A new variant of the nefarious TeslaCrypt ransomware is circling the Web. This time, the malicious threat is encrypting files in a .vvv file format. Once it affects your system, it will create thousands of files inside multiple folders, along with “how_recover+abc” files to which a ransom note is attached.
| Name | TeslaCrypt |
| Type | Ransomware, Ransomware Trojan |
| Short Description | Encrypts the user’s files. No decryption key is stored on the computer. |
| Symptoms | Encrypts files with a .vvv extension, creates decrypt.exe, decrypt.html, and decrypt.txt files in almost every folder. Drops a new ransom note in how_recover+abc.html and how_recover+abc.txt files. |
| Distribution Method | Email Attachments, Spam Emails, Suspicious Sites |
| Detection Tool | Download Malware Removal Tool, to See If Your System Has Been Affected by malware |
| User Experience | Join our forum to discuss the TeslaCrypt Ransomware. |
TeslaCrypt Ransomware – How Did I Get It?
We have already seen other members of this ransomware family around the Web. Learn more about TeslaCrypt and AlphaCrypt.
Ransomware such as TeslaCrypt could enter your system in a number of ways.
The most common distribution method known is through malicious email attachments and spam emails. There are even cases, where the email body itself contains a malicious code and upon opening the email, the user infects his computer with it, even if he doesn’t open the attachment inside.
Social networks and file sharing services may also contain the TeslaCrypt ransomware, disguised as a regular file. Keep in mind that TeslaCrypt may hide in dubious websites as well. Once you visit such a website, you risk infecting your system with TeslaCrypt without you even knowing it.
TeslaCrypt Ransomware – Description
Once executed, the latest TeslaCrypt ransomware will search for files with more than 150 extensions, and more specifically the following ones:
