Article, created to help users remove the .Sage file virus and try to restore AES encrypted files by Sage ransomware for free.
Article, created to help users remove the .Sage file virus and try to restore AES encrypted files by Sage ransomware for free.
Users have begun to complain about a new ransomware threat on the loose that has the ability to render the files on targeted computers no longer openable. The virus is named Sage and its primary goal is to extort users for the decryption of their files, which the virus scrambles after infecting. The virus demands different sum for different infection. Some websites report it to want the sum of approximately 0.7 BTC and we have seen a website related to it, which demands the sum of 0.2 BTC. Anyone who has been infected by Sage ransomware is strongly advised not to pay any ransom amount and to focus on removing the virus and restoring the files using alternative file restoration methods.

Threat Summary
| Name | Sage |
| Type | Ransomware, Cryptovirus |
| Short Description | The Sage ransomware encrypts your data and then displays a ransom message with instructions for payment. |
| Symptoms | Sage ransomware encrypts the files and adds the .sage file extension. A ransom note is dropped on the desktop with the following content. |
| Distribution Method | Spam Emails, Email Attachments, malicious .xls files, .htm Files, .js files, .ZIP archives |
| Detection Tool |
See If Your System Has Been Affected by malware
Download
Malware Removal Tool
|
User Experience | Join Our Forum to Discuss Sage. |
| Data Recovery Tool | Windows Data Recovery by Stellar Phoenix Notice! This product scans your drive sectors to recover lost files and it may not recover 100% of the encrypted files, but only few of them, depending on the situation and whether or not you have reformatted your drive. |
Update November 2017. After Sage’s initial appearance on the malware scene in December 2016, the virus continues to attack users, encrypting their files and demanding ransom in exchange for decryption. Sage has also seen 2 updates in Sage 2.0 and Sage 2.2. In terms of distribution, it has been established that Sage operators mostly rely on phishing emails containing Microsoft Office documents with malicious macros. The virus continues to be dropped by downloader scripts spread via the very same malicious emails. Malwarebytes researchers were able to identify the list of files targeted by Sage ransomware. The ransomware comes with an extensive list of the targeted extensions, which is hard-coded in the binary. Here is the list:
