 STF researchers have already reported about URL:Mal detected in svchost.exe. The number of affected users has increased, as visible by their complaints. However, it is now known that the infection is associated with the URL wpad.browserupdatecheck.in/wpad.dat. Keep in mind that other URLs may also be used by URL:Mal. URL:Mal has been detected by Avast.
STF researchers have already reported about URL:Mal detected in svchost.exe. The number of affected users has increased, as visible by their complaints. However, it is now known that the infection is associated with the URL wpad.browserupdatecheck.in/wpad.dat. Keep in mind that other URLs may also be used by URL:Mal. URL:Mal has been detected by Avast.
URL:Mal and https://wpad.browserupdatecheck.in/wpad.dat Description
wpad.browserupdatecheck.in/wpad.dat may be able to download and run a WPAD file and compromise the system’s security. The suspicious file may have entered the system via fake browser or program updates, often brought by adware and PUPs.
Read more about URL:Mal and svchost.exe.
What is WPAD?
WPAD stands for Web Proxy Auto-Discovery Protocol. It is a method that is usually used by clients to locate the URL of a configuration file. However, WPAD can turn into an issue despite the fact its primary purpose is to simplify browser configurations. When mistakes happen, the WPAD can open a door on the system and let attackers in.
Even though more details are needed to confirm the way URL:Mal works, users should proceed towards scanning and protecting their systems.
According to one research, the WPAD file works as a scanner that aims to find the system’s vulnerabilities and exploit them once they are unveiled.
How Does wpad.browserupdatecheck.in/wpad.dat Work?
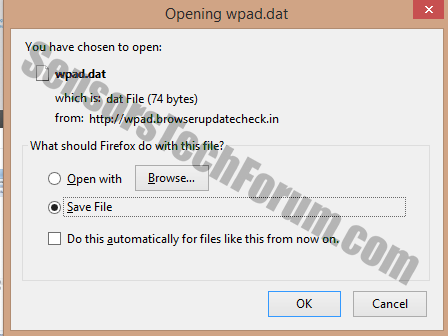
If the URL is opened in the browser, the user will encounter a pop-up window tricking the user into downloading it. Once installed, the PC’s performance will worsen drastically. The user may also start experiencing suspicious browser redirects.
How to Proceed If Affected by wpad.browserupdatecheck.in/wpad.dat?
Considering the aggressive behavior of wpad.dat and its high infection rates, a powerful AV solution is needed to eliminate it completely from the system. Several helpful steps are available below the article.

Spy Hunter scanner will only detect the threat. If you want the threat to be automatically removed, you need to purchase the full version of the anti-malware tool.Find Out More About SpyHunter Anti-Malware Tool / How to Uninstall SpyHunter
Preparation before removing wpad.browserupdatecheck.in/wpad.dat and wpad.dat.
Before starting the actual removal process, we recommend that you do the following preparation steps.
- Make sure you have these instructions always open and in front of your eyes.
- Do a backup of all of your files, even if they could be damaged. You should back up your data with a cloud backup solution and insure your files against any type of loss, even from the most severe threats.
- Be patient as this could take a while.
- Scan for Malware
- Fix Registries
- Remove Virus Files
Step 1: Scan for wpad.browserupdatecheck.in/wpad.dat and wpad.dat with SpyHunter Anti-Malware Tool



Step 2: Clean any registries, created by wpad.browserupdatecheck.in/wpad.dat and wpad.dat on your computer.
The usually targeted registries of Windows machines are the following:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
You can access them by opening the Windows registry editor and deleting any values, created by wpad.browserupdatecheck.in/wpad.dat and wpad.dat there. This can happen by following the steps underneath:


 Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.Step 3: Find virus files created by wpad.browserupdatecheck.in/wpad.dat and wpad.dat on your PC.
1.For Windows 8, 8.1 and 10.
For Newer Windows Operating Systems
1: On your keyboard press + R and write explorer.exe in the Run text box and then click on the Ok button.

2: Click on your PC from the quick access bar. This is usually an icon with a monitor and its name is either “My Computer”, “My PC” or “This PC” or whatever you have named it.

