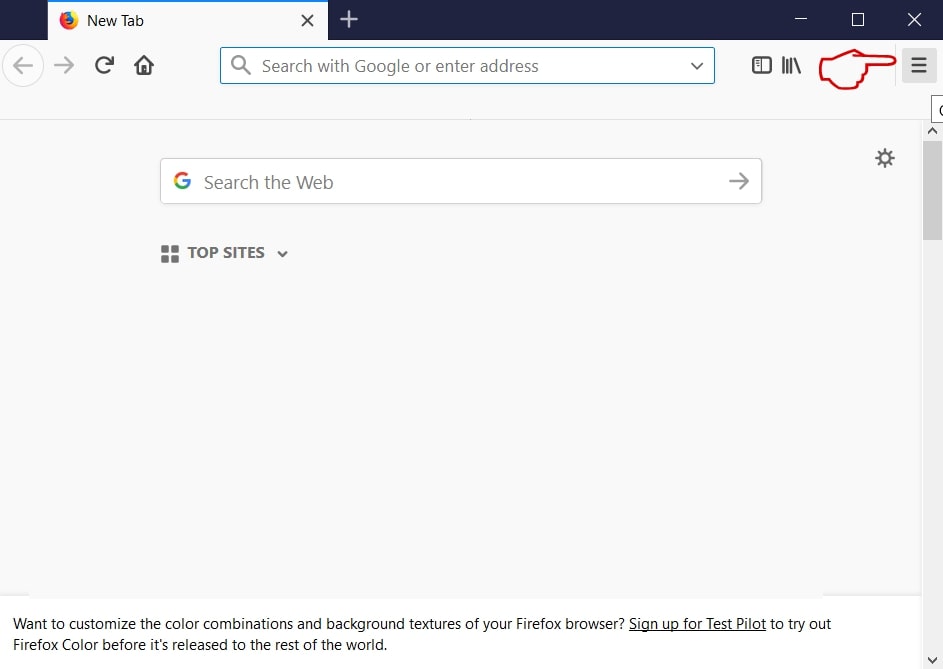
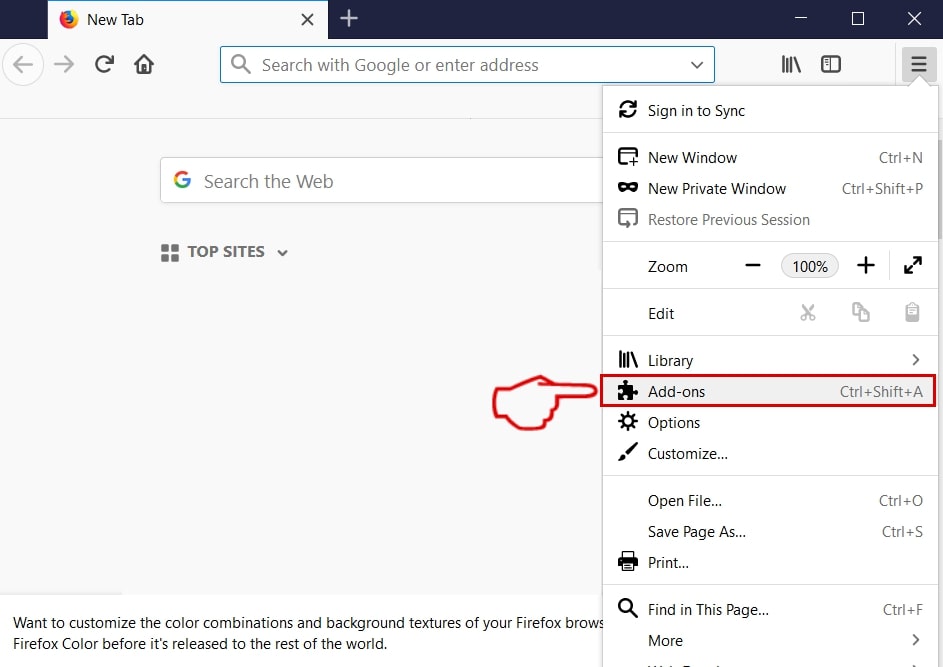
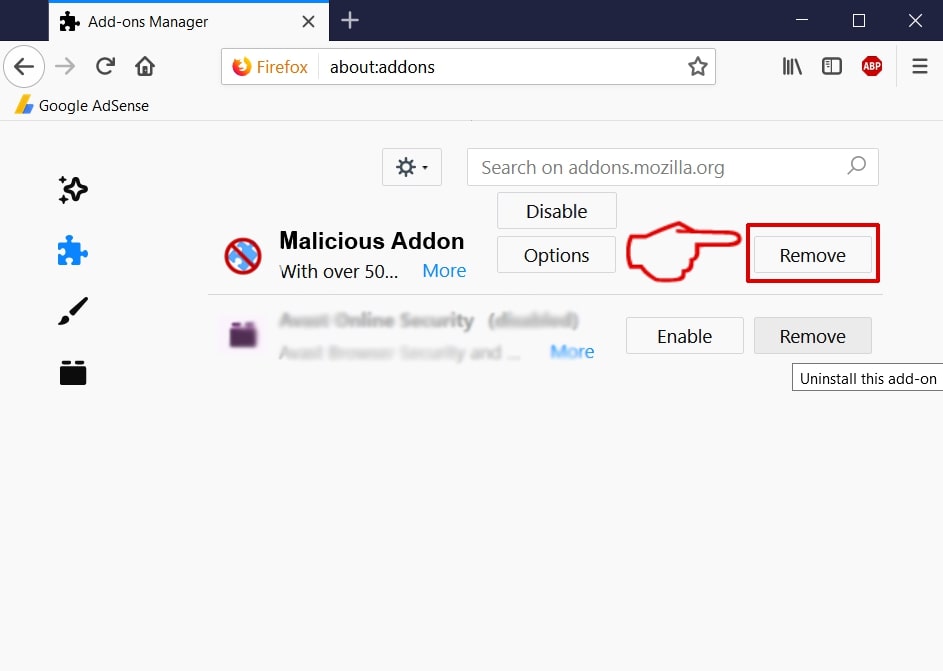
Step 3: Remove Shlayer Mac Trojan – related extensions from Safari / Chrome / Firefox
Shlayer Mac Trojan-FAQ
What is Shlayer Mac Trojan on your Mac?
The Shlayer Mac Trojan threat is probably a potentially unwanted app. There is also a chance it could be related to Mac malware. If so, such apps tend to slow your Mac down significantly and display advertisements. They could also use cookies and other trackers to obtain browsing information from the installed web browsers on your Mac.
Can Macs Get Viruses?
Yes. As much as any other device, Apple computers do get malware. Apple devices may not be a frequent target by malware authors, but rest assured that almost all of the Apple devices can become infected with a threat.
What Types of Mac Threats Are There?
According to most malware researchers and cyber-security experts, the types of threats that can currently infect your Mac can be rogue antivirus programs, adware or hijackers (PUPs), Trojan horses, ransomware and crypto-miner malware.
What To Do If I Have a Mac Virus, Like Shlayer Mac Trojan?
Do not panic! You can easily get rid of most Mac threats by firstly isolating them and then removing them. One recommended way to do that is by using a reputable malware removal software that can take care of the removal automatically for you.
There are many Mac anti-malware apps out there that you can choose from. SpyHunter for Mac is one of the reccomended Mac anti-malware apps, that can scan for free and detect any viruses. This saves time for manual removal that you would otherwise have to do.
How to Secure My Data from Shlayer Mac Trojan?
With few simple actions. First and foremost, it is imperative that you follow these steps:
Step 1: Find a safe computer and connect it to another network, not the one that your Mac was infected in.
Step 2: Change all of your passwords, starting from your e-mail passwords.