→.sql, .mp4, .7z, .rar, .m4a, .wma, .avi, .wmv, .csv, .d3dbsp, .zip, .sie, .sum, .ibank, .t13, .t12, .qdf, .gdb, .tax, .pkpass, .bc6, .bc7, .bkp, .qic, .bkf, .sidn, .sidd, .mddata, .itl, .itdb, .icxs, .hvpl, .hplg, .hkdb, .mdbackup, .syncdb, .gho, .cas, .svg, .map, .wmo, .itm, .sb, .fos, .mov, .vdf, .ztmp, .sis, .sid, .ncf, .menu, .layout, .dmp, .blob, .esm, .vcf, .vtf, .dazip, .fpk, .mlx, .kf, .iwd, .vpk, .tor, .psk, .rim, .w3x, .fsh, .ntl, .arch00, .lvl, .snx, .cfr, .ff, .vpp_pc, .lrf, .m2, .mcmeta, .vfs0, .mpqge, .kdb, .db0, .dba, .rofl, .hkx, .bar, .upk, .das, .iwi, .litemod, .asset, .forge, .ltx, .bsa, .apk, .re4, .sav, .lbf, .slm, .bik, .epk, .rgss3a, .pak, .big, wallet, .wotreplay, .xxx, .desc, .py, .m3u, .flv, .js, .css, .rb, .png, .jpeg, .txt, .p7c, .p7b, .p12, .pfx, .pem, .crt, .cer, .der, .x3f, .srw, .pef, .ptx, .r3d, .rw2, .rwl, .raw, .raf, .orf, .nrw, .mrwref, .mef, .erf, .kdc, .dcr, .cr2, .crw, .bay, .sr2, .srf, .arw, .3fr, .dng, .jpe, .jpg, .cdr, .indd, .ai, .eps, .pdf, .pdd, .psd, .dbf, .mdf, .wb2, .rtf, .wpd, .dxg, .xf, .dwg, .pst, .accdb, .mdb, .pptm, .pptx, .ppt, .xlk, .xlsb, .xlsm, .xlsx, .xls, .wps, .docm, .docx, .doc, .odb, .odc, .odm, .odp, .ods, .odt
After TeslaCrypt threat finds files with these extensions, it will encrypt them with the extension “.vvv”. This variant does not use data files like the previous one, nor does it store information about the decryption key on the compromised computer.
So, decryption is possible, by using a Network Sniffer to get the encryption key, while files are encrypted on your system. A Network Sniffer is a program and/or device monitoring data traveling over a network, such as its internet traffic and internet packets. If you have a sniffer set before the attack happened you might get information about the decryption key. Another way to get your files back is to restore them if you have backups on an external storage device. Other potential ways for decryption are included in the instructions at the end of the article.
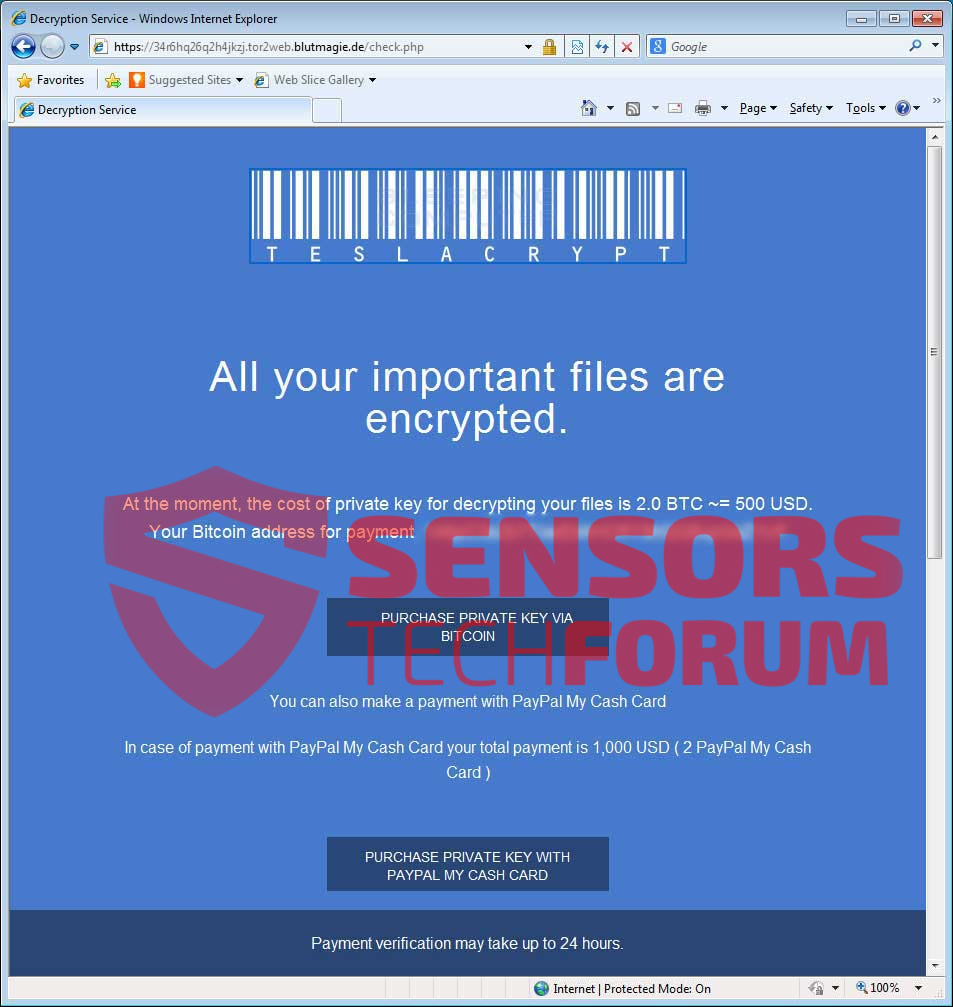
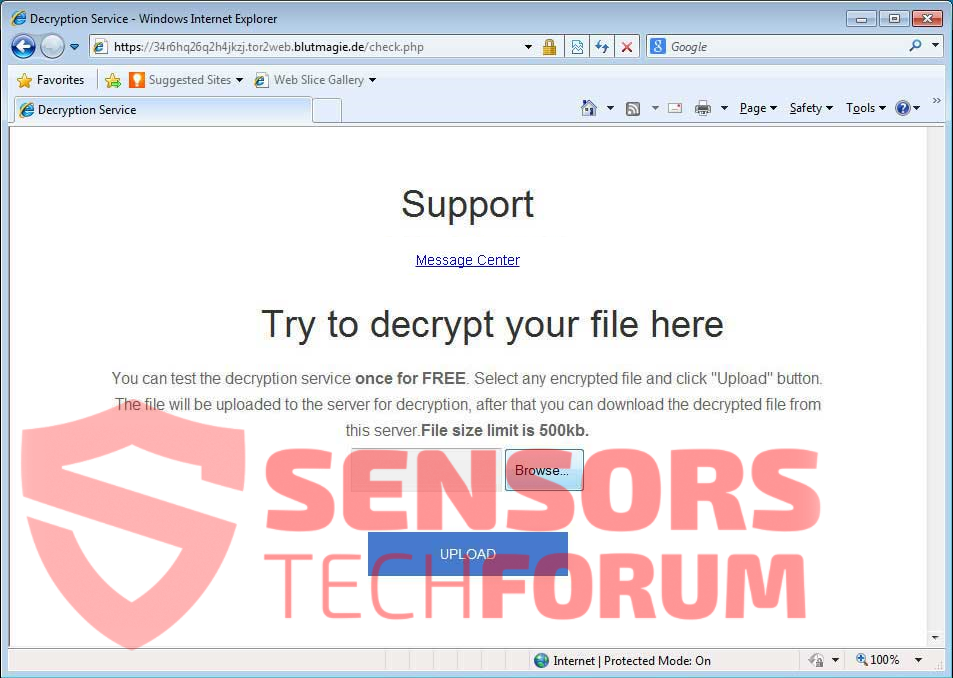
In the ransom note it is described how you can pay the ransom with different currencies like, BitCoins, Ukash, and PayPal My Cash Cards. At the end of the note, there is an upload form, where you can test if the decryption will work:
We advise you not to pay the ransom, as there is no guarantee you will get a decryption key, let alone a working one. The ransomware can create thousands of files with the names: decrypt.exe, decrypt.html, and decrypt.txt, along with the ransom note files, how_recover+abc.txt and how_recover+abc.html.
