CamuBot Trojan is a dangerous banking virus that will infect the system at a deep level. It is introduced via a sophisticated social engineering campaign and its end goals are to retrieve sensitive banking account information and private user data. Its modular engine also allows it to deploy other threats. Our article shows how victim users can remove active infections and restore their computers.

Threat Summary
| Name | CamuBot Trojan |
| Type | Trojan |
| Short Description | CamuBot Trojan is an advanced and modular virus that is programmed to spy on the users in real-time and acquire their banking account credentials. |
| Symptoms | The victims may not experience any apparent symptoms of infection. |
| Distribution Method | Freeware Installations, Bundled Packages, Scripts and others. |
| Detection Tool |
See If Your System Has Been Affected by malware
Download
Malware Removal Tool
|
| User Experience | Join Our Forum to Discuss CamuBot Trojan. |
February 2020 Brazil Campaign
The CamuBot Trojan has once again resurfaced with another dangerous attack campaign once again targeting Brazil. This comes a lot of time after the previous version has been detected. This particular attack is using a combination of two methods — manipulating the victims via social engineering and by directing malware infections in potential weak spots.
Of particular notice is the configuration of the attack campaign to be very target-specific. Coupled with the fact that the Trojan contains unique code means that it can potentially produce income for the hacking group behind it. The strategy used in the latest attack is to conceal the Trojan executable as a security application. Common ways how this can be done include the following tactics:
- Email Messages Preparation — The email messages which are sent to the victims will include advertising, notifications and various other kind of content that can mimic or impersonate well-known software.
- Fake Websites — With the aim of making the fake CamuBot-carrier files seem more legitimate the hacking group can create numerous landing pages, download portals and other types of typical sites that are used to spread such apps. They can be hosted on domains that sound very similar to well-known examples of security solutions and also contain self-signed security certificates.
The CamuBot Trojan in its latest attacks appears to be designed to keep a low profile by individually attempting to target the individual hosts. Most of the victims to date are small business which are likely to use banking applications and services in their day-to-day activities.
An analysis of the behavior of the virus samples shows that the attackers will first investigate the victims by acquiring open-source information. They can also come in contact with them by performing social engineering calls and attempting to build trust. The attackers will attempt to instruct the victims into installing the fake security program containing the CamuBot Trojan.
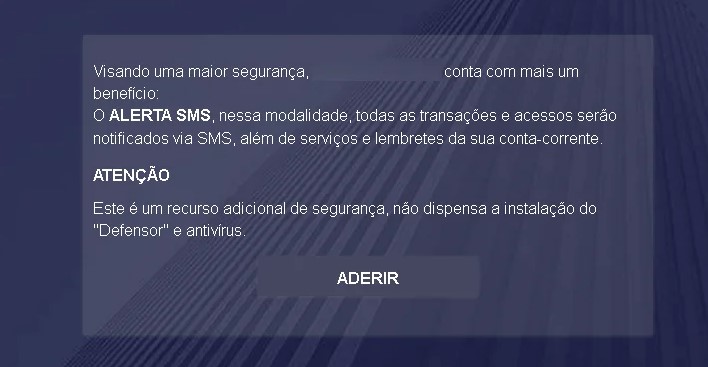
When the victims reach a crafted page the visitors will see a prompt that will ask for login credentials — this faked step has been embedded in order to appear more trustworthy. The CamuBot will be downloaded via the security application, the hackers have even prepared two versions — 32 and 64 bit editions. The fake applicator will ask for their mobile phone number in order to acquire information about it. A very non-standard approach is that the app will also request that the mobile device to be connected to the computer. This is used in order to view any SMS authorization tokens which are used to enter into online banking services.
The CamuBot Trojan will continue with its usual activity attempting to hijack financial funds, personal information and data from the host computers.
CamuBot Trojan – Distribution Methods
The CamuBot Trojan infections have been observed to spread through highly-directed large-scale attack campaigns. At this moment the identity of the hacker or criminal collective behind it is not known. The criminals depend largely on the social engineering premises that they can trick the victim users in various payloads into interacting with a element that will ultimately lead to the virus infection.
As always there are several main methods that are used to spread the executable file. The hackers can employ email messages containing elements taken from legitimate banking services such as text, images and design layouts. The Trojan files can be either directly attached or linked in the body contents.
To help facilitate the high number of infections the criminals can also create fake download sites that mimic the real-world login gateways of online banks. Similar sounding domain names and security certificates are used to create an impression that the victim users have accessed a legitimate address.
The goals of the hackers is to create an impression that the victims are downloading and using a legitimate applications. As such the usual strategy of placing it in a malicious payload carrier (documents and app installers) is not used so much.
When running the application the user interface will be similar to the legitimate apps typically offered by online banks and financial institutions.
A sophisticated phishing tactic is used to deliver the CamuBot Trojan:
- The hacking group chooses a target bank which will be the focus of the attack campaign. Using a premade scenario they will initiate calls to people and pose as bank employees in an attempt to extract information about their accounts.
- The victims will be directed to an online site by manipulating them into performing a “security check”. The address will feature legitimate elements taken from the target bank.
- Information you provide
The prompts on the site will coerce the users the victim users into downloading a “new security module” which are the CamuBot Trojan files. The latest attack campaign has been spotted in August 2018 targeting business users in Brazil. According to the available information the following victims are chosen: public sector organizations, trade companies, institutions and small businesses.
CamuBot Trojan – Detailed Description
The CamuBot Trojan infection unfold in several steps. The first stage of its behavior is the addition of two files to the Program Data service folder used by the operating system. Interestingly the name of the executable files are changed at every attack — this is done in order to prevent some types of signature scans to detect the virus instances.
The stealth protection module is started afterwards — it will look for signs of installed anti-virus tools and bypasses their real-time engines. It has also been found to modify the built-in Firewall rules and adding itself as a “trusted” application. This allows the Trojan to make both incoming and outgoing network connections without any blocks.
The CamuBot Trojan will then start to write dynamic files in the system folders and will create a secure connection to a hacker-controlled site. It will also set up a proxy server setting which means that all Internet traffic will be forwarded through а hacker server. This means that they will be able to spy on the users activities in real time. The Trojan server connection itself is used to take over control of the machines at any given time and deploy other threats. Banking Trojans like this one are usually used to look out for user actions related to access to banks. Whenever this is done the threat will automatically relay the entered credentials to the operators.
Following the active infection a pop-up window will be spawned which displays a phishing site. In most cases it will be the target bank chosen by the hackers during the campaign planning. One of the dangerous characteristics attributed to it is the fact that its engine can bypass biometric authentication — they are popularly used as a two-factor authentication mechanism. They are deemed as a reliable method and preferred over other methods. This virus proves the fact that no method is secure by itself and that weaknesses can always be found.
The security analysts note that the route of infection is not traditional as compared to other threats. While most of the banking Trojans attempt to install themselves in a silent way an avoid discovery this one is presented as an legitimate application.
When the criminals have acquired access to the online banking services they will be able to carry out a variety of tasks:
- Monitor Transactions
- Modify Values
- Create New Transactions
- Modify Account Credentials
- Modify Settings
As the Trojan has been found to contain a modular engine it can also be programmed to carry out other actions such as the following:
- Carry out Information Gathering — The engine can be programmed into harvesting information about the users, hardware and operating system by looking out for specific strings. The criminals can use the acquired information to carry out identity theft and financial abuse of the user’s data. The data harvesting component can collect information including the following: their name, address, phone number, interests, location and account credentials. Other valuable information that can be acquired includes a report on the installed hardware components, user settings and operating system values.
- Deploy Additional Threats — Installed CamuBot Trojan strains can be used as payloads for other virus infections.
- System Changes — The CamuBot Trojan can modify essential Windows settings such as the Registry. This can have a lasting impact on the overall performance, it can also disable certain functions.

