| Name | CoreBot |
| Type | Trojan Stealer and Downloader |
| Short Description | Steals all types of credentials – login details, financial information, files, etc. |
| Symptoms | Appearing of different objects in various user folders or the Desktop or on startup. Files encoded with unfamiliar extensions |
| Distribution Method | Spam mails. MiTM attacks, malicious redirects. |
| Detection tool | Download SpyHunter, to See If Your System Has Been Affected By CoreBot |
 A dangerous malware infection has been detected out in the wild. It is called CoreBot, and it can cause a lot of havoc and headaches to many users. It is focused mainly on stealing information without any restrictions what so ever. According to IBM’s report this Trojan infects computers mainly via dropper, immediately attacking svchost.exe, a critical Windows process. More to it than that, this RAT (Remote Access Tool) is created in a particular method, allowing it to stay undetected while inputting new methods of data theft from the victim computer. IBM Security X-Force researchers report that the threat name is well concealed, and the most antivirus programs report is as Dynamer!ac or some other similar threats.
A dangerous malware infection has been detected out in the wild. It is called CoreBot, and it can cause a lot of havoc and headaches to many users. It is focused mainly on stealing information without any restrictions what so ever. According to IBM’s report this Trojan infects computers mainly via dropper, immediately attacking svchost.exe, a critical Windows process. More to it than that, this RAT (Remote Access Tool) is created in a particular method, allowing it to stay undetected while inputting new methods of data theft from the victim computer. IBM Security X-Force researchers report that the threat name is well concealed, and the most antivirus programs report is as Dynamer!ac or some other similar threats.
CoreBot – Methods of Infection
Malware such as CoreBot may infect systems via massive spam email campaigns. Also, targeted attacks may be the reason for some infections. Targeted attacks are mainly present where there are organizations or any LANs (Local Area Networks) containing average and vast numbers of devices. A good strategy to infect massive amount of users is by using an approach called spoof mailing. It is easy to complete when you try to trick a user. All you need to know is information about who he corresponds by email with often to mask it. When it comes to infecting organizations, however, the attacker has to be very well informed regarding Microsoft Outlook and other mail programs (Mozilla Thunderbird, etc.), because they have spoof email detection protocols. More to it than that, the attackers have to be connected directly to the server of the organization and be within the local network to be able to send the message locally. Basically in this case many attackers may prefer the ‘hands-on’ approach.
CoreBot – More About Information Stealing Software
Information stealing type of Trojans may vary a lot in their methods of infection, methods of data theft, when they steal, do they choose to create a botnet (zombie networks). Either way, Trojan stealers, like CoreBot sniff out the user PC for email credentials, online account information and all types of financial data. Everything may be transferred to the servers of the attackers, where the information could be manually filtered and prioritized by relevance. A lot of Trojan botnet attackers usually sell any stolen information on underground markets to other users. It is a common practice to sell information taken from organizations to competitors.
As previously mentioned, CoreBot uses a dropper to infiltrate a user system. Once this particular code is put into actions, it immediately activates svchost type of process. This process is used as a backbone and allows malicious files to be recorded on the memory drive of the machine. After the dropper has performed its job, it closes.
The following step for CoreBot is to create a UID (unique identifier). This type of code may be used for the purpose of successfully interacting with Windows Registry Editor.
More to it than that IBM engineers report that this type of threat uses a plugin system that enables it to download .dll files and plugins from the attackers’ control center.
Also, researchers say that despite the ability of CoreBot to steal passwords, it is not able to capture live data from online browsing. It is mainly focused on obtaining stored login information in most famous web browsers. Also, the threat scans for any passwords stored in the computer by various clients, as well as information about online wallets and e-payment data.
The malware also has a very specific algorithm, allowing it to communicate safely with the control server via automatically created custom domain names. These particular names are created with the purpose only to be known to the attacker, and it takes an experienced specialist to reverse engineer and discover them. This type of communication is excellent for botnets, and those domain names may or may not change to remain undetected over time. A very interesting discovery, regarding DGA (Domain Generation Algorithm), was that, in this case, the malware creates a domain based on the device’s location.
