We have just received reports that a team of researchers discovered a new variation of the Spectre CPU bug known as the SplitSpectre CPU Vulnerability. It allows malicious users to hijack sensitive data vi the same speculative execution approach as the Spectre bugs.
The SplitSpectre Vulnerability is a Variation of the Spectre Bug
A team of researchers from Northeastern University and researchers from IBM have discovered a new variation of a speculative execution bug, the first of which was Spectre. The problem has been found to be within the way CPUs are designed. As with the prior Spectre variants the execution of processes is an optimization process which is designed to run the applications faster. This particular case has been found to be distinct from Spectre as it operates using a different attack scenario.
SplitSpectre is reported to be far easier to execute than the Spectre attacks. It requires a certain “gadget” (victim code) to be executed on the target machine. Three components are required in order to carry out the intrusions: a conditional branch on a variable, a first array access token using this variable and a second array access which uses the result of the first array access. What this means is that malicious code available on the target machine can trigger the exploit. In the demonstration the SplitSpectre attack used a browser-like setting with an untrusted JavaScript code. This allowed the hackers to successfully extract sensitive information. This also allows for input fields in browser windows. What this means is that the following attack scenarios are following:
- Field Manipulation — While the users are entering in form data the information can interactively be changed without them noticing.
- Sensitive Data Theft — This speculative execution behavior can be used to successfully hijack sensitive information such as login information.
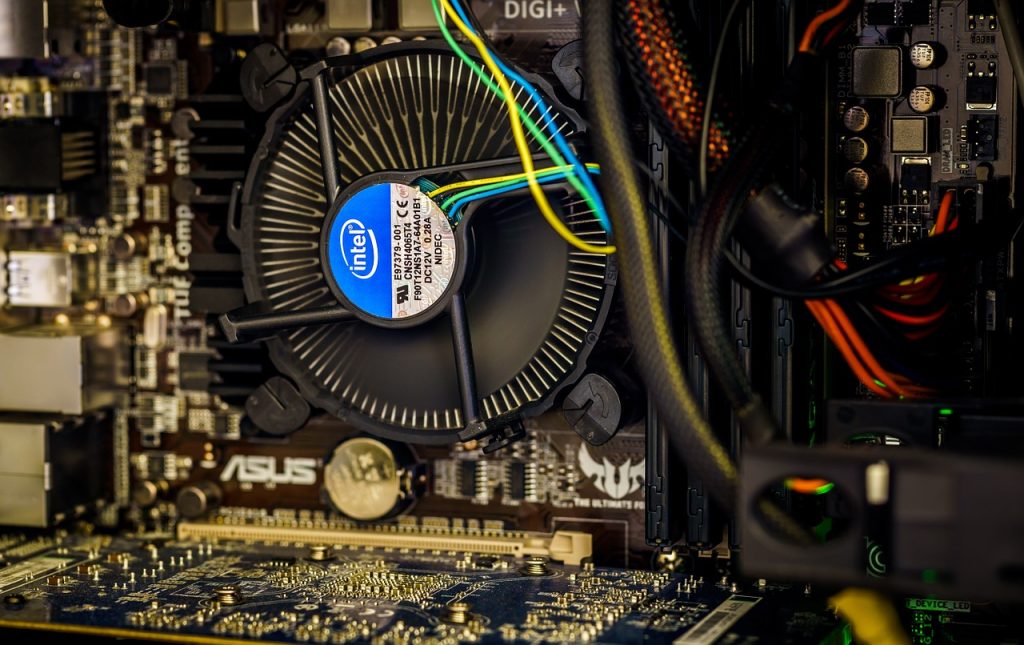
At the moment it has been confirmed that it targets Intel Haswell and Skylake processors, along with the AMD Ryzen models. The demonstrations were done using SpiderMonkey 52.7.4 which is Firefox’s JavaScript engine. hat’s dangerous is that the intrusions are based on a hardware design flaw and cannot be countered by a software applications or service. The only way to protect the machines is to apply the necessary patches. The researchers note that the existing mitigation for the main Spectre vulnerability. For more information into the issue the report has been published online.


