Security experts detected that an ongoing attack campaign is spreading fake Fortnite Android games that lead to malware infections. Several outlets are being used to push the malicious apps — both third-party repositories and fake download sites.
Malicious Fortnite Installers Lead to Dangerous Virus Infections
Fortnite as one of the most popular Android games at the moment has received major attention both by gamers and malicious users. Two weeks ago the CEO of Epic Games stated that the game would not be available on the Google Play Store repository. This resulted in the download of the APK (installation file) from the vendor’s download sites. Such situations are exploited by computer criminals that take advantage of the fact.
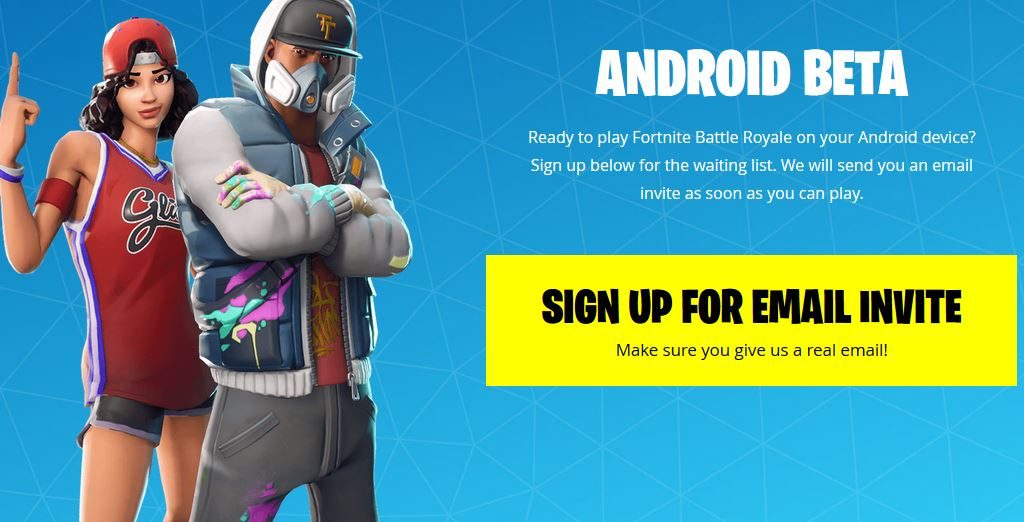
As soon as the game was officially released numerous download sites appeared attempting to coerce the users that they are a legitimate vendor page. They exhibit the legitimate web elements and design layout as the official Fortnite Android game. The fact that the application is not distributed on Google Play means that the repository’s internal malware protection scan will not be initiated. Some malicious copies can be automatically detected by Google and removed, when the installations are ordered by the users it is much more difficult to distinguish the real from the fake setup.
There are several warning signs that can be attributed to the fake Fortnite installer samples:
- The string “Fortnite” is included in the URL when the address does not contain Epic Games or other names that are part of the official vendor site.
- The criminals behind the fake apps use the same web design elements, layout and landing pages to construct convincing looking sites.
- A complex network of redirect links can be constructed in certain examples. Links to the fake pages can be distributed on gaming forums, communities, social networks and etc.
The fake Fortnite Android installers have been found to malware — the collected samples can be grouped into releases coming from two distinct families. The first group is a referred to as “FakeNight” which launches a Fortnite loading screen as soon as the fake game is launched. The users will be presented a notification prompt showing the message “Mobile Verification Required”. A browser will be launched which instructs the user into clicking on ads, in return the victim is promised game codes. Interaction with the threat will return no benefits.
The second malicious is called “WeakSignal” and symptoms of infection are again a Fortnite loading screen. However instead of loading the game a series of ads will be displayed on the user’s screen and they will be followed by a message that informs of a weak signal. Ads are presented to the users on a continuous basis.
Both of these malware are delivery mechanisms for the so-called “click farms” — utility software that are used by hackers to monetize ad earnings.