Step 3: Enable two-factor authentication for protection of your important accounts.
Step 4: Call your bank to change your credit card details (secret code, etc.) if you have saved your credit card for online shopping or have done online activiites with your card.
Step 5: Make sure to call your ISP (Internet provider or carrier) and ask them to change your IP address.
Step 6: Change your Wi-Fi password.
Step 7: (Optional): Make sure to scan all of the devices connected to your network for viruses and repeat these steps for them if they are affected.
Step 8: Install anti-malware software with real-time protection on every device you have.
Step 9: Try not to download software from sites you know nothing about and stay away from low-reputation websites in general.
If you follow these reccomendations, your network and Apple devices will become significantly more safe against any threats or information invasive software and be virus free and protected in the future too.
More tips you can find on our MacOS Virus section, where you can also ask any questions and comment about your Mac problems.
About the Shlayer Mac Trojan Research
The content we publish on SensorsTechForum.com, this Shlayer Mac Trojan how-to removal guide included, is the outcome of extensive research, hard work and our team’s devotion to help you remove the specific macOS issue.
How did we conduct the research on Shlayer Mac Trojan?
Please note that our research is based on an independent investigation. We are in contact with independent security researchers, thanks to which we receive daily updates on the latest malware definitions, including the various types of Mac threats, especially adware and potentially unwanted apps (PUAs).
Furthermore, the research behind the Shlayer Mac Trojan threat is backed with VirusTotal.
To better understand the threat posed by Mac malware, please refer to the following articles which provide knowledgeable details.


