A very intriguing and intensive DDoS/botnet attack has been just investigated by security researchers at US security vendor Sucuri. The botnet in question comprises of more than 25,000 bots targeting businesses at a global level. More specifically, it’s a Layer 7 DDoS attack that engulfs web servers and crashes their websites. The attacks continued for days. The more researchers dived into their analysis, the more curious details they found.
As we extracted the geo-location from the IP addresses generating the DDoS, we noticed that they were coming from all over the world, different countries and networks. A total of 25,513 unique IP addresses came within a couple of hours.
What Did Sucuri Researchers Discover About the Attacks?
The research indicates that the botnet consists of compromised international CCTV systems situated in various locations around the globe. The first collision Sucuri had with the botnet happened when a jewelry shop was put through a continuous DDoS attack. The business’s website was moved behind Sucuri’s WAF (Web Application Firewall).
However, things didn’t end there, as the attacks continued. Like we already said, the initial attack was a Layer 7 DDoS one (with more than 35,000 HTTP requests per second). Attacker quickly noticed the WAF protection and speeded things up to 50,000 requests/ second.
The source of the attack concentrated in Taiwan, with 24% of the IP address, followed by the USA with 12%, Indonesia with 9%, Mexico with 8% and Malaysia with 6%. The top 10 countries with the most compromised CCTV devices used in this attack were: Taiwan, USA, Indonesia, Mexico, Malaysia, Israel, Italy, Vietnam, France.
IoT Botnet Leveraging CCTVs?
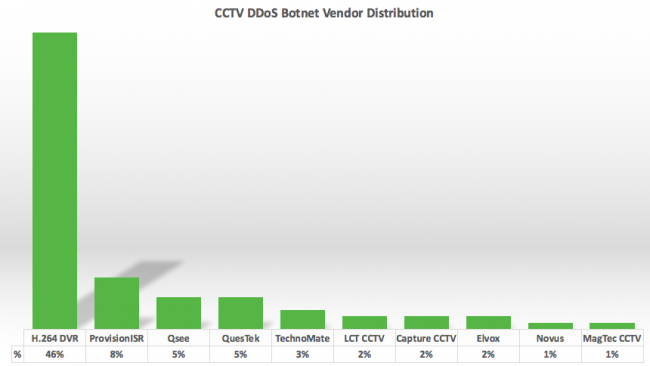
As the research went deeper into the IP addresses, it became clear that all of them were running the Cross Web Server, and all had a similar default HTTP page, containing a DVR Components title. This is when researchers came to realize that they were most likely dealing with an IoT botnet leveraging CCTVs as part of the attack vector. Further, they uncovered the company logos from the resellers and manufactures on all of the IP addresses.
Sucuri believes that all of the devices are associated with RSA security researcher Rotem Kerner Rotem Kerner’s investigation that discovered a backdoor in the firmware of 70 CCTV DVR vendors.
Sucuri is currently in the process of contacting the networks that use the compromised cameras. However, even when affected cameras are patched, attackers can easily find other devices to include in their botnets. That’s why companies should think of adequate DDoS protection.