Remove TeslaCrypt Ransomware Completely
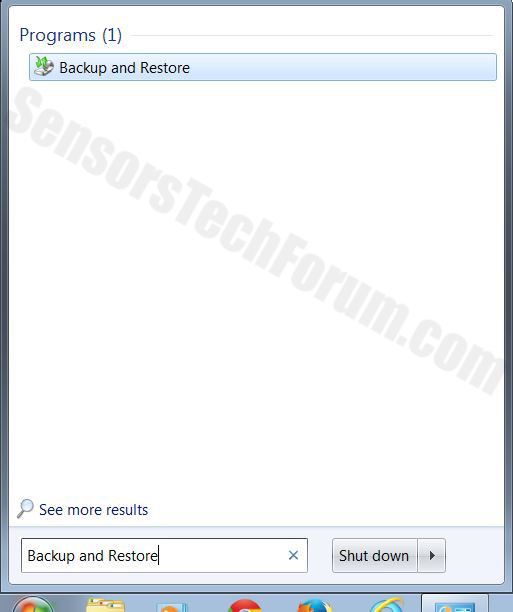
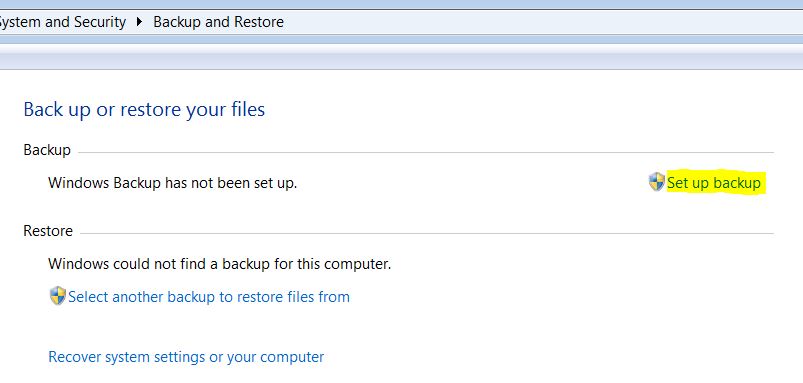
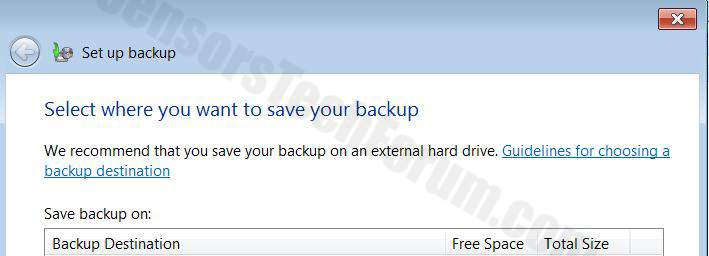
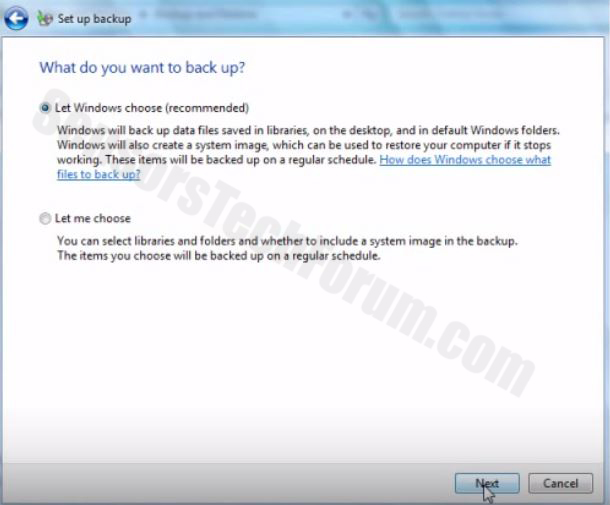
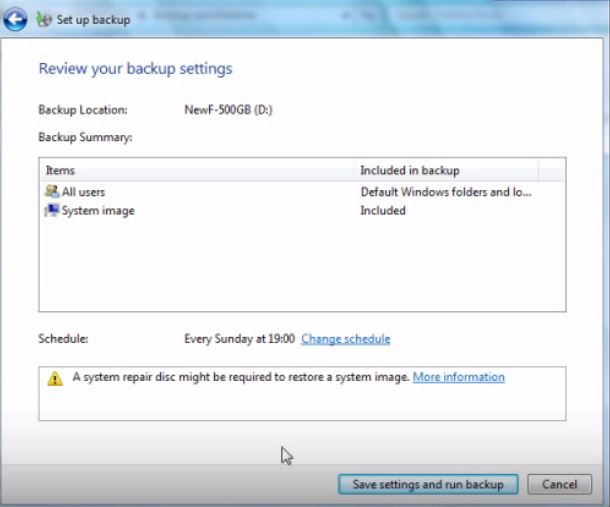
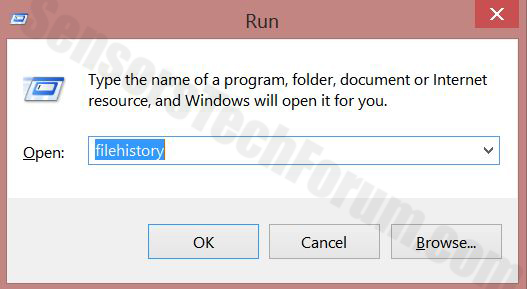
To completely remove TeslaCrypt from your computer, you should have basic knowledge in removing viruses. We highly recommend you to back up your system files first. Afterwards, carefully follow the instructions provided here:
- Step 1
- Step 2
- Step 3
- Step 4
- Step 5
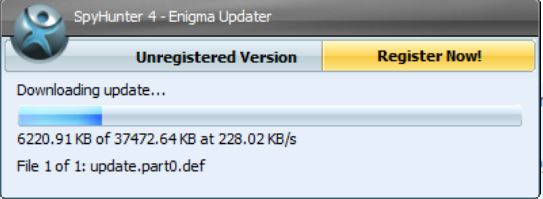
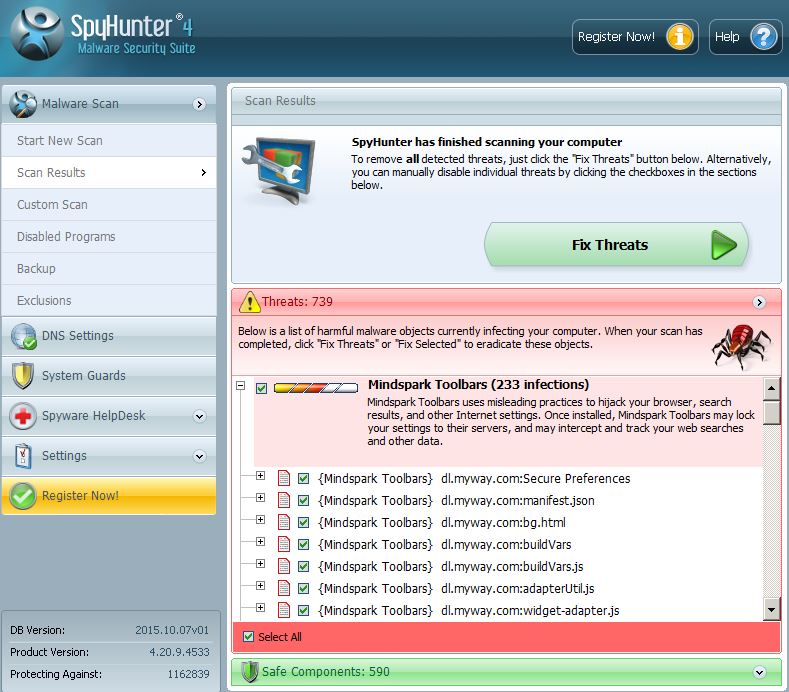
Step 1: Scan for TeslaCrypt with SpyHunter Anti-Malware Tool



Ransomware Automatic Removal - Video Guide
Step 2: Uninstall TeslaCrypt and related malware from Windows
Here is a method in few easy steps that should be able to uninstall most programs. No matter if you are using Windows 10, 8, 7, Vista or XP, those steps will get the job done. Dragging the program or its folder to the recycle bin can be a very bad decision. If you do that, bits and pieces of the program are left behind, and that can lead to unstable work of your PC, errors with the file type associations and other unpleasant activities. The proper way to get a program off your computer is to Uninstall it. To do that:


 Follow the instructions above and you will successfully delete most unwanted and malicious programs.
Follow the instructions above and you will successfully delete most unwanted and malicious programs.
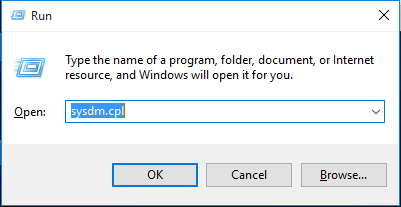
Step 3: Clean any registries, created by TeslaCrypt on your computer.
The usually targeted registries of Windows machines are the following:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
You can access them by opening the Windows registry editor and deleting any values, created by TeslaCrypt there. This can happen by following the steps underneath:


 Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Before starting "Step 4", please boot back into Normal mode, in case you are currently in Safe Mode.
This will enable you to install and use SpyHunter 5 successfully.
