What To Do When Your System Gets Infected with Ransomware
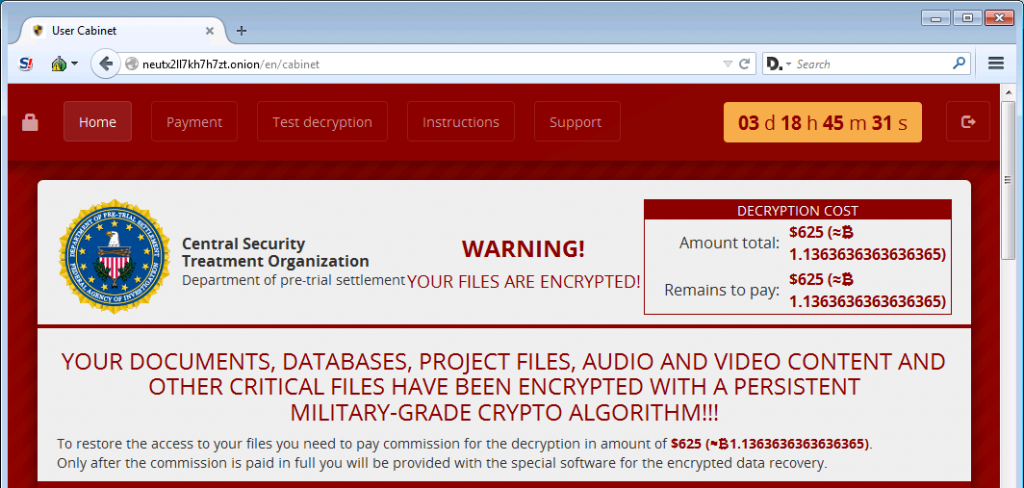
You should know by now that ransomware is currently the worst of online threats you could get on your PC. It’s a virus so powerful that is capable of destroying your business and/or personal life in seconds by hijacking your…




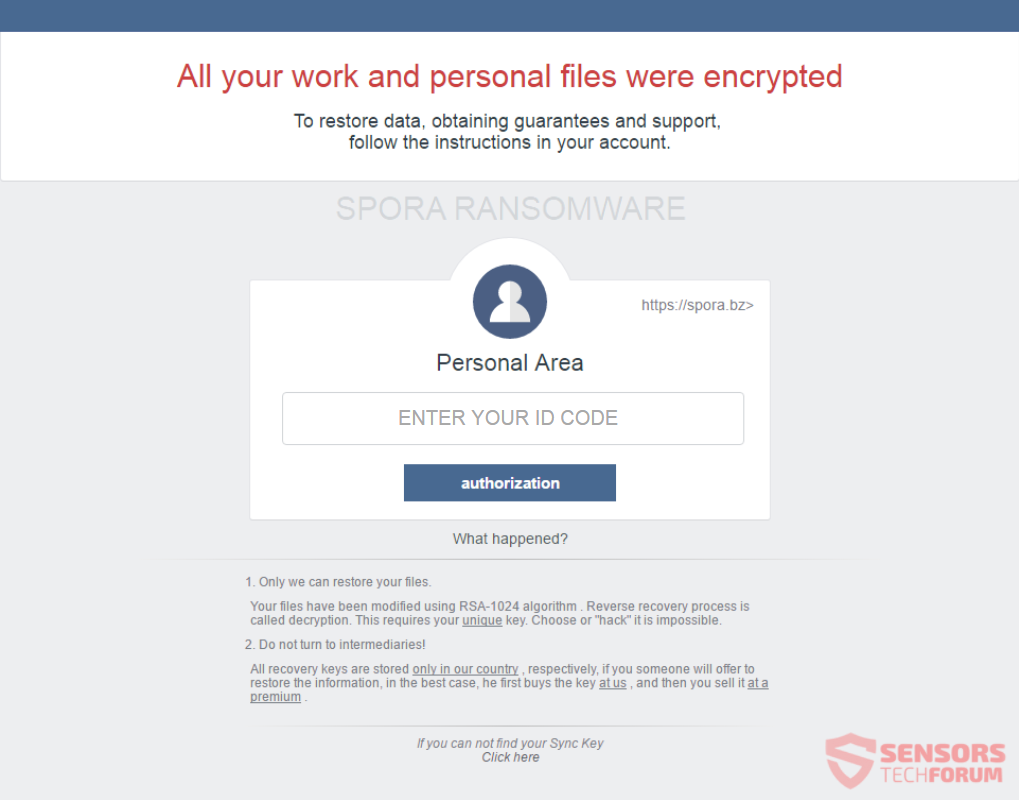



![Dharma Ransomware Using New File Extension [Mkgoro@india.com].xtbl and [Mkgoro@india.com].wallet New Dharma ransom note](https://cdn.sensorstechforum.com/wp-content/uploads/2016/12/Screen-Shot-2016-12-30-at-1.19.57-PM-150x150.png)