Reading a cybersecurity book may not sound like something entertaining. Scott Schober’s Hacked Again, however, proved that a book covering a very serious topic could be fun to read. Written in a light and easy-to-understand style, the book reveals Mr. Schober’s own collision with hackers, and all that is wrong with the modern banking system.
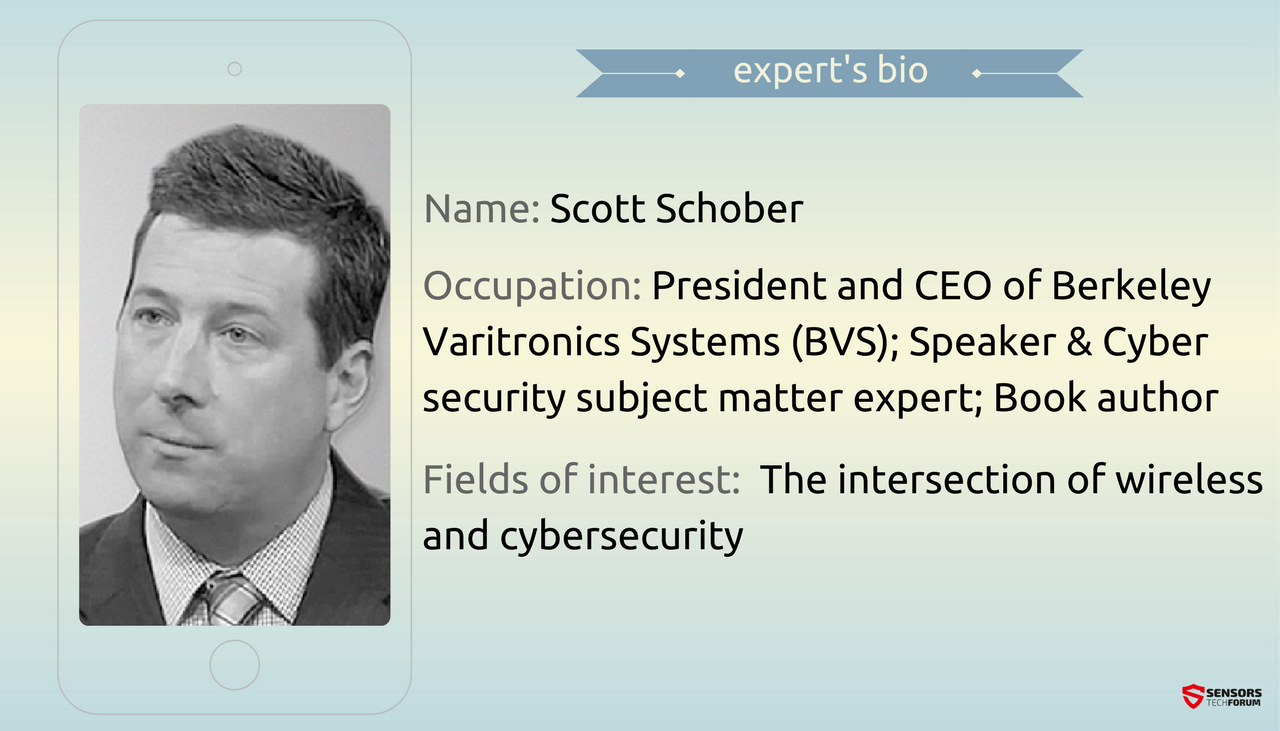
But who is Scott Schober? He is the President and CEO of a 44-year-old New Jersey-based company called BVS (Berkeley Varitronics Systems). Mr. Schober is also an experienced software engineer who has developed cellular test instruments used for measuring, optimizing and plotting signal coverage, primarily for the initial cellular build-out throughout the United States.
He is recently focused on the development of BVS’ cell phone detection tools, used to enforce a ‘no cell phone policy’ in various markets including government, corporate, military, educational, correctional and law enforcement.
Scott is also a frequent speaker and an educator. Get to know him in the interview below!
STF: Hacked Again is the perfect read for the average PC user. You have presented the concepts of cybersecurity in a subtle and practical way. Have you ever considered writing a book aimed at the tech-savvy reader?