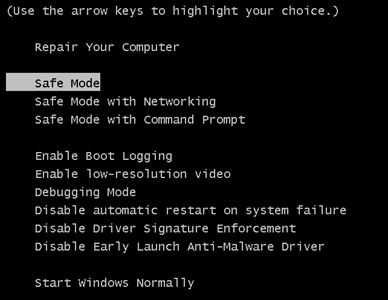
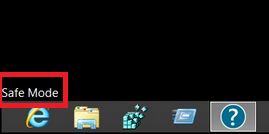
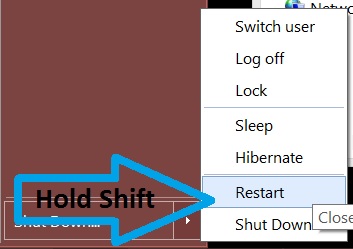
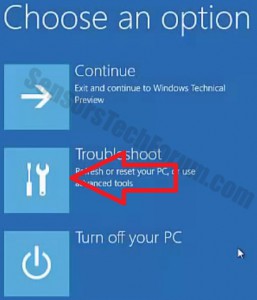
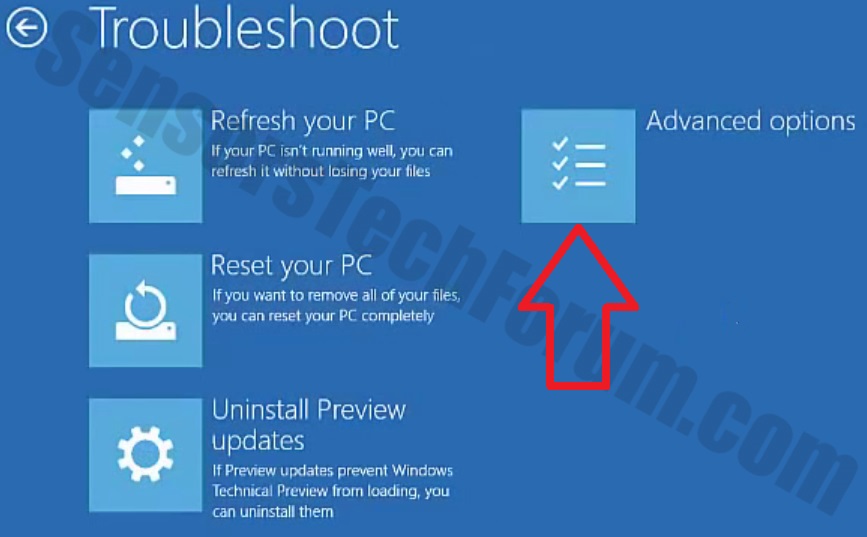
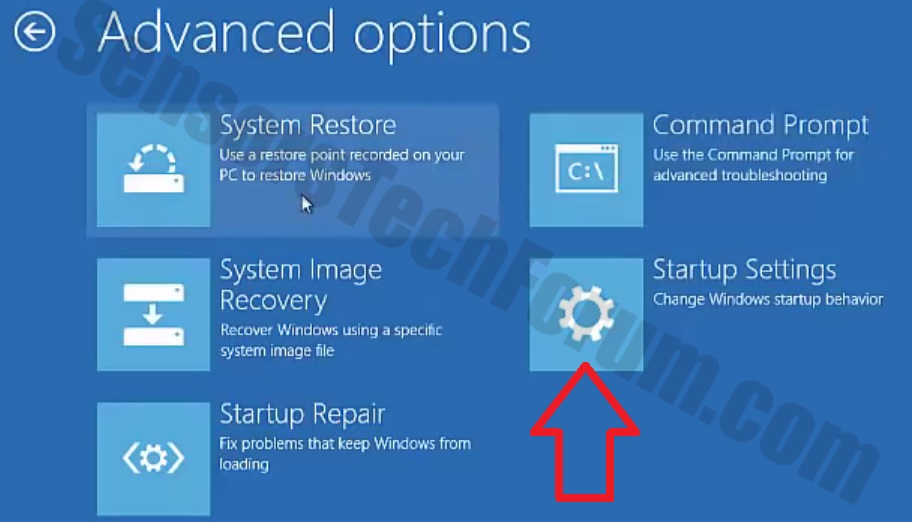
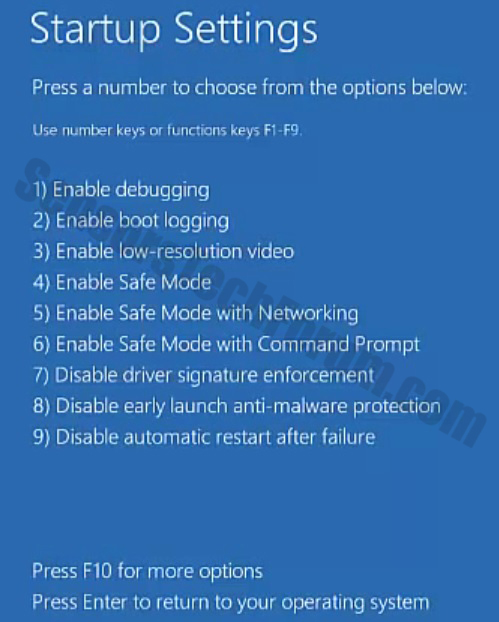
Step 4: Boot Your PC In Safe Mode to isolate and remove TeslaCrypt





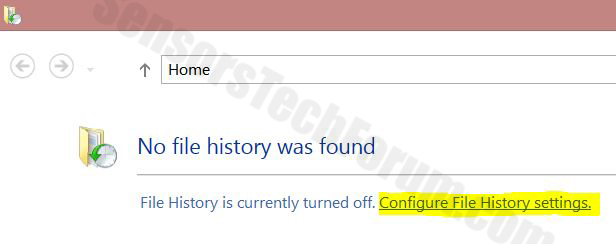
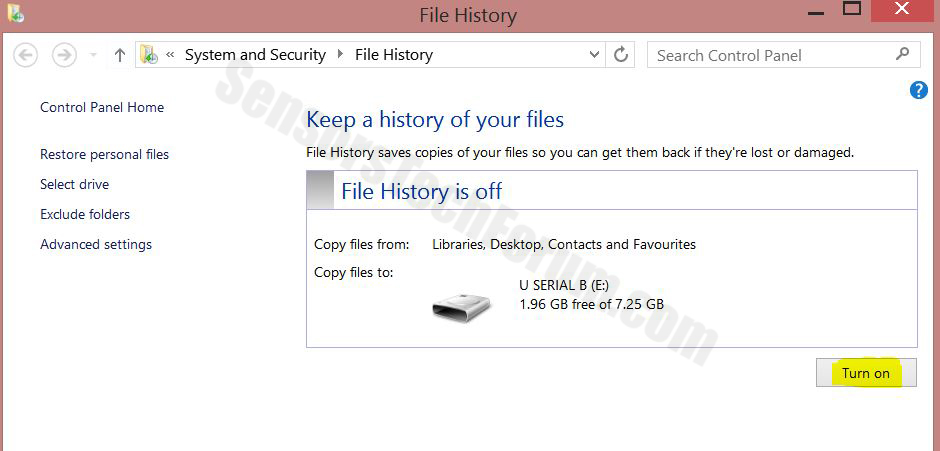
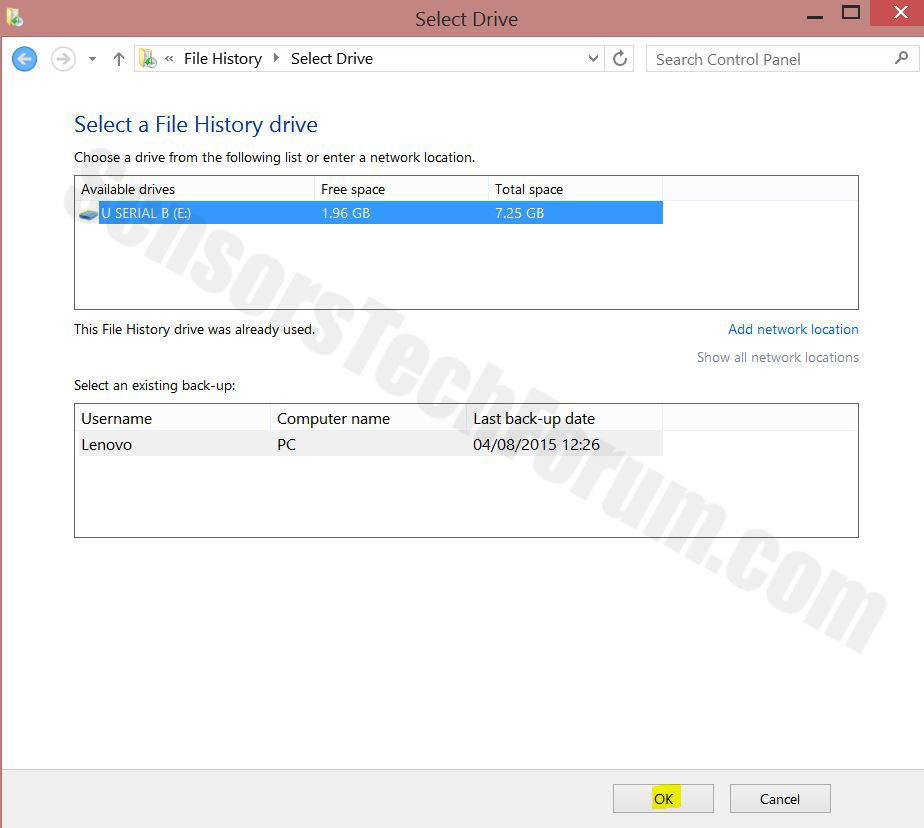
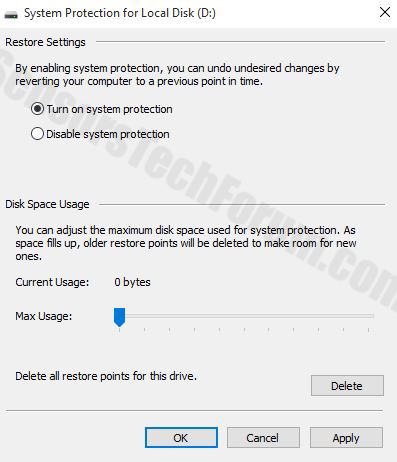
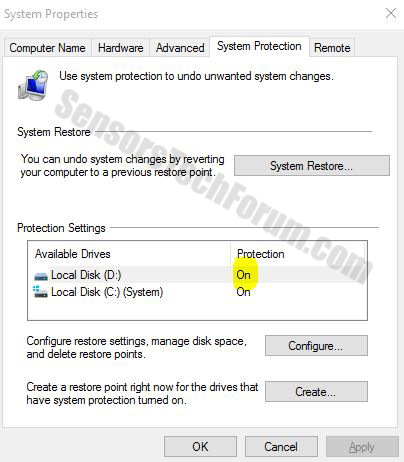
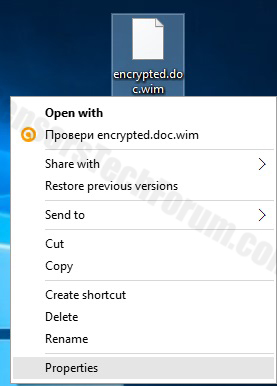
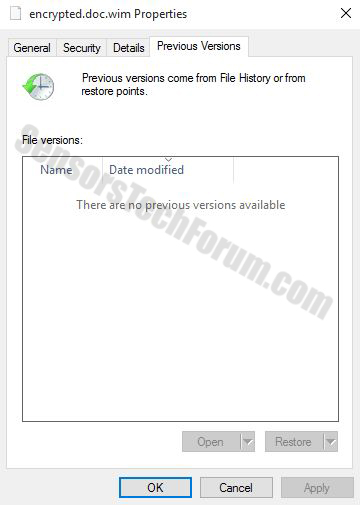
Step 5: Try to Restore Files Encrypted by TeslaCrypt.
Method 1: Use STOP Decrypter by Emsisoft.
Not all variants of this ransomware can be decrypted for free, but we have added the decryptor used by researchers that is often updated with the variants which become eventually decrypted. You can try and decrypt your files using the instructions below, but if they do not work, then unfortunately your variant of the ransomware virus is not decryptable.
Follow the instructions below to use the Emsisoft decrypter and decrypt your files for free. You can download the Emsisoft decryption tool linked here and then follow the steps provided below:
1 Right-click on the decrypter and click on Run as Administrator as shown below:

2. Agree with the license terms:

3. Click on "Add Folder" and then add the folders where you want files decrypted as shown underneath:

4. Click on "Decrypt" and wait for your files to be decoded.

Note: Credit for the decryptor goes to Emsisoft researchers who have made the breakthrough with this virus.
Method 2: Use data recovery software
Ransomware infections and TeslaCrypt aim to encrypt your files using an encryption algorithm which may be very difficult to decrypt. This is why we have suggested a data recovery method that may help you go around direct decryption and try to restore your files. Bear in mind that this method may not be 100% effective but may also help you a little or a lot in different situations.
Simply click on the link and on the website menus on the top, choose Data Recovery - Data Recovery Wizard for Windows or Mac (depending on your OS), and then download and run the tool.
TeslaCrypt-FAQ
What is TeslaCrypt Ransomware?
TeslaCrypt is a ransomware infection - the malicious software that enters your computer silently and blocks either access to the computer itself or encrypt your files.
Many ransomware viruses use sophisticated encryption algorithms to make your files inaccessible. The goal of ransomware infections is to demand that you pay a ransom payment to get access to your files back.
What Does TeslaCrypt Ransomware Do?
Ransomware in general is a malicious software that is designed to block access to your computer or files until a ransom is paid.
