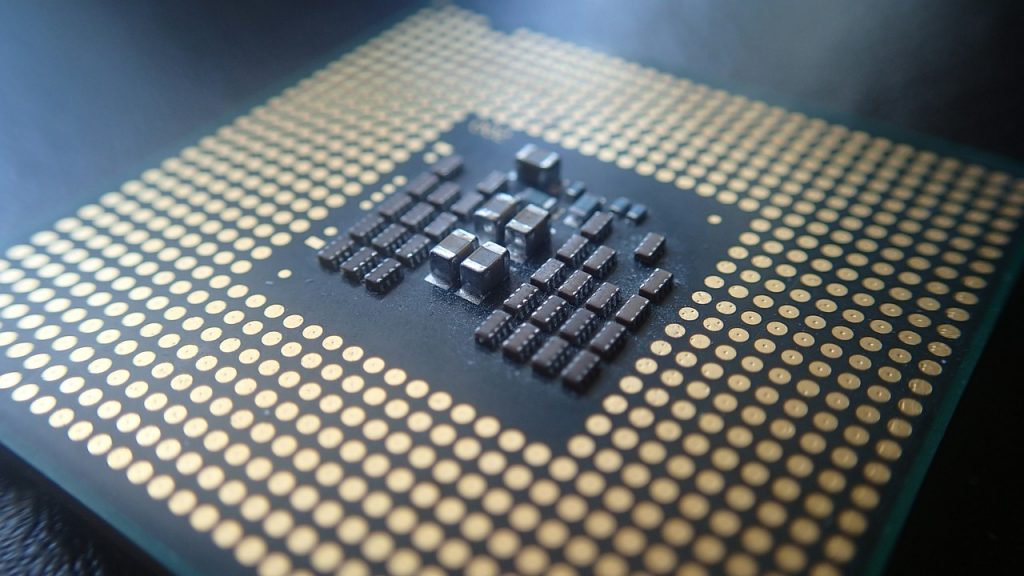
Another serious issue has been found targeting modern CPUs — the Portsmash Side-channel Vulnerability which is similar to previous cases like Meltdown. By exploiting this bug hackers can hijack information from processes that are running in the same core.
CVE-2018-5407: Portsmash Side-channel Vulnerability Is the Latest Example of a CPU Bug
A team of security experts discovered and presented a new bug that specifically targets modern hyper-threading processors. This is the latest example of a side-channel vulnerability — a critical bug in the way information is handled by the processor. These type of attacks essentially display a fundamental flaw in the way the systems are designed, a recent example is the [wplinkpreview url=”https://sensorstechforum.com/tlbleed-vulnerability-affects-intel-processors/”]TLBleed exploit. As a consequence of exploit malicious operators can steal information of running processes in the same core.
The demonstrated proof-of-concept code shows how it is possible to steal the private key during an OpenSSL session. The issue is also tracked in the CVE-2018-5407 advisory which gives further details about the problem. The tests showcase that the verified models are Intel Skylake and Kaby Lake however every model implementation using this execution approach is affected.
A very dangerous circumstance is the fact that such side-channel vulnerabilities can easily be exploited via malicious code. The only requirement to access the information is to have a running process on the same core. This is extremely simple to do as most modern languages allow the applications to run on all cores for performance reasons. This consequently means that if not patched this bug can be used to hijack any data, including the aforementioned encryption keys.
The security analysts also note that this problem is related to another vulnerability tracked in the CVE-2005-0109 which reads the following:
Hyper-Threading technology, as used in FreeBSD and other operating systems that are run on Intel Pentium and other processors, allows local users to use a malicious thread to create covert channels, monitor the execution of other threads, and obtain sensitive information such as cryptographic keys, via a timing attack on memory cache misses.
The disclosure timeline of events pertaining to the Portsmash Side-channel Vulnerability is the following:
- 01 Oct 2018: Notified Intel Security
- 26 Oct 2018: Notified openssl-security
- 26 Oct 2018: Notified CERT-FI
- 26 Oct 2018: Notified oss-security distros list
- 01 Nov 2018: Embargo expired
A patch has still not been released by the vendors. We expect to see them released to the motherboards vendors from where on the users will receive the necessary notifications. For more information read the security announcement.


