 Crypto-viruses are an increasing menace that aims to turn your day the other way around, making you pay to cyber-criminals for keys that were encrypted. And what is worse is that cyber-crooks constantly keep developing new and more sophisticated ways to increase the defense of their viruses, implementing combined encryption keys that travel safely to their servers. However, there still are those ransomware viruses that send unencrypted information, allowing you, the user to sniff out traffic from your computer and with luck to get the decryption key for your files. We have designed to make a tutorial which is as simple as possible to theoretically explain how could you detect your decryption key by sniffing out your web traffic using Wireshark.
Crypto-viruses are an increasing menace that aims to turn your day the other way around, making you pay to cyber-criminals for keys that were encrypted. And what is worse is that cyber-crooks constantly keep developing new and more sophisticated ways to increase the defense of their viruses, implementing combined encryption keys that travel safely to their servers. However, there still are those ransomware viruses that send unencrypted information, allowing you, the user to sniff out traffic from your computer and with luck to get the decryption key for your files. We have designed to make a tutorial which is as simple as possible to theoretically explain how could you detect your decryption key by sniffing out your web traffic using Wireshark.
Useful Advice: Before actually engaging in any network sniffing or other methods we have suggested below, it is urgently advisable to do it from a safe and secure computer system unaffected by any type of malware. If you want to make sure that your computer system is 100% safe while you are following these instructions, experts often advise to download an advanced anti-malware tool which is frequently updated and features next-gen active protection against viruses to see if your PC is safe:
Spy Hunter scanner will only detect the threat. If you want the threat to be automatically removed, you need to purchase the full version of the anti-malware tool.Find Out More About SpyHunter Anti-Malware Tool / How to Uninstall SpyHunter

How It Works – Brief Explanation
Bear in mind that this solution is only theoretical since different ransomware viruses perform different activities on user PCs. To best clarify that, most ransomware viruses use encryption algorithm – a cryptic language replacing the original language code of the files, making them inaccessible. The two most widely used encryption algorithms are RSA and AES encryption algorithms. Both of them are extremely strong and impenetrable. In the past, most malware writers used only one encryption cipher in a special manner. The standard action for the ransomware virus was in the following consequence:
- Drop it’s payload.
- Modify the Windows Registry Editor to run on startup or after the specific action is done.
- Delete backups and perform other activities.
- Encrypt the files.
- Send the decryption key in a file or as a communication directly to the command and control (C&C) center of the cyber-criminals.
- Drop it’s ransom note and other support files that notify the user of this “complication”.
However, since malware researchers have united their resources and put a lot of effort to detect codes in the flaw or capture decryption keys and develop free decrypters, malware writers have also made quite the improvements themselves. One of those improvements is implementing a two-way encryption, using a combination of RSA and AES encryption algorithms.
In brief, they did not just encrypt your files with one of the ciphers, but now they also use a second encryption algorithm to encrypt the decryption key in a special file which is then sent to their servers. These files are impossible to decrypt, and users are hopelessly looking for alternative methods to decrypt them.
For more information on this encryption method, please visit:
Ransomware Encryption Explained – Why Is It So Effective?
Another tactic the cyber-crook “devs” started to use is a so-called cipher block chaining. This is a mode that briefly explained, breaks the file if you try to tamper with it, making any form of recovery completely impossible.
So, here is where we are. At this point, there are even new developments in the world of ransomware, which are yet to be revealed.
It is very difficult to stay ahead of ransomware, but despite all, we have decided to show you how to use Wireshark to your benefit and hopefully intercept HTTP traffic in the correct moment. However, bear in mind that these instructions are THEORETICAL, and there are a lot of factors that may prevent them from working in an actual situation. Still, it is better than not trying before paying the ransom, right?

Using Wireshark to Find Decryption Key
Before downloading and using Wireshark – one of the most widely used network sniffers out there, you should have the malware’s executable on standby and infect your computer once again. However, bear in mind that some ransomware viruses perform new encryption every time a computer is restarted as well, so you should also configure Wireshark to run automatically on startup. Let’s begin!
