Magniber ransomware stands out as an evolving threat since its emergence in 2017. Once a shadowy menace lurking in the corners of South Korea’s digital space, it has broadened its reach, casting a wider net across Asia with its refined attack strategies and cunning evasion tactics.
This article dives into the heart of Magniber’s evolution, dissecting its adaptability and the sophisticated tactics it employs to slip through cybersecurity defenses.
Threat Summary
| Name | Magniber Ransomware |
| Type | Ransomware, Cryptovirus |
| Short Description | The ransomware encrypts files on your computer system and demands a ransom to be paid to allegedly recover them. |
| Distribution Method | Spam Emails, Email Attachments, System vulnerabilities |
| Detection Tool |
See If Your System Has Been Affected by malware
Download
Malware Removal Tool
|
| Data Recovery Tool | Windows Data Recovery by Stellar Phoenix Notice! This product scans your drive sectors to recover lost files and it may not recover 100% of the encrypted files, but only few of them, depending on the situation and whether or not you have reformatted your drive. |
The Evolution of Magniber Ransomware
Since its inception in 2017, Magniber ransomware has transitioned from a relatively unknown threat to a sophisticated and persistent danger.
Initially recognized for targeting users in South Korea, this malware has expanded its horizons to affect various Asian countries. Its ability to evolve over time, developing new tactics, techniques, and procedures (TTPs), makes it a notable example of how cyber threats are continuously advancing.
Magniber ransomware’s unique approach, such as its fileless infection chain, sets it apart from other ransomware families. By exploiting vulnerabilities within browsers and leveraging Windows zero-days without leaving the typical digital footprint, Magniber demonstrates an advanced level of stealth.
These methods make detection and mitigation more challenging for both individuals and cybersecurity mechanisms. The ransomware’s shift towards exploiting the ‘PrintNightmare’ vulnerability and later, browser exploits, represents a strategic adaptation to continually changing digital environments, confirming the group’s commitment to refining their attack methods.
Another significant aspect of Magniber’s evolution is its delivery mechanism. The utilization of ZIP files containing JavaScript payloads, dropped via malicious ads on the internet, underscores a shift towards more sophisticated initial access vectors. This change not only illustrates the group’s innovative approach but also serves as a critical reminder of the dynamic nature of cyber threats. Specifically, the adaptation to distribute payloads without the Mark-of-the-Web (MotW) indicates a calculated effort to bypass traditional security measures.
Over the years, the payload of Magniber ransomware has undergone complete rewrites, showcasing the group’s continual development to evade detection and enhance the efficacy of their attacks. Despite these advancements and its targeted attacks on Asian firms, the ransomware doesn’t follow the trend of file-stealing or double extortion, preferring instead to focus on file encryption. This distinct characteristic further emphasizes the need for targeted defense strategies, such as maintaining regular backups on isolated systems, to mitigate the impact of such tailored threats.
Why Magniber Ransomware is a Significant Threat in 2024
In 2024, Magniber ransomware remains a critical concern due to its progressively refined TTPs and the scarce availability of public research on its recent versions. Its evolution signifies not just a threat to individual systems but poses a substantial risk to organizations, especially those within its geographic focus of Asia. Magniber’s continued development and use of sophisticated evasion tactics such as fileless infections and direct system calls make it a challenging adversary for cybersecurity defenses.
The significance of Magniber in the current year also lies in its selective targeting and method of distribution, which reflect a strategic evolution aimed at maximizing impact and evading detection. The ability of this ransomware to bypass established security measures calls for a proactive and dynamic approach to cybersecurity. Traditional security tools may not be enough to detect or block Magniber due to its use of direct system calls over Windows API calls, a method not typically monitored by many endpoint detection and response (EDR) technologies.
With Magniber’s capability to inflict damage without engaging in the more common ransomware practices of data theft or double extortion, it poses a unique challenge. This approach suggests that the creators prioritize encryption and immediate financial gain over the longer-term strategies employed by other ransomware groups. Consequently, businesses and individuals alike must employ comprehensive security solutions that can adapt to and counter such evolving threats.
To defend against Magniber and similar sophisticated threats, integrating advanced security tools like SpyHunter is essential. SpyHunter’s ability to detect and remove threats like Magniber helps in maintaining a secure digital environment. Offering comprehensive protection against the latest malware strains, SpyHunter ensures that evolving threats do not compromise your digital safety.