Remove CamuBot Trojan
If your computer system got infected with the CamuBot Trojan, you should have a bit of experience in removing malware. You should get rid of this Trojan, as quickly as possible before it can have the chance to spread further and infect other computers. You should remove the Trojan, and follow the step-by-step instructions guide provided below.
Preparation before removing CamuBot Trojan.
Before starting the actual removal process, we recommend that you do the following preparation steps.
- Make sure you have these instructions always open and in front of your eyes.
- Do a backup of all of your files, even if they could be damaged. You should back up your data with a cloud backup solution and insure your files against any type of loss, even from the most severe threats.
- Be patient as this could take a while.
- Scan for Malware
- Fix Registries
- Remove Virus Files
Step 1: Scan for CamuBot Trojan with SpyHunter Anti-Malware Tool



Step 2: Clean any registries, created by CamuBot Trojan on your computer.
The usually targeted registries of Windows machines are the following:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
You can access them by opening the Windows registry editor and deleting any values, created by CamuBot Trojan there. This can happen by following the steps underneath:


 Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.Step 3: Find virus files created by CamuBot Trojan on your PC.
1.For Windows 8, 8.1 and 10.
For Newer Windows Operating Systems
1: On your keyboard press + R and write explorer.exe in the Run text box and then click on the Ok button.

