This article is dedicated to the various ways through which scams infiltrate our digital interactions, offering insights into common fraudulent practices and laying out practical strategies for protection. Read on to discover how to build your defenses against the sophisticated deceits of today’s online scams.

Threat Summary
| Name | Online Scam |
| Type | Phishing; Tech Support Scam; Investment and Cryptocurrency Scam; Romance Scam |
| Removal Time | Approximately 15 minutes to scan the whole system and remove any discovered threats |
| Detection Tool |
See If Your System Has Been Affected by malware
Download
Malware Removal Tool
|
What Are Online Scams?
Online scams are deceptive strategies executed through the internet, aiming to trick individuals into handing over sensitive information or stealing money directly. These scams are not constrained to a single method but manifest through various channels such as phishing emails, fraudulent websites, and too-good-to-be-true investment opportunities, utilizing social engineering to exploit and manipulate victims.
An online scam operates by casting a wide net, hoping to catch unsuspecting individuals through deceitful practices. It could involve emails pretending to be from legitimate organizations, social media messages from fake profiles, or websites mirroring legitimate businesses. The ultimate goal is to trick individuals into revealing personal, financial, or other sensitive information or to directly transfer money to the scammers.
The Most Common Types of Online Fraud
The digital space is rife with various types of online fraud, targeting users in numerous ways:
Why Email Phishing Is Still Effective
Email phishing remains a prevalent method for scammers, using forged emails to extract sensitive information from recipients. These emails often mimic the appearance and tone of legitimate emails from well-known organizations, urging the recipient to act urgently – such as updating payment information or confirming account details – leading them to fraudulent websites designed to steal their information. Another popular form of phishing is the so-called sextortion scam.
The Rise of Social Media Scams
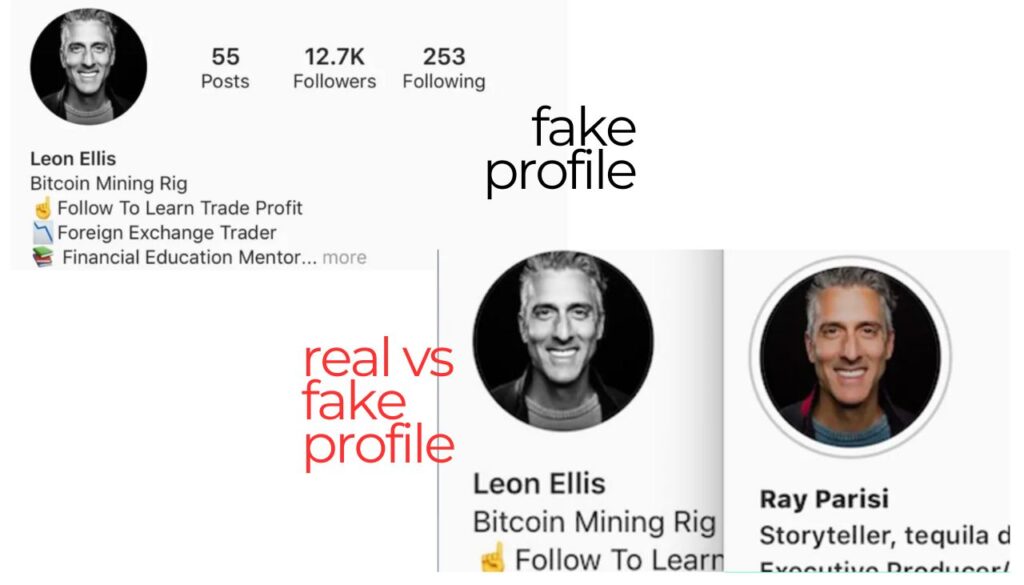
Social media platforms such as Instagram and Facebook have become a fertile ground for scams, with fraudsters creating fake profiles or hijacking existing ones to commit fraud. They engage in acts ranging from running fake advertisements and fake profiles to conducting romance scams, preying on the emotional vulnerability of users. The interactive nature of these platforms makes it easier for scammers to build trust and manipulate individuals into divulging personal information or sending money.
Online Shopping Scams: A Modern Consumer’s Nemesis
Online shopping scams trick consumers with the promise of high-value goods at low prices on fake or counterfeit websites. These sites often advertise on legitimate platforms and leverage the appeal of luxury items or hard-to-find goods to lure shoppers. Victims may end up with counterfeit products, inferior goods, or, in some cases, nothing at all. Payment methods requested by scammers, such as wire transfers or cryptocurrencies, are often untraceable, complicating the process of recovery and reporting.
The Dangerous Allure of Investment and Cryptocurrency Scams
Investment and crypto scams exploit the allure of high returns with supposedly low risk. Scammers use sophisticated tactics, including fake testimonials and manipulated news articles, to promote fraudulent investment opportunities. These schemes promise significant returns, exploiting the lack of investment knowledge and the desire for quick gains among potential victims. By the time the deception is uncovered, the scammers and the money are often gone.
Each of these scams leverages digital communication’s reach and anonymity, underscoring the importance of vigilance and secure practices online. Implementing security measures like using comprehensive security solutions such as SpyHunter can help protect against malicious attempts to compromise devices and personal data. SpyHunter is designed to detect and remove malware, thwart phishing attempts, and keep your digital life secure, effectively guarding against the tactics scammers use to exploit online vulnerabilities.
Real-world Examples of Common Online Scams
How Romance Scams Prey on Emotional Vulnerability
Romance scams exploit the natural human desire for connection. Scammers create compelling fake profiles on dating sites or social media platforms, then engage in long-term discussions to build trust and emotional closeness. Once a strong bond is established, they concoct stories needing financial assistance, tapping into victims’ empathy and affection. From covering medical bills to helping with travel expenses to reunite, the requests seem legitimate but are designed to defraud. Identifying these frauds early involves recognizing sudden financial requests or sob stories as red flags, especially when coupled with an unwillingness to meet in person or via video calls.
The Psychology Behind Lottery and Advance Fee Scams
Lotteries and advance-fee scams exploit the universal dream of sudden wealth. These schemes often promise large sums of money, rewards, or exclusive opportunities in exchange for an upfront fee. The psychological lure here is twofold: greed and urgency. Scammers fabricate stories of pending large payouts or found wealth, only accessible after paying ‘small’ processing fees. Victims are led to believe that a small investment will lead to considerable gain, overlooking the inconsistency of the proposition. These scams also pressurize the victim to act quickly, hindering rational decision-making and exploiting emotional vulnerabilities. Awareness and skepticism are crucial defenses, as genuine entities do not require upfront payments for genuine prizes or financial gains.
Identifying and Avoiding Job and Employment Scams
With the increasing demand for remote and freelance work, job and employment scams are on the rise. These swindles often promise high earnings for little work or ask for money upfront for training, application processes, or equipment. Signs of such scams include job offers without interviews, guarantees of employment, and any request for financial transactions. To avoid falling prey, individuals should research the company, avoid sharing personal financial information, and be wary of any job requiring payment to start. Valid employers never charge employees for the opportunity to work. Instead, they invest in their team’s growth and success.
The Evolution of Tech Support Scams
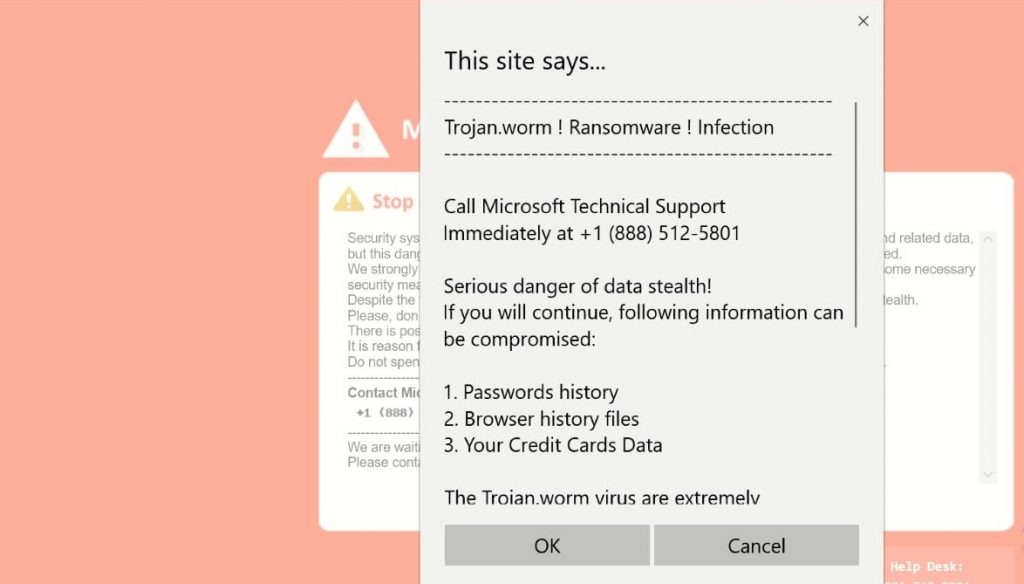
Tech support scams have evolved with the digital age, becoming increasingly sophisticated. Fraudsters pose as representatives from reputable companies, claiming to have detected a non-existent problem with your computer or online accounts. These scams often involve urgent requests for remote access to your computer, where scammers can install malware, steal personal information, or sell unnecessary software. Key indicators of these scams include unsolicited phone calls, emails, or pop-up warnings urging immediate action. To protect yourself, verify any such contact directly with the company involved and rely on reputable security software like SpyHunter to guard against malware and other threats. Remember, real tech support teams will never initiate unsolicited contact asking for sensitive information or access to your devices.
How to Recognize an Online Scam
Identifying online scams in today’s digital world is crucial for protecting your personal and financial information. Scammers constantly find new ways to deceive individuals, but knowing what to watch for can help you stay safe. Let’s delve into how you can spot these scams and safeguard your digital life.
Signs You’re Being Targeted by a Scammer
Recognizing the signs of a potential scam is your first line of defense against cybercriminals. Here are key indicators that you might be targeted:
- Unrealistic Offers: If an offer seems too good to be true, it likely is. Scammers often lure victims with amazing deals that don’t seem realistic.
- Pressure Tactics: Being rushed to make a decision should be a warning sign. Scammers use urgency to push their targets into making hasty decisions without proper judgement.
- Request for Personal Information: Legitimate companies will not ask for your sensitive details like bank information or passwords unsolicitedly.
- Odd Payment Methods: Be wary of requests for payment through gift cards, wire transfers, or cryptocurrencies. Such methods are preferred by scammers for their lack of traceability.
- Communication Off-platform: Scammers may try to move conversations away from secure platforms. This is to avoid detection and reduce your safety.
Being able to identify these signs can greatly increase your ability to avoid falling victim to online scams.
Why Strange Emails or Messages Should Raise Red Flags
Emails or messages that seem odd, out of place, or from unknown senders should immediately raise suspicions. Here’s why:
- Unexpected Attachments: Unsolicited emails with attachments could contain malware designed to harm your computer or steal personal information.
- Phishing Attempts: Scammers use phishing emails to impersonate legitimate companies. They often include links that lead to fake websites to steal your credentials.
- Generic Greetings: Generic or impersonal greetings are a hallmark of mass-sent scam emails.
- Spelling and Grammar Errors: Professional entities have proofreaders. Frequent errors in an email could indicate a scam.
- Requests for Sensitive Information: Any message asking for personal or financial information should be viewed with skepticism.
Always approach strange emails or messages with caution. Verify the sender’s email address, look out for odd requests or attachments, and do not click on any links without verifying their authenticity.
If ever in doubt about the legitimacy of an offer or a suspicious message, it’s wise to err on the side of caution. For those concerned about their digital security, SpyHunter offers comprehensive protection against malware, spyware, and other cyber threats, ensuring your online environment remains secure against the diverse tactics used by scammers today.
Being informed about the common signs of scams and understanding why certain emails or messages should be treated with suspicion can make all the difference in protecting yourself online. Stay vigilant, question offers that seem too favorable, and safeguard your digital footprint with robust security solutions like SpyHunter.
Steps to Take If You’ve Fallen Victim to a Scam
Falling victim to an online scam can be a distressing experience, leaving you feeling vulnerable and violated. If you find yourself in this unfortunate situation, knowing the immediate steps to take can help you mitigate the damage and protect yourself from further risk. Follow these guidelines to begin the recovery process and regain control of your personal and financial security.