The Latest Attack Vectors Utilized by Magniber Ransomware
Magniber ransomware continues to adapt, showcasing its resilience and innovation in the cyber threat landscape. This section delves into the contemporary strategies employed by Magniber to compromise systems, emphasizing the importance of staying informed and proactive in cybersecurity measures.
How Magniber Targets Its Victims
The operation of Magniber ransomware is a testament to the evolving nature of cyber threats. By exploiting vulnerabilities and leveraging deceitful tactics, Magniber aims to infiltrate and capitalize on compromised systems.
Exploiting Browser Vulnerabilities: A New Magniber Tactic
In a noticeable pivot from previous strategies, Magniber has begun exploiting browser vulnerabilities to orchestrate its attacks. This method marks a significant shift, particularly underlining the exploitation of older, less secure browsers such as Internet Explorer. Despite Internet Explorer’s decreased popularity, it still represents a viable target due to its residual use, evidenced by millions of page views monthly. By targeting inherent flaws within the browser, Magniber can initiate its malicious operations without direct interaction from the user, merely requiring the victim to visit a compromised webpage.
The Role of Phishing Emails in Spreading Magniber
While not the primary method of distribution for Magniber, phishing emails remain a potential vector for its spread. These carefully crafted emails, which may masquerade as legitimate communications, can entice users into opening attachments or clicking links that lead to the downloading of Magniber’s payload. This technique shows the significance of vigilance and education in recognizing and avoiding phishing attempts as a line of defense against ransomware.
To mitigate the threats posed by Magniber and similar ransomware, implementing robust cybersecurity measures is essential. Solutions like SpyHunter can offer comprehensive protection against such evolving threats. SpyHunter is uniquely designed to detect and eliminate ransomware and other malware, safeguarding your system against the latest cyber threats through real-time monitoring and advanced defense mechanisms.
Decoding Magniber Ransomware’s Execution Strategy
Understanding how Magniber ransomware infiltrates and exploits systems is critical for cybersecurity efforts. This malware launches a multi-step attack, starting with deceiving the user into clicking on a compromised website or email. Initially, the malware disguises itself through obfuscated JavaScript, awaiting activation by an unsuspecting user. Upon user interaction, the malware leverages the DotNetToJScript technique to evade detection, loading its harmful payload directly into the system’s memory.
Subsequently, Magniber employs direct system calls to decode and execute shell code, a strategic move to remain under the radar of traditional anti-virus software. A unique aspect of Magniber’s methodology is its focus on crippling the system’s recovery capabilities. It achieves this by deleting volume shadow copies and disabling backup services, utilizing VBScript for registry manipulation.
Furthermore, Magniber can escalate its privileges through the unorthodox use of fodhelper.exe, provided the user has administrative rights. Awareness of these tactics is essential for prevention, highlighting the importance of limiting admin privileges and employing sophisticated security solutions like SpyHunter that can detect and mitigate such advanced threats.
An In-depth Analysis of Magniber’s Encryption Techniques
Magniber ransomware’s encryption technique is both effective and elusive. Once activated on a system with the Korean language settings, it proceeds to encrypt files with a precision that suggests the use of a strong encryption algorithm, likely AES in CBC mode. Each file is appended with a distinct extension, linked to a unique identifier for the victim’s sample of Magniber. This approach underlines the personalized nature of its attacks.
