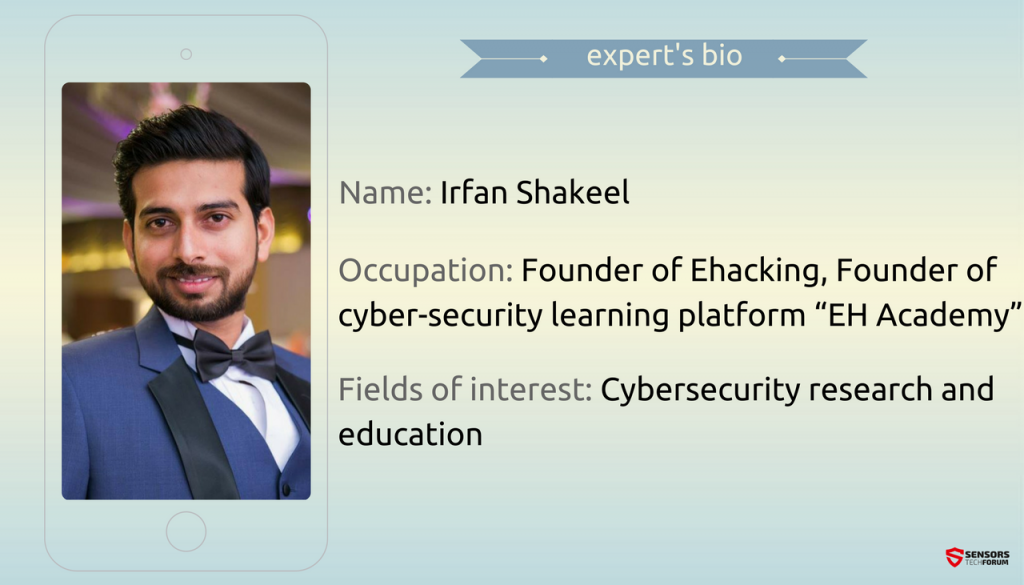
Irfan Shakeel is an engineer, penetration tester, a security researcher who has dedicated his career to securing information through quality education.
Irfan is the founder of ehacking.net and the EH Academy where people interested in programming, penetration testing, wireless and network security, web application and system security are welcome to enroll. His academy has helped thousands of students become experts in the field.
STF: Tell us about yourself. How did you become interested in cybersecurity?
Irfan: As an engineering student back in 2008, I used to read blogs about the IT industry. Cybersecurity has always been a fascinating and challenging industry; I was also inspired by the hacking attacks happening at that time.
Then an idea cаme up and I created a cyber-security blog, which turned into a full-time job, as a founder of ehacking, I have also started a cybersecurity learning platform called “EH Academy”. The aim of the ehacking project is “Securing Information through Quality Education”.
As of today, we are now operating this academy for thousands of students around the globe and helping them to become experts in the field to address the future’s threat landscape.
STF: What is the biggest challenge you have faced in your career so far?
Irfan: A cybersecurity professional’s life revolves around the edge of black hat and white hat. A single breach to the organization for which you are working can bring an end to your career. In my career, I have faced many such challenges where it’s critical to work while remaining at the good side to defend the organization. But, there are some cases in which I had to go anonymous to gather intelligence about the attacker so that we can develop strategies to prevent them in future.
This industry is full of challenges and you have to deal with them every day.
STF: What are your predictions for 2017 in terms of IoT-related attacks?
Irfan: As many organizations are launching IoT related products without surveying market needs, it will create a vast pool of unsecured IoT devices which will lead towards Distributed Denial of Service (DDoS) attacks on the Internet infrastructure. However, we should not connect all the devices to the Internet just because we can; it can and will be used against our network to breach our systems.
STF: What are the most important steps to be considered when securing services in the cloud?
Irfan: As far as cloud services provide opportunities to provision improved security services that are better than those many organizations implement on their own, it also introduces new security threats if not secured properly. In my opinion these steps are important when securing services in the cloud:
- Ensure effective governance, risk and compliance processes exist;
- Enforce privacy policies;
- Ensure proper protection of data and information;
- Manage security terms in the cloud service agreement;
- Evaluate security controls on physical infrastructure and facilities.
STF: While technology helps improve the quality of life it also makes it more vulnerable. How did we get to that contradiction?
Irfan: As far as technological evolution is concerned, every day thousands of new technologies come to exist to enhance our quality of life, but have many risks associated. Like, the most common example is how unnecessary network connectivity makes our critical data vulnerable. No device is well secured to prevent cyber criminals to breach into, however, we can reduce this factor of making technology more vulnerable by implementing high end security features in the technology prior to testing and connecting it to the Internet.
STF: What’s your opinion on the Vault 7 scandal?
Irfan: The Vault7 scandal is one of its own kind and such exposure of critical and confidential information is unbearable, whether it’s linked with any small organization, government or government security agencies. However, in most of such cases, there are high chances of the involvement of malicious insiders. Breaching into CIA and leaking such confidential information is near to impossible and can only be achieved by the help of unhappy or corrupt employees. So, securing and implementing security layers doesn’t guarantee the safety of our information, we should emphasize on insider threat as well.
STF: Organized cybercrime seems to be a perfectly oiled machine. Is there something cyber security experts could learn from it?
Irfan: Yes, as cybercriminals are rapidly evolving and enhancing their exploiting methods, cybersecurity professionals should look forward to track patterns in it and learn what they are seeking for.
Whether its financial gain, destroying reputation or hatred initiated crime, the attackers also make mistakes. We should learn from their methods and look forward to strengthen our security layers to prevent the previously used techniques and try to identify new techniques and targets by learning from their trends.
STF: Nowadays more and more home users are switching to Linux believing it is more secure than Windows. But security shouldn’t be underestimated, no matter what operating system you’re running. What are the essentials of Linux security that every user should implement?
Irfan: There is no doubt that many home users are switching to Linux due to its complex security that requires much hacking efforts to breach into it. But, there are some common mistakes that home users do, due to lack of knowledge and leave their system vulnerable to cyber attacks. Here are some essential tips for Linux security that every Linux user should implement:
- There should be no open ports;
- Enable password hashing;
- Enable automatic security update;
- Configure firewall to prevent cyber attacks and malicious files and communication;
- Enable Syn-cookies to mitigate a SYN-flood attack;
- Enable kernel live-patch service to mitigate major kernel security issues without requiring a reboot;
- Use Encrypted LVM file system encryption
SensorsTechForum’s “Ask the Experts” Interview Series
If you are a cybersecurity expert and you want to share your experience with our audience, send us an email at support[at]sensorstechforum.com. We will gladly converse with you about anything on the subject!
Aditya Gupta, IoT Security Expert
Dr. Mansur Hasib, Healthcare Expert
Scott Schober, Speaker and Book Author
Dr. Roman Yampolskiy, AI Expert
Raef Meeuwisse, Infosec Expert
Dr. Vesselin Bontchev, Scientist