CVE-2019-6340: A New Highly Critical Flaw in Drupal
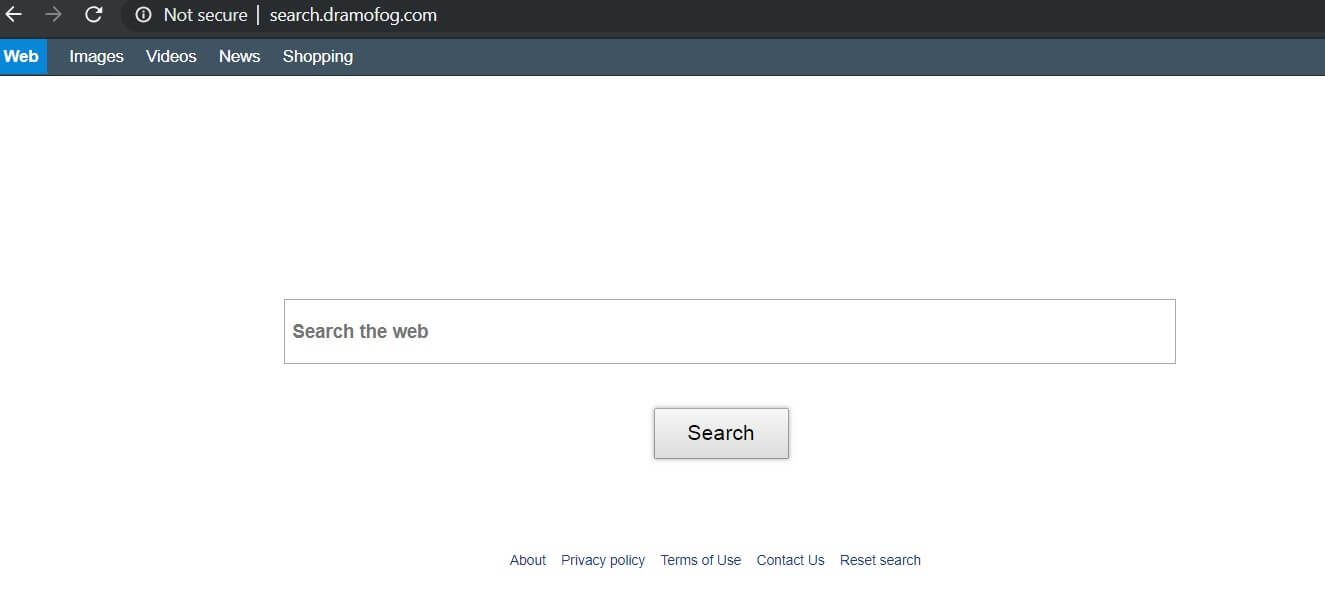
A new highly critical vulnerability, identified as CVE-2019-6340, was just discovered in Drupal, and luckily it’s already fixed in the latest version of the content management system. If you are running Drupal 7, no core update is required, but you…