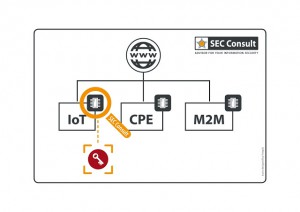
 A new research on 4000 devices from 70 different vendors reveals the alarming reuse of private keys. The research has been led by Stefan Viehböck from SEC Consult. The senior security consultant has investigated the HTTPS certificates and SSH keys of embedded devices such as Internet gateways, modems, routers, IP cameras, VoIP phones. The results showed that 580 unique crypto keys were being re-shared among firmware images, particularly for SSH host keys and X.509 HTTPS certificates.
A new research on 4000 devices from 70 different vendors reveals the alarming reuse of private keys. The research has been led by Stefan Viehböck from SEC Consult. The senior security consultant has investigated the HTTPS certificates and SSH keys of embedded devices such as Internet gateways, modems, routers, IP cameras, VoIP phones. The results showed that 580 unique crypto keys were being re-shared among firmware images, particularly for SSH host keys and X.509 HTTPS certificates.
The ‘recycling’ of cryptographic keys is the heart of the problem
The SEC Consult research team used device scanning services such as Scans.io and Censys.io to go through multiple Internet-connected devices. The first amazing discovery was that 5% of the detected HTTPS hosts shared the same private keys represented by approximately 150 server certificates. The latter were distributed across the staggering 3.2 million hosts.
Must Read:
9271 Vulnerabilities Revealed in 1925 Firmware Images
Another peculiar discovery – the same problem was found in SSH keys. 6% of the SSH hosts shared private keys in the form of approximately 80 SSH host keys distributed across almost 1 million hosts.
Who is to blame for the ‘recycling’ situation?
According to the researchers, the blame is placed somewhere between the vendor and the product itself. There are companies ‘caught at the crime scene’, or in other words, found to reuse encryption keys. Here is the ‘short’ list:
ADB, AMX, Actiontec, Adtran, Alcatel-Lucent, Alpha Networks, Aruba Networks, Aztech, Bewan, Busch-Jaeger, CTC Union, Cisco, Clear, Comtrend, D-Link, Deutsche Telekom, DrayTek, Edimax, General Electric (GE), Green Packet, Huawei, Infomark, Innatech, Linksys, Motorola, Moxa, NETGEAR, NetComm Wireless, ONT, Observa Telecom, Opengear, Pace, Philips, Pirelli , Robustel, Sagemcom, Seagate, Seowon Intech, Sierra Wireless, Smart RG, TP-LINK, TRENDnet, Technicolor, Tenda, Totolink, unify, UPVEL, Ubee Interactive, Ubiquiti Networks, Vodafone, Western Digital, ZTE, Zhone, ZyXEL.
Why is this reuse of crypto keys dangerous?
In a nutshell, malicious actors can easily accomplish man-in-the-middle attacks as well as passive decryption attacks. Things can get pretty ugly because of the diversity of embedded devices. The attack can take place at an Autonomous System ISP level or on any Internet-connected device found in people’s homes. Any such device can be exploited because of its open SSH port.
References
ScMagazine
SoftPedia
SecConsult


