Linux is not only targeted by DDoS attackers but also by ransomware writers. Linux is now endangered by a threat registered as Linux.Encoder.1, first spotted by Dr. Web’s security researchers.
Linux.Encoder.1 targets Linux-powered websites and servers by encrypting MySQL, Apache and the home or root folders of the target. In exchange for the decryption of the data, the authors ask for a payment of 1 Bitcoin, or approximately $300.
How Does the Linux.Encoder.1 Attack Happen?
Nothing surprising here. The Linux ransomware is distributed via exploiting vulnerabilities in website plugins and third-party software products.
Once Linux.Encoder.1 has sneaked into a system, it will start encrypting the files in the Home directories, together with the Backup locations and the System Folders of the website files, pages, images, code libraries and scripts.
What is the Type of Encryption Used by Linux.Encoder.1?
The encryption used is the AES algorithm. However, in order for the ransomware to work, it needs to obtain root privileges. Once activated, it will download:
- The ransom message.
- A file with the public RSA key.
Then, the Linux ransomware acts as a daemon and deletes the original files. An .encrypt extension is added to the compromised files, an a ransom message is added to every folder.
KrebsOnSecurity has reported one recent victim of the file-encrypting malware – the professional website designer Daniel Macadar. He has shared that the ransom note was dropped in a plain text file called ‘instructions to decrypt’ and it was situated in every file directory that had encrypted data.
This is the text:
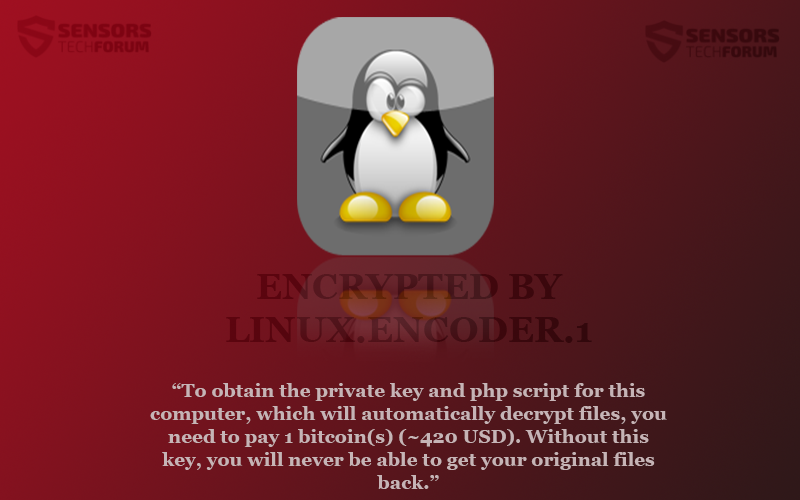
→“To obtain the private key and php script for this computer, which will automatically decrypt files, you need to pay 1 bitcoin(s) (~420 USD). Without this key, you will never be able to get your original files back.”
The victim proceeded with the payment, as he didn’t have backups.
Who Should Look Out for Linux.Encoder.1?
As mentioned in the beginning, the malware targets folders that are located in Linux web server setups, along with directories such as home, root, MySQL, Apache. Also, any other directory that has git, svn, webapp, www, public_html, or backup in it is endangered by the ransom software.
Linux.Encoder.1 also searches for files with extensions such as .js, .css, .properties, .xml, .ruby, .php, .html, .gz, and .asp. Files of these types are typical for web development environments. Other targeted extensions include .rar, .7z, .xls, .pdf, .doc, .avi, .mov, .png, .jpg.
As with any file-encryption ransomware, having your files backed up is the best way to prevent paying the ransom.