Immediate Actions to Mitigate Damage
The moment you realize you’ve been scammed, quick action can prevent further harm. Here’s what you should do immediately:
- Cut off all contact with the scammer: Stop all communication with the fraudster. Block their email address, phone number, and unfriend or block them on social media platforms to prevent them from reaching out to you again or obtaining any more of your personal information.
- Contact your financial institution: Alert your bank or credit card provider about the scam. They can guide you through the process of protecting your accounts, including changing passwords and possibly reversing unauthorized transactions.
- Freeze your credit: By freezing your credit, you make it more difficult for a scammer to open new accounts in your name. Contact the major credit bureaus to implement a credit freeze as soon as possible.
- Change your passwords: Especially if you’ve shared sensitive information with the scammer, change all your key passwords. This includes your financial accounts, email, social media, and any other services where personal information is stored.
- Update your security software: In the case of clicking on malicious links or downloading suspicious attachments, ensure your antivirus software, such as SpyHunter, is up-to-date and run a full system scan to detect and remove any malware.
Taking these steps immediately can help lock down your personal information and begin the process of reclaiming your online presence and security.
Reporting Scams: When and Where
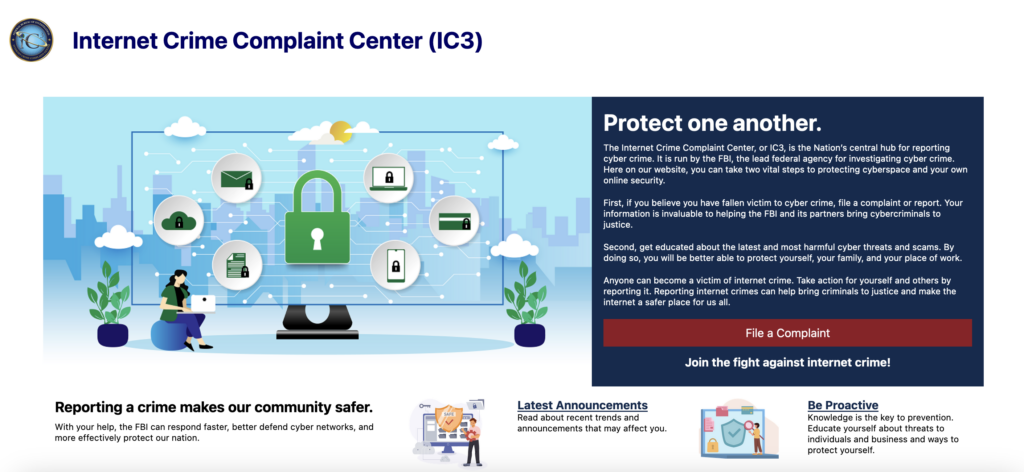
After securing your accounts and personal information, the next step is to report the scam. This not only helps you potentially recoup any financial losses but also aids in preventing others from falling victim to the same scam.
- Local authorities: Report the scam to your local police station. Provide as much information as possible, including any correspondence with the scammer, transaction details, and how you were initially contacted.
- Financial institutions: Inform your bank or credit card issuer about the scam if you haven’t already done so as part of securing your accounts. They may have additional steps for you to follow to report the fraud.
- The Federal Trade Commission (FTC): Reporting the scam to the FTC through their website helps them track scam patterns and advise the public on avoiding similar scams.
- Internet Crime Complaint Center (IC3): The IC3 is an essential resource for reporting internet crimes. Filing a complaint with them adds your report to a nationwide database that can help track down and prosecute cybercriminals.
Each report is a valuable step towards fighting back against scammers and protecting the community from future scams. While the thought of engaging in these processes may seem overwhelming, remember that you are contributing to a larger effort to curb online fraud and assist others who may be vulnerable to similar threats.
Though the immediate aftermath of falling for a scam can be challenging, taking these measured steps can help mitigate the damage and restore some peace of mind. Always remember to maintain vigilant online practices and update your cybersecurity measures regularly to protect against future scams. For comprehensive protection, consider employing security tools like SpyHunter that provide active monitoring and malware removal to keep your digital life secure.
Proven Strategies for Protecting Yourself Against Online Scams
With the rise of sophisticated online scams, safeguarding your digital presence has never been more crucial. By adopting a proactive approach to security, you can significantly reduce your risk of falling victim to cybercriminals. Here are several effective strategies designed to strengthen your defenses against online scams.
The Role of Internet Security Software in Scam Prevention
Internet security software plays a pivotal role in defending against the myriad of scams circulating online. These programs serve as the first line of defense, protecting against malware, phishing attempts, and various forms of cyber extortion. By continuously monitoring for suspicious activities and threats, internet security solutions help identify and block potentially harmful content before it can cause damage. Furthermore, they ensure that your personal information remains secure, guarding against unauthorized access and data breaches.
Why SpyHunter Is Your Ally Against Scammers
SpyHunter stands out as a robust ally in the fight against scammers. Designed with the latest detection technologies, it offers real-time protection against malware, ransomware, and phishing attempts. SpyHunter is intuitive, making it accessible for both tech-savvy users and those new to cyber defense. Its malware definitions database is regularly updated, ensuring that even the most recent threats are recognized and neutralized. For those seeking to fortify their digital security posture, SpyHunter presents a comprehensive solution.
Protecting Your Personal Information Online
One of the most effective tactics against online scams is to remain vigilant about your personal information. Sharing too much online, especially on social media, can inadvertently provide scammers with the data they need to target you. To maintain a secure online profile, it’s important to:
- Limit the personal information you share on social media and other online platforms.
- Regularly review and adjust your privacy settings on each platform to control who can see your data.
- Be mindful of phishing attempts that may come in the form of emails or messages, seeking to extract personal or financial details.
Taking these precautions can significantly reduce the likelihood of your information being compromised.
The Importance of Regular Software Updates and Secure Passwords
Keeping your software updated and using secure passwords are critical components of a strong online security strategy. Regular software updates not only introduce new features but also patch vulnerabilities that scammers could exploit. In addition, complex passwords that are unique for each account can make unauthorized access much more difficult for cybercriminals. Implementing these practices is key to safeguarding your digital identity and personal data.
- Ensure all your devices and applications are regularly updated to the latest versions.
- Use strong passwords that combine letters, numbers, and symbols, and consider using a reputable password manager.
- Enable two-factor authentication (2FA) where available for an added layer of security.
By integrating these habits into your daily online routine, you enhance your defenses against the increasingly sophisticated scams that threaten digital safety.
The Future of Online Scams
As technology advances, so too does the ingenuity of online scams. The digital age has brought about sophisticated threats that were unimaginable just a decade ago, pushing the boundaries of what we must do to stay safe online. Understanding these evolving risks is the first step in protecting ourselves against the cunning tactics of cybercriminals.
Anticipating New Scam Techniques
In an ever-connected world, the techniques used by scammers grow more complex by the day. From deepfake technology to sophisticated phishing schemes that mimic legitimate communication from trusted institutions, these scams are constantly adapting. Emerging threats also include the increased use of artificial intelligence by cybercriminals to automate scam messages and calls, making them more convincing and harder to detect.
To stay one step ahead, individuals and organizations must remain vigilant, continuously educating themselves about the latest scam methods. This includes being aware of the signs of phishing emails, such as unexpected requests for personal information or payments and emails with poor grammar and spelling. Additionally, staying updated on news regarding data breaches can alert you to potential threats related to your personal information.
How Technology Is Shaping the Fight Against Scams
Fortunately, as scam techniques have evolved, so have the tools we can use to defend against them. Antivirus software and personal firewalls are more sophisticated than ever, offering not just protection against malware but also features like safe browsing, email scanning, and even home network security. These tools are essential in identifying and blocking threats before they can do harm.
Artificial intelligence and machine learning are also playing a crucial role in detecting fraudulent patterns and protecting sensitive information. For example, Banks and financial institutions now employ advanced algorithms to spot unusual transactions in real-time, helping to prevent financial fraud.
On an individual level, using complex, unique passwords for different accounts and enabling multi-factor authentication wherever possible adds an extra layer of security. Similarly, keeping software updated can close security vulnerabilities, and being cautious about the information shared on social media can reduce the risk of identity theft.
When it comes to combatting online scams, being proactive is key. Installing reputable security software like SpyHunter offers comprehensive protection against malware, ransomware, and other malicious threats. Its real-time scanning capabilities can identify and neutralize threats, ensuring that your online experience remains safe and secure. By leveraging technologies designed to enhance cybersecurity, individuals and businesses can significantly reduce their vulnerability to online scams.
In conclusion, the fight against online scams is ongoing, with both threats and defenses evolving rapidly. By staying informed, using the right tools, and practicing good cyber hygiene, we can protect ourselves against the cunning tricks of cybercriminals and enjoy the benefits of the digital world with peace of mind.
- Windows
- Mac OS X
- Google Chrome
- Mozilla Firefox
- Microsoft Edge
- Safari
- Internet Explorer
- Stop Push Pop-ups
How to Remove Online Scam from Windows.
