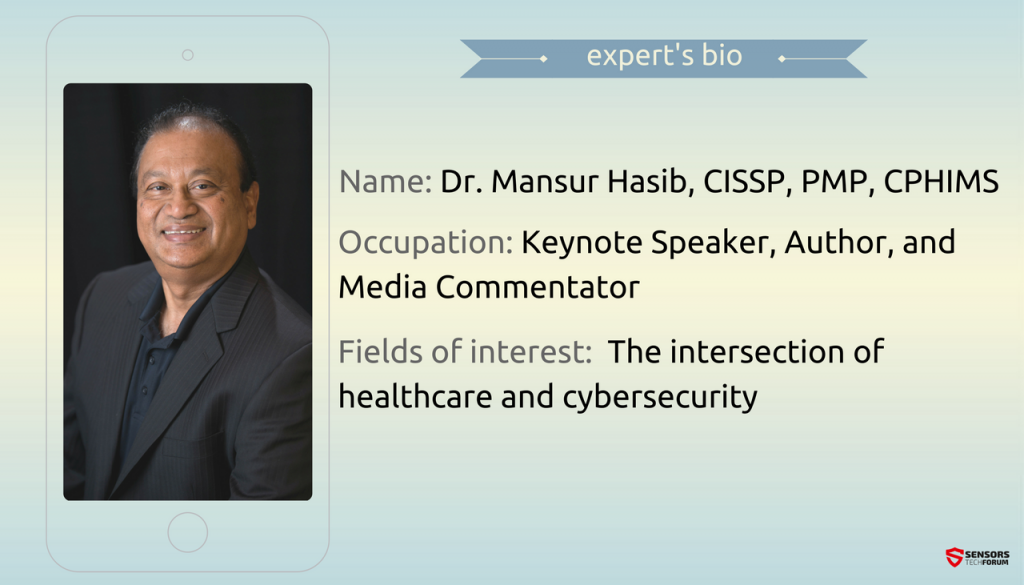
Dr. Mansur Hasib has been helping executives transform their organizations through digital leadership and cybersecurity strategy in healthcare, biotechnology, education, and energy. Dr. Hasib is a Doctor of Science in Cybersecurity (IA), and holds the prestigious CISSP, PMP, and CPHIMS certifications. He is also an author, speaker, and media commentator. His professional experience is a perfect mixture of theory and practice, as you can see from our conversation with him…
STF: How and why did you decide to dedicate your professional career to cybersecurity in healthcare?
Dr. Hasib: When I first started to implement cybersecurity strategy as an organization’s digital strategy, it was simply to modernize organizations, run all the business functions efficiently, create value for the organization, reduce costs, make paper records searchable and accessible by appropriate people. I also focused on proper training of people in the use of the technology I was implementing.
Related: Dr. Vesselin Bontchev: Non-Replicating Malware Has Taken over the Computer Virus
I always felt that the power of technology is not in the technology itself but by how innovative and productive it made people. Training people on technology simply felt like the right thing to do and I discovered that by focusing on people and their use of technology, I was creating intellectual capital for the organization. Cybersecurity was not a word then and it was not taught at any college. People often confuse cybersecurity as pure network protection.
I view cybersecurity as a way to drive innovation and productivity in an organization. To me, cybersecurity is people powered perpetual innovation. That is how I teach cybersecurity.
The push to electronic health records started around 2003/2004 and then accelerated during 2009/2010. I felt that electronic health records, health information exchanges, artificial intelligence engines could play a major role in reducing the annual half a million medical error and misdiagnosis related deaths in the US. Healthcare has been slow to adopt the appropriate governance structures needed to implement technology properly – for example about half of US healthcare IT and cybersecurity is run by Chief Financial Officers or other similar officers. Healthcare desperately needs to hire and empower IT and cybersecurity executives.
Related: Dr. Roman Yampolskiy: AI Has Tremendous Ability to Help in All Domains of Interest
With my passion and experiences in these fields, I felt I could help build a new breed of executive leaders required to make organizations successful.
STF: In your experience, what is the biggest problem that healthcare institutions deal with (in terms of cyber attacks)?
Dr. Hasib: The biggest problem is the reluctance of the finance executives to hire and empower the right cybersecurity executives who would implement a proper cybersecurity strategy. During my national survey in 2013 I found IT and cybersecurity being run by finance and other similar non-IT executives in half the US healthcare organizations. One third had no Chief Information Security Officer and about a fifth had no plans to hire one anytime soon.
STF: Tell us the story of a breached healthcare record. What is the worst case scenario?
Dr. Hasib: The worst breach in healthcare so far was at Anthem where over 80 million records (including mine) were breached. The worst case scenario is that many people were minors at the time of the breach and it may take years for them to find out the extent of damage. Credit monitoring for a limited time does not protect the people who were damaged.
STF: What is a good incident response program? What in your opinion is the best way to detect and respond to healthcare breaches?
Dr. Hasib: Better incident response plans combine several things: automated responses, artificial intelligence, analytics of all the data from suspicious incident logs, response prior to any damage caused to actual data, use of honeypots and honeydata to observe and learn about the malicious actors. The best response is to ensure that the data even if breached will be useless outside a context. Organizations should ensure data self-destruct or become useless when moved outside an authorized context.
STF: What should be included in a security awareness program?
Dr. Hasib: Most security awareness programs are obsolete and useless. Training needs to be specific to job roles and go well beyond simple awareness training. Training needs to be related to the data and the systems used by people. Training needs to ensure that people use data and systems safely and know how to recognize and solve problems on their own.
Related: Scott Schober: Hackers, Like Terrorists, Play on Our Fears
STF: What are your darkest expectations for the security of the healthcare sector?
Dr. Hasib: I expect the spate of breaches to continue until a new breed of ethically inclined and digitally informed executive leaders focused on doing the right thing for customers, employees, and members of the public are placed in charge at the top levels of healthcare organizations.
STF: What is your opinion on biometrics? Will biometric checks worsen or improve the security of our lives?
Dr. Hasib: Implemented improperly biometrics can actually reduce security. We do need to have solid authentication and authorization systems and biometrics alone is not the answer. However, combined with some other form of one-time authentication code which rely on something a person knows and is not written or stored anywhere, biometrics may help increase ease of use.
STF: Do you have a favorite cybersecurity quote or motto to guide you in both your personal and business life?
Dr. Hasib: Knowledge in our head is completely useless. Its power is unleashed only when it is shared. Sharing our knowledge does not diminish it in any way. So we should share what we know and learn from others what they know. This is the key to implementing a perpetual innovation culture in our personal and business lives.
STF: And finally: Any advice on how to protect our personal information, including healthcare records? Could we do something to be more secure, or is it entirely up to organizations?
Dr. Hasib: We can choose to do business with and reward organizations who can protect our information better. We can choose to limit what we share with any organization. We have the right to have a view to the information stored about us as well as its use, storage, and sharing. We can work with our legislators to ensure that appropriate data protection laws exist and organizational executives are held accountable for appropriate protection of public data they are entrusted with.
Related: Raef Meeuwisse: Criminals Share Information Better and Faster than Legitimate Organizations
SensorsTechForum’s “Ask the Experts” Interview Series
If you are a cyber security expert and you want to share your experience with our audience, send us an email at support[at]sensorstechforum.com. We will gladly converse with you about anything cyber security!