 Bitdefender security researchers have discovered a clickbot, dubbed Redirector.Paco which has continuously abused companies’ Google advertising revenues. Cristina Vatamanu, Răzvan Benchea, and Alexandru Maximciuc have discovered that the botnet’s start of activity dates back to September 2014. Since then, over 900,000 computers have been affected. Victims are located in India, Malaysia, Greece, and the USA.
Bitdefender security researchers have discovered a clickbot, dubbed Redirector.Paco which has continuously abused companies’ Google advertising revenues. Cristina Vatamanu, Răzvan Benchea, and Alexandru Maximciuc have discovered that the botnet’s start of activity dates back to September 2014. Since then, over 900,000 computers have been affected. Victims are located in India, Malaysia, Greece, and the USA.

How Does Redirector.Paco Function?
The malware’s purpose is to redirect all traffic displayed when using a popular search engine like Google, Yahoo, and Bing. The clickbot aims to replace the results with such obtained from a Google custom search, so that fraudsters earn money from the AdSense platform.
Learn More about Recent Spam Botnet Campaigns
Google’s AdSense for Search program situates ads on Custom Search Engine’s search result pages, and then splits some of its ad revenue with AdSense partners. The malicious clickbot redirects that traffic by tweaking the registry of the victim’s machine. Here’s what Redirector.Paco does:
It modifies the “AutoConfigURL” and “AutoConfigProxy” values from the “Internet Settings” registry key so that for every request that a user makes, a PAC (Proxy auto-config) file will be queried. This file tells the browser to redirect the traffic to a different address.
How to Recognize the Fraud Activity?
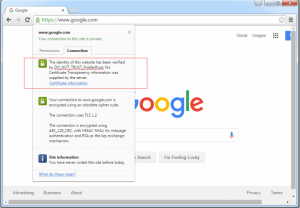
The clickbot also attempts to make the search results credible. However, an experienced eye may spot details in some occasions that would give away the true nature of the results. As explained by Bitdefender’s research trio, those signs include:
- Messages like “waiting for proxy tunnel” or “downloading found in the browser’s status bar;
- The Google page may take an unusually long time to load;
- The clickbot doesn’t display the usual yellow ‘o’ characters above the page numbers.
Users should also know that Redirector.Paco resides in compromised software bundles such as Youtube Downloader, pirated versions of WinRAR, KMSpico, and Stardock Start. Freeware and pirated software are often associated with malware infestations. That being said, the best way to stay away from any malware is avoiding freeware pages, and sustaining strong anti-malware protection.
Here’s the full technical overview of Redirector.Paco.
Spy Hunter scanner will only detect the threat. If you want the threat to be automatically removed, you need to purchase the full version of the anti-malware tool.Find Out More About SpyHunter Anti-Malware Tool / How to Uninstall SpyHunter