Step 1: Scan for Online Scam with SpyHunter Anti-Malware Tool



Step 2: Boot Your PC In Safe Mode





Step 3: Uninstall Online Scam and related software from Windows
Uninstall Steps for Windows 11
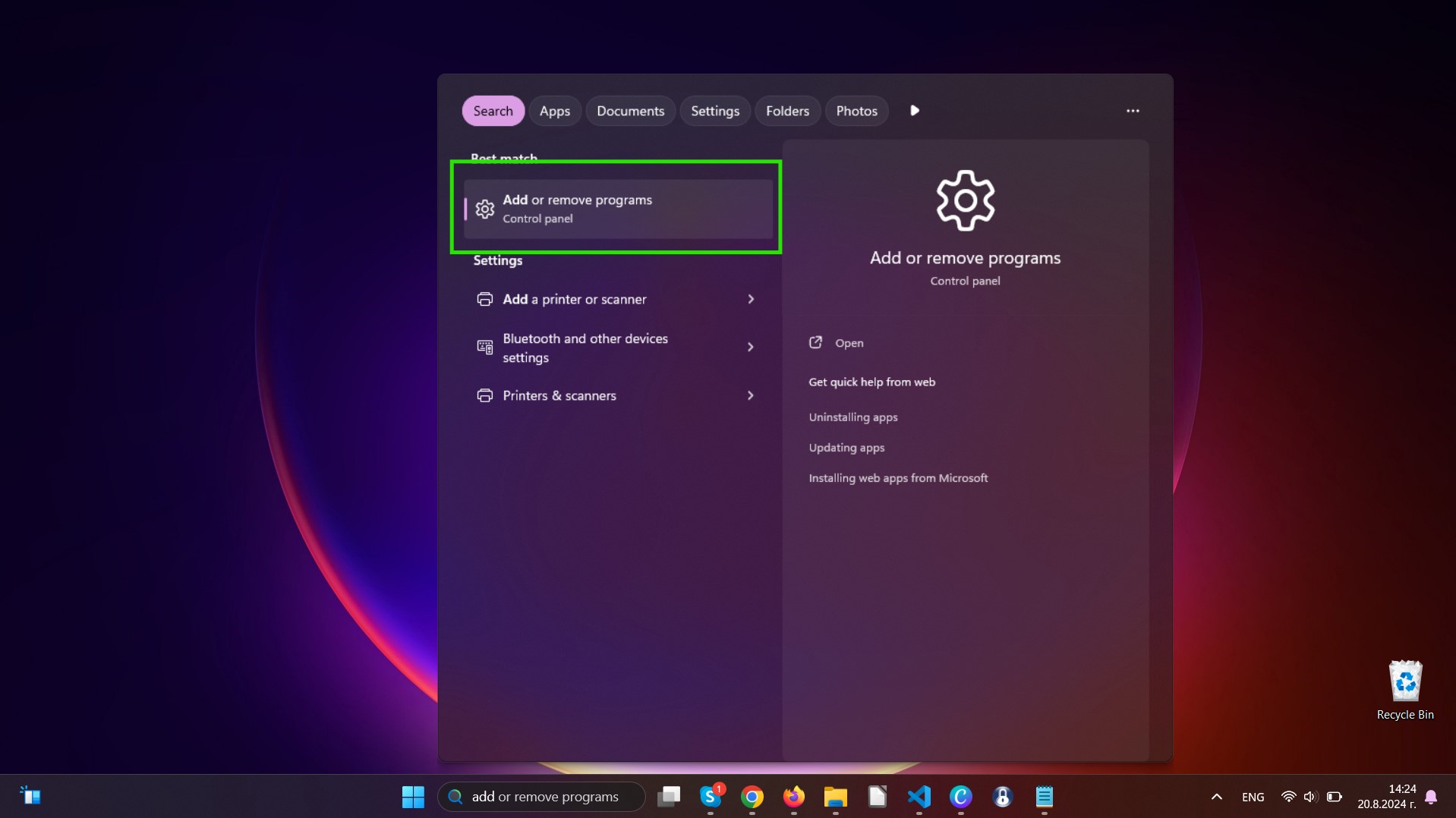
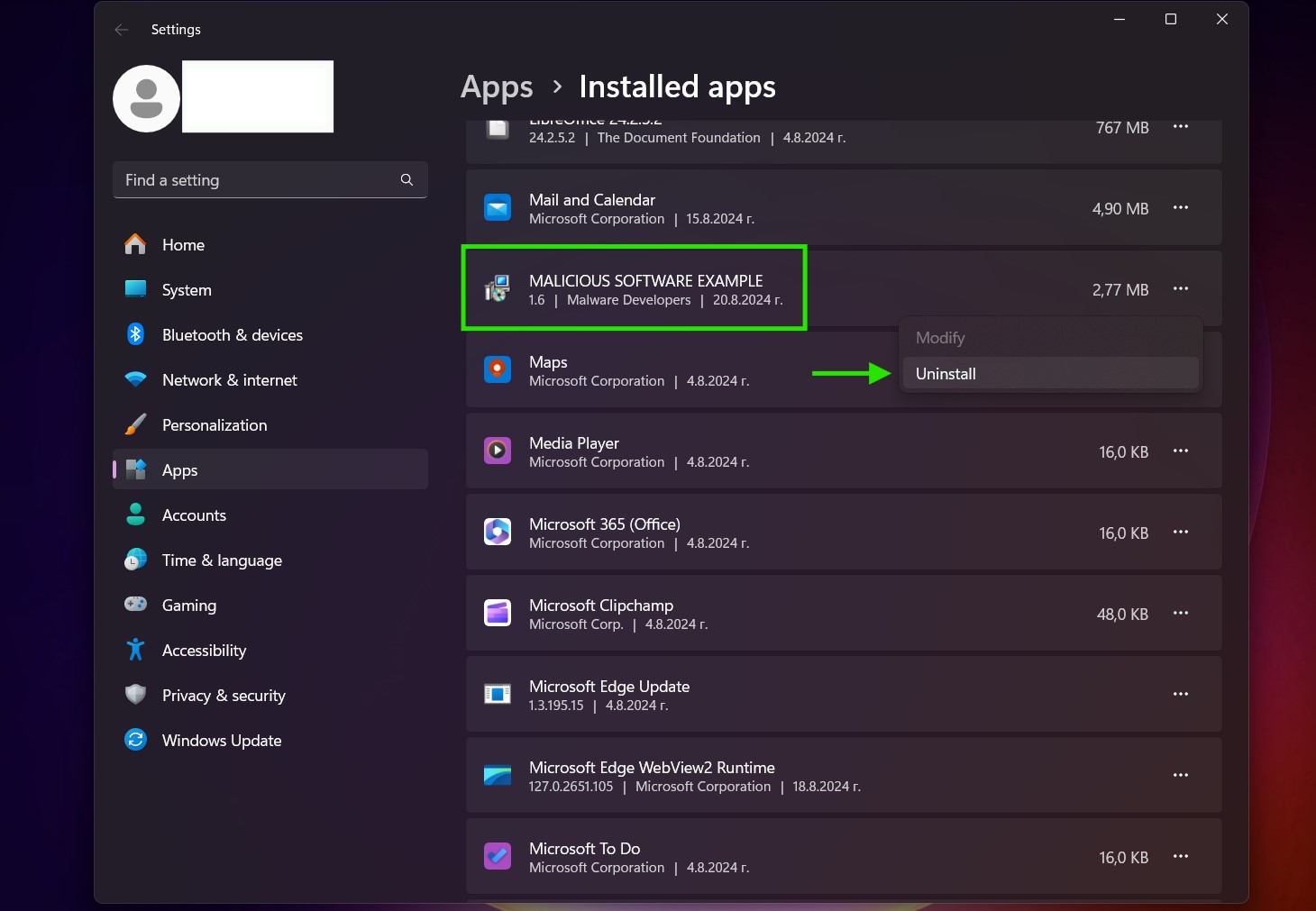
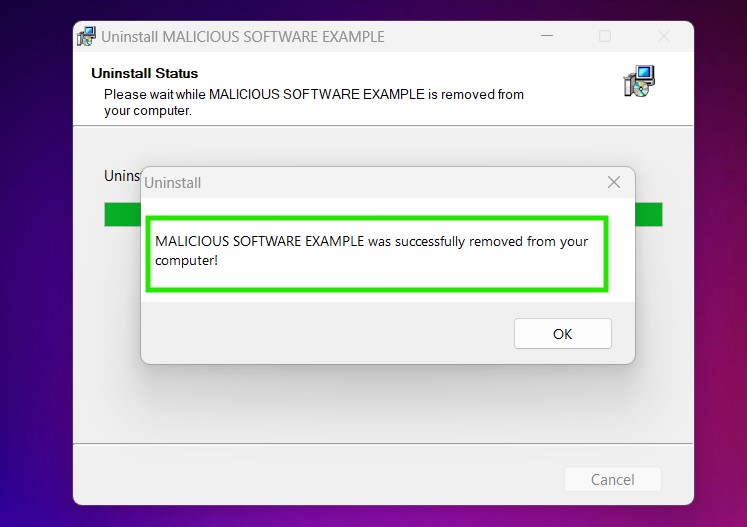
Uninstall Steps for Windows 10 and Older Versions
Here is a method in few easy steps that should be able to uninstall most programs. No matter if you are using Windows 10, 8, 7, Vista or XP, those steps will get the job done. Dragging the program or its folder to the recycle bin can be a very bad decision. If you do that, bits and pieces of the program are left behind, and that can lead to unstable work of your PC, errors with the file type associations and other unpleasant activities. The proper way to get a program off your computer is to Uninstall it. To do that:


 Follow the instructions above and you will successfully uninstall most programs.
Follow the instructions above and you will successfully uninstall most programs.
Step 4: Clean Any registries, Created by Online Scam on Your PC.
The usually targeted registries of Windows machines are the following:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
You can access them by opening the Windows registry editor and deleting any values, created by Online Scam there. This can happen by following the steps underneath:


 Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Video Removal Guide for Online Scam (Windows).
Get rid of Online Scam from Mac OS X.
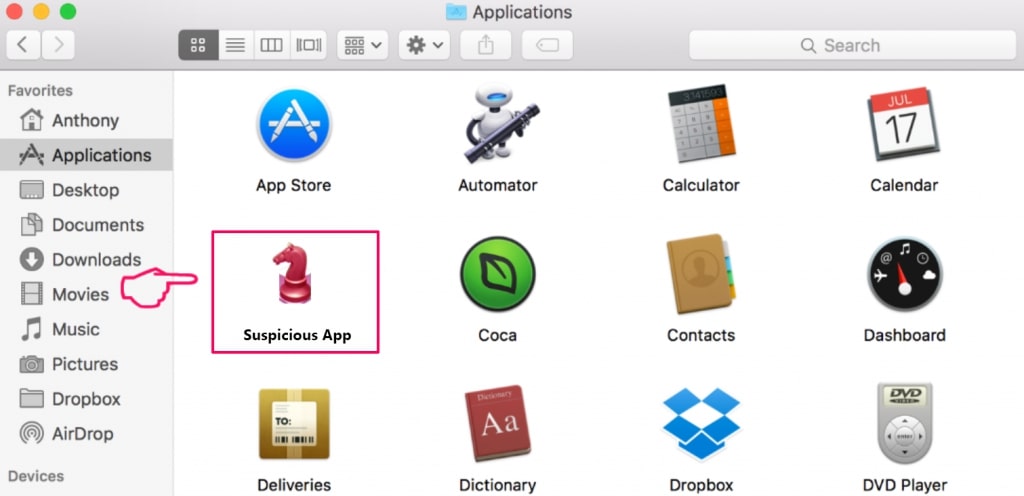
Step 1: Uninstall Online Scam and remove related files and objects
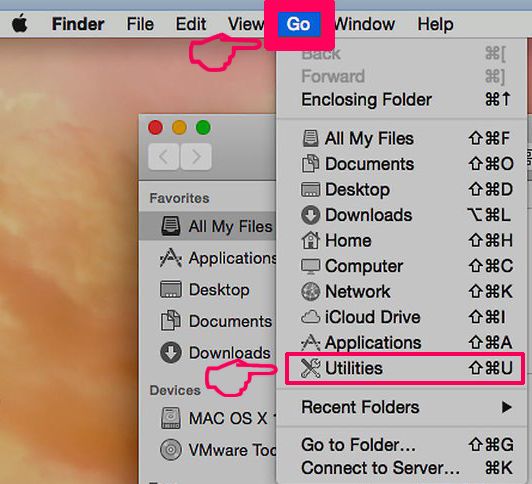
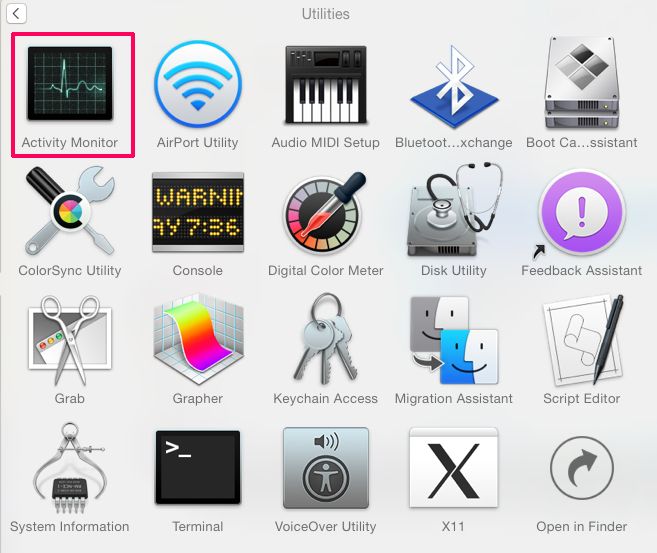
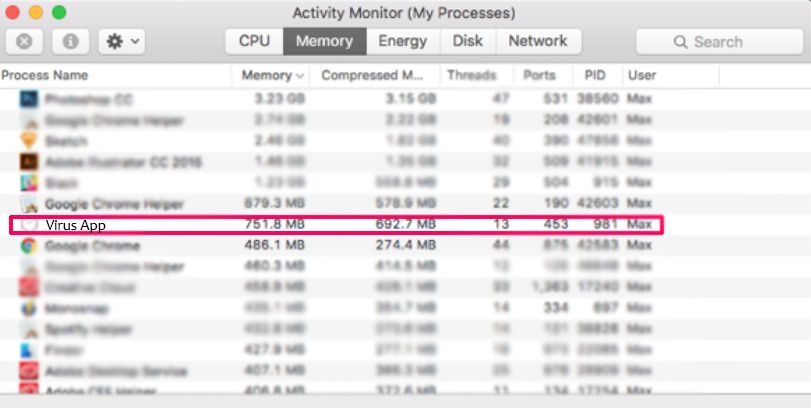
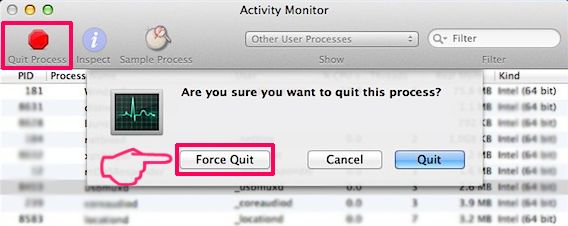
Your Mac will then show you a list of items that start automatically when you log in. Look for any suspicious apps identical or similar to Online Scam. Check the app you want to stop from running automatically and then select on the Minus (“-“) icon to hide it.