Ransomware viruses can also damage your system, corrupt data and delete files, resulting in the permanent loss of important files.
How Does TeslaCrypt Infect?
Via several ways.TeslaCrypt Ransomware infects computers by being sent via phishing emails, containing virus attachment. This attachment is usually masked as an important document, like an invoice, bank document or even a plane ticket and it looks very convincing to users.
Another way you may become a victim of TeslaCrypt is if you download a fake installer, crack or patch from a low reputation website or if you click on a virus link. Many users report getting a ransomware infection by downloading torrents.
How to Open .TeslaCrypt files?
You can't without a decryptor. At this point, the .TeslaCrypt files are encrypted. You can only open them once they are decrypted using a specific decryption key for the particular algorithm.
What to Do If a Decryptor Does Not Work?
Do not panic, and backup the files. If a decryptor did not decrypt your .TeslaCrypt files successfully, then do not despair, because this virus is still new.
Can I Restore ".TeslaCrypt" Files?
Yes, sometimes files can be restored. We have suggested several file recovery methods that could work if you want to restore .TeslaCrypt files.
These methods are in no way 100% guaranteed that you will be able to get your files back. But if you have a backup, your chances of success are much greater.
How To Get Rid of TeslaCrypt Virus?
The safest way and the most efficient one for the removal of this ransomware infection is the use a professional anti-malware program.
It will scan for and locate TeslaCrypt ransomware and then remove it without causing any additional harm to your important .TeslaCrypt files.
Can I Report Ransomware to Authorities?
In case your computer got infected with a ransomware infection, you can report it to the local Police departments. It can help authorities worldwide track and determine the perpetrators behind the virus that has infected your computer.
Below, we have prepared a list with government websites, where you can file a report in case you are a victim of a cybercrime:
Cyber-security authorities, responsible for handling ransomware attack reports in different regions all over the world:
Germany - Offizielles Portal der deutschen Polizei
United States - IC3 Internet Crime Complaint Centre
United Kingdom - Action Fraud Police
France - Ministère de l'Intérieur
Italy - Polizia Di Stato
Spain - Policía Nacional
Netherlands - Politie
Poland - Policja
Portugal - Polícia Judiciária
Greece - Cyber Crime Unit (Hellenic Police)
India - Mumbai Police - CyberCrime Investigation Cell
Australia - Australian High Tech Crime Center
Reports may be responded to in different timeframes, depending on your local authorities.
Can You Stop Ransomware from Encrypting Your Files?
Yes, you can prevent ransomware. The best way to do this is to ensure your computer system is updated with the latest security patches, use a reputable anti-malware program and firewall, backup your important files frequently, and avoid clicking on malicious links or downloading unknown files.
Can TeslaCrypt Ransomware Steal Your Data?
Yes, in most cases ransomware will steal your information. It is a form of malware that steals data from a user's computer, encrypts it, and then demands a ransom in order to decrypt it.
In many cases, the malware authors or attackers will threaten to delete the data or publish it online unless the ransom is paid.
Can Ransomware Infect WiFi?
Yes, ransomware can infect WiFi networks, as malicious actors can use it to gain control of the network, steal confidential data, and lock out users. If a ransomware attack is successful, it could lead to a loss of service and/or data, and in some cases, financial losses.
Should I Pay Ransomware?
No, you should not pay ransomware extortionists. Paying them only encourages criminals and does not guarantee that the files or data will be restored. The better approach is to have a secure backup of important data and be vigilant about security in the first place.
What Happens If I Don't Pay Ransom?
If you don't pay the ransom, the hackers may still have access to your computer, data, or files and may continue to threaten to expose or delete them, or even use them to commit cybercrimes. In some cases, they may even continue to demand additional ransom payments.
Can a Ransomware Attack Be Detected?
Yes, ransomware can be detected. Anti-malware software and other advanced security tools can detect ransomware and alert the user when it is present on a machine.
It is important to stay up-to-date on the latest security measures and to keep security software updated to ensure ransomware can be detected and prevented.
Do Ransomware Criminals Get Caught?
Yes, ransomware criminals do get caught. Law enforcement agencies, such as the FBI, Interpol and others have been successful in tracking down and prosecuting ransomware criminals in the US and other countries. As ransomware threats continue to increase, so does the enforcement activity.
About the TeslaCrypt Research
The content we publish on SensorsTechForum.com, this TeslaCrypt how-to removal guide included, is the outcome of extensive research, hard work and our team’s devotion to help you remove the specific malware and restore your encrypted files.
How did we conduct the research on this ransomware?
Our research is based on an independent investigation. We are in contact with independent security researchers, and as such, we receive daily updates on the latest malware and ransomware definitions.
Furthermore, the research behind the TeslaCrypt ransomware threat is backed with VirusTotal and the NoMoreRansom project.
To better understand the ransomware threat, please refer to the following articles which provide knowledgeable details.
As a site that has been dedicated to providing free removal instructions for ransomware and malware since 2014, SensorsTechForum’s recommendation is to only pay attention to trustworthy sources.
How to recognize trustworthy sources:
- Always check "About Us" web page.
- Profile of the content creator.
- Make sure that real people are behind the site and not fake names and profiles.
- Verify Facebook, LinkedIn and Twitter personal profiles.