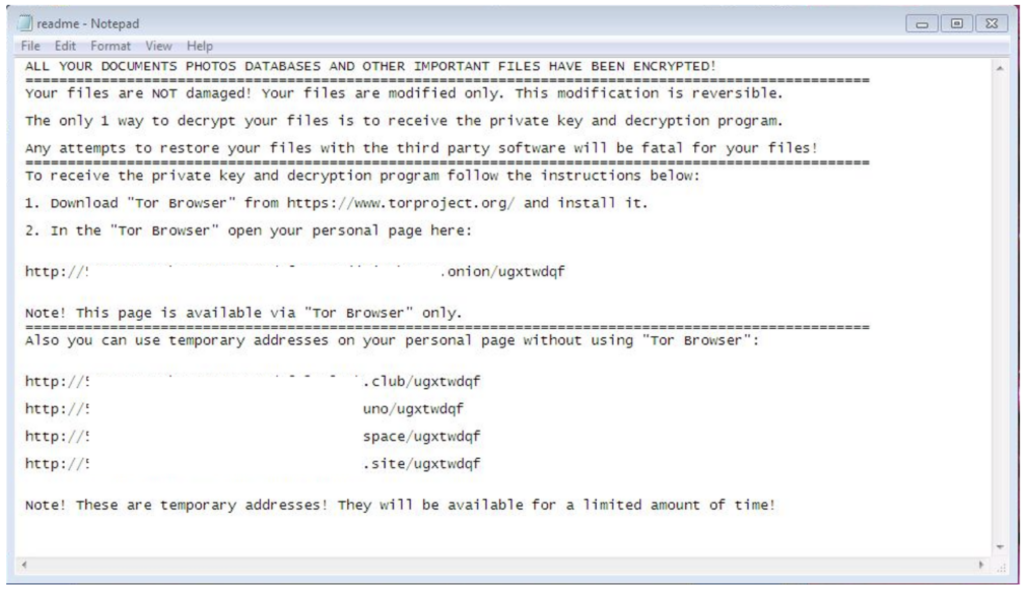
The ransomware’s encryption process ensures that no two files share the same encrypted output despite using the same key, complicating decryption efforts. At the end of the encryption spree, the ransomware conspicuously places a ransom note in a TXT format on the victim’s desktop. This note, while minimalistic, guides the victim towards making a ransom payment, further emphasizing the need for strong preemptive measures.
Understanding Magniber’s Unique Encryption Algorithm
The encryption algorithm employed by Magniber ransomware is sophisticated, utilizing a consistent key across the infected sample to lock down files. This method adds a unique identifier at the beginning of each encrypted file, essentially ‘signing’ the data as its own. Despite the complexity of the encryption, the fundamental weakness lies in the uniform use of the key across all files, which, if obtained, allows for decryption.
However, obtaining the key is a formidable challenge without the correct tools and expertise. Security professionals can sometimes extract the key from network traffic or by analyzing the ransomware’s code. Once the key is known, decryption tools, such as the magniber_decryptor.exe developed by the security community, become valuable assets in restoring encrypted files. This underscores the paramount importance of advanced threat detection and response systems like SpyHunter, capable of preventing such attacks before they execute their payload.
How Magniber Affects Home Users and Businesses
The impact of Magniber ransomware has evolved significantly since its inception in 2017, initially focusing on South Korean users but rapidly expanding its target to various Asian territories. This expansion not only underlines the adaptability and dangerousness of the Magniber ransomware but also heightens the concern for both home users and businesses within its geographical focus.
Assessing the Threat to Asian Enterprises by Magniber Ransomware
For Asian businesses, the stakes are even higher. The encryption of business-critical files can paralyze operations, leading to significant financial losses, reputational damage, and in some cases, permanent closure. The targeted nature of this ransomware, combined with its evolving methods of distribution, makes it a particularly formidable challenge for IT security teams.
- Operational Disruption: Companies have experienced complete operational halts, unable to access customer data, financial records, or manage day-to-day operations.
- Cost of Recovery: Beyond the immediate impact, the long-term costs of recovery including IT expenditure, loss of business, and increased security measures can be substantial.
- Reputational Damage: Trust is hard to earn and easy to lose. Businesses impacted by Magniber may find it challenging to regain the confidence of their customers and partners.
Protecting against such threats necessitates a multi-layered security approach, including employee training, up-to-date security solutions like SpyHunter, and a robust backup strategy to ensure business continuity in the event of an attack. Combating Magniber’s targeted approach requires not only advanced technological defenses but also a proactive mindset towards cybersecurity.
Ultimately, the threat posed by Magniber to both home users and Asian enterprises underscores the importance of comprehensive cybersecurity practices and the value of forward-thinking security solutions.
Preventive Measures and Removal Options against Magniber Ransomware
The emergence of Magniber ransomware has posed critical security challenges, particularly for users in the Republic of Korea, targeting systems with a specific focus on those operating the Hangeul version of Windows.
Understanding how to mitigate the threat and effectively deal with an infection is vital for maintaining cybersecurity. Here, we delve into essential practices to safeguard against Magniber attacks, highlighting the use of SpyHunter for detection and removal, and emphasizing the significance of backup management as a defensive strategy.
Essential Practices to Safeguard Against Magniber Attacks
To defend against the cunning tactics of Magniber ransomware, adopting proactive and comprehensive security measures is indispensable. Implementing strict security protocols and staying informed about the ransomware’s operational methods can significantly diminish the likelihood of an attack.
