Kali Linux is one of the most famous and widely used Linux distributions for security testing, digital forensics and penetration testing. It has grown in popularity so fast that it is now perceived as an essential part of every security expert (and hacker) toolkit.
Kali Linux Is Based on Tradition
Kali Linux is based on Debian Gnu/Linux that is one of the large and famed distributions of the open-source operating system. It has explicitly been built with security engineers in mind – it includes over 600 packages for penetration testing. It can be easily run using a live CD or USB or used in virtual machines. Some security experts even speculate that the growing popularity of Kali Linux can be linked to the numerous amateur attacks that they counter. The distribution is very easy to use even by beginners and its large collection of applications has helped the outlaws to create an extensive collection of hacking tutorials.
As Kali Linux originates from Debian it allows its users to take advantage of the Advanced Package Tool (APT) that provides experts with the ability to add various third-party repositories. They allow the administrators to set up their own hosts, mirrors and gateways and to manage the software installations. APT is one of the most popular systems and it is used by other popular distributions such as Ubuntu.
The distribution can be downloaded in various flavors – it supports both 32 and 64-bit computing, as well as several ARM platforms. This makes it possible to use it with board computers such as the Raspberry Pi and other cheap platforms on which it can run. Like other distributions Kali Linux can be downloaded with different graphical environments depending on the computer’s resources or the user preferences.
The Kali Linux Software Collection
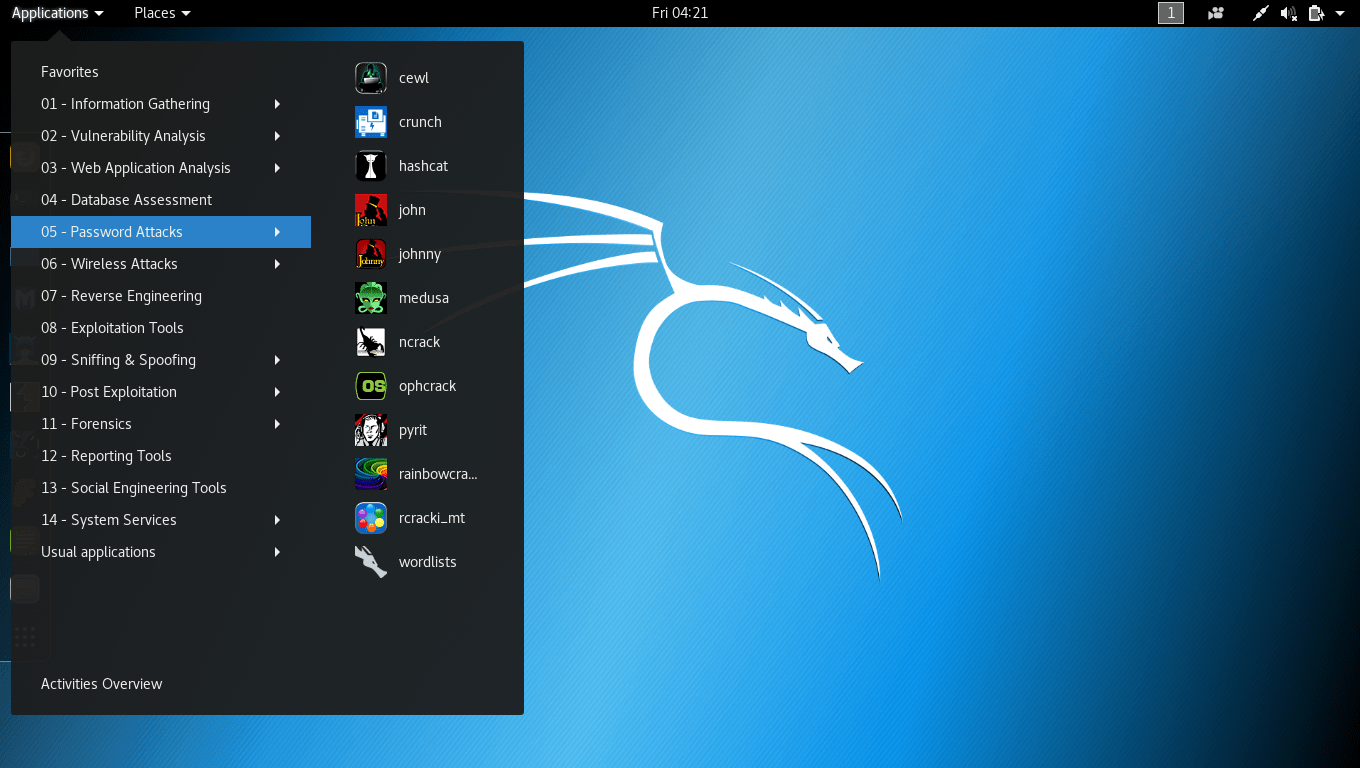
The extensive list of applications and the easy to use menu organizations helps the security experts to quickly and easily execute their actions. Using Kali Linux practically every penetration testing and forensics data collection task is possible. Popular case scenarios include the following:
- Cracking WI-Fi Passwords – Kali Linux includes the popular tools for gaining access to protected Wi-Fi Passwords using the three most popular encryption methods: WEP, WPA and WPA2. This can be done by automated tools or selectively capturing network traffic and cracking the handshakes and hashes.
- Network Traffic Analysis – Using powerful network analysis tools Kali Linux can be used to analyze the traffic via different network interfaces, connection methods and protocols. Any “sniffing” (eavesdropping) can provide information about what sites are being visited, form data, cookies, passwords, account data and files.
- Vulnerability Testing – Both computer security experts and hackers can use the array of available tools to launch exploits against the targets. This can be done in an automated way by launching scripts or user interface programs. Kali Linux includes the well known Metasploit framework that is regarded as one of the premier hacking and cyber security tool.
- Mass E-Mail Spam Campaigns – The integrated Kali Linux tools can be used to create and coordinate malicious email campaigns that can contain viruses or vulnerability exploits. Using the applications the criminals can craft payloads of their own by choosing what malware to include, the type of exploit and the behavior flow.
- Web Attacks – Using toolkits and collected information the penetration testers can launch complex and varied attacks against web sites, servers and even networks. Depending on the goal some of steps may be automated by only specifying the target address.
- Forensic Data Collection – Kali Linux allows extensive data collection both from local and network hosts. Digital forensic experts can trace with detail any file changes, computer interactions. Encrypted files can be recovered using dictionary attacks, brute force attacks or other methods. Kali Linux is especially suited for digital forensics experts. When booted from a live CD or USB the users can enter the special “Forensics” mode that does not mount any drives (even detected swap partitions). It enables them to work with the computers, create perfect backups (without resorting to any write operations of the target drives) and investigate the data.
- System Restore – The distribution is also useful for diagnosing and fixing security incidents on local computers. Using the built-in applications system administrators can restore access to password-protected drives and other improperly configured security features.
- Stress Testing – Kali Linux can be used to test networks and servers for performance and resource usage. It includes different types of applications that can be fine tuned to the specific environment.
Kali Linux Is More Than a Remastered Distribution
Even though the main goal of Kali Linux is penetration testing the fact that it has grown popular among both security experts and criminals makes it an important software to monitor. Statistics show that is the most popular standalone security-focused Gnu/Linux distribution, currently ranking in 18th place on the Distrowatch website.
By downloading a customized version of their choice, the computer users acquire a complete desktop environment that even include some of the most important end user applications. The operating system is preferred by many specialists and dedicated security tutorials and courses based on Kali Linux are offered by professional and academic institutions.
For more information visit the project’s official website.




nt bad
I thought it was based on what we need to learn before learning KALI. but never mind