 1. For Windows 7,XP and Vista.
1. For Windows 7,XP and Vista. 2. For Windows 8, 8.1 and 10.
2. For Windows 8, 8.1 and 10.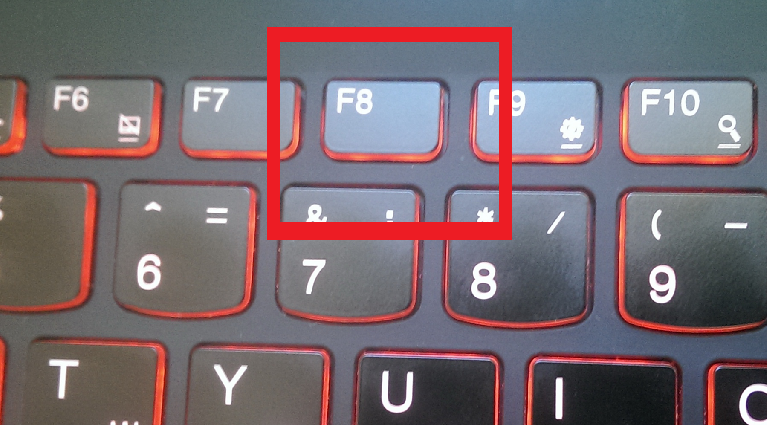
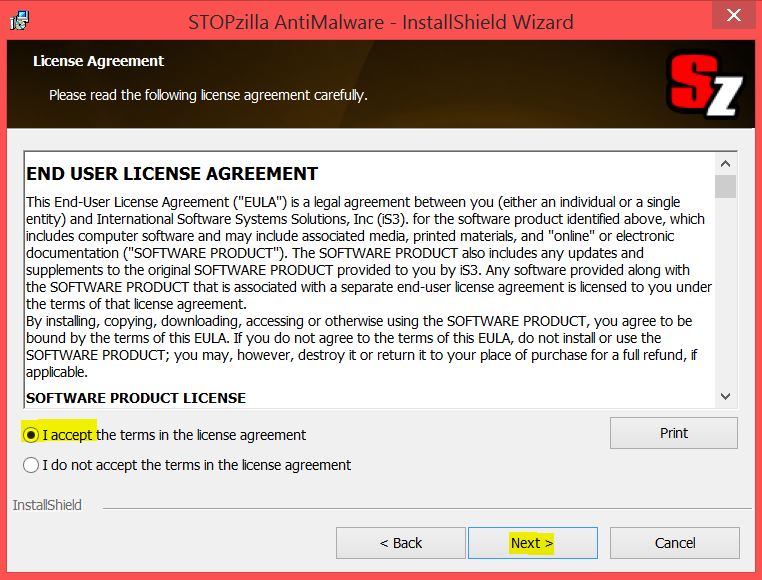
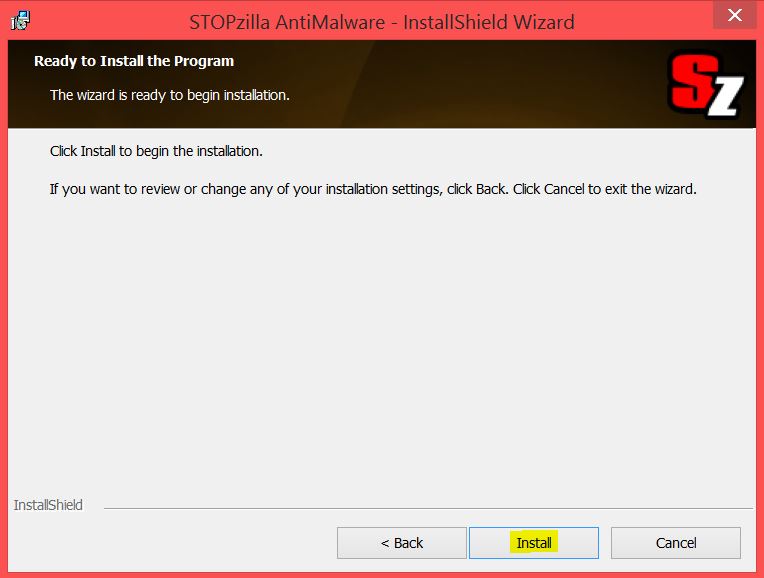
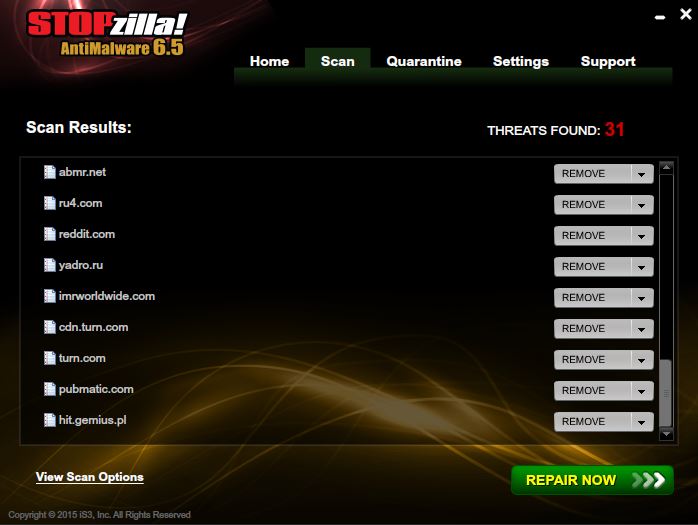
 1. Install SpyHunter to scan for and remove TeslaCrypt.
1. Install SpyHunter to scan for and remove TeslaCrypt.


 STOPZilla Anti Malware
STOPZilla Anti Malware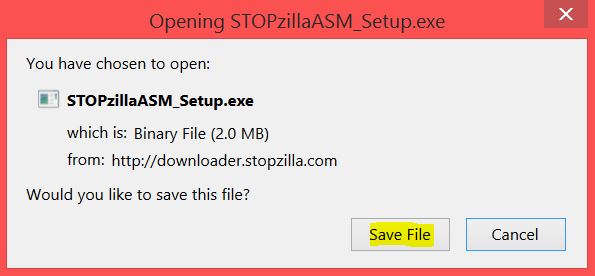

ok good explanation , but is there any way to encrypt files?
Hello,
To all users who have had their files ENCRYPTED.
The newest variant of TeslaCrypt is not yet analyzed so there may be very little chance to decrypt your files.
But you can still try with the following decryption tools, mentioned in our forum:
sensorstechforum.com/forums/malware-removal-questions-and-guides/restore-vvv-files-encrypted-by-teslacrypt-ransomware/
sensorstechforum.com/forums/malware-removal-questions-and-guides/restore-vvv-files-encrypted-by-teslacrypt-ransomware/
Please, let the others know if it worked so that you can raise awareness.
Thanks!
bonjour
moi aussi piégé par tesla….
avez-vous du nouveau pour décrypter?
merci
buenas tardes,
actualmente me encuentro que con este problema en el servidor de la empresa donde trabajo, que tan confiable y seguro son los pasos que sugieren para la solucion a este problema?
bueno quedo en espera de sus comentarios, saludos…
gracias.
Hello Omar,
Sorry to hear you have been attacked by TeslaCrypt.
First of all, please tell us what you have done so far. Have you isolated the threat successfully?
Please refer to the topic at our forum:
sensorstechforum.com/forums/malware-removal-questions-and-guides/restore-vvv-files-encrypted-by-teslacrypt-ransomware/
milena buenos dias,
hasta ahortia estoy recuperando las veriones anteriores de cada carpeta dentro del servidor, a que te refieres que si tengo aislado la amenaza exito?
de que manera me puedes ayudar, debido a que el foro esta en ingles y no lo entiendo muy bien, saludos
con que programa has recuperado las versiones anteriores de las carpetas que mencionas
Hi Jose, what program have you used?
Hello Omar,
If I understand correctly, you can see folders in your previous versions. Before doing anything else, you should remove TeslaCrypt with an anti-malware tool. Let me know how it goes. Also, it would help if you send me an email to idunn0 @ abv.bg with 3 or 4 encrypted files and some files of the virus (.tmp, .bin, .exe or .dll).