- Go to Finder.
- In the search bar type the name of the app that you want to remove.
- Above the search bar change the two drop down menus to “System Files” and “Are Included” so that you can see all of the files associated with the application you want to remove. Bear in mind that some of the files may not be related to the app so be very careful which files you delete.
- If all of the files are related, hold the ⌘+A buttons to select them and then drive them to “Trash”.
In case you cannot remove Online Scam via Step 1 above:
In case you cannot find the virus files and objects in your Applications or other places we have shown above, you can manually look for them in the Libraries of your Mac. But before doing this, please read the disclaimer below:
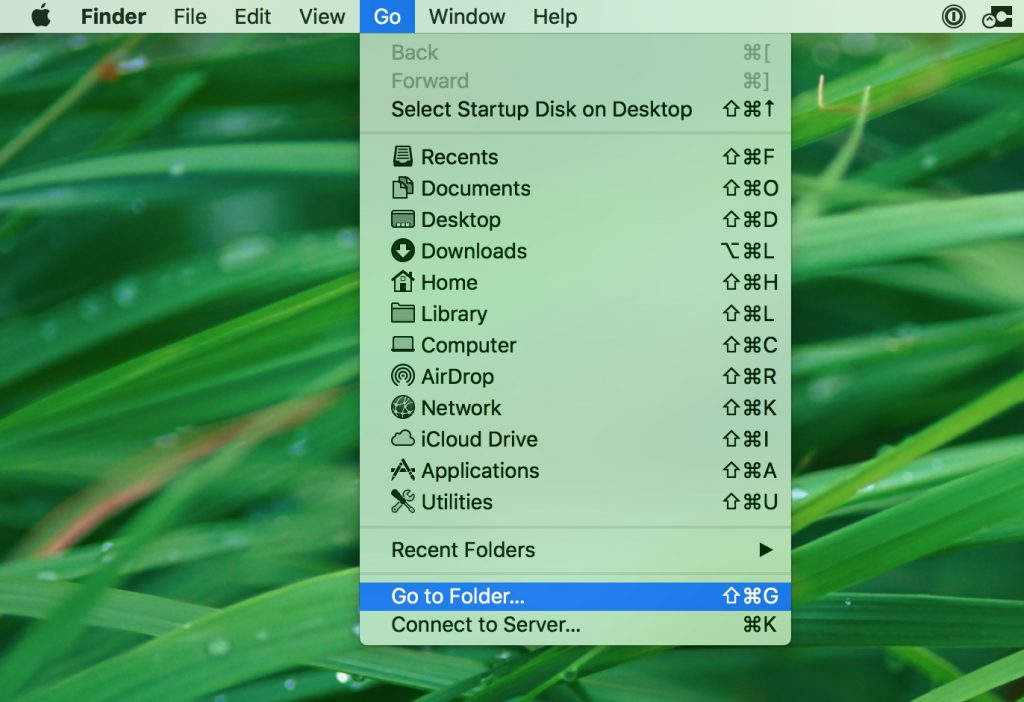
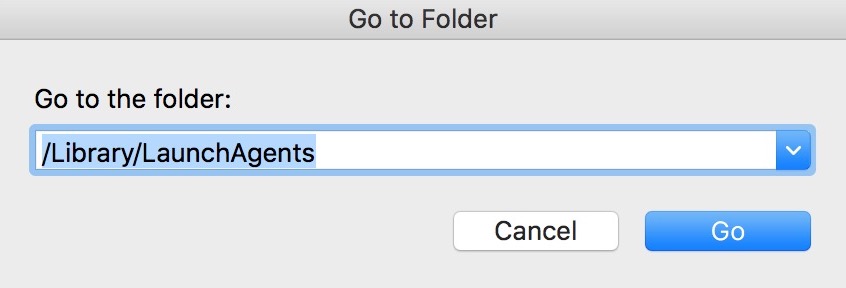
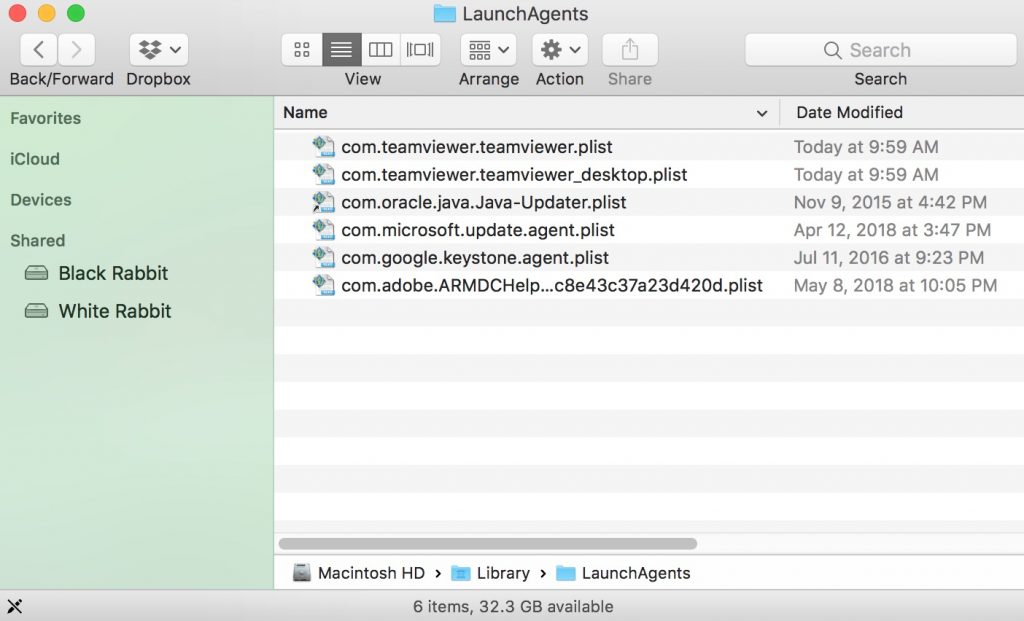
You can repeat the same procedure with the following other Library directories:
→ ~/Library/LaunchAgents
/Library/LaunchDaemons
Tip: ~ is there on purpose, because it leads to more LaunchAgents.
Step 2: Scan for and remove Online Scam files from your Mac
When you are facing problems on your Mac as a result of unwanted scripts and programs such as Online Scam, the recommended way of eliminating the threat is by using an anti-malware program. SpyHunter for Mac offers advanced security features along with other modules that will improve your Mac’s security and protect it in the future.
Video Removal Guide for Online Scam (Mac)
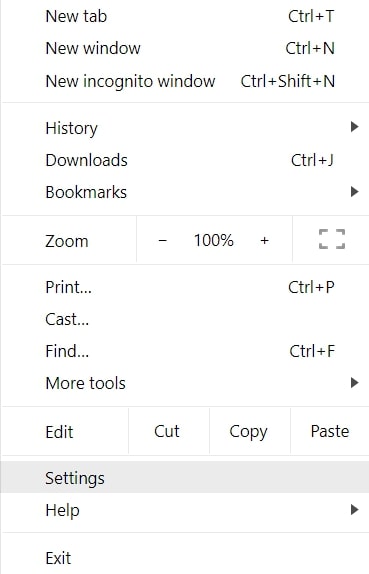
Remove Online Scam from Google Chrome.
Step 1: Start Google Chrome and open the drop menu
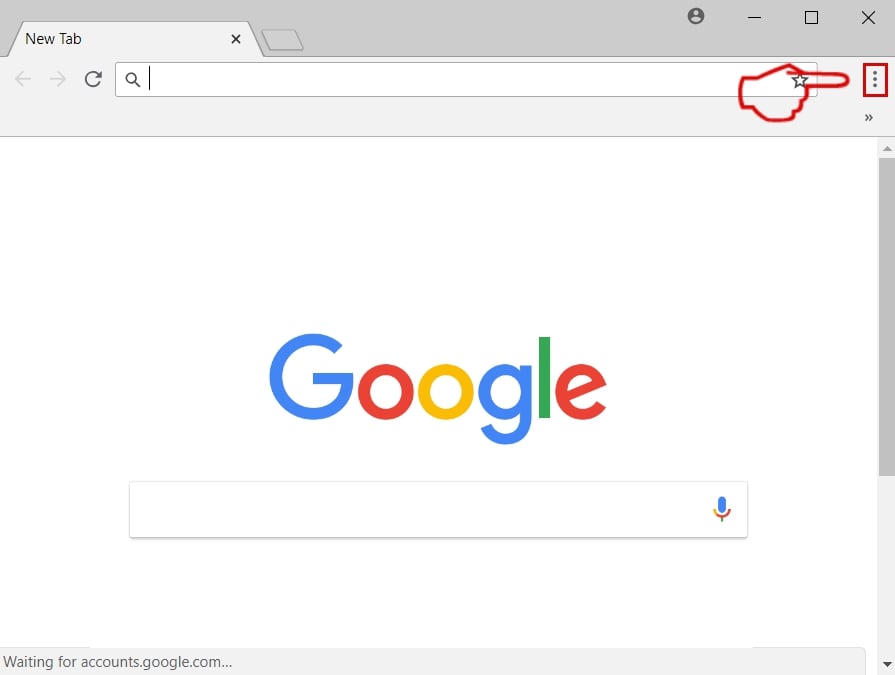
Step 2: Move the cursor over "Tools" and then from the extended menu choose "Extensions"
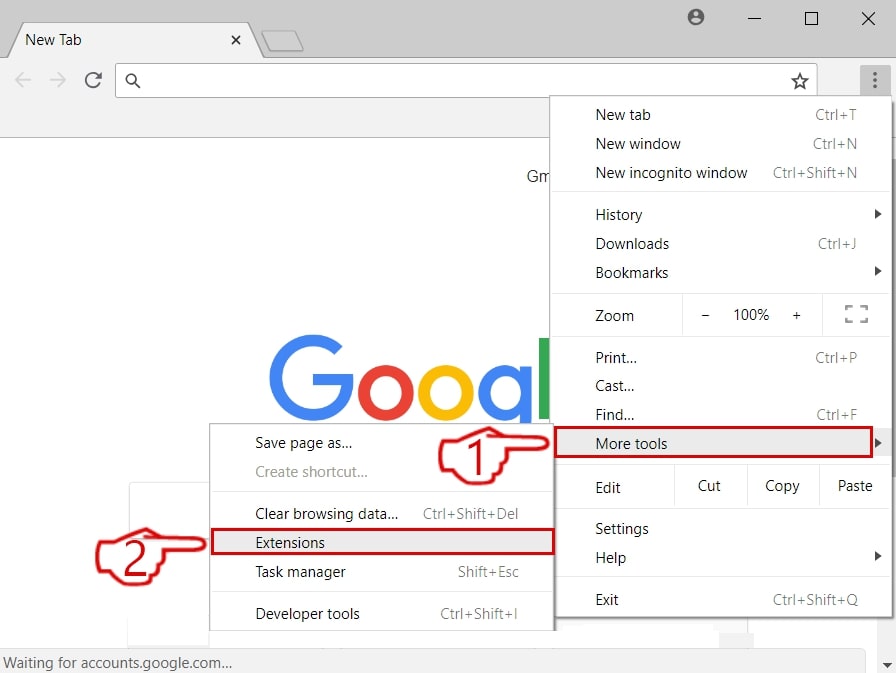
Step 3: From the opened "Extensions" menu locate the unwanted extension and click on its "Remove" button.
