 Snake Ransomware was discovered by MalwareHunterTeam last week who shared it with Vitali Kremez to reverse engineer and learn more about the infection.
Snake Ransomware was discovered by MalwareHunterTeam last week who shared it with Vitali Kremez to reverse engineer and learn more about the infection.
A new ransomware was recently discovered by MalwareHunterTeam researchers. Dubbed Snake ransomware, the threat was reverse engineered by Vitali Kremez. Thanks to him, now more details are available about Snake, which is considered a targeted type of ransomware deployed against organizations and enterprises.

Threat Summary
| Name | Snake ransomware |
| File Extension | A 5-character string to each file’s extension. |
| Type | Ransomware, Cryptovirus |
| What Is It | A ransomware that specifically targets networks of organizations. |
| Symptoms | Specific files are encrypted. In each encrypted file, the EKANS file marker will be added. |
| Ransom Note | Fix-Your-Files.txt |
| Distribution Method | Currently not known |
| Removal | To effectively remove active Snake ransomware virus infections, we recommend that you use an advanced anti-malware tool. Download
Malware Removal Tool
|
User Experience | Join Our Forum to Discuss Snake ransomware. |
| Data Recovery Tool | Windows Data Recovery by Stellar Phoenix Notice! This product scans your drive sectors to recover lost files and it may not recover 100% of the encrypted files, but only few of them, depending on the situation and whether or not you have reformatted your drive. |
New information regarding the Snake ransomware became available this month. According to a new sample analysis that was posted this month (January 2020) more detailed information about the targets and the behavior exhibited by the engine. The latest versions of the ransomware are heavily obfuscated and appear to be designed specifically to take down entire networks rather than individual computers. The files which are detected as Snake ransomware samples appear to be configured against industrial systems.
The Snake virus now includes several advanced functions which will be triggered once a host is infected. Among them are the following capabilities:
- Data Removal — The Snake ransomware has been found to delete any found Shadow Volume Copies of files found on the contaminated computer. This will make data recovery much more difficult and may hinder some restore operations.
- Process Control — The Snake virus engine will be able to scan for running processes of software which can block the ransomware — virtual machines, access systems, remote control tools, network management, anti-virus software and etc.
- Sabotage — Important SCADA systems and other industrial control software will be stopped from running. When this step has run in a working production environment this can cause a big overall issue in the factory which can be labeled as industrial sabotage.
- Encryption Control — During the ransomware encryption process the analysts have discovered that the engine will skip files that belong to the operating system. This is intentional in order not to corrupt the running systems. This ensures that the proper damage is done and that the victim users will be aable to review the posted ransom message.
Further investigation into the hacking group behind the Snake ransomware reveals that the criminals may be behind other dangerous attacks as well. Of particular note is the possibility that they have launched an attack with a disk wiper called ZeroCleare in the past. This was a highly sophisticated and devastating planned operation against industrial and energy organizations in the Middle East region.
Further information about the threat became available on January 13 when another detailed report about the Snake ransomware was posted. The dangerous aspect about this particular threat is that the victim files will be encrypted with a random input cipher — this means that the data will not be processed with a single algorithm. The way this is done is that the main engine will record the original file names and directories which are used as parameters. A special string is included as well — public-key encryption is used by the Snake ransomware.
Markers are added to the files as extensions — random sets of character combinations are placed as file extensions. The ransom note generated by the current version of the virus is called *Fix-Your-Files.txt which begins with the line What happened to your files?.
Snake Ransomware – Technical Analysis
Kremez’s analysis indicates that the ransomware is written in the Golang language, and that it is highly obfuscated.
The level of routine obfuscation is much higher than what is usually seen in ransomware deployed in targeted attacks.
When the Snake ransomware infection is initiated, Shadow Volume Copies will be removed from the system.
Then, various processes related to SCADA systems, virtual machines, industrial control systems, remote management tools and network management tools will be killed.
After these two stages are completed, the ransomware will continue with data encryption, but it will skip files located in Windows system folders and some system files, such as:
windir
SystemDrive
:\$Recycle.Bin
:\ProgramData
:\Users\All Users
:\Program Files
:\Local Settings
:\Boot
:\System Volume Information
:\Recovery
\AppData\
Upon encryption, the Snake ransomware will append a 5-character string to each file’s extension. As a result, an file named file.doc will look like this after encryption – file.docknfgT (think is a random example).