dat mx0 cd pdb xqx old cnt rtp qss qst fx0 fx1 ipg ert pic img cur fxr
slk m4u mpe mov wmv mpg vob mpeg 3g2 m4v avi mp4 flv mkv 3gp asf m3u m3u8
wav mp3 m4a m rm flac mp2 mpa aac wma djv pdf djvu jpeg jpg bmp png jp2 lz
rz zipx gz bz2 s7z tar 7z tgz rar ziparc paq bak set back std vmx vmdk vdi
qcow ini accd db sqli sdf mdf myd frm odb myi dbf indb mdb ibd sql cgn dcr
fpx pcx rif tga wpg wi wmf tif xcf tiff xpm nef orf ra bay pcd dng ptx r3d
raf rw2 rwl kdc yuv sr2 srf dip x3f mef raw log odg uop potx potm pptx rss
pptm aaf xla sxd pot eps as3 pns wpd wps msg pps xlam xll ost sti sxi otp
odp wks vcf xltx xltm xlsx xlsm xlsb cntk xlw xlt xlm xlc dif sxc vsd ots
prn ods hwp dotm dotx docm docx dot cal shw sldm txt csv mac met wk3 wk4
uot rtf sldx xls ppt stw sxw dtd eml ott odt doc odm ppsm xlr odc xlk ppsx
obi ppam text docb wb2 mda wk1 sxm otg oab cmd bat h asx lua pl as hpp clas
js fla py rb jsp cs c jar java asp vb vbs asm pas cpp xml php plb asc lay6
pp4 pp5 ppf pat sct ms11 lay iff ldf tbk swf brd css dxf dds efx sch dch
ses mml fon gif psd html ico ipe dwg jng cdr aep aepx 123 prel prpr aet
fim pfb ppj indd mhtm cmx cpt csl indl dsf ds4 drw indt pdd per lcd pct
prf pst inx plt idml pmd psp ttf 3dm ai 3ds ps cpx str cgm clk cdx xhtm
cdt fmv aes gem max svg mid iif nd 2017 tt20 qsm 2015 2014 2013 aif qbw
qbb qbm ptb qbi qbr 2012 des v30 qbo stc lgb qwc qbp qba tlg qbx qby 1pa
ach qpd gdb tax qif t14 qdf ofx qfx t13 ebc ebq 2016 tax2 mye myox ets
tt14 epb 500 txf t15 t11 gpc qtx itf tt13 t10 qsd iban ofc bc9 mny 13t
qxf amj m14 _vc tbp qbk aci npc qbmb sba cfp nv2 tfx n43 let tt12 210
dac slp qb20 saj zdb tt15 ssg t09 epa qch pd6 rdy sic ta1 lmr pr5 op sdy
brw vnd esv kd3 vmb qph t08 qel m12 pvc q43 etq u12 hsr ati t00 mmw bd2
ac2 qpb tt11 zix ec8 nv lid qmtf hif lld quic mbsb nl2 qml wac cf8 vbpf
m10 qix t04 qpg quo ptdb gto pr0 vdf q01 fcr gnc ldc t05 t06 tom tt10
qb1 t01 rpf t02 tax1 1pe skg pls t03 xaa dgc mnp qdt mn8 ptk t07 chg
#vc qfi acc m11 kb7 q09 esk 09i cpw sbf mql dxi kmo md u11 oet ta8 efs
h12 mne ebd fef qpi mn5 exp m16 09t 00c qmt cfdi u10 s12 qme int? cf9
ta5 u08 mmb qnx q07 tb2 say ab4 pma defx tkr q06 tpl ta2 qob m15 fca eqb
q00 mn4 lhr t99 mn9 qem scd mwi mrq q98 i2b mn6 q08 kmy bk2 stm mn1 bc8
pfd bgt hts tax0 cb resx mn7 08i mn3 ch meta 07i rcs dtl ta9 mem seam
btif 11t efsl $ac emp imp fxw sbc bpw mlb 10t fa1 saf trm fa2 pr2 xeq
sbd fcpa ta6 tdr acm lin dsb vyp emd pr1 mn2 bpf mws h11 pr3 gsb mlc
nni cus ldr ta4 inv omf reb qdfx pg coa rec rda ffd ml2 ddd ess qbmd
afm d07 vyr acr dtau ml9 bd3 pcif cat h10 ent fyc p08 jsd zka hbk bkf
mone pr4 qw5 cdf gfi cht por qbz ens 3pe pxa intu trn 3me 07g jsda