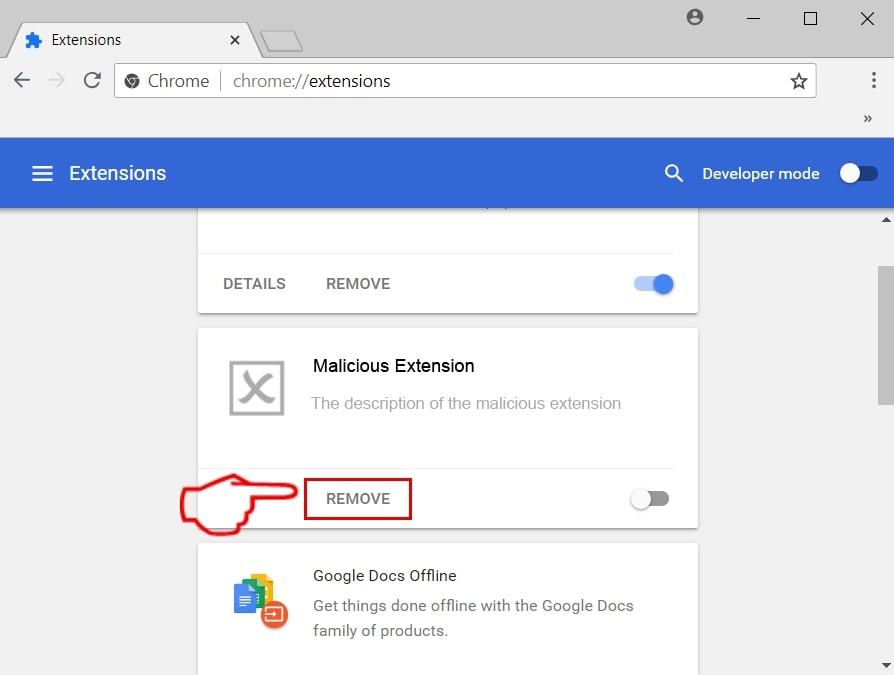
Step 4: After the extension is removed, restart Google Chrome by closing it from the red "X" button at the top right corner and start it again.
Erase Online Scam from Mozilla Firefox.
Step 1: Start Mozilla Firefox. Open the menu window:
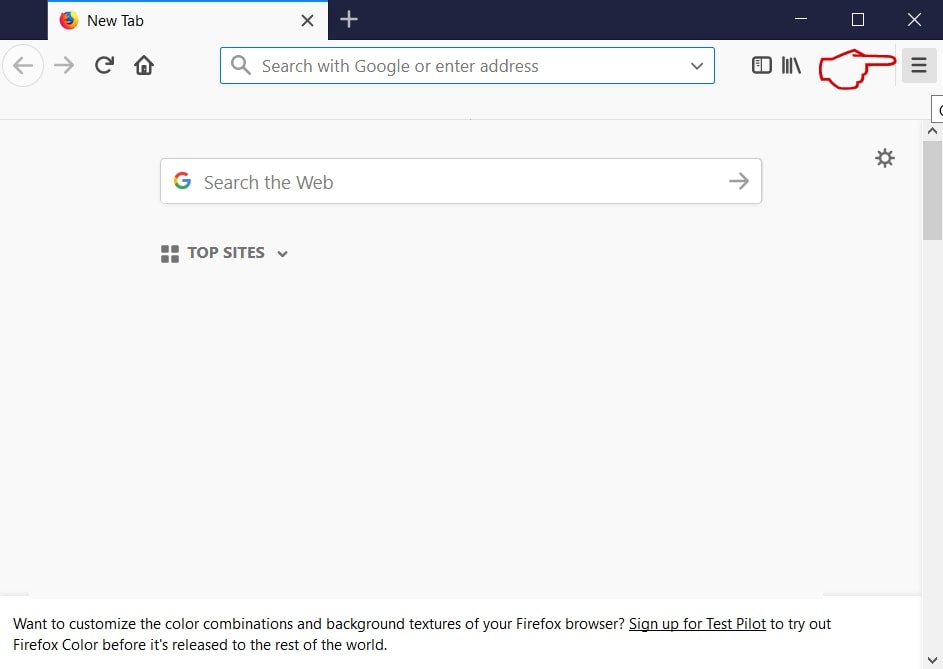
Step 2: Select the "Add-ons" icon from the menu.
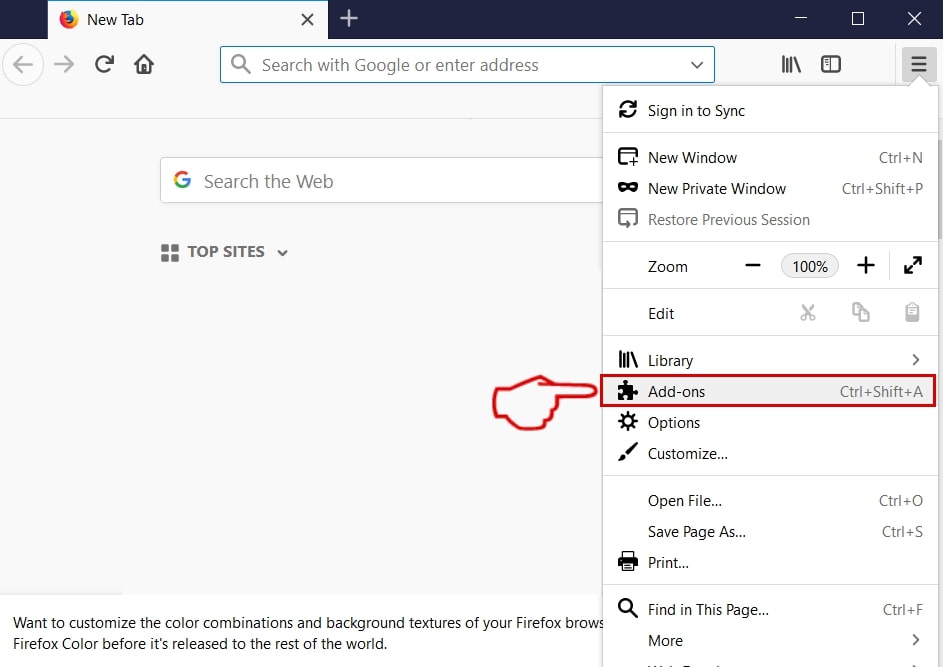
Step 3: Select the unwanted extension and click "Remove"

Step 4: After the extension is removed, restart Mozilla Firefox by closing it from the red "X" button at the top right corner and start it again.
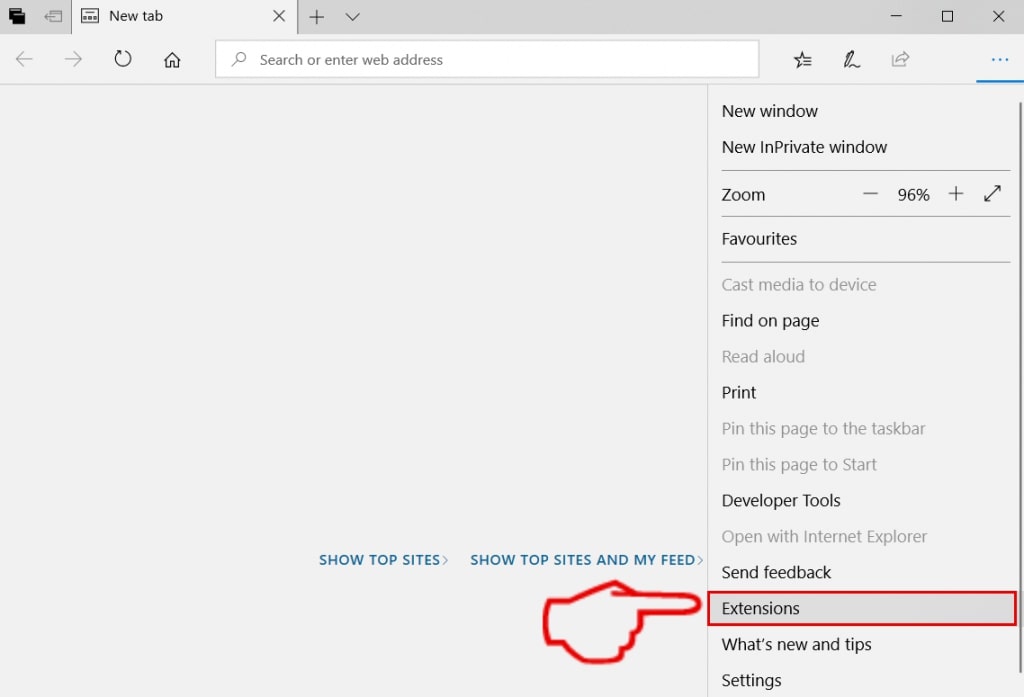
Uninstall Online Scam from Microsoft Edge.
Step 1: Start Edge browser.
Step 2: Open the drop menu by clicking on the icon at the top right corner.
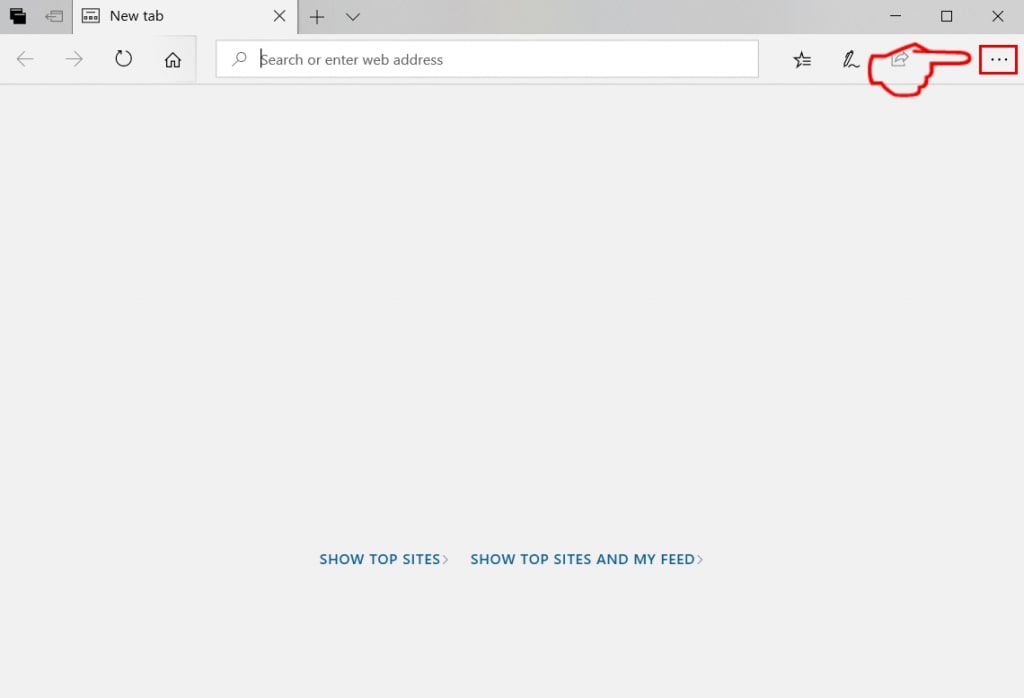
Step 3: From the drop menu select "Extensions".
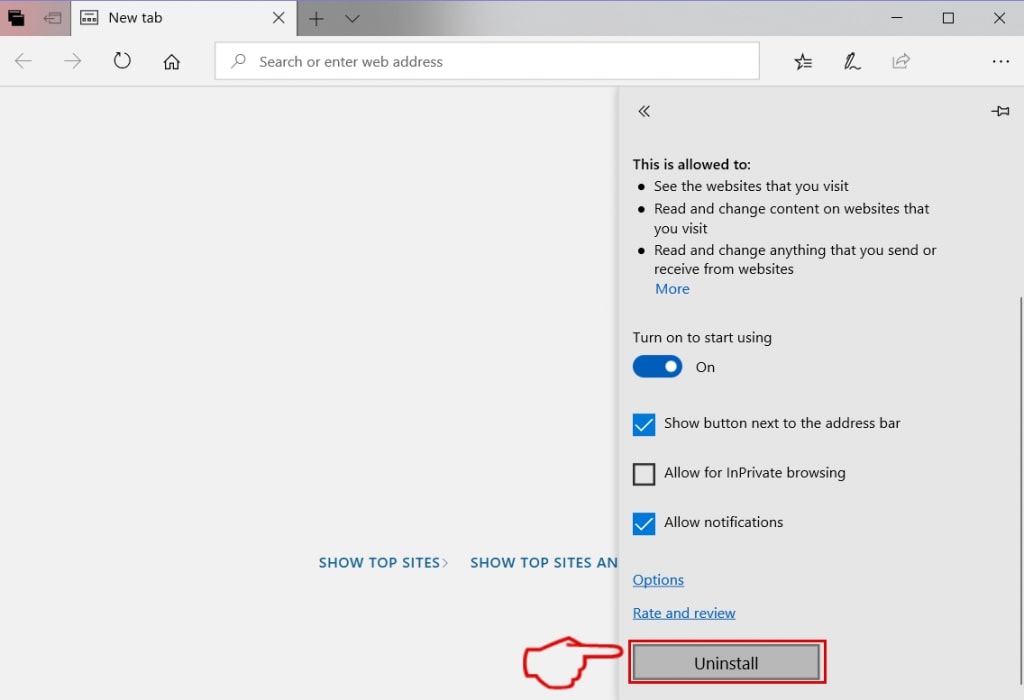
Step 4: Choose the suspected malicious extension you want to remove and then click on the gear icon.