Step 1: Download Wireshark on your computer by clicking on the following buttons( for your version of Windows)
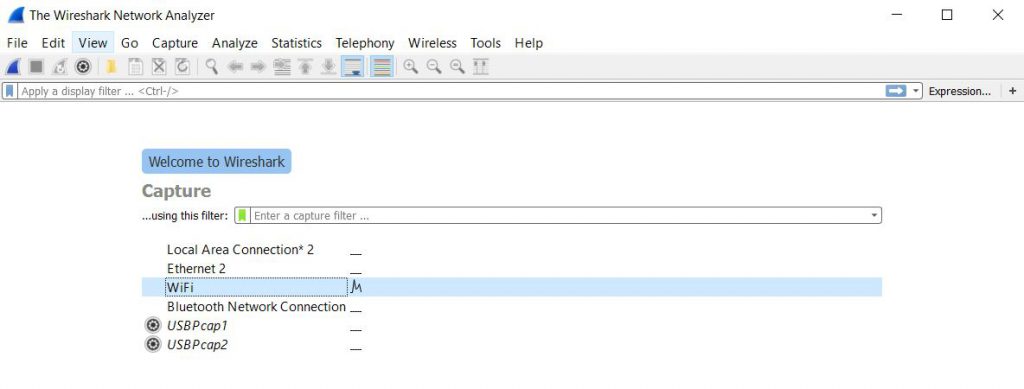
Step 2: Run, configure and learn how to sniff packets with Wireshark. To learn how to start analyzing packets and check where your packets save the data, you should open Wireshark first and then choose your active network interface for analyzing packets. For most users, that would be the interface with traffic bouncing up and down on it’s right. You should choose it and click twice fast to start sniffing:
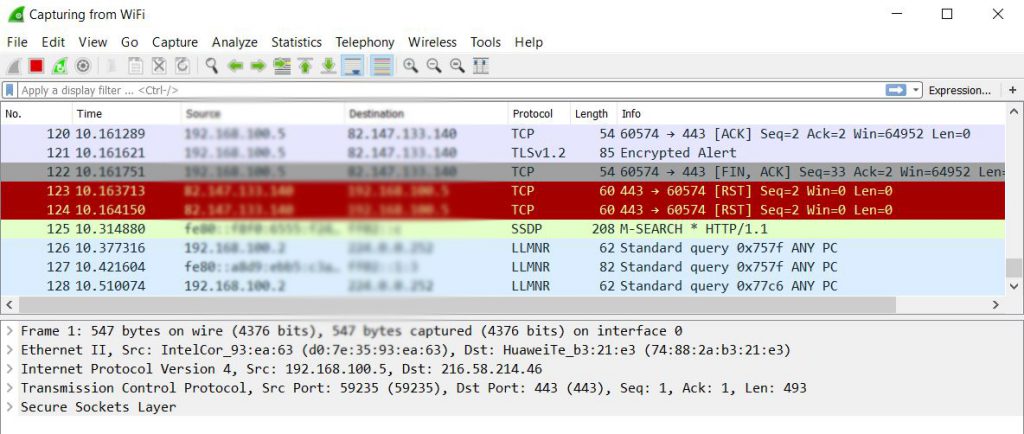
Step 3: Sniffing packets. Since ransomware viruses communicate via HTTP traffic, you should filter all the packets first. Here is how the packets look initially after you choose your interface and sniff traffic from it:
To intercept only HTTP traffic, you should type the following into the display filter bar:
→ http.request – to intercept the requested traffic
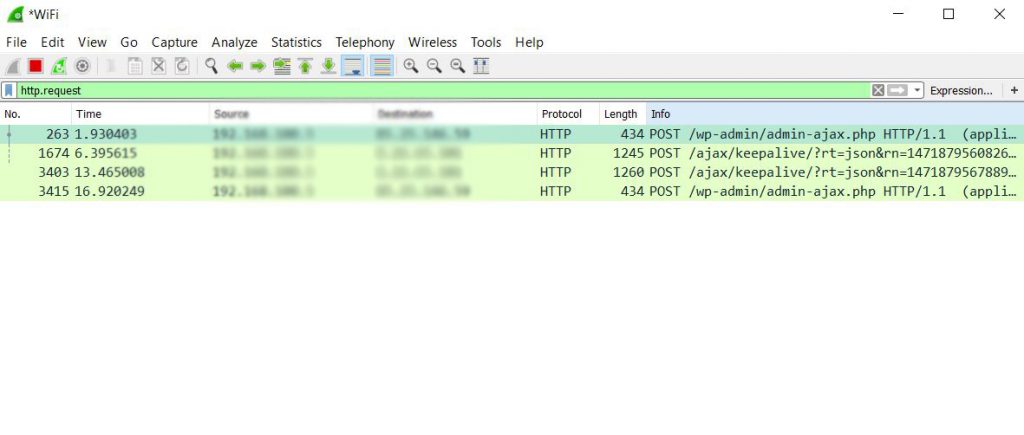
Once filtered it should look like this:
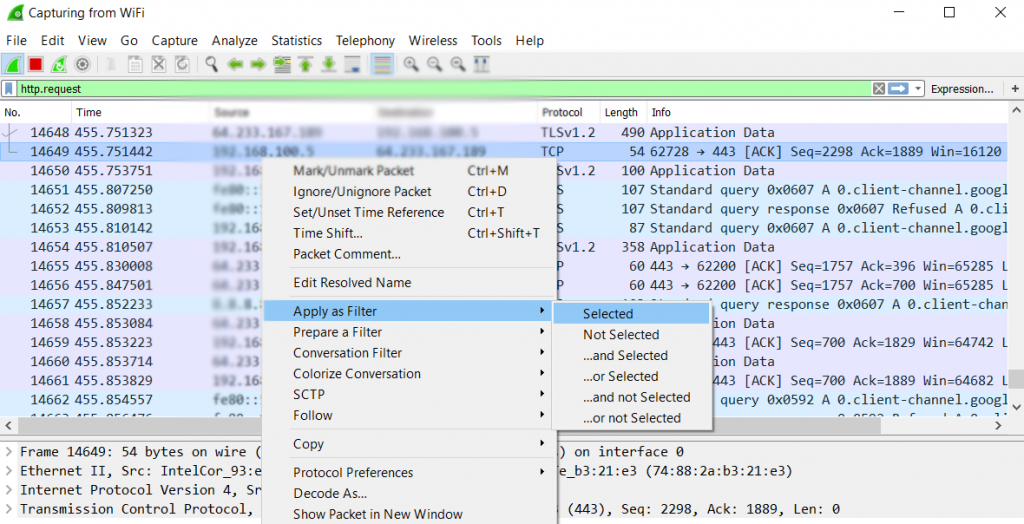
You can also filter the source and destination IP addresses by scrolling up and down and choosing one address, then right clicking on it and navigating to the following feature:
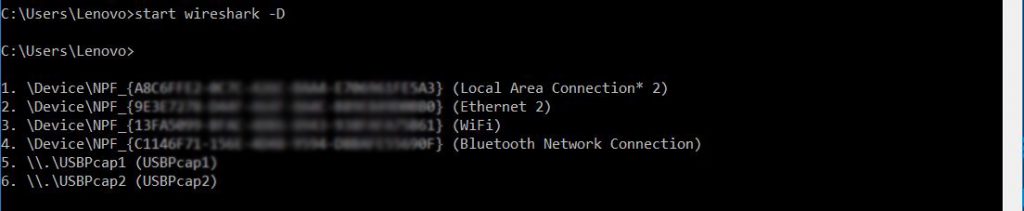
Step 4: Configure Wireshark to run automatically. To do this, first, you should go to the command prompt of your computer by typing cmd on your Windows search and running it. From there, type the following command with capital “-D” setting to get the unique key for your interface. The keys should look like the following:
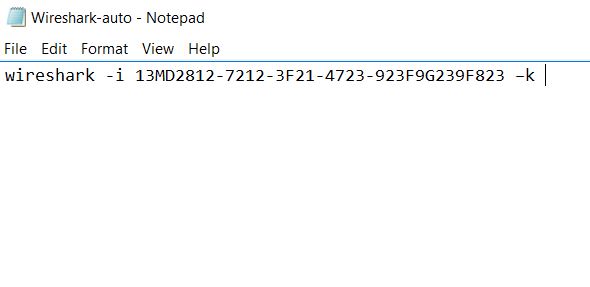
Step 5: Copy the key for your active connection and create a New Text Document and in it write the following code:
→ wireshark -i 13MD2812-7212-3F21-4723-923F9G239F823(<= Your copied key) –k
You can additionally modify the command by adding the –w letter and creating a name for the file that will save it onto your computer, allowing you to analyze the packets. The result should look similarly to this one:
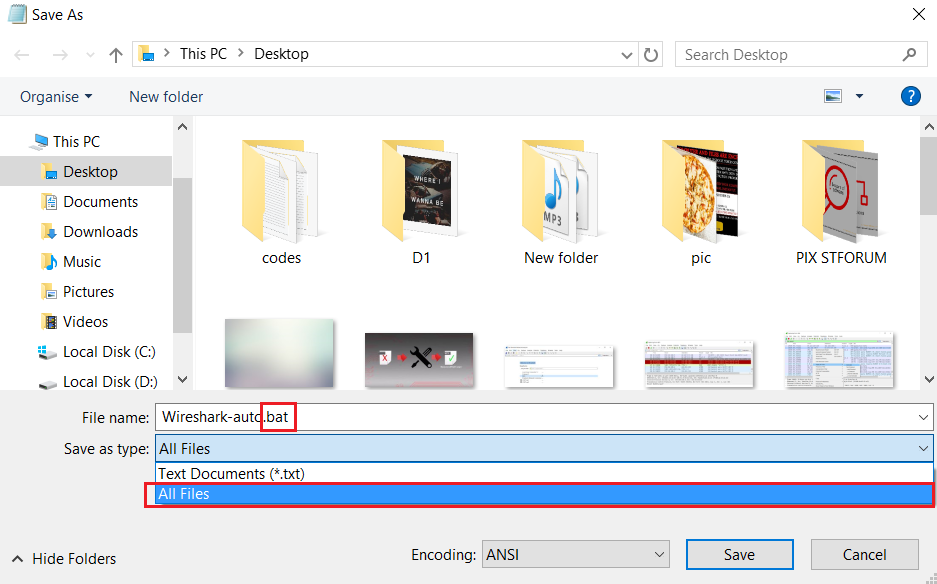
Step 6: Save the newly created text document as a .bat file, by going to File>Save As… and choosing All Files after which typing .BAT as a file extension, like the picture below shows. Make sure the name of the file and the location where you save it are easy to find:
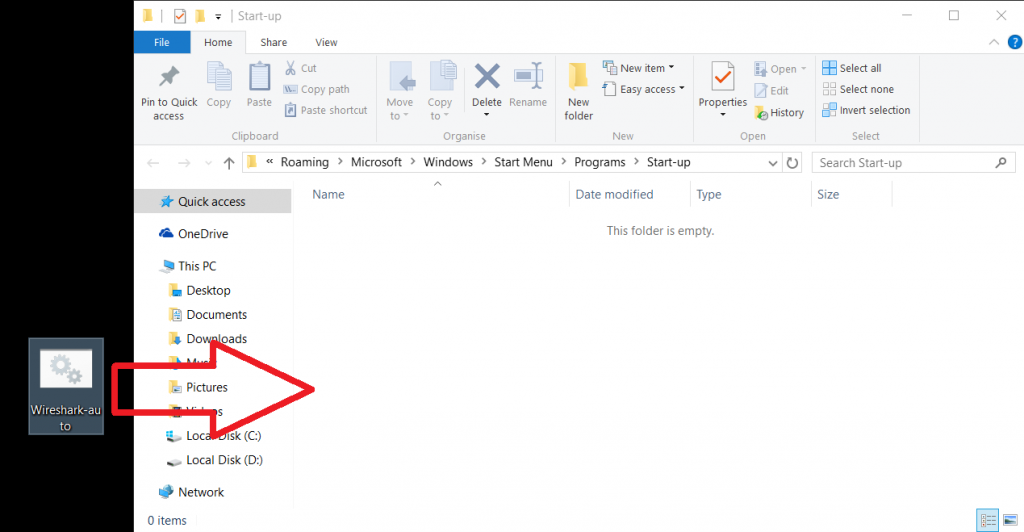
Step 7: Paste the .bat file in the Windows startup folder. The original location of the folder is:
→ C:\Users\Username\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup,/p>
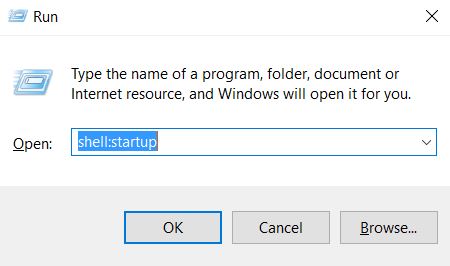
To easily access it, press Windows Button + R key combination and in the Window box type – shell:startup, like the picture below shows and click OK:
After your computer is restarted, if the ransomware virus encrypts your files after which generates a key and sends it to the cyber-criminals’ servers, you should be able to intercept the communication packets and analyze them.