Key strategies include updating and patching systems regularly to fix vulnerabilities, employing strong and unique passwords, and educating users about the dangers of phishing emails and malicious attachments. Moreover, adopting a layered security approach, which includes using antivirus software, firewalls, and intrusion detection systems, can provide a robust defense against potential attacks.
Using SpyHunter for Detecting and Removing Magniber Ransomware
SpyHunter stands out as an exceptionally competent tool in detecting and removing Magniber ransomware. With its advanced algorithms and up-to-date ransomware definitions, SpyHunter excels at identifying and neutralizing threats, including the latest variants of Magniber.
It conducts comprehensive system scans to detect anomalies and potentially malicious activities, ensuring that any trace of Magniber is eradicated. For users seeking a reliable solution to secure their systems against this formidable threat, SpyHunter provides an effective, user-friendly option, thereby embodying an essential component of a comprehensive cybersecurity strategy.
Creating and Managing Backups: A Key Defense Strategy
One cannot overstate the importance of backup creation and management in the context of ransomware defense. Backups serve as a safety net, enabling users to restore their systems and data following an attack. To maximize their effectiveness, backups should be regularly updated and stored in multiple locations, including offline storage, which Magniber cannot access.
This strategy not only secures critical data against ransomware threats but also significantly reduces downtime and data loss, thereby mitigating the overall impact of an attack. It is a simple yet profoundly effective measure that complements other cybersecurity practices.
Recovering from a Magniber Ransomware Attack
Facing a Magniber ransomware attack can be a terrifying experience, especially when your important documents, photos, and files are encrypted. However, there are steps you can take to recover from an attack and potentially restore your encrypted files. This guide will walk you through the process of finding free and paid decryption tools, exploring data recovery options, and understanding how security software like SpyHunter can assist in these situations.
Free and Paid Decryption Tools: Scouting for Solutions
After a ransomware attack, one of the first steps to consider is finding a decryption tool. Security researchers often develop free decryption tools for specific ransomware strains. For instance, AhnLab released a free decryptor for Magniber ransomware, which could be a beacon of hope for victims. While not all ransomware types have a free decryptor available, it’s worth checking resources like the No More Ransom Project for any potential solutions.
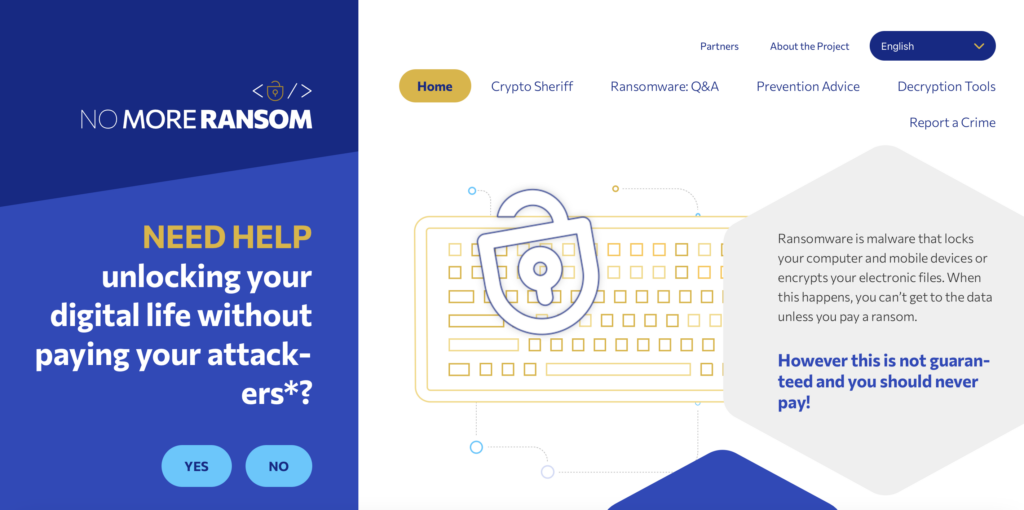
In cases where free decryptors are not available, some may consider paid decryption services. However, it’s important to proceed with caution, as there are risks involved, including scams and further financial losses. One reliable method before considering paid options is to explore the capabilities of established security solutions known for their effectiveness against ransomware.