2: Click on your PC from the quick access bar. This is usually an icon with a monitor and its name is either “My Computer”, “My PC” or “This PC” or whatever you have named it.

3: Navigate to the search box in the top-right of your PC's screen and type “fileextension:” and after which type the file extension. If you are looking for malicious executables, an example may be "fileextension:exe". After doing that, leave a space and type the file name you believe the malware has created. Here is how it may appear if your file has been found:

N.B. We recommend to wait for the green loading bar in the navigation box to fill up in case the PC is looking for the file and hasn't found it yet.
2.For Windows XP, Vista, and 7.
For Older Windows Operating Systems
In older Windows OS's the conventional approach should be the effective one:
1: Click on the Start Menu icon (usually on your bottom-left) and then choose the Search preference.

2: After the search window appears, choose More Advanced Options from the search assistant box. Another way is by clicking on All Files and Folders.

3: After that type the name of the file you are looking for and click on the Search button. This might take some time after which results will appear. If you have found the malicious file, you may copy or open its location by right-clicking on it.
Now you should be able to discover any file on Windows as long as it is on your hard drive and is not concealed via special software.
CamuBot Trojan FAQ
What Does CamuBot Trojan Trojan Do?
The CamuBot Trojan Trojan is a malicious computer program designed to disrupt, damage, or gain unauthorized access to a computer system. It can be used to steal sensitive data, gain control over a system, or launch other malicious activities.
Can Trojans Steal Passwords?
Yes, Trojans, like CamuBot Trojan, can steal passwords. These malicious programs are designed to gain access to a user's computer, spy on victims and steal sensitive information such as banking details and passwords.
Can CamuBot Trojan Trojan Hide Itself?
Yes, it can. A Trojan can use various techniques to mask itself, including rootkits, encryption, and obfuscation, to hide from security scanners and evade detection.
Can a Trojan be Removed by Factory Reset?
Yes, a Trojan can be removed by factory resetting your device. This is because it will restore the device to its original state, eliminating any malicious software that may have been installed. Bear in mind that there are more sophisticated Trojans that leave backdoors and reinfect even after a factory reset.
Can CamuBot Trojan Trojan Infect WiFi?
Yes, it is possible for a Trojan to infect WiFi networks. When a user connects to the infected network, the Trojan can spread to other connected devices and can access sensitive information on the network.
Can Trojans Be Deleted?
Yes, Trojans can be deleted. This is typically done by running a powerful anti-virus or anti-malware program that is designed to detect and remove malicious files. In some cases, manual deletion of the Trojan may also be necessary.
Can Trojans Steal Files?
Yes, Trojans can steal files if they are installed on a computer. This is done by allowing the malware author or user to gain access to the computer and then steal the files stored on it.
Which Anti-Malware Can Remove Trojans?
Anti-malware programs such as SpyHunter are capable of scanning for and removing Trojans from your computer. It is important to keep your anti-malware up to date and regularly scan your system for any malicious software.
Can Trojans Infect USB?
Yes, Trojans can infect USB devices. USB Trojans typically spread through malicious files downloaded from the internet or shared via email, allowing the hacker to gain access to a user's confidential data.
About the CamuBot Trojan Research
The content we publish on SensorsTechForum.com, this CamuBot Trojan how-to removal guide included, is the outcome of extensive research, hard work and our team’s devotion to help you remove the specific trojan problem.
How did we conduct the research on CamuBot Trojan?
Please note that our research is based on an independent investigation. We are in contact with independent security researchers, thanks to which we receive daily updates on the latest malware definitions, including the various types of trojans (backdoor, downloader, infostealer, ransom, etc.)
Furthermore, the research behind the CamuBot Trojan threat is backed with VirusTotal.
To better understand the threat posed by trojans, please refer to the following articles which provide knowledgeable details.