Step 8: How to analyze the traffic?
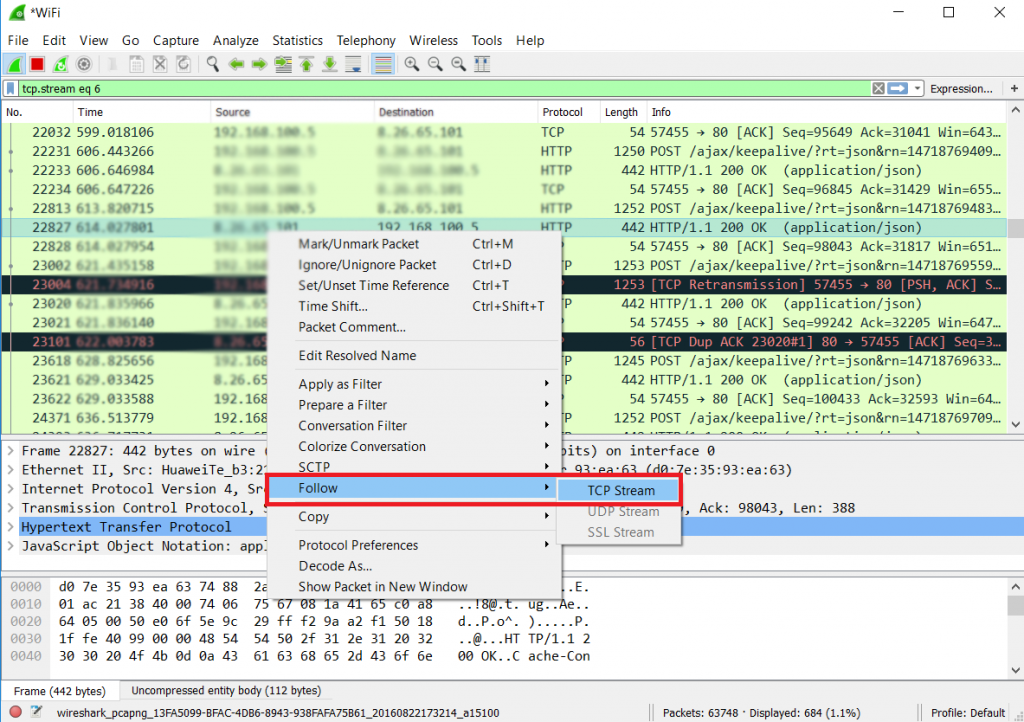
To analyze the traffic of a given packet, simply right-click it and then click on the following to intercept the traffic:
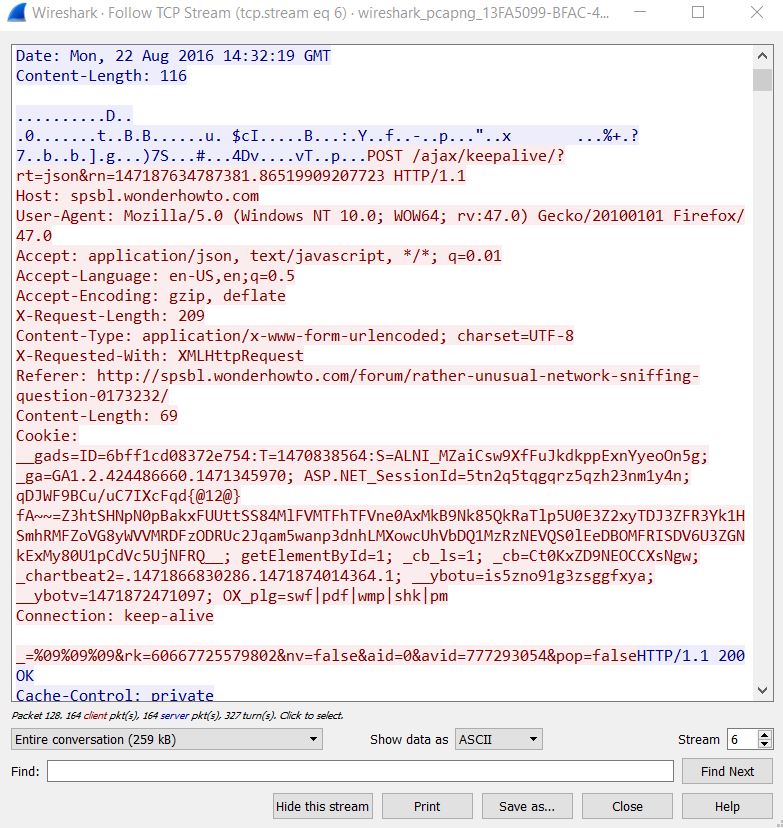
After doing this, a Window will appear with the information. Make sure to inspect the information carefully and look for keywords that give away the encryption keys, like encrypted, RSA, AES, etc. Take your time and check the packets’ size, make sure that they are similar to the size of a key file.

