Gmail phishing attempts have been registered. Security researchers at Wordfence have detected a highly effective and massively spread phishing technique stealing login credentials for Gmail and other services. Apparently, during the last couple of weeks, tech-savvy users compromised by the Gmail phishing attacks have been sharing reports and details so that more users are aware.
Gmail Phishing Attack: Technical Details
Gmail is the primary target of these attempts, but other services are targeted as well. It’s a typical phishing scam where the attacker would send an email to a Gmail account. The email may appear to be sent by someone the target knows, and that’s because their account has been hacked. The email may include an attachment of an image. Upon clicking on the image to preview it, a new tab will open up and the user will be prompted to sign in to Gmail again. The location bar shows the following address: accounts.google.com, so even the experienced eye may be misled.
Once the sign-in is completed, the targeted account is compromised. Here is what one victim of the phishing scheme shares:
The attackers log in to your account immediately once they get the credentials, and they use one of your actual attachments, along with one of your actual subject lines, and send it to people in your contact list.
For example, they went into one student’s account, pulled an attachment with an athletic team practice schedule, generated the screenshot, and then paired that with a subject line that was tangentially related, and emailed it to the other members of the athletic team.
The whole process happens very quickly, and it is either automated or the attackers are on standby, processing the compromised accounts.
Once access to an account is obtained, the attacker has full access to all the victim’s emails, and is also granted access to other services accessible via the password reset mechanism. This includes other email accounts, SaaS services, etc.
Full description of this Gmail phishing attack is available at Wordfence.
Phishing Schemes Often Compromise Popular Service Like Google
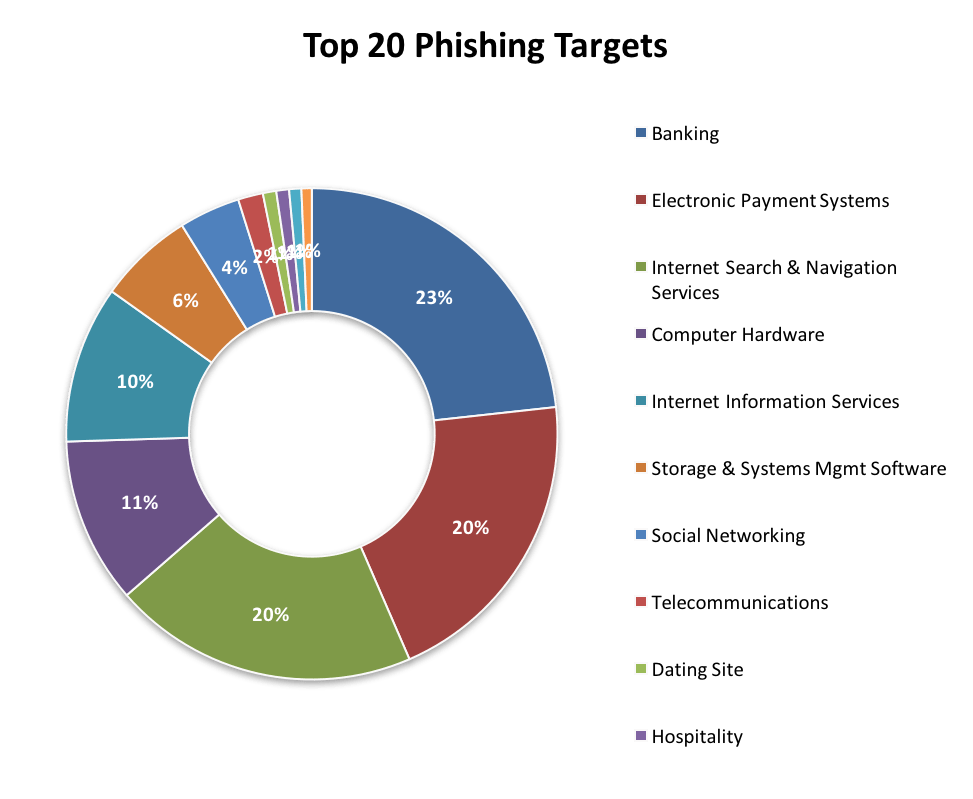
Last year, Webroot researchers established that Google is the company with the largest negative impact of an impersonation. These are outlined as high-risk organizations, with 21% of all phishing sites in the period January-September 2016 impersonating Google.
On top of everything, attackers are restless when it comes to developing new tactics and attack vectors, and phishing is not an exception. Sensitive information is highly desirable, and the shift towards “malicious-software and-activities-as-a-service” only makes things worse.
Phishing Statistics, Update April 2017
LookingGlass Cyber Solutions has reported an increase in phishing activity in the first week of April. Overall phishing activity increased by 30%, the most notable increase being registered in the Electronic Payment Systems industry:
Gmail phishing attempts haven’t been observed. However, phishing attacks on other services have been. Dropbox has been targeted in April, 2017, via smartly crafted emails that look legitimate. One of the scams involving Dropbox was trying to harvest users’ Dropbox login credentials using an order request that looked like a legitimate one. The other scam was trying to steal the user’s email password via a fake file sharing request.
A LinkedIn phishing attack has also been detected being active in Mid-April. The scheme was trying to trick users of the professional network to upload their CVs. Scammers were sending emails about alleged “job openings for active LinkedIn users”.
As you have noticed, despite the different targets (Gmail, Dropbox, Facebook, LinkedIn, various banks, etc.) phishing emails always have a lot in common.
Tips to Protect Yourself from Phishing Attempts
- Be careful with emails demanding personal information from you. Remember that legitimate services typically do not send such requests via email.
- Don’t be tricked into giving away sensitive details, financial details included. Keep in mind that attackers may also use scare tactics to lure you into revealing personally identifiable information.
- Be careful with generic-looking requests for information. A legitimate email from a legitimate organization such as one’s bank would know the person’s name. Phishing emails often begin with “Dear Sir/Madam”.
- Don’t submit sensitive information via forms within email messages.
- Don’t interact with links or attachments in an email unless you are absolutely sure the email comes from a trustworthy source.
- Make sure that your anti-malware protection has a feature against phishing.
Spy Hunter scanner will only detect the threat. If you want the threat to be automatically removed, you need to purchase the full version of the anti-malware tool.Find Out More About SpyHunter Anti-Malware Tool / How to Uninstall SpyHunter