Thanks in advance and looking forward to your reply.
Tengo todo encriptados en .vvv y no me funciono shadow explorer y trate con recuba y al recuperar sale como que nada se ha eliminado y me muestra los mismos archivos encriptados que podría hacer
gracias
Hi Jorge, there are several decryptors that can be tried to restore files. However, every version of Teslacrypt uses different combination of file-encryption techniques.
Here is how to remove TeslaCrypt: sensorstechforum.com/forums/malware-removal-questions-and-guides/remove-malware-from-your-pc-completely/
The decryptors: The TeslaDecoder by BloodDolly, Talos TeslaCrypt Decryption Tool, EaseUS Data Recovery Wizard Free. More information is available here: sensorstechforum.com/forums/malware-removal-questions-and-guides/restore-vvv-files-encrypted-by-teslacrypt-ransomware/
Let us know what happens.
Regards,
Milena
Dear Milena,
First of all thank you very much for your useful comments for infected users, i read all above comments and other referenced pages too, we need to know how i can try “Network Sniffer” which wrote in this page, and with which software ? thanks in advance.
Hola a todos, mi equipo con windows xp tambíen ha sido infectado y ahora todos los archivos están con extensión .vvv, habría alguna forma de desencriptar dichos archivos? he leido por ahí en muchas páginas que por el momento es completamente imposible…
He probado varios programas de recuperación de archivos y no hay manera, ojala alguien pueda dar con alguna solucíon. Por el momento creo que he quitado el virus con malwarebytes
Hi David,
We will let you know immediately, if a solution is found…
hola Milena, tengo el mismo problema que comentan los demás me paso lo mismo, los únicos archivos que no se infectaron fue unas fotos que había recuperado con el programa recovery my file, el resto de fotos que estaban con extensión jpg aun no logro recuperar, si tienes algún software para corregir el cifrado se agradece.
Hi Oscar, you can find information about decryptors here: sensorstechforum.com/forums/malware-removal-questions-and-guides/restore-vvv-files-encrypted-by-teslacrypt-ransomware/
je suis infecté par teslacrypt extension .vvv j’ai le script qui a posé pb est ce que de ce script je peux trouver la clé ?
j’ai également le fichier d’origine et le fichier infecté en word et excel. je n’ai malheureusement pas trouver le fichier key.dat puis-je espérer décrypter mes fichiers svp ?
merci par avance
Samy
buongiorno a tutti, quindi un modo per provare a recuperare i file crittati c’è o no ?? con cosa si può provare? io ho provato solo a rinominare il file ma non funziona.
Bonjour tous le monde
Mon pc est affecté par un virus ou je sais pas quoi, tous mes fichiers Word, PDF, et image ainsi que les xl sont devenu .vvv
Veuillez m’informer sur une solution SVP
Cordialement
Ouachic
J’ai exactement le même problème depuis ce matin,
avez-vous une réponse ?
Merci
Même chose pour moi … infecter depuis ce matin … tout mes fichier, tonne de photo de famille / voyage etc est rendu avec l’extension .VVV …. Est-ce Teslacrypt, Cryptowall,Cryptolocker….. bref je suis legerement paniquer en ce moment. Je suis presentement en train de scanner mon PC avec SpyHunter 4 …. est-ce la bonne marche a suivre ?
Est-ce que Spyhunter seras en mesure de suprimer ce virus ?
Il y a t’il espoir de reussir a tout decrypter ou ma seule alternative serais de payer la foutu rencon ?
Merci a l’avance … d’un père de famille bien désespérer … McAfee antivirus … gros ZERO !!!
Hello Eric and Steph, an antivirus program should remove the leftovers of the ransomware. However, it won’t be able to decrypt the encrypted files. Please keep in mind that every infection is unique, and that there are may be more variants of the same ransomware.
You can find information about decryptors here: sensorstechforum.com/forums/malware-removal-questions-and-guides/restore-vvv-files-encrypted-by-teslacrypt-ransomware/
Hallo, leider funktioniert keiner der Links zum Forum?!
“Nichts gefunden
> 404
Entschuldigen Sie bitte, aber keine Ergebnisse wurden für Ihre Anfrage gefunden. Vielleicht suchen helfen Sie zu finden verwandten Inhalten.”
Ich habe den Tesla Crypt eliminiert mit Spy Hunter.
Was bleibt sind .vvv Dateianhänge an Dateien wie .pdf .docx .doc .xls .bmp .png .pst // ect.
Mit welchen Programmen kann ich testen zum Encrypten der Dateien??
Hello Pedro,
Follow this link to open our forum sensorstechforum.com/forums/malware-removal-questions-and-guides/restore-vvv-files-encrypted-by-teslacrypt-ransomware/. We have provided information about the decryptors there – TeslaDecoder by BloodDolly, Talos TeslaCrypt Decryption Tool, EaseUS Data Recovery Wizard Free.
Does anyone know if this version drops files in particular locations? Or leaves clues to its presence in the registry, etc.?
Also, is there a Trojan involved in this? If so, where might its location be?
Hey Luke!
TeslaCrypt is a Trojan horse ransomware. This means that it is a Trojan itself, and it was spread with other malware.
There were executables that dropped with the ransomware in these locations:
%Temp%
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
or randomly in the C: drive.
But no data for the key was dropped for this variant, neither was the Windows Registry tampered by it.
Fortunately, this ransomware case has already been resolved : sensorstechforum.com/teslacrypt-master-decryption-key-available
Stay tuned!
STForum
Hi,
You can use the shadow copy of your windows to recover the previous version before the attack. This is the best safest way. You can have other tool like ShadowExplorer-0.9-portable that will help to recover your previous good version.
Regards
Zahur
No ser como solucionar lo del crab, e restaurado i nada
Grüß euch alle!
Nach über 10 Jahren habe ich es wiede mal geschafft meinen PC zu infizieren. Ärgerlich das dies nur durch meine unvorsichtigkeit auf einem zweiten System passiert ist und von diesem dann alles verschlüsselt wurde.
Da ich mit einigen Antiviren usw. (bitDefender wäre meine empfehlung! Stand 15.05.2018) drüber gefahren bin ist das System sauber aber ich kann leider nicht mehr sagen welches genau den PC befallen hat.
Milena Dimitrova
Alle dateien enden mit .2226499124.ransomed@india.com und beim ausführen wird angezeigt das es eine MS-Dos anwendung sei.
DateiTyp: MS-DOS-Anwendung (.com)
2226499124 wäre ja meine ID bei den Spasten!
ransomedia@india.com wird sicher nicht die Dateienendung sein.
Können Sie mir behilflich sein?
Kann ich noch etwas tun um Ihnen mehr Informationen zu geben?
Bendake mich schon mal im Voraus
Aysses