Sniffing Ransomware Decryption Keys – Things You Need To Know
Like mentioned before, this tutorial is fully theoretical and in case you cannot cope with it and sniff out the keys, we strongly advise you to remove the ransomware that has infected you and attempt restoring your files using the step-by-step instructions below. Also, if you are going to attempt this method, we strongly advise you to test it out first on your computer and see the traffic. An example of how researchers have identified traffic by ransomware is the research, performed by PaloAlto network experts on Locky ransomware, which we also advise you to check.
- Step 1
- Step 2
- Step 3
- Step 4
- Step 5
Step 1: Scan for Ransomware with SpyHunter Anti-Malware Tool



Ransomware Automatic Removal - Video Guide
Step 2: Uninstall Ransomware and related malware from Windows
Here is a method in few easy steps that should be able to uninstall most programs. No matter if you are using Windows 10, 8, 7, Vista or XP, those steps will get the job done. Dragging the program or its folder to the recycle bin can be a very bad decision. If you do that, bits and pieces of the program are left behind, and that can lead to unstable work of your PC, errors with the file type associations and other unpleasant activities. The proper way to get a program off your computer is to Uninstall it. To do that:


 Follow the instructions above and you will successfully delete most unwanted and malicious programs.
Follow the instructions above and you will successfully delete most unwanted and malicious programs.
Step 3: Clean any registries, created by Ransomware on your computer.
The usually targeted registries of Windows machines are the following:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
You can access them by opening the Windows registry editor and deleting any values, created by Ransomware there. This can happen by following the steps underneath:


 Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Before starting "Step 4", please boot back into Normal mode, in case you are currently in Safe Mode.
This will enable you to install and use SpyHunter 5 successfully.
Step 4: Boot Your PC In Safe Mode to isolate and remove Ransomware





Step 5: Try to Restore Files Encrypted by Ransomware.
Method 1: Use STOP Decrypter by Emsisoft.
Not all variants of this ransomware can be decrypted for free, but we have added the decryptor used by researchers that is often updated with the variants which become eventually decrypted. You can try and decrypt your files using the instructions below, but if they do not work, then unfortunately your variant of the ransomware virus is not decryptable.
Follow the instructions below to use the Emsisoft decrypter and decrypt your files for free. You can download the Emsisoft decryption tool linked here and then follow the steps provided below:
1 Right-click on the decrypter and click on Run as Administrator as shown below:

2. Agree with the license terms:

3. Click on "Add Folder" and then add the folders where you want files decrypted as shown underneath:

4. Click on "Decrypt" and wait for your files to be decoded.

Note: Credit for the decryptor goes to Emsisoft researchers who have made the breakthrough with this virus.
Method 2: Use data recovery software
Ransomware infections and Ransomware aim to encrypt your files using an encryption algorithm which may be very difficult to decrypt. This is why we have suggested a data recovery method that may help you go around direct decryption and try to restore your files. Bear in mind that this method may not be 100% effective but may also help you a little or a lot in different situations.
Simply click on the link and on the website menus on the top, choose Data Recovery - Data Recovery Wizard for Windows or Mac (depending on your OS), and then download and run the tool.
Ransomware-FAQ
What is Ransomware Ransomware?
Ransomware is a ransomware infection - the malicious software that enters your computer silently and blocks either access to the computer itself or encrypt your files.
Many ransomware viruses use sophisticated encryption algorithms to make your files inaccessible. The goal of ransomware infections is to demand that you pay a ransom payment to get access to your files back.
What Does Ransomware Ransomware Do?
Ransomware in general is a malicious software that is designed to block access to your computer or files until a ransom is paid.
Ransomware viruses can also damage your system, corrupt data and delete files, resulting in the permanent loss of important files.
How Does Ransomware Infect?
Via several ways.Ransomware Ransomware infects computers by being sent via phishing emails, containing virus attachment. This attachment is usually masked as an important document, like an invoice, bank document or even a plane ticket and it looks very convincing to users.
Another way you may become a victim of Ransomware is if you download a fake installer, crack or patch from a low reputation website or if you click on a virus link. Many users report getting a ransomware infection by downloading torrents.
How to Open .Ransomware files?
You can't without a decryptor. At this point, the .Ransomware files are encrypted. You can only open them once they are decrypted using a specific decryption key for the particular algorithm.
What to Do If a Decryptor Does Not Work?
Do not panic, and backup the files. If a decryptor did not decrypt your .Ransomware files successfully, then do not despair, because this virus is still new.
Can I Restore ".Ransomware" Files?
Yes, sometimes files can be restored. We have suggested several file recovery methods that could work if you want to restore .Ransomware files.
These methods are in no way 100% guaranteed that you will be able to get your files back. But if you have a backup, your chances of success are much greater.
How To Get Rid of Ransomware Virus?