Mr. Schober: Actually, the initial manuscript was written for more tech-savvy readers. But as I started to talk about the book with colleagues, friends and family, I realized that they had so many of their own cybersecurity questions, troubles and concerns. They became an audience that I could not ignore. So when I took the revised manuscript to my editors, I knew we had something great for consumers, small business owners and even some experts that appreciate occasional refreshers on cybersecurity best practices. My goal was not only to tell my story and ordeal of being hacked but more importantly to share what I have learned with readers so they do not become victims themselves.
Related: Dr. Vesselin Bontchev: Non-Replicating Malware Has Taken over the Computer Virus
I was also encouraged to spend more time defining unfamiliar terms as I introduced them into the writing process. I pulled all the unfamiliar ‘cyber’ terms together into a complete glossary so my readers have a handy source to get a quick non-techie definition. I also created an online glossary that is always being updated and was encouraged to see successful cybersecurity web sites like CyberSecurityVentures include my glossary on their homepage.
Since I have had such a tremendous response to Hacked Again, I started working on a follow up book tentatively titled ‘Hacked Again – Lessons Learned’. This new book continues where Hacked Again left off as well as cover the cybersecurity stories like Apple vs. the FBI in 2016 that occurred after my book already went to the presses. Of course breaches such as Ashley Madison, Yahoo, and DNC / Russian hacks along with my analysis are also included in this new book.
STF: Organized cybercrime seems to be a perfectly oiled machine. Is there something we, the cybersecurity people, could learn from it? I asked cybersecurity expert Raef Meeuwisse the same question and he said that we could learn from the fact that cybercriminals share information better and faster than legitimate organizations.
Mr. Schober: I concur with Raef’s sentiment and feel that we need to learn to share our successes and failures with each other when it comes to cybersecurity. Hackers only have to get it right one time but we have to get it correct every time. The odds are stacked against us but if we collectively worry less about admitting that we’ve been compromised and spend more time sharing knowledge, we all benefit. I recently attended the Herjavec Group’s LIFT OFF cybersecurity event. The one thing every speaker had in common was the notion of sharing stories, techniques and data with fellow cybersecurity experts regardless of how embarrassing or revealing those facts look to others. We have technologically outpaced ourselves but are far behind in securing ourselves with and from that very same technology.
Hackers play in the Dark Web and share hacking tools, hacking tips, and even provide assistance to new hackers learning the ropes. The concept of criminals sharing techniques could also be applied by the ‘good guys’ fighting the cyber hackers. Sharing information will allow companies and individuals to anticipate the next threat and be proactive in stopping hackers in their tracks.
STF: In your book you say that “one of the most effective ways to gain instant access to valuable personal and secure information is through passwords”. How do you feel about biometrics replacing passwords? Will biometric checks worsen or improve the security of our lives?
Mr. Schober: I am optimistic about biometrics as an additional form of authentication. Biometrics, when properly used, stored and encrypted are extremely secure. Right now they are an additional level of security kind of like two-factor authentication. Companies like Apple and Samsung have successfully introduced convenient fingerprint sensors. These biometric advances are really no more secure than passwords but since general users are so hesitant to create strong passcodes (as in the case of unlocking your smartphone) or passwords, the convenience of biometrics outweigh the general laziness or ignorance of the public.
Again, nothing is 100% secure but biometrics will continue to advance and provide greater levels of security. It is important to keep in mind that biometrics have tradeoffs as well. Some go to great lengths to hide passwords from others, but we don’t walk around wearing gloves to keep our fingerprints from being scanned or copied by hackers. The recent OPM (Office of Personnel Management) compromise of government employees had 5.6 million fingerprints compromised. Unfortunately, the ability to misuse fingerprint data in future breaches in inevitable.
STF: “А computer plastered with sticky notes full of passwords is a billboard advertising security leaks.“ I really like that quote from your book! Do you have a favorite cybersecurity quote or motto to guide you in both your personal and business life?
Mr. Schober: I make a mental note to check for things such as sticky notes containing passwords at every office I visit and I continually find these security weaknesses everywhere. I was doing a cybersecurity interview on a prominent radio program and halfway through the interview, I glanced over at the host’s monitor and noticed sticky notes prominently displaying remote access passwords to their terminal. After the segment, I mentioned this to the host who was embarrassed but thanked me for mentioning this as they quickly pulled them off the side of their monitor. It’s hard to remember a password, let alone dozens or more passwords across multiple devices or websites.
Occasionally, I like to go through all of my software apps and ask when is the last time I have used them. If I have not used it in the last few months, I simply delete them as they are no longer critical to my life or work. And that is also one less password to remember or manage. If you are not comfortable with documenting and locking up a small book of long/strong passwords, then I recommend you get a good password manager such as Dashlane.