What is scary for this particular threat is that CoreBot may use the Windows Power Shell to download other malware, such as ransomware (CryptoWall, Bitcrypt, etc.), other trojans, rootkits, keyloggers and more malware on the infected computer.
CoreBot is especially risky to organisations, because if it infects an essential equipment, storing all of the valuable information, can gain access to and steal critical employee data. What is worse, CoreBot can obtain customer information, such as the case of the recent Ashley Madison’s customer information publishing.
CoreBot – How To Remove and Protect Yourself?
In order to prevent such threats from penetrating your defenses, standard protection protocols may not be effective against CryptoBot. You need to use unusual methods of data distribution within your company, such as storing the data offline and keeping it in safe machines that do not even have network cards. These machines may be turned on only when necessary, and the data distribution to them should always be from a secure memory carrier. This is one way of protecting data, but it is surely not the best one. The most important detail is that no matter where you store your important data, you should not share information about how you store it in which location, because experts know that the biggest percentage of information leaking are because of human error.
Removing CoreBot should be done in offline mode, in order to break any active connections with the command and control servers of the attackers. It is recommended to follow the tutorial below to boot into safe mode and from there perform the usual anti-malware scan with such program. Also, since CoreBot has the explicit ability to download other malware onto machines, it is very much recommended to scan the computer for a Rootkit virus with a rootkit remover type of software. Rootkits are not a very common threat but if a cybercriminal wants to remain persistent in the user PC.
1. Start Your PC in Safe Mode to Remove CoreBot.
For Windows XP, Vista, 7 systems:
1. Remove all CDs and DVDs, and then Restart your PC from the “Start” menu.
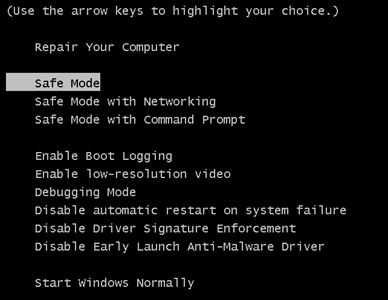
2. Select one of the two options provided below:
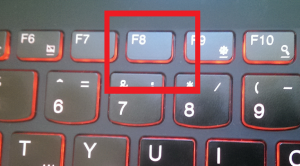
– For PCs with a single operating system: Press “F8” repeatedly after the first boot screen shows up during the restart of your computer. In case the Windows logo appears on the screen, you have to repeat the same task again.
– For PCs with multiple operating systems: Тhe arrow keys will help you select the operating system you prefer to start in Safe Mode. Press “F8” just as described for a single operating system.
3. As the “Advanced Boot Options” screen appears, select the Safe Mode option you want using the arrow keys. As you make your selection, press “Enter“.
4. Log on to your computer using your administrator account
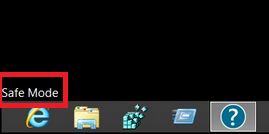
While your computer is in Safe Mode, the words “Safe Mode” will appear in all four corners of your screen.
For Windows 8, 8.1 and 10 systems:
Step 1: Open the Start Menu
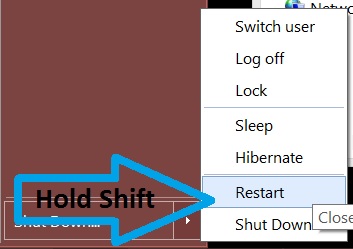
Step 2: Whilst holding down Shift button, click on Power and then click on Restart.
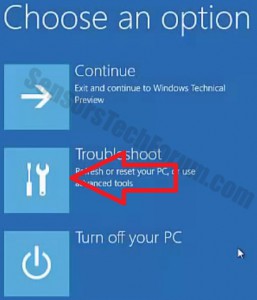
Step 3: After reboot, the aftermentioned menu will appear. From there you should choose Troubleshoot.
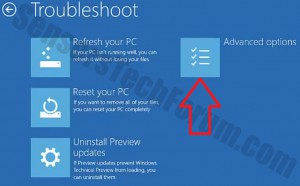
Step 4: You will see the Troubleshoot menu. From this menu you can choose Advanced Options.
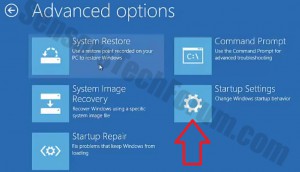
Step 5: After the Advanced Options menu appears, click on Startup Settings.
Step 6: Click on Restart.
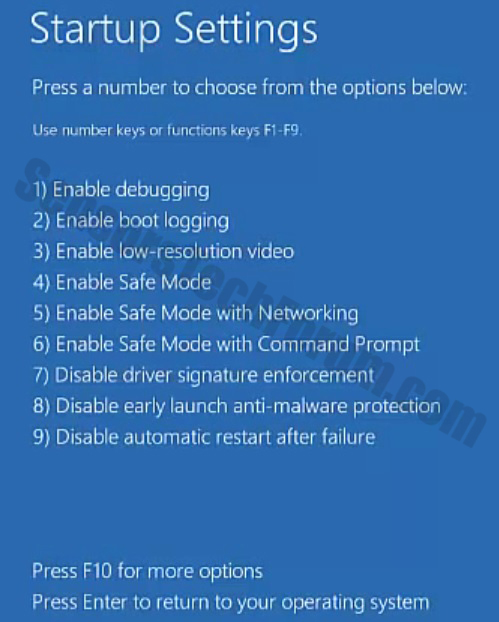
Step 7: A menu will appear upon reboot. You should choose Safe Mode by pressing its corresponding number and the machine will restart.
2. Remove CoreBot automatically by downloading an advanced anti-malware program.
To clean your computer you must download an updated anti-malware program on a safe PC and then install it on the affected computer in offline mode. After that you should boot into safe mode and scan your computer to remove all CoreBot associated objec
Preparation before removing CoreBot.
Before starting the actual removal process, we recommend that you do the following preparation steps.
- Make sure you have these instructions always open and in front of your eyes.
- Do a backup of all of your files, even if they could be damaged. You should back up your data with a cloud backup solution and insure your files against any type of loss, even from the most severe threats.
- Be patient as this could take a while.
- Scan for Malware
- Fix Registries
- Remove Virus Files
Step 1: Scan for CoreBot with SpyHunter Anti-Malware Tool