The safest way and the most efficient one for the removal of this ransomware infection is the use a professional anti-malware program.
It will scan for and locate Ransomware ransomware and then remove it without causing any additional harm to your important .Ransomware files.
Can I Report Ransomware to Authorities?
In case your computer got infected with a ransomware infection, you can report it to the local Police departments. It can help authorities worldwide track and determine the perpetrators behind the virus that has infected your computer.
Below, we have prepared a list with government websites, where you can file a report in case you are a victim of a cybercrime:
Cyber-security authorities, responsible for handling ransomware attack reports in different regions all over the world:
Germany - Offizielles Portal der deutschen Polizei
United States - IC3 Internet Crime Complaint Centre
United Kingdom - Action Fraud Police
France - Ministère de l'Intérieur
Italy - Polizia Di Stato
Spain - Policía Nacional
Netherlands - Politie
Poland - Policja
Portugal - Polícia Judiciária
Greece - Cyber Crime Unit (Hellenic Police)
India - Mumbai Police - CyberCrime Investigation Cell
Australia - Australian High Tech Crime Center
Reports may be responded to in different timeframes, depending on your local authorities.
Can You Stop Ransomware from Encrypting Your Files?
Yes, you can prevent ransomware. The best way to do this is to ensure your computer system is updated with the latest security patches, use a reputable anti-malware program and firewall, backup your important files frequently, and avoid clicking on malicious links or downloading unknown files.
Can Ransomware Ransomware Steal Your Data?
Yes, in most cases ransomware will steal your information. It is a form of malware that steals data from a user's computer, encrypts it, and then demands a ransom in order to decrypt it.
In many cases, the malware authors or attackers will threaten to delete the data or publish it online unless the ransom is paid.
Can Ransomware Infect WiFi?
Yes, ransomware can infect WiFi networks, as malicious actors can use it to gain control of the network, steal confidential data, and lock out users. If a ransomware attack is successful, it could lead to a loss of service and/or data, and in some cases, financial losses.
Should I Pay Ransomware?
No, you should not pay ransomware extortionists. Paying them only encourages criminals and does not guarantee that the files or data will be restored. The better approach is to have a secure backup of important data and be vigilant about security in the first place.
What Happens If I Don't Pay Ransom?
If you don't pay the ransom, the hackers may still have access to your computer, data, or files and may continue to threaten to expose or delete them, or even use them to commit cybercrimes. In some cases, they may even continue to demand additional ransom payments.
Can a Ransomware Attack Be Detected?
Yes, ransomware can be detected. Anti-malware software and other advanced security tools can detect ransomware and alert the user when it is present on a machine.
It is important to stay up-to-date on the latest security measures and to keep security software updated to ensure ransomware can be detected and prevented.
Do Ransomware Criminals Get Caught?
Yes, ransomware criminals do get caught. Law enforcement agencies, such as the FBI, Interpol and others have been successful in tracking down and prosecuting ransomware criminals in the US and other countries. As ransomware threats continue to increase, so does the enforcement activity.
About the Ransomware Research
The content we publish on SensorsTechForum.com, this Ransomware how-to removal guide included, is the outcome of extensive research, hard work and our team’s devotion to help you remove the specific malware and restore your encrypted files.
How did we conduct the research on this ransomware?
Our research is based on an independent investigation. We are in contact with independent security researchers, and as such, we receive daily updates on the latest malware and ransomware definitions.
Furthermore, the research behind the Ransomware ransomware threat is backed with VirusTotal and the NoMoreRansom project.
To better understand the ransomware threat, please refer to the following articles which provide knowledgeable details.
As a site that has been dedicated to providing free removal instructions for ransomware and malware since 2014, SensorsTechForum’s recommendation is to only pay attention to trustworthy sources.
How to recognize trustworthy sources:
- Always check "About Us" web page.
- Profile of the content creator.
- Make sure that real people are behind the site and not fake names and profiles.
- Verify Facebook, LinkedIn and Twitter personal profiles.




I have tried to follow your recommendations about wireshark and somehow I get to find several lines that contain the following description in “info”:
“Server Hello, Certificate, Certificate status, Server key exchange, Server Hello done”
“Client key exchange, Change Cipher Spec, Encrypted Handshake message”
Then Application Data……
And this goes on and on all the time between one source and one destination (always the same).
I can do a right click on the line, then “follow” and “TCP” : it opens a window with a dialogue but i don’t know if I could find in it a “key” and I don’t know either how to recognize it. It doesn’t look like a common text, but includes a mix between words, net adresses, symbols…
Let’s assume it’s possible ang I find it, how then coul I use it? I wouldn’t know how to build my own working decryptor.
Is there anyone here who knows more about all of this and tried the way of wireshark sniffing and would have some advice to help me use the software and get to discover my “key”?
Thank you for your time
Hello, please see the following filters which you can use on the filter box on top of where the packets are of your Wireshark software:
1. ip.addr ==10.0.0.1 [Sets a filter for any packet with 10.0.0.1, as either the
source or dest]
2. ip.addr==10.0.0.1 && ip.addr==10.0.0.2 [sets
a conversation filter between the two defined IP addresses]
3. http or dns [sets
a filter to display all http and dns]
4. tcp.port==4000
[sets a filter for any TCP packet with 4000 as a source or dest port]
5. tcp.flags.reset==1
[displays all TCP resets]
6. http.request
[displays all HTTP GET requests]
7. tcp contains
traffic [displays all TCP packets that contain the word ‘traffic’.
