Another day, another breach. Brian Krebs just reported that Verifone, the largest manufacturer of credit card terminals in the US, is currently investigating a breach of its internal networks. These computer networks appear to have been limited to Verifone’s corporate network, and the payment services network doesn’t seem to have been impacted.
According to Krebs:
Credit and debit card payments giant Verifone [NYSE: PAY] is investigating a breach of its internal computer networks that appears to have impacted a number of companies running its point-of-sale solutions, according to sources. Verifone says the extent of the breach was limited to its corporate network and that its payment services network was not impacted.
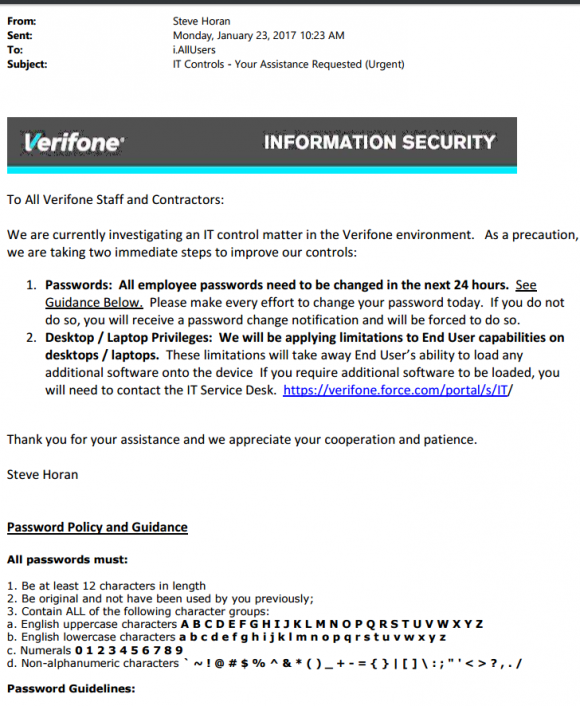
Verifone Warns of Intrusion, Limits Desktop/Laptop Privileges
On January 23 this year, the company sent an urgent message to all company staff and contractors, giving out a warning that all company passwords had to be changed within 24 hours. The memo was penned by Steve Horan, Verifone’s senior VP and Chief Information Officer. “We are currently investigating an IT control matter in the Verifone environment”, he said in the memo. “As a precaution, we are taking immediate steps to improve out controls,” he added.
Related: U.S. Survey Reveals Troublesome Details About Medical Data Breaches
The memo also warns that desktop/laptop privileges would be affected and the company will be applying limitations to the End User capabilities on those devices. The limitations would take away the employee’s ability to download additional software onto the device. In case additional software was needed, the user would have to contact the IT Service Desk:
The limitations suggest that the breach might have something to do with malware downloaded onto company’s devices. Is that the case?
This is what Verifone’s spokesperson commented:
In January 2017, Verifone’s information security team saw evidence of a limited cyber intrusion into our corporate network. Our payment services network was not impacted. We immediately began work to determine the type of information targeted and executed appropriate measures in response. We believe today that due to our immediate response, the potential for misuse of information is limited.
The information available also indicates that the incident had an impact on a customer support unit in Florida. The unit provides payment solutions to gas and petrol stations, and the products it offers include pay-at-the-pump credit card processing, cash registers for the fuel station, etc. This fact alone makes the intrusion more dangerous than Verifone would like us to believe.
Related: Privacy Service Keeps Debit Cards Anonymous. For Free
A later update given by the company and quoted by Krebs reads the following:
According to the forensic information to-date, the cyber attempt was limited to controllers at approximately two dozen gas stations, and occurred over a short time frame. We believe that no other merchants were targeted and the integrity of our networks and merchants’ payment terminals remain secure and fully operational.