Mobile biometrics have been on the rise since Apple released Touch ID in 2013. After its release, the global market for mobile biometrics has earned over $14 billion. To paint a better picture, 57% of today’s available apps feature a biometric login option.
Consumers are taking to the security transition very well; in fact, 70% feel biometrics are easier to use, and 46% feel biometrics are more secure. Mobile biometrics are now emerging into payment authentication, but are biometrics better than traditional security and PINs?
Related: Android P to Get Better Biometrics against Spoofing Attacks
In short, yes – which is excellent news since 48% of US consumers have already authenticated a payment with biometrics. This can be completed through the likes of Apple Pay, Google Pay, Cash App, or Venmo- 42% won’t even use banking apps that lack biometric authentication. Similarly, 63% want to use biometrics to authorize payments when shopping in-store. So, what is biometrics?
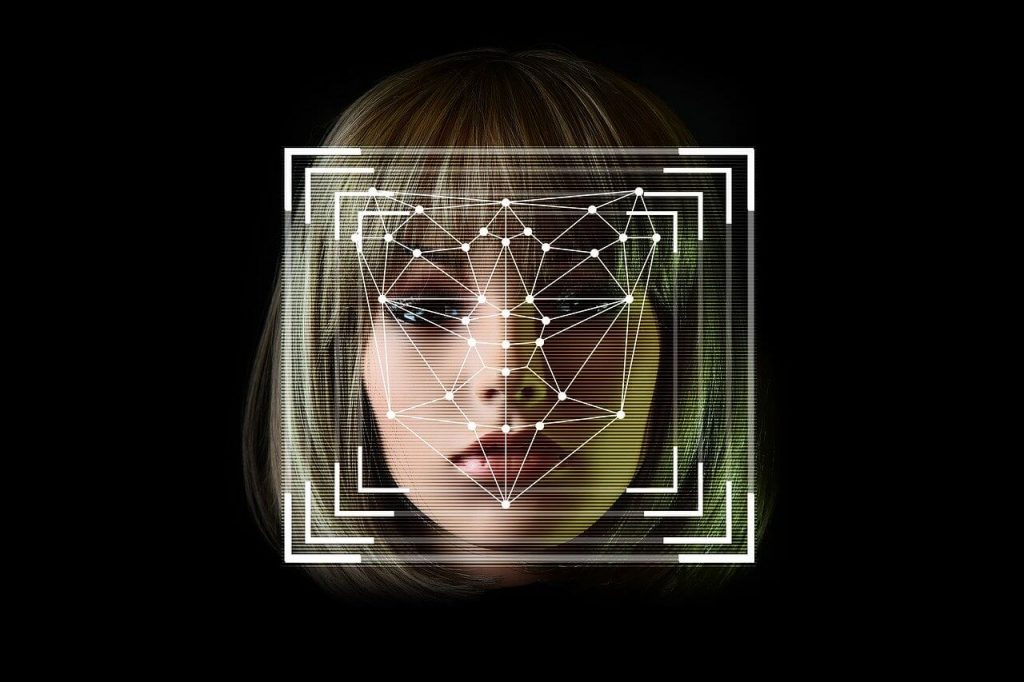
Defining Biometric Security
Biometric security uses human and behavior identifiers to recognize authorized users (typically the device owner) and detect imposters. The most common human or physical, marker used in biometric security is also the default American preference – fingerprints. 63% of Americans prefer to use fingerprint scanners over other physical marker software: facial recognition, retinal scans, and voice recognition. Biometric software can also identify your behavior identifiers or patterns. Such are gestures and finger movements, frequency of checking social media accounts, how a phone is tilted when it is held, and device usage patterns such as your time and location.
Previously it was mentioned that 46% of Americans feel biometrics are more secure, but that doesn’t make one’s device bulletproof. What makes biometrics more secure than PINs and traditional passwords? The answer: their difficulty to hack.
The Strength of Biometric Security
Biometric technology is not standardized, even by manufacturers. Each device requires a unique approach to use, requiring a unique approach to hack. A hacker would need to study the instruction manual on each device he or she wished to hack, slowing down the rate of frequency. In other words, biometrics are much more time consuming to hack than traditional passwords & PINs. Now, it is possible to fool a biometric security device, but creating a fake (mask, fingerprint) would require a large amount of user data. This is extremely difficult to obtain without being noticed by the biometric’s firewalls.
Instances Mobile Biometrics Have Been Tricked
Yet, there have been successful attempts in bypassing biometrics. Some Android devices can be tricked with just a photo- including many Samsung, Sony, and Motorola devices. Fingerprint scanners can also be easily fooled. Let’s tie this back into Samsung (whose facial recognition biometrics can also be tricked with photos). The Samsung Galaxy S10 features a new ultrasonic fingerprint sensor with a reputation of being harder to hack. The ultrasonic technology can be easily fooled by a 3-D printed fingerprint replication.
Family members can also trick biometrics. Siblings, a mother, son, and even distant cousin have been able to gain access to each other’s iPhones using the Face ID (facial recognition) software. Here’s how it works: After the Face ID fails to recognize an authorized user, it will request the phone’s password to continue. Unbeknown to most, if the passcode is entered correctly, the phone assumes it was at fault and this is the actual user. As a result, it will scan the user’s face to improve its recognition model. If favoring family members continue to do this, Face ID may eventually identify them as you over time.
Related: Taking Password Security to the Next Level Through Our Bodies
How To Maximize Your Device’s Security
Biometrics security is an ever growing field. The best way to lower your chances of becoming a statistic is to get the most of your biometric security. To do so is very simple- just get to know the limits of your biometrics. In addition to this, there are physical things you can do to ensure the safety of your device.
For starters, keep an eye on your device. Your tech is valuable, and biometrics cannot secure your phone if you leave it outside of your supervision while unlocked. Once you’ve unlocked your phone, tailgaters can easily swoop in and gain access to your information.
Along with this, be sure to choose the best tech before committing to a purchase. A good starting point would be to look for features that can’t be fooled by 3D print or photographs: 3D recognition and liveness detection.
There are also additional security measures within your phone that can be enabled. An example of this is 2-step authentication. Here’s how it works: you go to log into Facebook and enter your passcode as usual. Upon entering the correct passcode, 2-step authentication will prompt for another user verification method (a second passcode not in the form of a passcode). This is a great time to pair biometrics and PIN/passwords for tighter security, making it harder to spoof. While it is likely an imposter can gain knowledge of your password, it would be difficult for them to trick the biometric system.
The future of security is proving to be heavily biometric, and the rise of mobile biometrics should be a topic that mobile users discuss regularly.
About the Author: Demetrius Harrison
 Demetrius has been a tech-lover since 2013. Demetrius currently writes tech news for Robotics Business Review & 21stCenTech, and has also conducted hands-on ISEF research from 2013-2016. Recently, Demetrius found an interest in SEO tech and halfway through completing his undergraduate’s degree. In the meantime, he is the Jr. Promotions Specialist at NowSourcing, Inc- an premier, award-winning design agency. Connect with Demetrius @demeharrison on social sites.
Demetrius has been a tech-lover since 2013. Demetrius currently writes tech news for Robotics Business Review & 21stCenTech, and has also conducted hands-on ISEF research from 2013-2016. Recently, Demetrius found an interest in SEO tech and halfway through completing his undergraduate’s degree. In the meantime, he is the Jr. Promotions Specialist at NowSourcing, Inc- an premier, award-winning design agency. Connect with Demetrius @demeharrison on social sites.