Spotlight on SpyHunter’s Capabilities in Restoring Encrypted Files
When tackling ransomware infections, SpyHunter offers reliable malware detection and removal. Though it’s crucial to understand that while SpyHunter excels at detecting and eliminating ransomware, decryption of files requires a different approach. In cases where a ransomware signature and behaviors are known, SpyHunter effectively prevents further damage by stopping the malware in its tracks, ensuring that users can utilize any available decryption tools in a safer environment.
Navigating Through Data Recovery Options Post-Infection
Even after removing the ransomware threat, the challenge of accessing encrypted files remains. This is where data recovery tools step in. Programs like Recuva can help retrieve deleted or damaged files, which, in some cases, could mean getting back the data encrypted by ransomware. These tools scan your drives for remnants of lost files, offering a glimmer of hope in seemingly bleak scenarios.
Implementing best practices for data backup and recovery is also crucial for personal and organizational cybersecurity postures. Regularly updated backups stored on external drives or cloud storage can drastically reduce the impact of ransomware attacks. Moreover, securing these backups with robust solutions like SpyHunter ensures they remain unaffected by future cyber threats.
In summary, while a Magniber ransomware attack can pose significant challenges, leveraging the right mixture of free and paid decryption tools, alongside potent security software and effective data recovery strategies can offer a pathway to regaining control over encrypted data.
Additional Questions About Magniber Ransomware
Is It Possible to Decrypt Files Locked by Magniber Ransomware?
Currently, decrypting files encrypted by Magniber ransomware presents significant challenges. While a specific decryption tool exists, its application is highly limited and works only when the AES key is already known. This scenario mainly occurs if the default key from a sample is used or if the key can be extracted from captured traffic.
It’s important to note that most real-world cases will not fall within these narrow parameters. As a result, the majority of victims cannot rely on decryption as a viable solution to regain access to their encrypted files. Instead, emphasizing prevention and having strong backup measures in place are the most effective strategies against Magniber ransomware.
How Can I Identify a Magniber Ransomware Infection Early?
Recognizing the early signs of a Magniber ransomware infection can help mitigate its impacts. Users may notice unusual file extensions, as Magniber renames files with specific patterns not commonly seen during normal operations. Additionally, victims often find ransom notes named “_HOW_TO_DECRYPT_MY_FILES_[random_characters].txt” or similar messages within affected directories, demanding payment in exchange for decryption keys. Another indicator is the inability to open or access files that were previously functional.
Computers may also exhibit a sudden decrease in performance due to the ransomware encrypting files in the background. Identifying these symptoms promptly can aid in stopping the spread of the infection and taking appropriate measures to protect uninfected systems.
When facing potential ransomware threats like Magniber, the use of a credible security solution like SpyHunter is recommended. Regular scans with SpyHunter can help identify vulnerabilities, detect malware, and remove threats before they can cause significant damage. By taking proactive steps, including the use of reputable anti-malware, individuals, and organizations can better defend against the evolving menace of ransomware.
Conclusion: Staying One Step Ahead of Magniber Ransomware
Ransomware threats, particularly Magniber, continue to evolve, stressing the importance of proactive and informed cybersecurity measures. Understanding the threat’s behavior and adopting a multi-layered security approach is paramount in safeguarding your digital assets against such sophisticated attacks. Thus, staying one step ahead involves keeping abreast of the latest cybersecurity trends, threats, and protective measures.
To mitigate the risk posed by Magniber and similar ransomware, it is essential to implement several best practices within your cybersecurity protocol. Regularly updating your software to patch vulnerabilities and using advanced security solutions like SpyHunter can significantly reduce the risk to your systems. SpyHunter’s ability to detect and remove threats like Magniber underscores the necessity of having reliable, cutting-edge security software as part of your defense strategy against malicious cyber activities.
Beyond software solutions, fostering cybersecurity awareness among your team plays a crucial role. Educating employees on the dangers of phishing emails, the importance of using strong, unique passwords, and recognizing the signs of a compromised system can turn your team into the first line of defense against ransomware. Combining well-informed human vigilance with advanced security tools creates a formidable barrier against the threats posed by ransomware.
Finally, implementing regular data backup procedures ensures that, in the event of an attack, your business’s critical information remains safe and recoverable. Offsite backups, whether in the cloud or through an external drive that is not constantly connected to your network, can save your organization from substantial data loss and downtime.