Excellent when searching on a specific string or user ID]
8. !(arp or icmp or
dns) [masks out arp, icmp, dns, or whatever other protocols may be
background noise. Allowing you to focus on the traffic of interest]
9. udp contains
33:27:58 [sets a filter for the HEX values of 0x33 0x27 0x58 at any
offset]
10. tcp.analysis.retransmission
[displays all retransmissions in the trace. Helps when tracking down slow
application performance and packet loss]
You can also find other useful recommendations there. Also, bear in mind that you should focus on the POST traffic when an infection takes place. If you have the malware sample, try to reinfect a testing computer while monitoring the packets. This may help you gain a deeper understanding on how the malware communicates.
In addition to this, when you “Follow TCP Stream” of a given packet, Wireshark has the so-called “SSL Dissector” which in some cases can be used to decipher some of the data in there and make sense of it. Ransomware is constantly evolving, however and may not also directly send the decryption key, but instead upload a .KEY file to the cyber-criminals’ command servers which is also encrypted with a strong algorithm. So if you are using WIreshark, first make sure the virus does not create such a file and directly sends the information via TCP or other form.
uploads.disquscdn.com/images/6df279d43a1a06afaa3be30dec6ba88d76cc48bc0475bad505862d8218082139.jpg
uploads.disquscdn.com/images/dcb0ed4b8a03a87ddecfd8343fe75b22c6a5686d75675e2e8603800301d12927.jpg
Is it work with Cerber ransomware?
I have been infected by spora. I have the html file with my ID and a lot of pairs with encripted and non encripted files. Can you extract the encription keys from all of these in order to decript the rest of my files? Or do you know somebody who can do it? Thanks.
calin.huidu@gmail.com
Tolle Methode. Manchmal geht es auch einfacher wenn man die Lücken von Dharma kennt. Wir werden diese nicht posten, da wir sonst die Programmierer darauf aufmerksam machen.
Hi, Is it possible to decrypt files encrypted with the Rapid Ramsomware virus?
Hello, has anyone managed to successfully decrypt files encrypted with the Rapid Ransomware?
Hello, has anyone managed to successfully decrypt files encrypted with the Rapid Ransomware?
Me infectó mis archivos un virus que agrega la extension .krab, cómo puedo desencriptar los archivos.
Hey I just got infected by Hermes 2.1 available on the net
Bonjour l’odinateur de mon patron est infecté que faire cela contient de nombreux document sensible et important. Il est infecté par Grandcrab V4 je peut avoir une clé qui fonctionne pour ton débloquer et supprimer ce malware s’il vous plait.
Please help me the .moresa virus extention is not decrypted by the Stop Decrypter from my computer all my files have been decrypted with this moresa virus
No key for ID: PBADSc0wL8KOzd5eGIaVThjIPeGxRqrsQgvU3qt1 (.moresa )
No key for ID: thCga3VaHug7jcvBWukhPrjC7a214iSfVCsbRuQi (.moresa )
Unidentified ID: PBADSc0wL8KOzd5eGIaVThjIPeGxRqrsQgvU3qt1 (.moresa )
Unidentified ID: thCga3VaHug7jcvBWukhPrjC7a214iSfVCsbRuQi (.moresa )
Proof is below
—————————————-
STOPDecrypter v2.0.2.3
OS Microsoft Windows NT 6.2.9200.0, .NET Framework Version 4.0.30319.42000—————————————-
Error on file ‘E:\autorun.inf\lpt3.Drive_is_protected_against_flash_viruses_by_RegRun’: System.ArgumentException: FileStream will not open Win32 devices such as disk partitions and tape drives. Avoid use of “\\.\” in the path.
at System.IO.FileStream.Init(String path, FileMode mode, FileAccess access, Int32 rights, Boolean useRights, FileShare share, Int32 bufferSize, FileOptions options, SECURITY_ATTRIBUTES secAttrs, String msgPath, Boolean bFromProxy, Boolean useLongPath, Boolean checkHost)
at System.IO.FileStream..ctor(String path, FileMode mode, FileAccess access)
at STOPDecrypter.Decrypter.FileIsSupported(String filepath)
at STOPDecrypter.MainForm.DecryptDirectory(String location, Boolean delete)
Error on file ‘E:\comment.htt\lpt3.Drive_is_protected_against_flash_viruses_by_RegRun’: System.ArgumentException: FileStream will not open Win32 devices such as disk partitions and tape drives. Avoid use of “\\.\” in the path.
at System.IO.FileStream.Init(String path, FileMode mode, FileAccess access, Int32 rights, Boolean useRights, FileShare share, Int32 bufferSize, FileOptions options, SECURITY_ATTRIBUTES secAttrs, String msgPath, Boolean bFromProxy, Boolean useLongPath, Boolean checkHost)
at System.IO.FileStream..ctor(String path, FileMode mode, FileAccess access)
at STOPDecrypter.Decrypter.FileIsSupported(String filepath)
at STOPDecrypter.MainForm.DecryptDirectory(String location, Boolean delete)
Error on file ‘E:\desktop.ini\lpt3.Drive_is_protected_against_flash_viruses_by_RegRun’: System.ArgumentException: FileStream will not open Win32 devices such as disk partitions and tape drives. Avoid use of “\\.\” in the path.