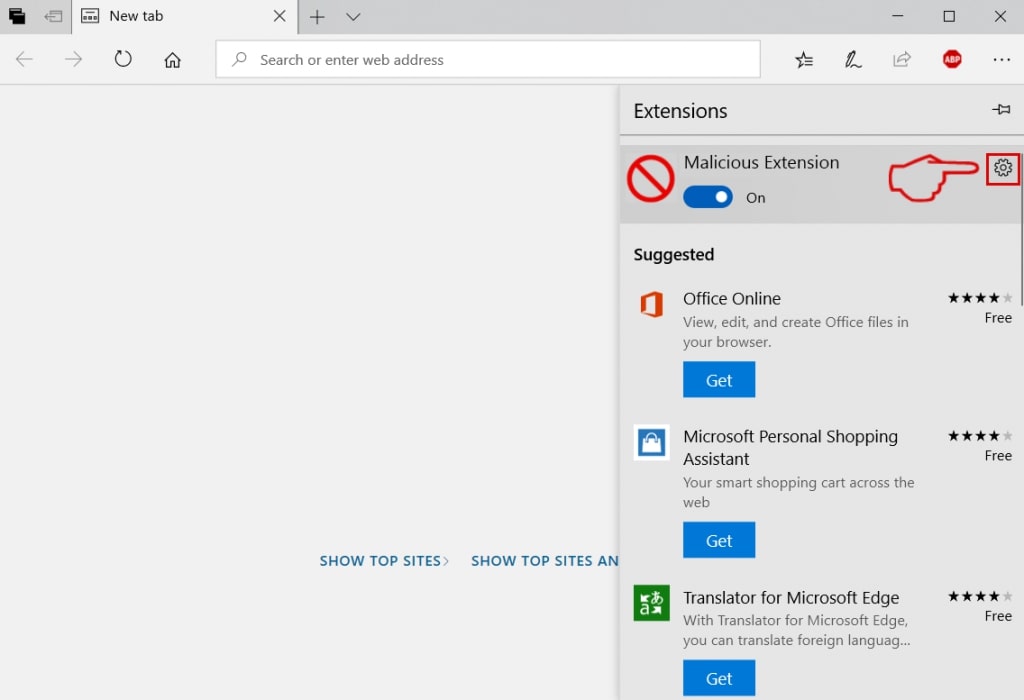
Step 5: Remove the malicious extension by scrolling down and then clicking on Uninstall.
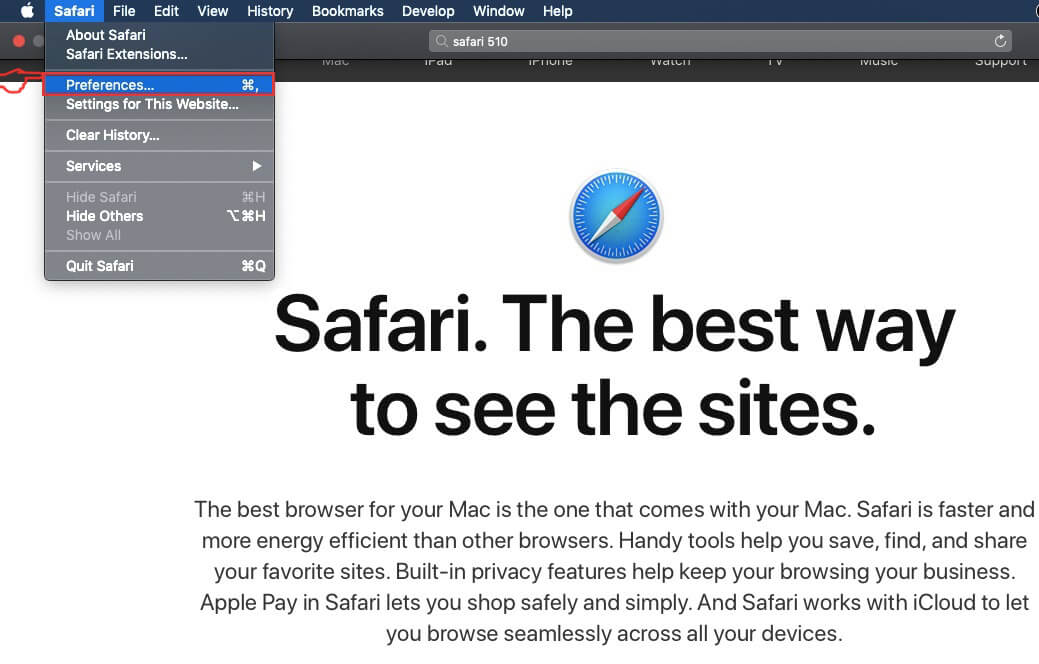
Remove Online Scam from Safari
Step 1: Start the Safari app.
Step 2: After hovering your mouse cursor to the top of the screen, click on the Safari text to open its drop down menu.
Step 3: From the menu, click on "Preferences".
Step 4: After that, select the 'Extensions' Tab.
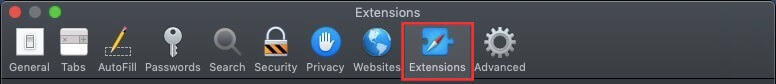
Step 5: Click once on the extension you want to remove.
Step 6: Click 'Uninstall'.
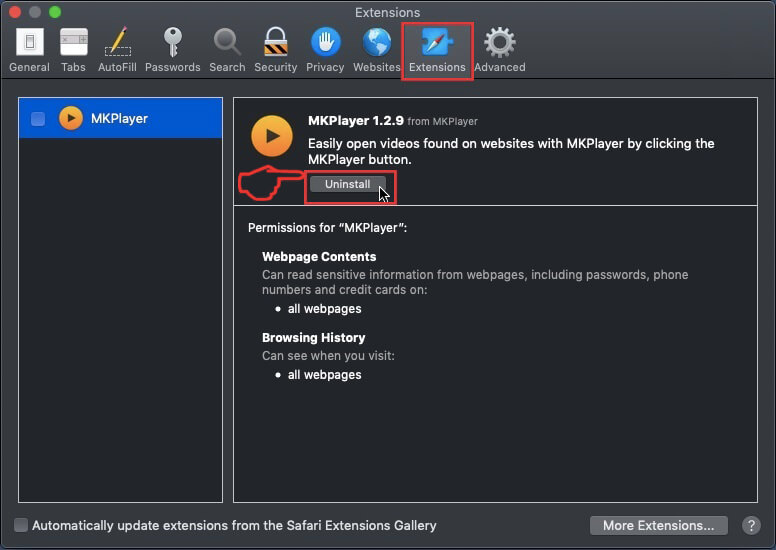
A pop-up window will appear asking for confirmation to uninstall the extension. Select 'Uninstall' again, and the Online Scam will be removed.
Eliminate Online Scam from Internet Explorer.
Step 1: Start Internet Explorer.
Step 2: Click on the gear icon labeled 'Tools' to open the drop menu and select 'Manage Add-ons'
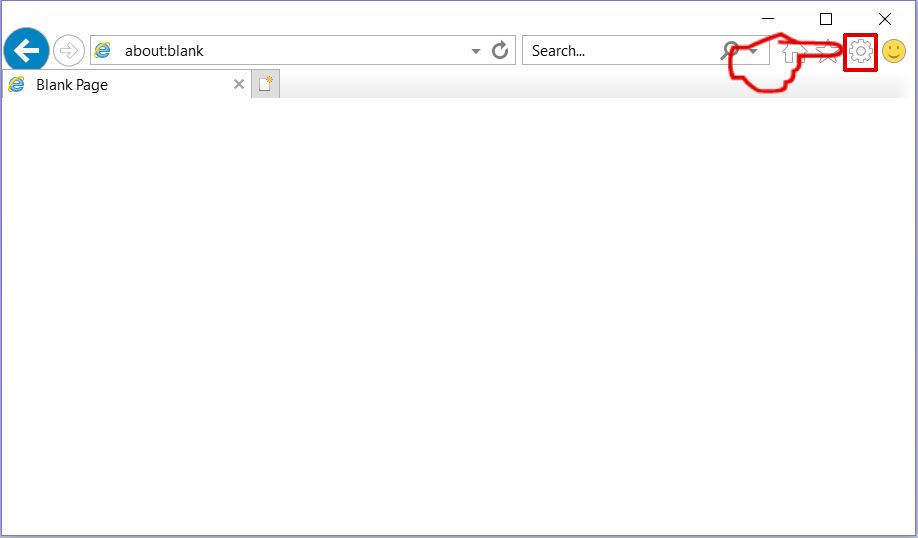
Step 3: In the 'Manage Add-ons' window.
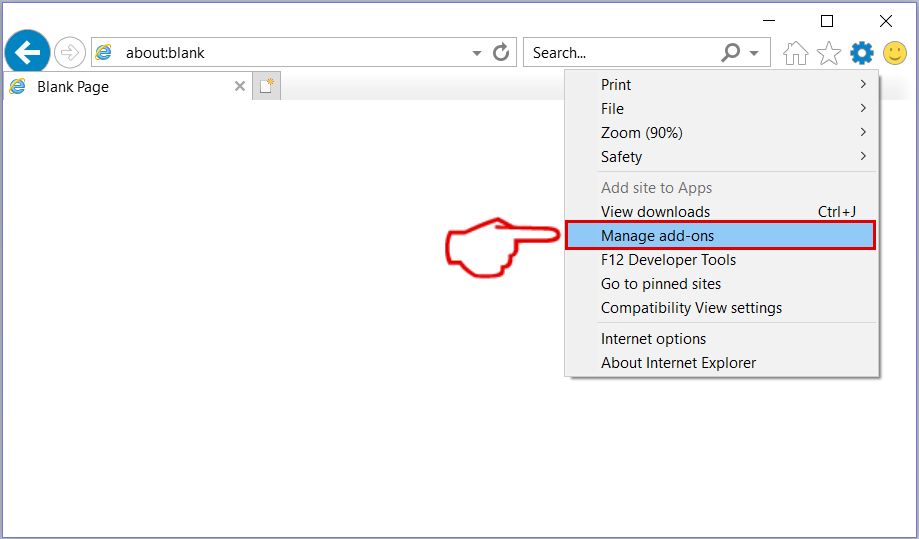
Step 4: Select the extension you want to remove and then click 'Disable'. A pop-up window will appear to inform you that you are about to disable the selected extension, and some more add-ons might be disabled as well. Leave all the boxes checked, and click 'Disable'.
