Cross-site scripting (XSS) is nothing to take lightly. As simultaneously the most prevalent and overlooked security vulnerability around today, this type of breach affects the way your pages load, makes it easier to steal financial and other data, or could allow a hacker to hijack an identity while a session is active.

The most effective approach is to make sure your website, landing page, blog, and social media accounts are protected in advance. If you are serious about guarding against XSS incursions, check out the following strategies.
1. Learn the Security Development Lifecycle
You’re probably familiar with the concept of a security development lifecycle and how SDL can help to protect websites and pages of all types. The idea was developed within Microsoft early in the current century and was declared mandatory for all Microsoft products by 2004. Others also began to develop their own approaches to SDL and included this in the bundle for their products.
How does this relate to dealing with XSS threats? It’s simple. You should learn what sort of SDL protections are found in any software product you buy. Whether you pick it up at a local office supply store or download software from a supplier, understand the security already inherent in the bundle.
You want to know what the software does in terms of identifying and dealing with vulnerabilities that may already be present on your pages. If the manufacturer offers no (or limited) protection, see a similar product from another source.
2. Whitelisting Is Your Friend
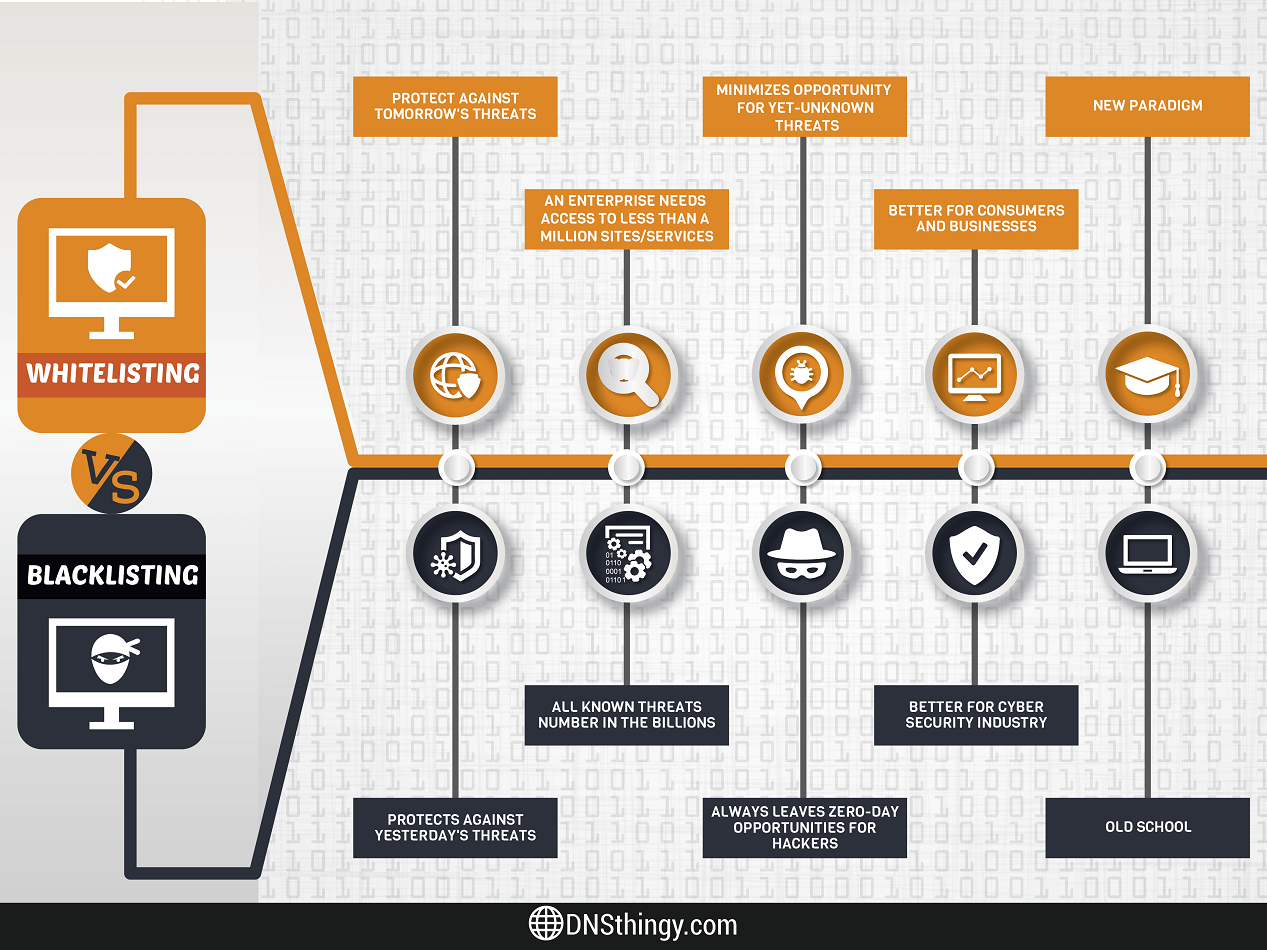
Blacklisting gets a lot of attention, and it is an important strategy for protecting your website and other pages from XSS attacks and other threats. Whitelisting is also something you need to take seriously. At its core, whitelisting is about identifying applications and data as being safe and trustworthy>.