In conclusion, the key to defending against Magniber ransomware lies in a well-rounded and proactive approach to cybersecurity. By staying educated on threats, utilizing advanced security tools like SpyHunter, promoting cybersecurity awareness, and maintaining robust backup strategies, you can safeguard your digital environment from the ever-evolving landscape of cyber threats.
- Step 1
- Step 2
- Step 3
- Step 4
- Step 5
Step 1: Scan for Magniber Ransomware with SpyHunter Anti-Malware Tool



Ransomware Automatic Removal - Video Guide
Step 2: Uninstall Magniber Ransomware and related malware from Windows
Here is a method in few easy steps that should be able to uninstall most programs. No matter if you are using Windows 10, 8, 7, Vista or XP, those steps will get the job done. Dragging the program or its folder to the recycle bin can be a very bad decision. If you do that, bits and pieces of the program are left behind, and that can lead to unstable work of your PC, errors with the file type associations and other unpleasant activities. The proper way to get a program off your computer is to Uninstall it. To do that:


 Follow the instructions above and you will successfully delete most unwanted and malicious programs.
Follow the instructions above and you will successfully delete most unwanted and malicious programs.
Step 3: Clean any registries, created by Magniber Ransomware on your computer.
The usually targeted registries of Windows machines are the following:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
You can access them by opening the Windows registry editor and deleting any values, created by Magniber Ransomware there. This can happen by following the steps underneath:


 Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Before starting "Step 4", please boot back into Normal mode, in case you are currently in Safe Mode.
This will enable you to install and use SpyHunter 5 successfully.
Step 4: Boot Your PC In Safe Mode to isolate and remove Magniber Ransomware





Step 5: Try to Restore Files Encrypted by Magniber Ransomware.
Method 1: Use STOP Decrypter by Emsisoft.
Not all variants of this ransomware can be decrypted for free, but we have added the decryptor used by researchers that is often updated with the variants which become eventually decrypted. You can try and decrypt your files using the instructions below, but if they do not work, then unfortunately your variant of the ransomware virus is not decryptable.
Follow the instructions below to use the Emsisoft decrypter and decrypt your files for free. You can download the Emsisoft decryption tool linked here and then follow the steps provided below:
1 Right-click on the decrypter and click on Run as Administrator as shown below:

2. Agree with the license terms:

3. Click on "Add Folder" and then add the folders where you want files decrypted as shown underneath:

4. Click on "Decrypt" and wait for your files to be decoded.

Note: Credit for the decryptor goes to Emsisoft researchers who have made the breakthrough with this virus.
Method 2: Use data recovery software
Ransomware infections and Magniber Ransomware aim to encrypt your files using an encryption algorithm which may be very difficult to decrypt. This is why we have suggested a data recovery method that may help you go around direct decryption and try to restore your files. Bear in mind that this method may not be 100% effective but may also help you a little or a lot in different situations.
Simply click on the link and on the website menus on the top, choose Data Recovery - Data Recovery Wizard for Windows or Mac (depending on your OS), and then download and run the tool.
Magniber Ransomware-FAQ
What is Magniber Ransomware Ransomware?
Magniber Ransomware is a ransomware infection - the malicious software that enters your computer silently and blocks either access to the computer itself or encrypt your files.
Many ransomware viruses use sophisticated encryption algorithms to make your files inaccessible. The goal of ransomware infections is to demand that you pay a ransom payment to get access to your files back.
What Does Magniber Ransomware Ransomware Do?
Ransomware in general is a malicious software that is designed to block access to your computer or files until a ransom is paid.
Ransomware viruses can also damage your system, corrupt data and delete files, resulting in the permanent loss of important files.
How Does Magniber Ransomware Infect?
Via several ways.Magniber Ransomware Ransomware infects computers by being sent via phishing emails, containing virus attachment. This attachment is usually masked as an important document, like an invoice, bank document or even a plane ticket and it looks very convincing to users.
Another way you may become a victim of Magniber Ransomware is if you download a fake installer, crack or patch from a low reputation website or if you click on a virus link. Many users report getting a ransomware infection by downloading torrents.
How to Open .Magniber Ransomware files?
You can't without a decryptor. At this point, the .Magniber Ransomware files are encrypted. You can only open them once they are decrypted using a specific decryption key for the particular algorithm.
What to Do If a Decryptor Does Not Work?
Do not panic, and backup the files. If a decryptor did not decrypt your .Magniber Ransomware files successfully, then do not despair, because this virus is still new.