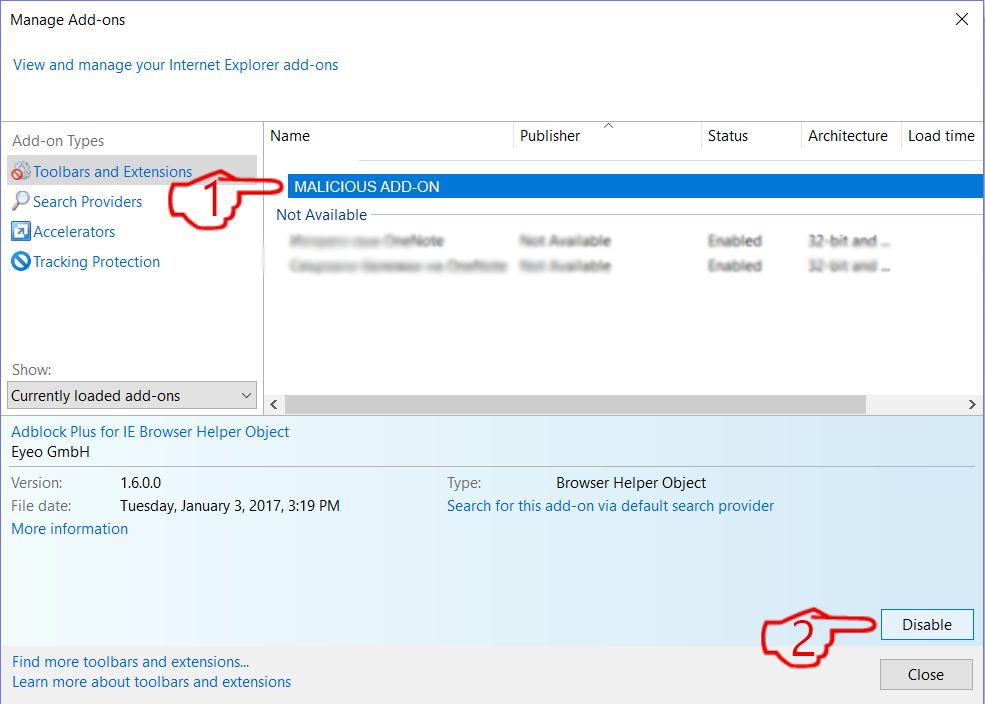
Step 5: After the unwanted extension has been removed, restart Internet Explorer by closing it from the red 'X' button located at the top right corner and start it again.
Remove Push Notifications from Your Browsers
Turn Off Push Notifications from Google Chrome
To disable any Push Notices from Google Chrome browser, please follow the steps below:
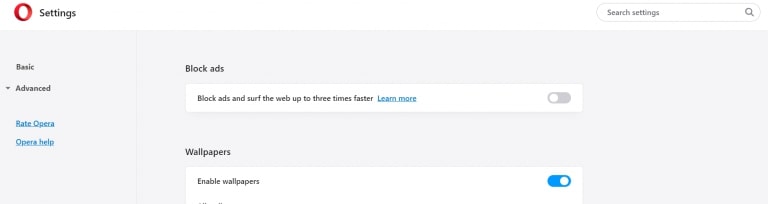
Step 1: Go to Settings in Chrome.
Step 2: In Settings, select “Advanced Settings”:
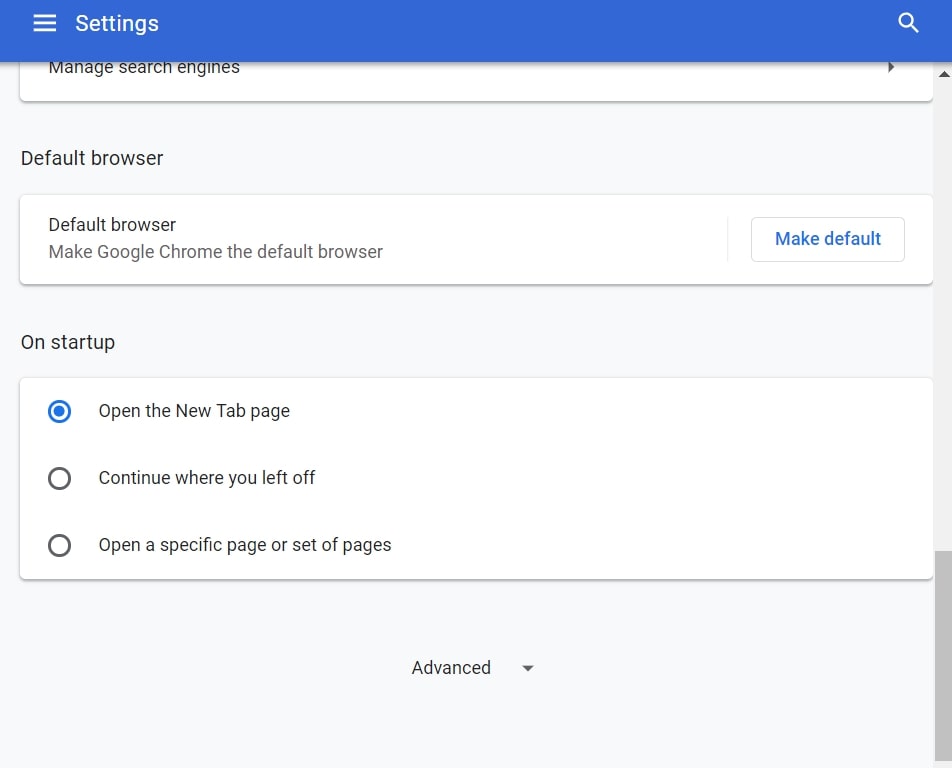
Step 3: Click “Content Settings”:
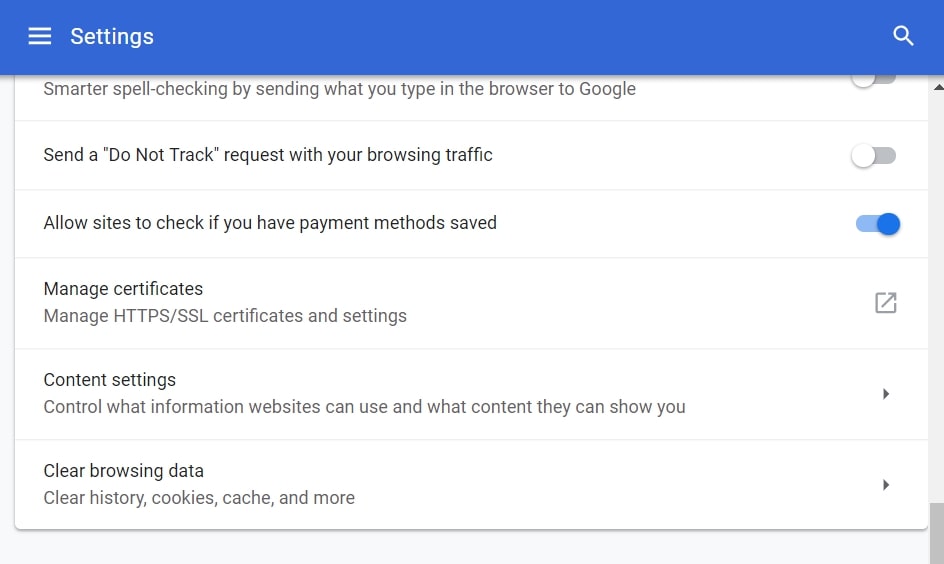
Step 4: Open “Notifications”:
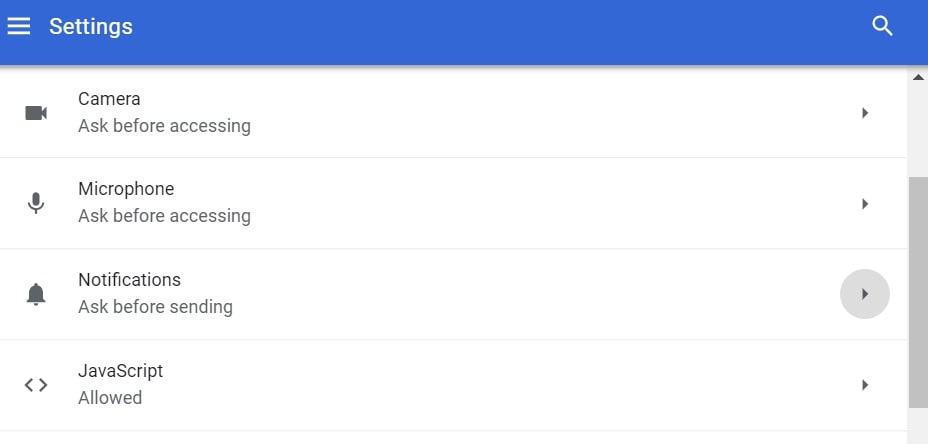
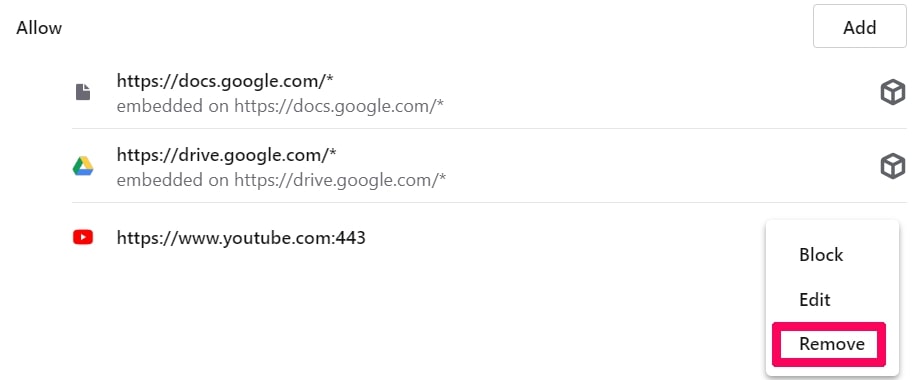
Step 5: Click the three dots and choose Block, Edit or Remove options:

Remove Push Notifications on Firefox
Step 1: Go to Firefox Options.
