Cybersecurity researchers have outlined a new type of attack involving Intel server-grade processors since 2012. The attack is based on a vulnerability named NetCAT (Network Cache Attack).
The vulnerability could allow sniffing data by mounting a side-channel attack over the network. The discovery of the NetCAT attack comes from researchers from the VUSec group at Vrije Universiteit Amsterdam.
“NetCAT shows that network-based cache side-channel attacks are a realistic threat,” the researchers explain. Cache attacks are not uncommon and they have been used to leak sensitive data on a local setting. NetCAT only shows how this threat extends to untrusted clients over the network. If exploited, NetCAT can leak sensitive information such as keystrokes in a SSH session from remote servers with no local access, the report says.
What is the cause of NetCAT?
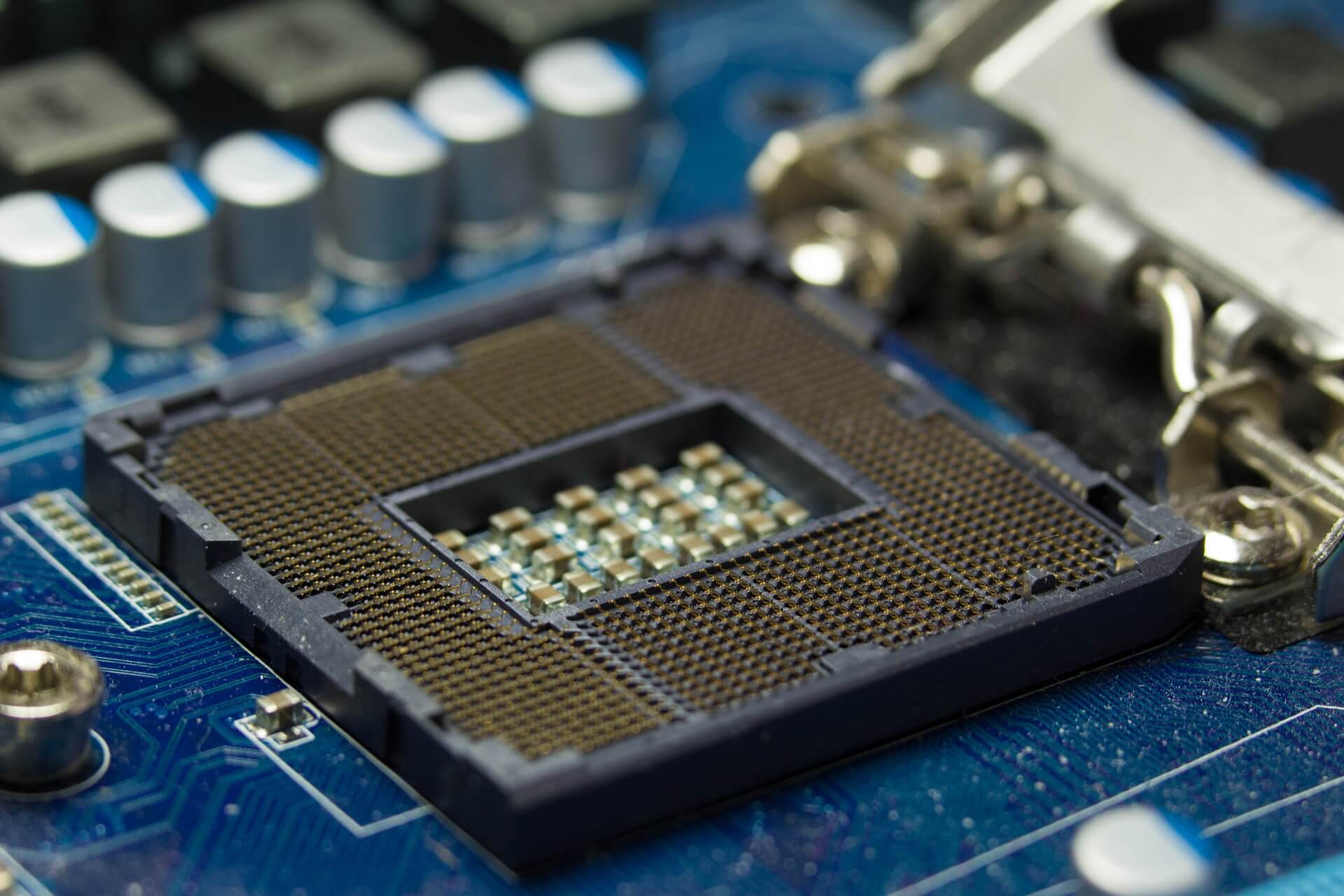
The vulnerability stems from a recent Intel feature called DDIO, which grants network devices and other peripherals access to the CPU cache. Designed with the idea to be a performance optimization in fast networks, DDIO has severe security implications, note the researchers. These issues expose servers in local untrusted networks to remote side-channel attacks.
Through their work, the researchers show how NetCAT can break the confidentiality of a SSH session from a third machine. Most importantly, no malicious software running on the remote server is needed, as the attacker is doing this by sending network packets to the remote server.
More about the attack:
With NetCAT, we can leak the arrival time of the individual network packets from a SSH session using a remote cache side channel. Why is this useful? In an interactive SSH session, every time you press a key, network packets are being directly transmitted. As a result, every time a victim you type a character inside an encrypted SSH session on your console, NetCAT can leak the timing of the event by leaking the arrival time of the corresponding network packet. Now, humans have distinct typing patterns. For example, typing ‘s’ right after ‘a’ is faster than typing ‘g’ after ‘s’. As a result, NetCAT can operate statical analysis of the inter-arrival timings of packets in what is known as a keystroke timing attack to leak what you type in your private SSH session.
It should be noted that in November 2018, two side-channel attacks were uncovered by security researchers -the so-called Portsmash side-channel vulnerability, and a GPU exploit. Portsmash is similar to previous cases like Meltdown.
By exploiting this bug hackers could hijack information from processes that are running in the same core. The demonstrated proof-of-concept code showed how it is possible to steal the private key during an OpenSSL session. The performed tests showcased that Intel Skylake and Kaby Lake are impacted by this.
As for the exploits regarding GPU cards, they could target individual end-users that use them in day-to-day activities as well as clusters that rely on GPUs for distributed computing.