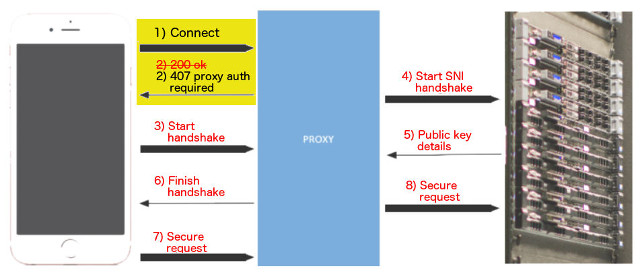
A new security vulnerability that can put a range of products at risk has been just disclosed by security researcher Jerry Decime. He has revealed shocking details about the flaw, dubbed FalseCONNECT. According to Decime’s analysis, the vulnerability can allow a Man-in-the-Middle attack and intercept HTTPS traffic. This would be due to flaws in the deployment of proxy authentication procedures in multiple products. More precisely, a flaw exists in how specific applications respond to HTTP CONNECT requests via the HTTP/1.0 407 Proxy Authentication Required responses.
A Deeper Look into the FalseCONNECT Vulnerability
Shortly said:
Mistakes were made in the implementation of proxy authentication. This, in turn, resulted in numerous vulnerabilities with the implementations of the “HTTP/1.0 407 Proxy Authentication Required” response to CONNECT requests across a broad range of operating systems, applications, and browsers for any device configured to use a proxy and even some that weren’t with auto-proxy support enabled by default in Windows.
It’s important to note that the flaw exists only in network environments. This is where users apply proxy connections. The setup is mostly popular in enterprise networks in which powerful firewalls are set in place. If an attacker has access to a compromised network and could listen to proxy traffic, he could also easily sniff for HTTP CONNECT requests sent to the local proxy.
Once such a request is intercepted by an attacker, he can reply to it instead of the real proxy server. Then, the attacker can issue a 407 Proxy Authentication Required response where the user is asked for a password to access a service.
Why Is the Vulnerability Called FalseCONNECT? Vendors Affected
HTTP connect requests are unencrypted and an attacker would know when the target wants to access sensitive accounts. This can happen even when the services are HTTPS.
Who Is Affected by FalseCONNECT?
In the researcher’s own words:
The worst of these vulnerabilities [is] impacting Apple, which until the release of the iOS 9.3.3 update manifested as a complete failure of HTTPS trust in iOS, all versions since at least iOS 5.1.1 for OS trust components, Safari, Opera, and applications utilizing WebKit when using proxies.
In addition, the researcher found that WebKit software is more vulnerable than others.
What Is WebKit?
WebKit is a layout engine software component for rendering web pages in web browsers. WebKit also powers Apple’s Safar, and a fork of the project is used by Chromium-based browsers, like Google Chrome and Opera. US-CERT has alerted that “WebKit-based clients are vulnerable to additional vectors due to the fact that HTML markup and JavaScript are rendered by the client Document Object Model (DOM) in the context of the originally requested HTTPS domain.”
Apple, Microsoft, Oracle and Opera have already endorsed their products affected by the flaw. Other vendors are still calculating the risks of FalseCONNECT and the impact it can have on their products. The list includes Linux distros, Cisco, HP, IBM, Google, Juniper, Nokia, Mozilla, SAP, Sony, etc.
Vendors can test for this vulnerability using an intercepting proxy such as The Fiddler. It supports the CONNECT interception. A bit of FiddlerScript after the OnBeforeResponse function is all that is needed, the researcher adds.
More information about this serious flaw is available on FalseConnect’s dedicated page.