2011 fcpr qwmo t12 pfx p7b der nap p12 p7c crt csr pem gpg key
Sage Virus – Distribution Strategy
In order to successfully spread and infect users, Sage ransomware may use spam campaigns that redistribute different types of files. These spam campaigns are focused primarily on inexperienced users and may contain e-mail attachments as well as malicious web links that may cause an infection via several different methods:
- Via malicious javascript.
- Via malicious macros.
- Via executables that are contained directly in an archive uploaded as an attachment.
After the user has already opened the malicious Sage files, the ransomware performs several different activities to drop malicious files In important Windows folders like the following:
- %AppData%
- %Roaming%
- %Local%
- %SystemDrive%
Sage Ransomware – Post-Infection Analysis
As soon as Sage ransomware has infected the user, the virus immediately modifies the registry entries of the affected computer. To perform this, sage may attack the following Windows registry keys:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Besides the Run and RunOnce keys which make its malicious executables encrypt files on Windows startup, the Sage virus may also perform other modifications of other types of files on compromised machines, such as add value strings in keys that change the wallpaper, drop files on the desktop and open them and others.
To encrypt user files, the Sage virus uses the AES encryption algorithm. This cipher is used with the one and only purpose of encrypting blocks of data in the source code of the infected file. This encryption procedure is enough to render a file no longer openable. For the encryption, Sage ransomware attacks files that are:
- Videos.
- Audio files.
- Files, related to Microsoft Office documents.
- Adobe Reader files.
- Images.
- Database files.
- Virtual drives.
As soon as Sage ransomware has performed the encryption, it adds the .sage file extension to the encrypted files. When this has been done, the files look like the following:
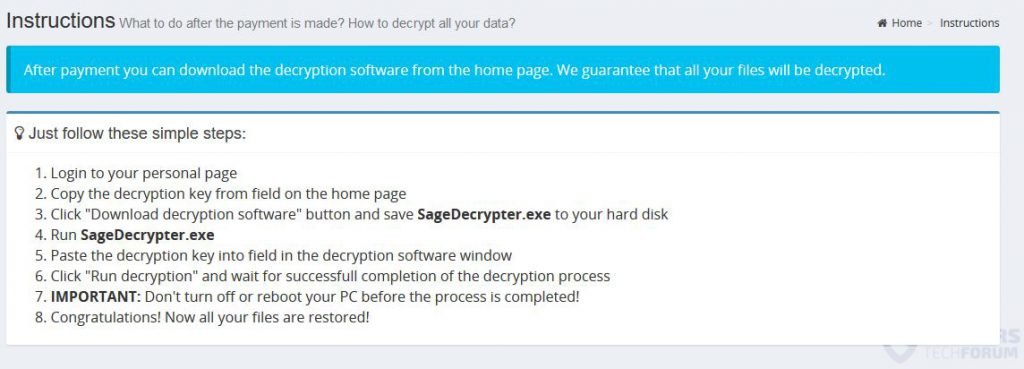
After encryption, Sage ransomware drops a very large ransom note to notify the user to open their website, which in return has the following message:
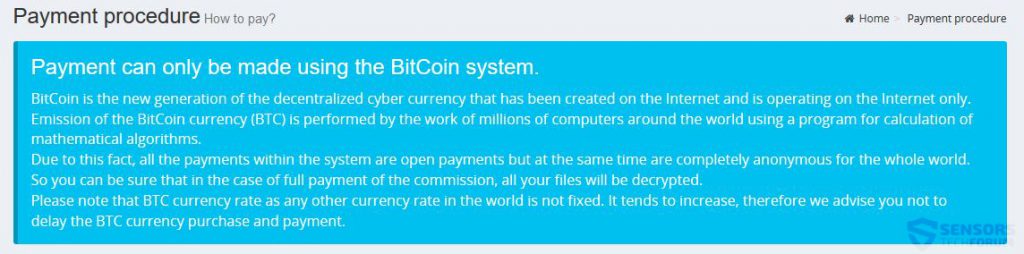
The website of Sage ransomware also includes advanced instructions on how to turn money in to BitCoin and use this to conduct a payment to the user.
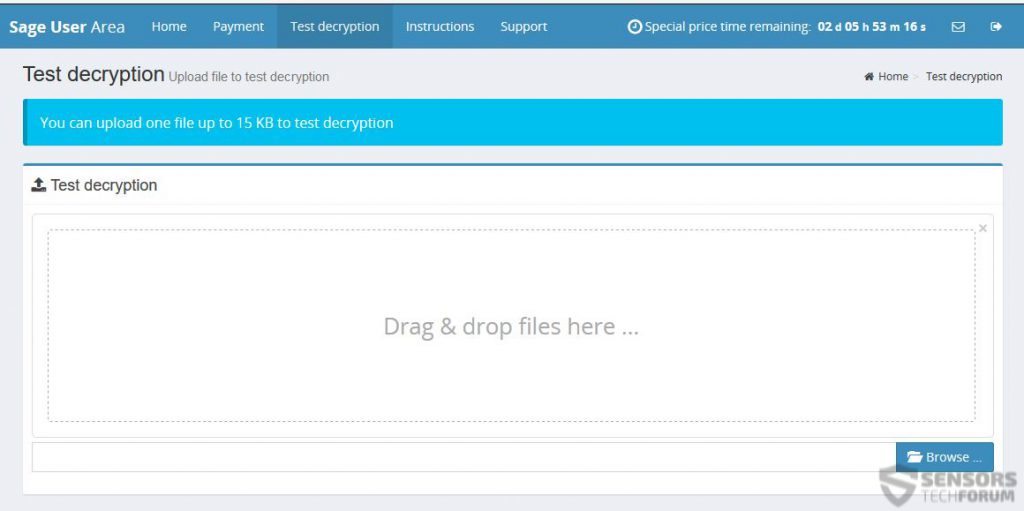
Not only this, but similar to Cerber ransomware, Sage also offers decryption of 1 file for free as customer support.