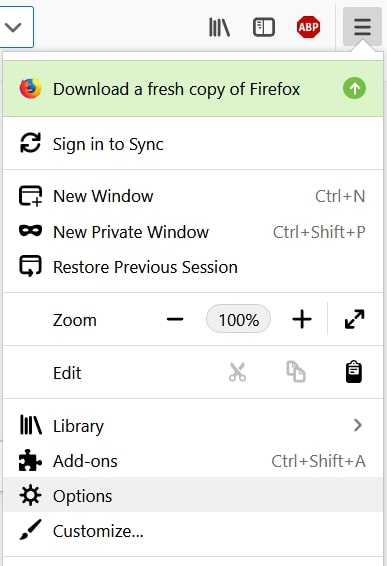
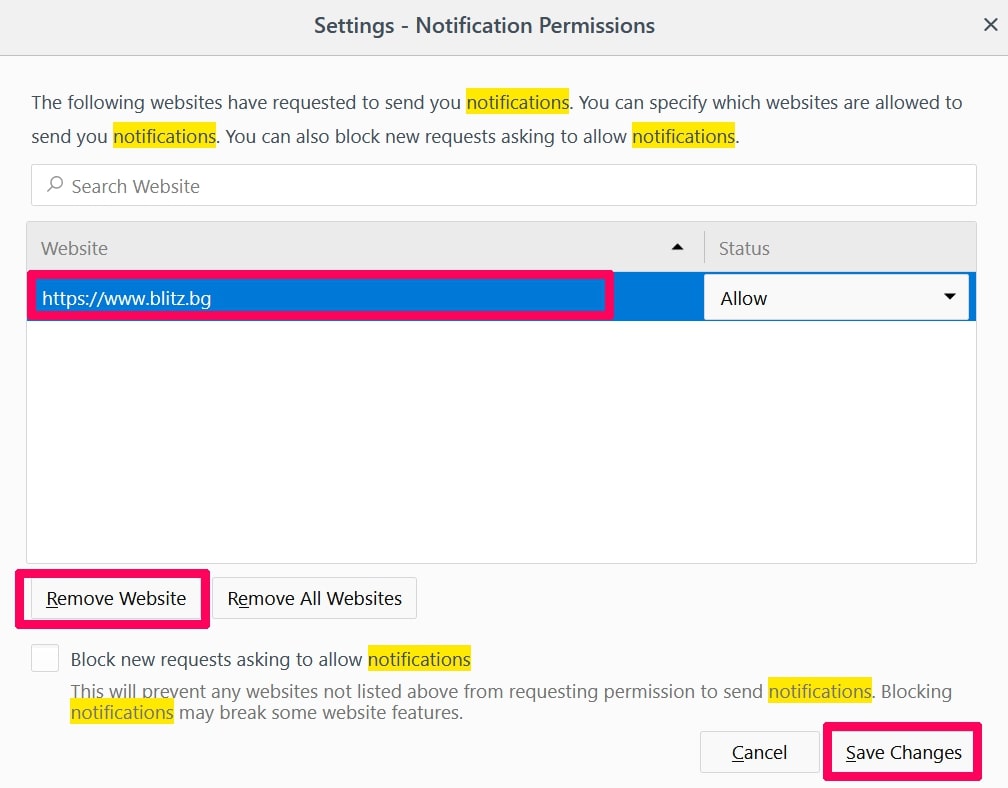
Step 2: Go to “Settings”, type “notifications” in the search bar and click "Settings":
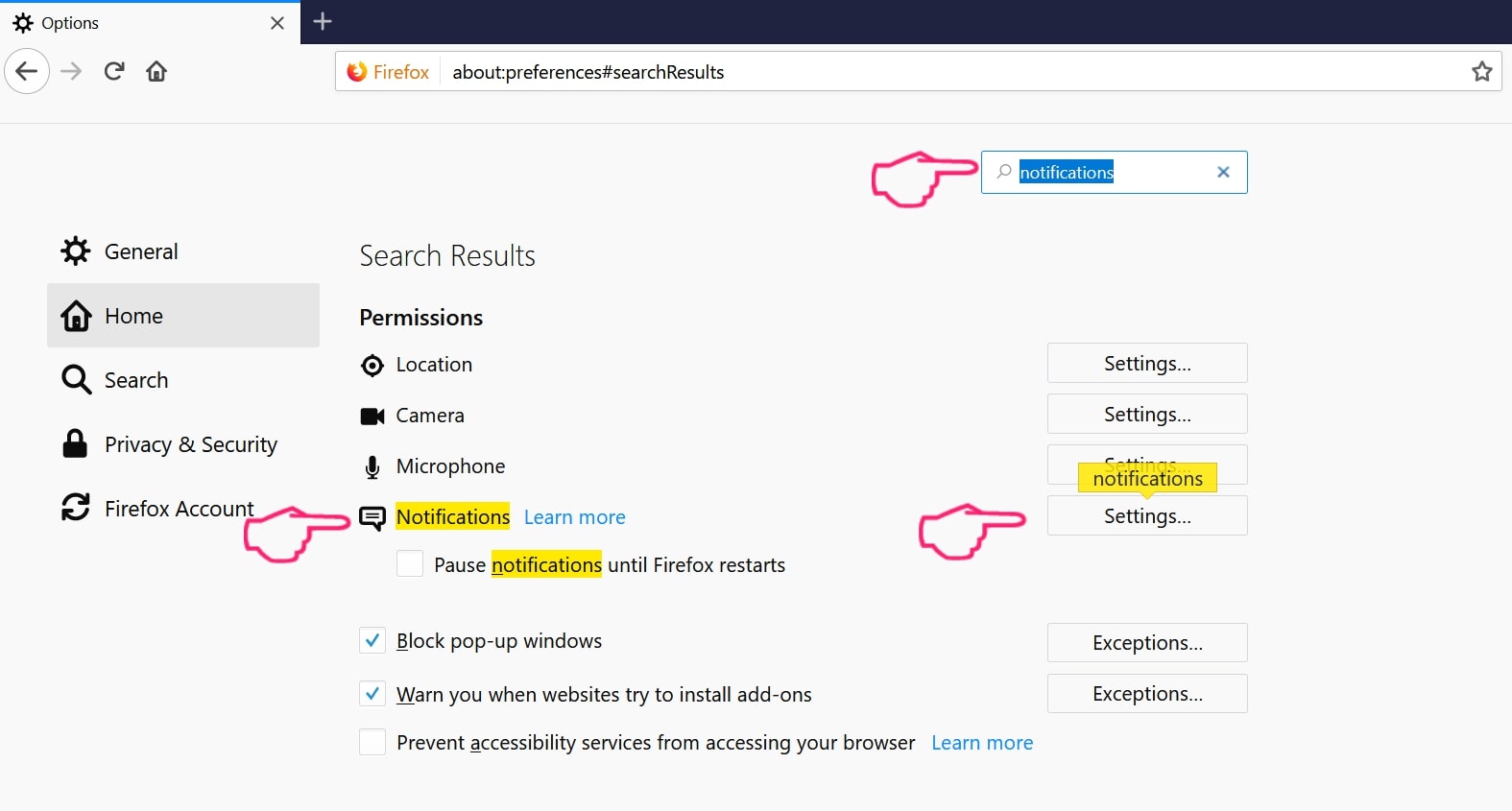
Step 3: Click “Remove” on any site you wish notifications gone and click “Save Changes”
Stop Push Notifications on Opera
Step 1: In Opera, press ALT+P to go to Settings.
Step 2: In Setting search, type “Content” to go to Content Settings.
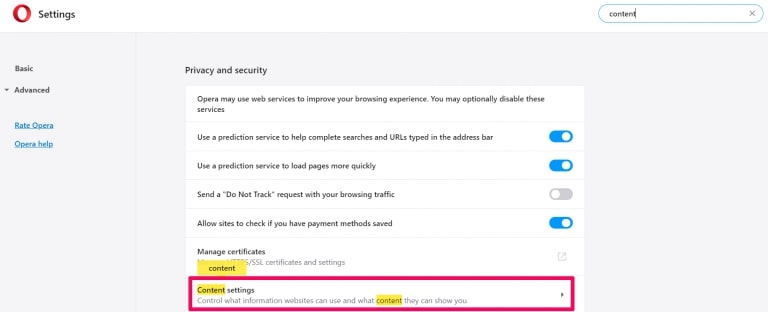
Step 3: Open Notifications:
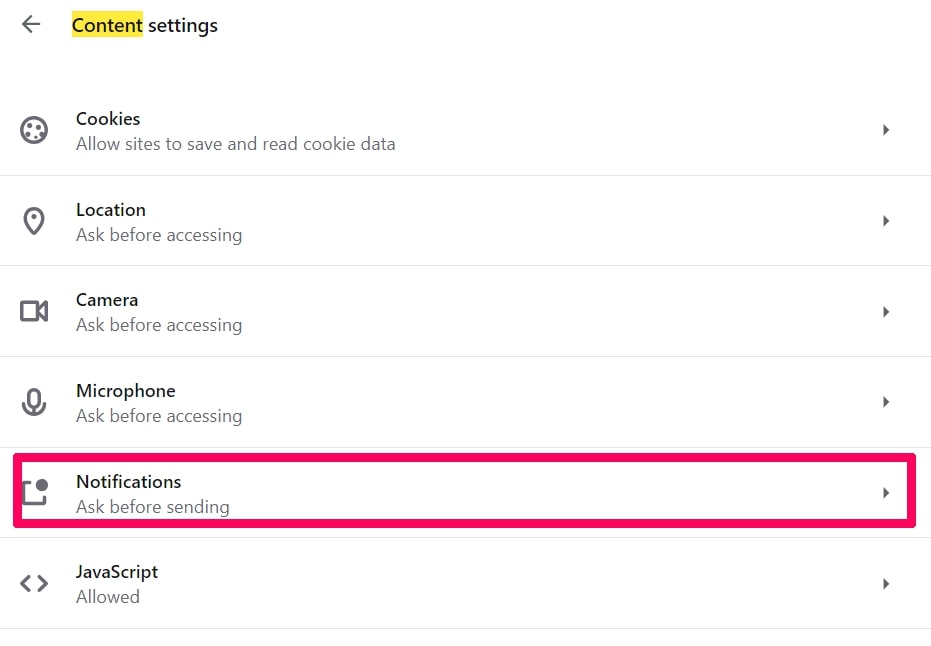
Step 4: Do the same as you did with Google Chrome (explained below):
Eliminate Push Notifications on Safari
Step 1: Open Safari Preferences.
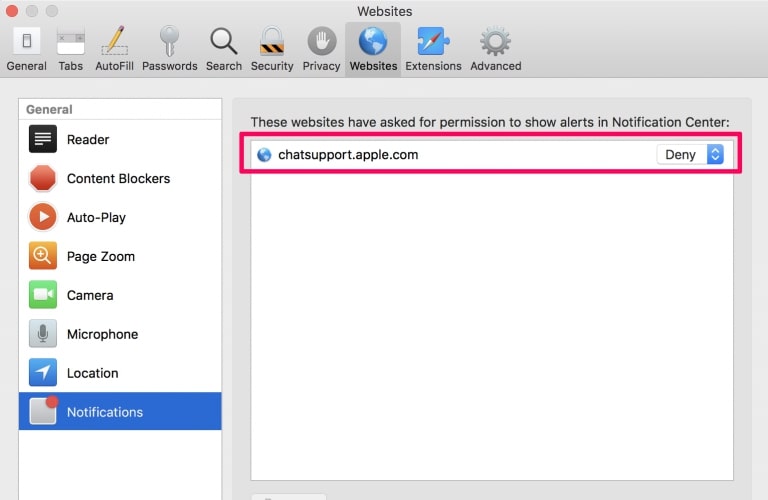
Step 2: Choose the domain from where you like push pop-ups gone and change to "Deny" from "Allow".
Online Scam-FAQ
What Is Online Scam?
The Online Scam threat is adware or browser redirect virus.
It may slow your computer down significantly and display advertisements. The main idea is for your information to likely get stolen or more ads to appear on your device.
The creators of such unwanted apps work with pay-per-click schemes to get your computer to visit risky or different types of websites that may generate them funds. This is why they do not even care what types of websites show up on the ads. This makes their unwanted software indirectly risky for your OS.
What Are the Symptoms of Online Scam?
There are several symptoms to look for when this particular threat and also unwanted apps in general are active:
Symptom #1: Your computer may become slow and have poor performance in general.
Symptom #2: You have toolbars, add-ons or extensions on your web browsers that you don't remember adding.
Symptom #3: You see all types of ads, like ad-supported search results, pop-ups and redirects to randomly appear.
Symptom #4: You see installed apps on your Mac running automatically and you do not remember installing them.
Symptom #5: You see suspicious processes running in your Task Manager.
If you see one or more of those symptoms, then security experts recommend that you check your computer for viruses.
What Types of Unwanted Programs Are There?
According to most malware researchers and cyber-security experts, the threats that can currently affect your device can be rogue antivirus software, adware, browser hijackers, clickers, fake optimizers and any forms of PUPs.
What to Do If I Have a "virus" like Online Scam?
With few simple actions. First and foremost, it is imperative that you follow these steps:
Step 1: Find a safe computer and connect it to another network, not the one that your Mac was infected in.
Step 2: Change all of your passwords, starting from your email passwords.
Step 3: Enable two-factor authentication for protection of your important accounts.
Step 4: Call your bank to change your credit card details (secret code, etc.) if you have saved your credit card for online shopping or have done online activities with your card.
Step 5: Make sure to call your ISP (Internet provider or carrier) and ask them to change your IP address.
Step 6: Change your Wi-Fi password.
Step 7: (Optional): Make sure to scan all of the devices connected to your network for viruses and repeat these steps for them if they are affected.
Step 8: Install anti-malware software with real-time protection on every device you have.
Step 9: Try not to download software from sites you know nothing about and stay away from low-reputation websites in general.
If you follow these recommendations, your network and all devices will become significantly more secure against any threats or information invasive software and be virus free and protected in the future too.
How Does Online Scam Work?
Once installed, Online Scam can collect data using trackers. This data is about your web browsing habits, such as the websites you visit and the search terms you use. It is then used to target you with ads or to sell your information to third parties.
Online Scam can also download other malicious software onto your computer, such as viruses and spyware, which can be used to steal your personal information and show risky ads, that may redirect to virus sites or scams.
Is Online Scam Malware?
The truth is that PUPs (adware, browser hijackers) are not viruses, but may be just as dangerous since they may show you and redirect you to malware websites and scam pages.
Many security experts classify potentially unwanted programs as malware. This is because of the unwanted effects that PUPs can cause, such as displaying intrusive ads and collecting user data without the user’s knowledge or consent.
About the Online Scam Research
The content we publish on SensorsTechForum.com, this Online Scam how-to removal guide included, is the outcome of extensive research, hard work and our team’s devotion to help you remove the specific, adware-related problem, and restore your browser and computer system.
How did we conduct the research on Online Scam?
Please note that our research is based on independent investigation. We are in contact with independent security researchers, thanks to which we receive daily updates on the latest malware, adware, and browser hijacker definitions.
Furthermore, the research behind the Online Scam threat is backed with VirusTotal.
To better understand this online threat, please refer to the following articles which provide knowledgeable details.




This information was very helpful thank you very much..