Hackers continue to take advantage of the recently discovered zero-day exploit in Adobe Flash to attack victims via BEDEP malware this time.
What Is a Zero-day Exploit?
A “zero-day exploit” (attack, threat, etc.) occurs during the time when a new program or an application is released and hackers find a vulnerability in it before the developers do or were not able to fix on time.
The developers have had no time or “zero days” to patch the flow just yet. It’s the perfect gap for cyber criminals to take advantage of that particular program and use the vulnerability to infect victims’ systems for various purposes and via various “malvertising” tricks.
The “Malvertising” Tricks…
“Malvertising” (malicious advertising) tricks are such that lure Internet users into clicking on fake ads which then redirect users to the URL hosting the exploit. Clicking the malvertisement allows the malware to download onto the victim’s system which then creates a backdoor for hackers to steal sensitive data, harm the system, install additional malware onto it, etc..
The Zero-day Exploit in Adobe Flash with BEDEP
On February the 2nd, Adobe developers found themselves rushing into patching a zero-day flow in the latest version of Adobe Flash.
At first, hackers took advantage of the Adobe vulnerability detected as SWF_EXPLOIT.MJST. Days later, malware experts discovered that the exploit is infecting victims’ systems via the BEDEP malware.
Apparently, according to the experts at trendmicro.com, this is not the first time BEDEP malware has been used for Adobe zero-days. In fact, in the end of January they spotted a Flash zero-day exploit leading to the BEDEP malware being downloaded on the infected computer.
Alvin Bacani, a research engineer at Trend Micro, explained that the first time the flow was detected, cyber criminals were using the so-called “Angler Exploit Kit” to send multiple malicious pop-up adverts.
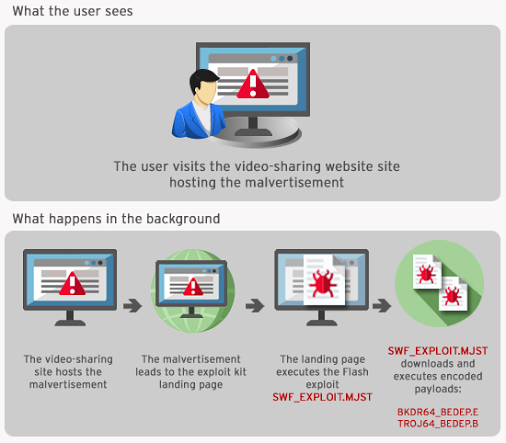
He added that the same malvertising tactic is employed by BEDEP malware as well, except it uses the “Hanjuan Exploit Kit” to connect the infected system to the hacker’s botnet.
In short, the malware’s purpose is to “turn infected systems into botnets for other malicious intentions,” according to Bacani.
“Additionally, BEDEP is known for carrying out advertising fraud routines and downloading additional malware.”
Bacany’s threat advisory also stated that, “BEDEP initially came undetected and unnoticed due to its heavy encryption and use of Microsoft file properties for its disguise as well as the use of seemingly legitimate export functions.”