3: Navigate to the search box in the top-right of your PC's screen and type “fileextension:” and after which type the file extension. If you are looking for malicious executables, an example may be "fileextension:exe". After doing that, leave a space and type the file name you believe the malware has created. Here is how it may appear if your file has been found:

N.B. We recommend to wait for the green loading bar in the navigation box to fill up in case the PC is looking for the file and hasn't found it yet.
2.For Windows XP, Vista, and 7.
For Older Windows Operating Systems
In older Windows OS's the conventional approach should be the effective one:
1: Click on the Start Menu icon (usually on your bottom-left) and then choose the Search preference.

2: After the search window appears, choose More Advanced Options from the search assistant box. Another way is by clicking on All Files and Folders.

3: After that type the name of the file you are looking for and click on the Search button. This might take some time after which results will appear. If you have found the malicious file, you may copy or open its location by right-clicking on it.
Now you should be able to discover any file on Windows as long as it is on your hard drive and is not concealed via special software.
wpad.browserupdatecheck.in/wpad.dat and wpad.dat FAQ
What Does wpad.browserupdatecheck.in/wpad.dat and wpad.dat Trojan Do?
The wpad.browserupdatecheck.in/wpad.dat and wpad.dat Trojan is a malicious computer program designed to disrupt, damage, or gain unauthorized access to a computer system. It can be used to steal sensitive data, gain control over a system, or launch other malicious activities.
Can Trojans Steal Passwords?
Yes, Trojans, like wpad.browserupdatecheck.in/wpad.dat and wpad.dat, can steal passwords. These malicious programs are designed to gain access to a user's computer, spy on victims and steal sensitive information such as banking details and passwords.
Can wpad.browserupdatecheck.in/wpad.dat and wpad.dat Trojan Hide Itself?
Yes, it can. A Trojan can use various techniques to mask itself, including rootkits, encryption, and obfuscation, to hide from security scanners and evade detection.
Can a Trojan be Removed by Factory Reset?
Yes, a Trojan can be removed by factory resetting your device. This is because it will restore the device to its original state, eliminating any malicious software that may have been installed. Bear in mind that there are more sophisticated Trojans that leave backdoors and reinfect even after a factory reset.
Can wpad.browserupdatecheck.in/wpad.dat and wpad.dat Trojan Infect WiFi?
Yes, it is possible for a Trojan to infect WiFi networks. When a user connects to the infected network, the Trojan can spread to other connected devices and can access sensitive information on the network.
Can Trojans Be Deleted?
Yes, Trojans can be deleted. This is typically done by running a powerful anti-virus or anti-malware program that is designed to detect and remove malicious files. In some cases, manual deletion of the Trojan may also be necessary.
Can Trojans Steal Files?
Yes, Trojans can steal files if they are installed on a computer. This is done by allowing the malware author or user to gain access to the computer and then steal the files stored on it.
Which Anti-Malware Can Remove Trojans?
Anti-malware programs such as SpyHunter are capable of scanning for and removing Trojans from your computer. It is important to keep your anti-malware up to date and regularly scan your system for any malicious software.
Can Trojans Infect USB?
Yes, Trojans can infect USB devices. USB Trojans typically spread through malicious files downloaded from the internet or shared via email, allowing the hacker to gain access to a user's confidential data.
About the wpad.browserupdatecheck.in/wpad.dat and wpad.dat Research
The content we publish on SensorsTechForum.com, this wpad.browserupdatecheck.in/wpad.dat and wpad.dat how-to removal guide included, is the outcome of extensive research, hard work and our team’s devotion to help you remove the specific trojan problem.
How did we conduct the research on wpad.browserupdatecheck.in/wpad.dat and wpad.dat?
Please note that our research is based on an independent investigation. We are in contact with independent security researchers, thanks to which we receive daily updates on the latest malware definitions, including the various types of trojans (backdoor, downloader, infostealer, ransom, etc.)
Furthermore, the research behind the wpad.browserupdatecheck.in/wpad.dat and wpad.dat threat is backed with VirusTotal.
To better understand the threat posed by trojans, please refer to the following articles which provide knowledgeable details.