Can I Restore ".Magniber Ransomware" Files?
Yes, sometimes files can be restored. We have suggested several file recovery methods that could work if you want to restore .Magniber Ransomware files.
These methods are in no way 100% guaranteed that you will be able to get your files back. But if you have a backup, your chances of success are much greater.
How To Get Rid of Magniber Ransomware Virus?
The safest way and the most efficient one for the removal of this ransomware infection is the use a professional anti-malware program.
It will scan for and locate Magniber Ransomware ransomware and then remove it without causing any additional harm to your important .Magniber Ransomware files.
Can I Report Ransomware to Authorities?
In case your computer got infected with a ransomware infection, you can report it to the local Police departments. It can help authorities worldwide track and determine the perpetrators behind the virus that has infected your computer.
Below, we have prepared a list with government websites, where you can file a report in case you are a victim of a cybercrime:
Cyber-security authorities, responsible for handling ransomware attack reports in different regions all over the world:
Germany - Offizielles Portal der deutschen Polizei
United States - IC3 Internet Crime Complaint Centre
United Kingdom - Action Fraud Police
France - Ministère de l'Intérieur
Italy - Polizia Di Stato
Spain - Policía Nacional
Netherlands - Politie
Poland - Policja
Portugal - Polícia Judiciária
Greece - Cyber Crime Unit (Hellenic Police)
India - Mumbai Police - CyberCrime Investigation Cell
Australia - Australian High Tech Crime Center
Reports may be responded to in different timeframes, depending on your local authorities.
Can You Stop Ransomware from Encrypting Your Files?
Yes, you can prevent ransomware. The best way to do this is to ensure your computer system is updated with the latest security patches, use a reputable anti-malware program and firewall, backup your important files frequently, and avoid clicking on malicious links or downloading unknown files.
Can Magniber Ransomware Ransomware Steal Your Data?
Yes, in most cases ransomware will steal your information. It is a form of malware that steals data from a user's computer, encrypts it, and then demands a ransom in order to decrypt it.
In many cases, the malware authors or attackers will threaten to delete the data or publish it online unless the ransom is paid.
Can Ransomware Infect WiFi?
Yes, ransomware can infect WiFi networks, as malicious actors can use it to gain control of the network, steal confidential data, and lock out users. If a ransomware attack is successful, it could lead to a loss of service and/or data, and in some cases, financial losses.
Should I Pay Ransomware?
No, you should not pay ransomware extortionists. Paying them only encourages criminals and does not guarantee that the files or data will be restored. The better approach is to have a secure backup of important data and be vigilant about security in the first place.
What Happens If I Don't Pay Ransom?
If you don't pay the ransom, the hackers may still have access to your computer, data, or files and may continue to threaten to expose or delete them, or even use them to commit cybercrimes. In some cases, they may even continue to demand additional ransom payments.
Can a Ransomware Attack Be Detected?
Yes, ransomware can be detected. Anti-malware software and other advanced security tools can detect ransomware and alert the user when it is present on a machine.
It is important to stay up-to-date on the latest security measures and to keep security software updated to ensure ransomware can be detected and prevented.
Do Ransomware Criminals Get Caught?
Yes, ransomware criminals do get caught. Law enforcement agencies, such as the FBI, Interpol and others have been successful in tracking down and prosecuting ransomware criminals in the US and other countries. As ransomware threats continue to increase, so does the enforcement activity.
About the Magniber Ransomware Research
The content we publish on SensorsTechForum.com, this Magniber Ransomware how-to removal guide included, is the outcome of extensive research, hard work and our team’s devotion to help you remove the specific malware and restore your encrypted files.
How did we conduct the research on this ransomware?
Our research is based on an independent investigation. We are in contact with independent security researchers, and as such, we receive daily updates on the latest malware and ransomware definitions.
Furthermore, the research behind the Magniber Ransomware ransomware threat is backed with VirusTotal and the NoMoreRansom project.
To better understand the ransomware threat, please refer to the following articles which provide knowledgeable details.
As a site that has been dedicated to providing free removal instructions for ransomware and malware since 2014, SensorsTechForum’s recommendation is to only pay attention to trustworthy sources.
How to recognize trustworthy sources:
- Always check "About Us" web page.
- Profile of the content creator.
- Make sure that real people are behind the site and not fake names and profiles.
- Verify Facebook, LinkedIn and Twitter personal profiles.