It may have to do with the code used to create the application, the reputation of the source, or the way that formatting is used. In every case, the goal is to make sure that any application or element that’s active is free from any type of threats.
Pair whitelisting with blacklisting. This approach ensures that each application is scanned and deemed safe before it launches. If a problem is detected, blacklisting will ensure that the application does not launch and that data is not transferred to an unauthorized party. When no threats are found, whitelisting supports the launch of the application and you don’t have to worry about a threat allowing a third party to hijack or alter data as it’s shared.
Remember that though you can prevent a lot of trouble by pairing these two, don’t consider yourself safe. Hackers have a way of getting around any protection effort eventually. You should deploy additional strategies for maximum hack repellent.
Related: Google Releases 2 New Dev Tools to Protect against XSS
3. Pay Attention to Meta Tag Creation
Meta tags are great. They provide an idea of what sort of content is on a page and what the page has to offer. The tags are often displayed by search engines in the form of a description. That’s one reason to pay close attention to how you create meta tags and meta descriptions. You want to motivate people to visit your pages.
There’s another reason to think about the way you create meta tags. They can be injected with infections, worms, and viruses just like other element. A resourceful hacker can place XSS in your tags if there is any slight flaw in how you structure them. If you are not sure how to make them harder to breach, get help from a professional. It’s worth the cost.
4. Implement a Crossing Boundaries Policy Now
Some people have the mistaken impression that using a virtual private network will protect your data against XSS attacks. Think again. Even the ostensibly best VPNs will protect you from a great many cyberattacks, but they are not necessarily going to help much with XSS. This is where the idea of a crossing boundaries policy comes into the picture.
A crossing boundaries policy qualifies data from different sources before it can be used. That includes data found in a sub-folder or data that is received via some sort of transmission. Consider it one way to check the trust factor of data before it can proliferate throughout your pages.
Use software, manual check points, or whatever combination you want. The point is establishing one more line that potentially dangerous data has to cross before it’s actually used.
5. Regular Use of a Vulnerability Scanner
Vulnerability scanners make it easier to identify potential points in your network or within software applications that could be exploited. That includes all your devices, including telecommunication equipment.
It also includes checking phishing emails that might get past your email client’s spam settings or defenses. See the scanner as one more way to be prepared in advance for something your other defenses may miss.
6. Sanitize User Input
ImageSource: Heimdal
Email-based attacks are alive and well. In some ways, they are more popular than ever since so many people receive email on phones and tablets as well as desktop and laptop systems. The same threats could be embedded in links or other input users enter in blog or social media comments.
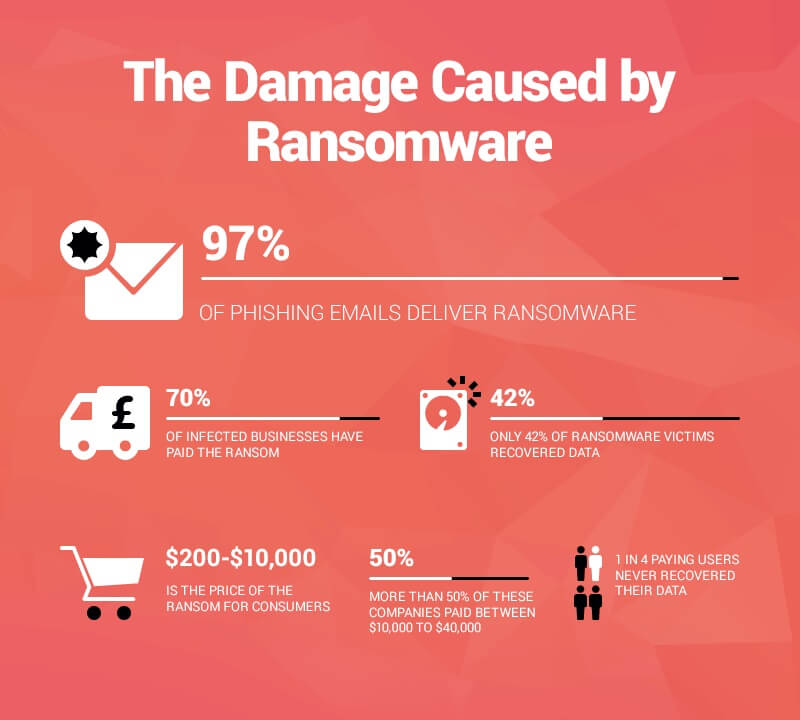
That’s one reason you want some means of checking and sanitizing user input found in template style emails or what appears to be a legitimate comment on a post. There could be code present that contains Trojans or some type of ransomware.
Remember, applications that protect and check user input on ordering pages, comment sections of blogs, and even responses to social media posts are available. Since each of these could be a point of exploitation via the injection of XSS, invest in an application that creates a means of stopping and containing the threat.
The Bottom Line
Dealing with XSS is an ongoing process. What worked fine five years ago may not offer the same level of protection today. Update your applications, browsers, and the version of the software you use to manage your blog and website. If you are able to stop a single threat, all the effort is worth it.
About the Author: Sam Bocetta
 Sam Bocetta is a former security analyst for the DoD, having spent 30+ years bolstering Cyber defenses for the Navy. He is now semi-retired, and educates the public about security and privacy technology.
Sam Bocetta is a former security analyst for the DoD, having spent 30+ years bolstering Cyber defenses for the Navy. He is now semi-retired, and educates the public about security and privacy technology.