STF: What are your deepest fears concerning big data and big data breaches?
Mr. Schober: Most people I have spoken to have a credit card compromised or their email hacked. I recently received a wave of phone calls and emails asking for assistance from colleagues who became victims of ransomware. I fear this will continue to plague computer and smart phone users in 2017. There are proactive steps everyone can take. There is some great software that offer whitelisting to allow only valid emails to come through. Everyone should take basic precautions and have a regular plan of backs ups for their important data in the event that they are a victim of ransomware. Ransomware will become more common than accidental deletion of files or hard drive failure so the same precautions apply.
My greatest fears are when hackers target critical infrastructure such as our power, water, electric, and sewage. We take these basic systems for granted it until we flip the switch and the light does not light up. Hackers, like terrorists, know this and play on our fears. Much of the critical infrastructure and smart grid have legacy systems in place which are easy hacking targets. This can be a security bonus because these older systems were not designed to be connected or controlled remotely. They lack the ease of interconnectivity which also means they lack multiple surfaces of attack and vulnerability that newer systems often possess. But the older systems eventually breakdown and will be replaced by newer ones so it is only a matter of time before governments and the private sector must come together to create more secure infrastructure.
STF: Best security practices for the home user?
Mr. Schober: Before any hacker would consider physically breaking into your home, most would opt to wirelessly hack your WiFi network. Protect your home network by changing the name of your WiFi network (also known as the SSID – Service Set Identifier). Do not use your family name or any address information in this SSID as this just makes a thief’s job that much easier. Always change the default name and password of any router to something unique and secure. When a hacker knows the router maker, they already have the first hack completed. All routers have their own set of known vulnerabilities that hackers share.
Always create a long, strong, and unique password for your wireless network with a minimum of 12 characters including upper case, lower case, numbers, and symbols. Never reuse the same password that you use for your wireless network anywhere else. It is recommended to create a long and strong administrator password to increase your WiFi security. Never leave the manufacturers default setting to ‘ADMIN’ which is an invitation for hackers to break in. Disable all remote access features unless you absolutely need them. Some routers enable these features by default. Hackers know which routers do this. Do you?
Related: Dr. Roman Yampolskiy: AI Has Tremendous Ability to Help in All Domains of Interest
Many people say they have nothing worth hacking, but hackers can steal more than just boring emails to family members. They can target your login credentials for banking, stock portfolio, life insurance, 401k, taxes, etc. All modern wireless networks come with multiple encryption built in so use it. WPA2 AES 128-bit level encryption should be a minimum.
I suggest physically placing the wireless router toward the center of your home increasing your coverage inside the house and minimizing the wireless foot print outside your house where hackers do their hacking. Not all routers are secure and new vulnerabilities surface so make sure you update firmware regularly. Some modern routers allow you to enable auto update which is a good idea if you are not inclined to regularly update. Also make sure your router has a built-in firewall by default. Check every device that you connect to your home network to make sure they have the latest security patches loaded.
STF: Online shopping may actually make our personal and banking information vulnerable to hackers. Do you have any recommendations for the active online shopper?
Mr. Schober: ONLY shop on sites that have ‘HTTPS’ in the URL. The ’S’ means that your private information is being sent securely. HTTPS uses SSL (or Secure Socket Layers) which means that your personal data is encrypted and much safer. Regularly update your internet browser. Hackers exploit older insecure browsers looking for vulnerabilities.
Do not click on attachments in emails no matter how convenient it makes them. Instead, type out the address in your browser to make sure you are going to the real website address. There are many phishing scams (especially during the holidays and shopping seasons) involving emails from what appears to be from legitimate sites.
Cyber hackers may have installed software key loggers into your PC to steal login credentials If you are an online shopper, I suggest you consider an ‘Anti-KeyLogger’. I use GuardedID for keystroke encryption software by Strikeforce. GuardedID will encrypted every keystroke to protect your data from key logging threats.
It is also a good practice to have a single credit card that you use for shopping on the internet only. Carefully monitor your statement on a regular basis to report any suspicious activity.
SensorsTechForum’s “Ask the Experts” Interview Series
If you are a cyber security expert and you want to share your experience with our audience, send us an email at support[at]sensorstechforum.com. We will gladly converse with you about anything cyber security!