Remove Sage Ransowmare and Restore Encrypted Files
In order to completely remove Sage ransomware, we urge you to follow the removal instructions below. In case you are having difficulties in manually removing the virus from your computer, experts recommend deleting it automatically via downloading and installing an advanced program for malware removal which will take care of this threat for you automatically. The instructions also include Alternative file restoration methods in step “2. Restore files encrypted by Sage” below. We advise you to backup the encrypted files before testing those tools since they may damage them. Also, bear in mind that those methods are not 100% effective, but they may also partially work for you.
- Step 1
- Step 2
- Step 3
- Step 4
- Step 5
Step 1: Scan for Sage with SpyHunter Anti-Malware Tool



Ransomware Automatic Removal - Video Guide
Step 2: Uninstall Sage and related malware from Windows
Here is a method in few easy steps that should be able to uninstall most programs. No matter if you are using Windows 10, 8, 7, Vista or XP, those steps will get the job done. Dragging the program or its folder to the recycle bin can be a very bad decision. If you do that, bits and pieces of the program are left behind, and that can lead to unstable work of your PC, errors with the file type associations and other unpleasant activities. The proper way to get a program off your computer is to Uninstall it. To do that:


 Follow the instructions above and you will successfully delete most unwanted and malicious programs.
Follow the instructions above and you will successfully delete most unwanted and malicious programs.
Step 3: Clean any registries, created by Sage on your computer.
The usually targeted registries of Windows machines are the following:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
You can access them by opening the Windows registry editor and deleting any values, created by Sage there. This can happen by following the steps underneath:


 Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Before starting "Step 4", please boot back into Normal mode, in case you are currently in Safe Mode.
This will enable you to install and use SpyHunter 5 successfully.
Step 4: Boot Your PC In Safe Mode to isolate and remove Sage





Step 5: Try to Restore Files Encrypted by Sage.
Method 1: Use STOP Decrypter by Emsisoft.
Not all variants of this ransomware can be decrypted for free, but we have added the decryptor used by researchers that is often updated with the variants which become eventually decrypted. You can try and decrypt your files using the instructions below, but if they do not work, then unfortunately your variant of the ransomware virus is not decryptable.
Follow the instructions below to use the Emsisoft decrypter and decrypt your files for free. You can download the Emsisoft decryption tool linked here and then follow the steps provided below:
1 Right-click on the decrypter and click on Run as Administrator as shown below:

2. Agree with the license terms:

3. Click on "Add Folder" and then add the folders where you want files decrypted as shown underneath:

4. Click on "Decrypt" and wait for your files to be decoded.

Note: Credit for the decryptor goes to Emsisoft researchers who have made the breakthrough with this virus.
Method 2: Use data recovery software
Ransomware infections and Sage aim to encrypt your files using an encryption algorithm which may be very difficult to decrypt. This is why we have suggested a data recovery method that may help you go around direct decryption and try to restore your files. Bear in mind that this method may not be 100% effective but may also help you a little or a lot in different situations.
Simply click on the link and on the website menus on the top, choose Data Recovery - Data Recovery Wizard for Windows or Mac (depending on your OS), and then download and run the tool.
Sage-FAQ
What is Sage Ransomware?
Sage is a ransomware infection - the malicious software that enters your computer silently and blocks either access to the computer itself or encrypt your files.
Many ransomware viruses use sophisticated encryption algorithms to make your files inaccessible. The goal of ransomware infections is to demand that you pay a ransom payment to get access to your files back.
What Does Sage Ransomware Do?
Ransomware in general is a malicious software that is designed to block access to your computer or files until a ransom is paid.
Ransomware viruses can also damage your system, corrupt data and delete files, resulting in the permanent loss of important files.
How Does Sage Infect?
Via several ways.Sage Ransomware infects computers by being sent via phishing emails, containing virus attachment. This attachment is usually masked as an important document, like an invoice, bank document or even a plane ticket and it looks very convincing to users.
Another way you may become a victim of Sage is if you download a fake installer, crack or patch from a low reputation website or if you click on a virus link. Many users report getting a ransomware infection by downloading torrents.
How to Open .Sage files?
You can't without a decryptor. At this point, the .Sage files are encrypted. You can only open them once they are decrypted using a specific decryption key for the particular algorithm.
What to Do If a Decryptor Does Not Work?
Do not panic, and backup the files. If a decryptor did not decrypt your .Sage files successfully, then do not despair, because this virus is still new.
Can I Restore ".Sage" Files?
Yes, sometimes files can be restored. We have suggested several file recovery methods that could work if you want to restore .Sage files.
These methods are in no way 100% guaranteed that you will be able to get your files back. But if you have a backup, your chances of success are much greater.
How To Get Rid of Sage Virus?
The safest way and the most efficient one for the removal of this ransomware infection is the use a professional anti-malware program.
It will scan for and locate Sage ransomware and then remove it without causing any additional harm to your important .Sage files.
Can I Report Ransomware to Authorities?
In case your computer got infected with a ransomware infection, you can report it to the local Police departments. It can help authorities worldwide track and determine the perpetrators behind the virus that has infected your computer.
Below, we have prepared a list with government websites, where you can file a report in case you are a victim of a cybercrime:
Cyber-security authorities, responsible for handling ransomware attack reports in different regions all over the world:
Germany - Offizielles Portal der deutschen Polizei
United States - IC3 Internet Crime Complaint Centre
United Kingdom - Action Fraud Police
France - Ministère de l'Intérieur
Italy - Polizia Di Stato
Spain - Policía Nacional
Netherlands - Politie
Poland - Policja
Portugal - Polícia Judiciária
Greece - Cyber Crime Unit (Hellenic Police)
India - Mumbai Police - CyberCrime Investigation Cell
Australia - Australian High Tech Crime Center
Reports may be responded to in different timeframes, depending on your local authorities.
Can You Stop Ransomware from Encrypting Your Files?
Yes, you can prevent ransomware. The best way to do this is to ensure your computer system is updated with the latest security patches, use a reputable anti-malware program and firewall, backup your important files frequently, and avoid clicking on malicious links or downloading unknown files.
Can Sage Ransomware Steal Your Data?
Yes, in most cases ransomware will steal your information. It is a form of malware that steals data from a user's computer, encrypts it, and then demands a ransom in order to decrypt it.
In many cases, the malware authors or attackers will threaten to delete the data or publish it online unless the ransom is paid.
Can Ransomware Infect WiFi?
Yes, ransomware can infect WiFi networks, as malicious actors can use it to gain control of the network, steal confidential data, and lock out users. If a ransomware attack is successful, it could lead to a loss of service and/or data, and in some cases, financial losses.
Should I Pay Ransomware?
No, you should not pay ransomware extortionists. Paying them only encourages criminals and does not guarantee that the files or data will be restored. The better approach is to have a secure backup of important data and be vigilant about security in the first place.
What Happens If I Don't Pay Ransom?
If you don't pay the ransom, the hackers may still have access to your computer, data, or files and may continue to threaten to expose or delete them, or even use them to commit cybercrimes. In some cases, they may even continue to demand additional ransom payments.
Can a Ransomware Attack Be Detected?
Yes, ransomware can be detected. Anti-malware software and other advanced security tools can detect ransomware and alert the user when it is present on a machine.
It is important to stay up-to-date on the latest security measures and to keep security software updated to ensure ransomware can be detected and prevented.
Do Ransomware Criminals Get Caught?
Yes, ransomware criminals do get caught. Law enforcement agencies, such as the FBI, Interpol and others have been successful in tracking down and prosecuting ransomware criminals in the US and other countries. As ransomware threats continue to increase, so does the enforcement activity.
About the Sage Research
The content we publish on SensorsTechForum.com, this Sage how-to removal guide included, is the outcome of extensive research, hard work and our team’s devotion to help you remove the specific malware and restore your encrypted files.
How did we conduct the research on this ransomware?
Our research is based on an independent investigation. We are in contact with independent security researchers, and as such, we receive daily updates on the latest malware and ransomware definitions.
Furthermore, the research behind the Sage ransomware threat is backed with VirusTotal and the NoMoreRansom project.
To better understand the ransomware threat, please refer to the following articles which provide knowledgeable details.
As a site that has been dedicated to providing free removal instructions for ransomware and malware since 2014, SensorsTechForum’s recommendation is to only pay attention to trustworthy sources.
How to recognize trustworthy sources:
- Always check "About Us" web page.
- Profile of the content creator.
- Make sure that real people are behind the site and not fake names and profiles.
- Verify Facebook, LinkedIn and Twitter personal profiles.