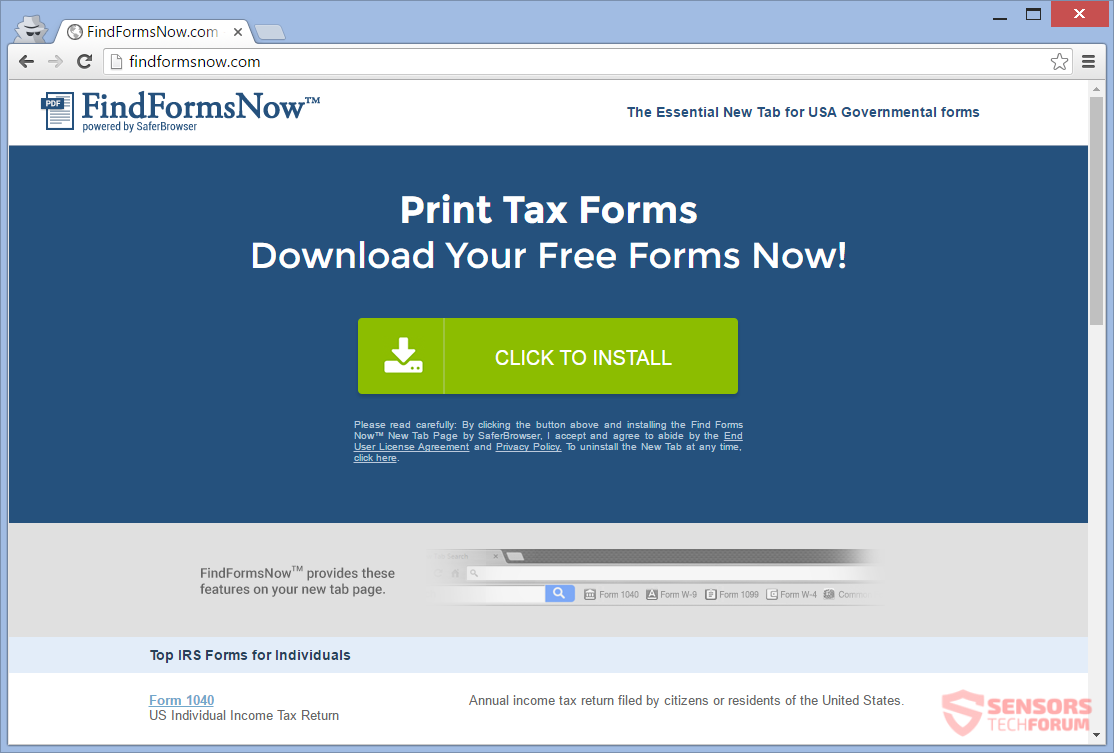
Remove FindFormsNow(.)com and Search.searchffn(.)com Hijacker
FindFormsNow(.)com is a website that hosts an extension for a browser hijacker. The extension is of the same name. The site is considered an adware because it generates ads. The extension is a version of the related browser hijacker. This…