at System.IO.FileStream.Init(String path, FileMode mode, FileAccess access, Int32 rights, Boolean useRights, FileShare share, Int32 bufferSize, FileOptions options, SECURITY_ATTRIBUTES secAttrs, String msgPath, Boolean bFromProxy, Boolean useLongPath, Boolean checkHost)
at System.IO.FileStream..ctor(String path, FileMode mode, FileAccess access)
at STOPDecrypter.Decrypter.FileIsSupported(String filepath)
at STOPDecrypter.MainForm.DecryptDirectory(String location, Boolean delete)
Error: System.UnauthorizedAccessException: (5) Access is denied: [E:\System Volume Information]
at Alphaleonis.Win32.NativeError.ThrowException(UInt32 errorCode, String readPath, String writePath) in C:\Users\jjangli\Documents\GitHub\AlphaFS\AlphaFS\NativeError.cs:line 121
at Alphaleonis.Win32.Filesystem.FindFileSystemEntryInfo.ThrowPossibleException(UInt32 lastError, String pathLp) in C:\Users\jjangli\Documents\GitHub\AlphaFS\AlphaFS\Filesystem\FindFileSystemEntryInfo.cs:line 409
at Alphaleonis.Win32.Filesystem.FindFileSystemEntryInfo.FindFirstFile(String pathLp, WIN32_FIND_DATA& win32FindData, Boolean suppressException) in C:\Users\jjangli\Documents\GitHub\AlphaFS\AlphaFS\Filesystem\FindFileSystemEntryInfo.cs:line 297
at Alphaleonis.Win32.Filesystem.FindFileSystemEntryInfo.d__88`1.MoveNext() in C:\Users\jjangli\Documents\GitHub\AlphaFS\AlphaFS\Filesystem\FindFileSystemEntryInfo.cs:line 466
at STOPDecrypter.MainForm.DecryptDirectory(String location, Boolean delete)
———————————————–
Dear Sir my Computer has completely Damaged by newest Ransomware virus extention
” .moresa “. This extention has been attached with all of my computer files pictures videos pdf software. Though virus has removed after using SpyHunter Anti-Malware Tool. But now my all personal data is not decrypting due to this ” .moresa ” extention virus. Please help me thanks. I received the following data from the hackers:
ATTENTION!
Don’t worry my friend, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.
To get this software you need write on our e-mail:
Reserve e-mail address to contact us:
Support Telegram account:
Your personal ID:
069OspdywaduiShdktrecthCga3VaHug7jcvBWukhPrjC7a214iSfVCsbRuQi
Now my personal Files are in the following shape:
.cdr, .pdf, .jpeg. etc etc
HI,
I have also the same trouble since april 22nd
I have tried several methods but in vain
need help
anyone has encountered “stone” encryption? i definitely need a solution, it has affected pictures of my late father and brother.
Hello,
Actaully my files are infected with encryption and asking me for money and i can’t afford his asking price.
my Files are infected with the extension of .recuz
please help me to retrieve my files.
Here this is the guy who is calling us friend but he is stigma on the human being.
and this is the readme text file lines.
ATTENTION!
Don’t worry my friend, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.
To get this software you need write on our e-mail:
bufalo@firemail.cc
Reserve e-mail address to contact us:
gorentos@bitmessage.ch
Our Telegram account:
@datarestore
Your personal ID:
091hushF63iUYSFDsdf7ULShpYyln4fiZkjMaQ6NbXD5vUCTYp5ieGdNCcq4
Sorry it was not .RECUZ but it is .REZUC
As Nabin’s data is infected, same my data is infected with this .REZUC
Bonjour,
je suis infecté par le virus .radman qui a decrypté tout mes fichiers. y’a t’il une solution pour decrypter mes fichiers?
j’ai essayé:
– Stopdecrypter
– Rakhnidecryptor
– …etc
mais rien de positif.
Merci
my system is ransome ware phobos. how can I descript my files.
Hi, TA!
Currently, no decrypter for Phobos ransomware is available. However, we recommend that you save your encrypted files and wait for a decrypter. Security researchers may be able to crack its code soon. Meanwhile, you can try alternative data recovery software as suggested in Step 5 from this how-to guide.
Is anyone has experience with .tocue ransomware? I try to use STOPDecryptor, but seems like there is no offline ID.
Then I looking for the ID, follow this guidance, but feel confuse in the step number 8. how to choose or which the appropriate packet that we should follow the stream?
HERAD Extension File Ransom Virus
Hi,
All my computer files have been infected and the .heard extension has been added to all files.
Please help to resolve the problem.
Thank you
How to decrypt “RSALIVE” extension ransomware infected file?
Hi Jummadon,
Here you can read more about the ransomware here – sensorstechforum.com/rsalive-virus-remove/
Unfortunately, at this point no free decryption tool for Scarab ransomware versions is available. So back up your .RSALIVE encrypted files and wait for a solution. While you are waiting you can try to restore .rsalive files with the help of the alternative methods mentioned in Step 5 form the removal guide above.
How to decrypt MTOGAS extension ransomware infected files? I got so many troubles, please i need help!
I tried STOPDecryptor, restore the operational system and another things.
everybody got a random encryption, we just need to find encryption method for decrypting files.
My files are encrypted by .npsk extension
for decryption process i need the same ransome-were program.
my ransome-were was deleted
Any one With solution please please Reply —
tutti i miei file sono con estensione .tuid
Come posso fare a recuperare tutto, esoste una chiave per l’id online?? Anche il programma di contabilità risulta criptato e sono nei guai.
Resto in attesa di un Vs riscontro alla presente