Software products are not perfect and can be full of vulnerabilities, anti-virus software included. Bug hunters and white hats are usually the ones to disclose flaws in applications, and to notify the vendors so that a fix is implemented. If the name Tavis Ormandy is familiar to you, it’s because he has found and reported flaws in Symantec’s products multiple times. His latest discovery is CVE-2016-2208.

CVE-2016-2208, An Exploit in the Core Symantec Antivirus Engine
Just a single look at Ormandy’s Twitter page is enough to spot the issues he has made public, the latest one being an exploitable overflow. The exploit, labeled CVE-2016-2208, is found in the core Symantec Antivirus Engine applied in most Symantec and Norton AV products, as the researcher writes.
When parsing executables packed by an early version of aspack, a buffer overflow can occur in the core Symantec Antivirus Engine used in most Symantec and Norton branded Antivirus products. The problem occurs when section data is truncated, that is, when SizeOfRawData is greater than SizeOfImage.
Shortly said, the issue us due to the way Symantec products handle executable files compressed via an older version of Aspack compression software. The vulnerability is a remote code execution one, and the only action an attacker needs to exploit it is emailing a file to the victim or sending them a link. The exploit can happen either via email or a browser, and affects Linux, OS X, and Windows:
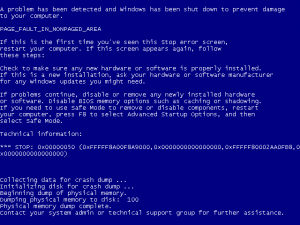
On Linux, Mac and other UNIX platforms, this results in a remote heap overflow as root in the Symantec or Norton process. On Windows, this results in kernel memory corruption, as the scan engine is loaded into the kernel (wtf!!!), making this a remote ring0 memory corruption vulnerability – this is about as bad as it can possibly get.
Learn More about Remote Code Execution
According to Ormandy’s discoveries, because of the core nature of the flaw, it affects several Symantec products, such as:
- Symantec Endpoint Antivirus – all platforms;
- Norton Antivirus – all platforms;
- Symantec Scan Engine – all platforms;
- Symantec Email Security – all platforms.
The researcher suspects that more Symantec products may be prone to the exploit, too. He has corresponded with the security firm, and security fixes are on their way. This is Symantec’s security response, published on May 16.