Step 2: Clean any registries, created by CoreBot on your computer.
The usually targeted registries of Windows machines are the following:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
You can access them by opening the Windows registry editor and deleting any values, created by CoreBot there. This can happen by following the steps underneath:


 Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.Step 3: Find virus files created by CoreBot on your PC.
1.For Windows 8, 8.1 and 10.
For Newer Windows Operating Systems
1: On your keyboard press + R and write explorer.exe in the Run text box and then click on the Ok button.

2: Click on your PC from the quick access bar. This is usually an icon with a monitor and its name is either “My Computer”, “My PC” or “This PC” or whatever you have named it.

3: Navigate to the search box in the top-right of your PC's screen and type “fileextension:” and after which type the file extension. If you are looking for malicious executables, an example may be "fileextension:exe". After doing that, leave a space and type the file name you believe the malware has created. Here is how it may appear if your file has been found:

N.B. We recommend to wait for the green loading bar in the navigation box to fill up in case the PC is looking for the file and hasn't found it yet.
2.For Windows XP, Vista, and 7.
For Older Windows Operating Systems
In older Windows OS's the conventional approach should be the effective one:
1: Click on the Start Menu icon (usually on your bottom-left) and then choose the Search preference.

2: After the search window appears, choose More Advanced Options from the search assistant box. Another way is by clicking on All Files and Folders.

3: After that type the name of the file you are looking for and click on the Search button. This might take some time after which results will appear. If you have found the malicious file, you may copy or open its location by right-clicking on it.
Now you should be able to discover any file on Windows as long as it is on your hard drive and is not concealed via special software.
CoreBot FAQ
What Does CoreBot Trojan Do?
The CoreBot Trojan is a malicious computer program designed to disrupt, damage, or gain unauthorized access to a computer system. It can be used to steal sensitive data, gain control over a system, or launch other malicious activities.
Can Trojans Steal Passwords?
Yes, Trojans, like CoreBot, can steal passwords. These malicious programs are designed to gain access to a user's computer, spy on victims and steal sensitive information such as banking details and passwords.
Can CoreBot Trojan Hide Itself?
Yes, it can. A Trojan can use various techniques to mask itself, including rootkits, encryption, and obfuscation, to hide from security scanners and evade detection.
Can a Trojan be Removed by Factory Reset?
Yes, a Trojan can be removed by factory resetting your device. This is because it will restore the device to its original state, eliminating any malicious software that may have been installed. Bear in mind that there are more sophisticated Trojans that leave backdoors and reinfect even after a factory reset.
Can CoreBot Trojan Infect WiFi?
Yes, it is possible for a Trojan to infect WiFi networks. When a user connects to the infected network, the Trojan can spread to other connected devices and can access sensitive information on the network.
Can Trojans Be Deleted?
Yes, Trojans can be deleted. This is typically done by running a powerful anti-virus or anti-malware program that is designed to detect and remove malicious files. In some cases, manual deletion of the Trojan may also be necessary.
Can Trojans Steal Files?
Yes, Trojans can steal files if they are installed on a computer. This is done by allowing the malware author or user to gain access to the computer and then steal the files stored on it.
Which Anti-Malware Can Remove Trojans?
Anti-malware programs such as SpyHunter are capable of scanning for and removing Trojans from your computer. It is important to keep your anti-malware up to date and regularly scan your system for any malicious software.
Can Trojans Infect USB?
Yes, Trojans can infect USB devices. USB Trojans typically spread through malicious files downloaded from the internet or shared via email, allowing the hacker to gain access to a user's confidential data.
About the CoreBot Research
The content we publish on SensorsTechForum.com, this CoreBot how-to removal guide included, is the outcome of extensive research, hard work and our team’s devotion to help you remove the specific trojan problem.
How did we conduct the research on CoreBot?
Please note that our research is based on an independent investigation. We are in contact with independent security researchers, thanks to which we receive daily updates on the latest malware definitions, including the various types of trojans (backdoor, downloader, infostealer, ransom, etc.)
Furthermore, the research behind the CoreBot threat is backed with VirusTotal.
To better understand the threat posed by trojans, please refer to the following articles which provide knowledgeable details.