In each encrypted file, the EKANS file marker will be added. It is curious to note that EKANS is SNAKE written in reverse.
The researchers say that the ransomware takes longer than usual to encrypt targeted data. However, since this is a targeted threat which is executed whenever the attacker decides, the time surely will not be much of an issue.
Once the encryption process is finalized, Snake will create a ransom note in C:\Users\Public\Desktop, and it will be called Fix-Your-Files.txt. The ransom note typically contains instructions to contact cybercriminals for payment instructions. The email provided for contact is bapcocrypt@ctemplar.com but the email may change in future releases of the ransomware.
This is what the ransom note looks like:
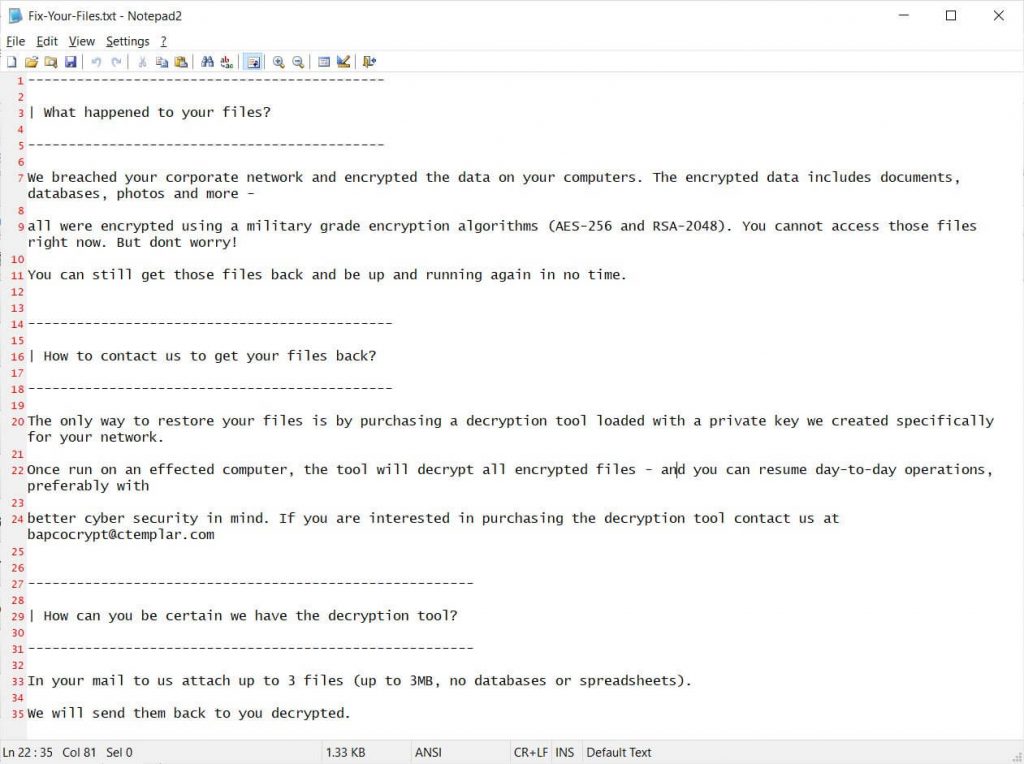
Here’s what the note says (parts of it):
What happened to your files?
We breached your corporate network and encrypted the data on your computers. The encrypted data includes documents, databases, photos and more –
All were encrypted using a military grade encryption algorithms (AES-256 and RSA-2048). You cannot access those files right now. But dont worry!
You can still get those files back and be up and running again in no time.
How to contact us to get your files back?
The only way to restore your files is by purchasing a decryption tool loaded with a private key we created specifically for your network.

Remove Snake Ransomware
In terms of file decryption, currently, there is no information whether files encrypted by Snake ransomware can be decrypted without the attackers’ decryption key. By the looks of it, the ransomware’s encryption is unbeatable, though.
Even though at the moment Snake ransomware is targeting organizations, large-scale campaigns against individuals can also be launched. If your ransomware infection’s symptoms resemble Snake ransomware’s behavior, you can try removing the ransomware using the instructions below.


