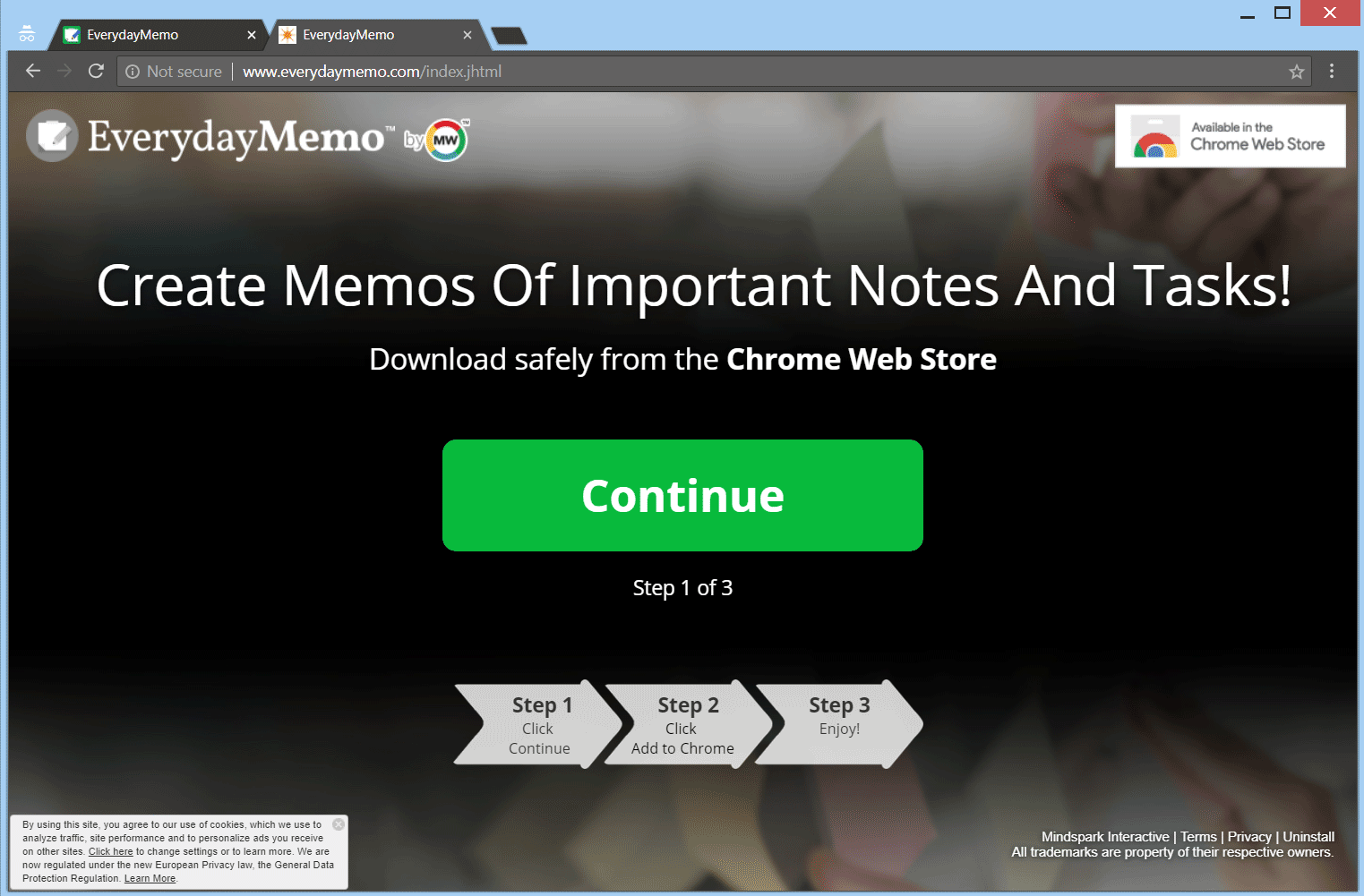
Remove EverydayMemo Browser Hijacker
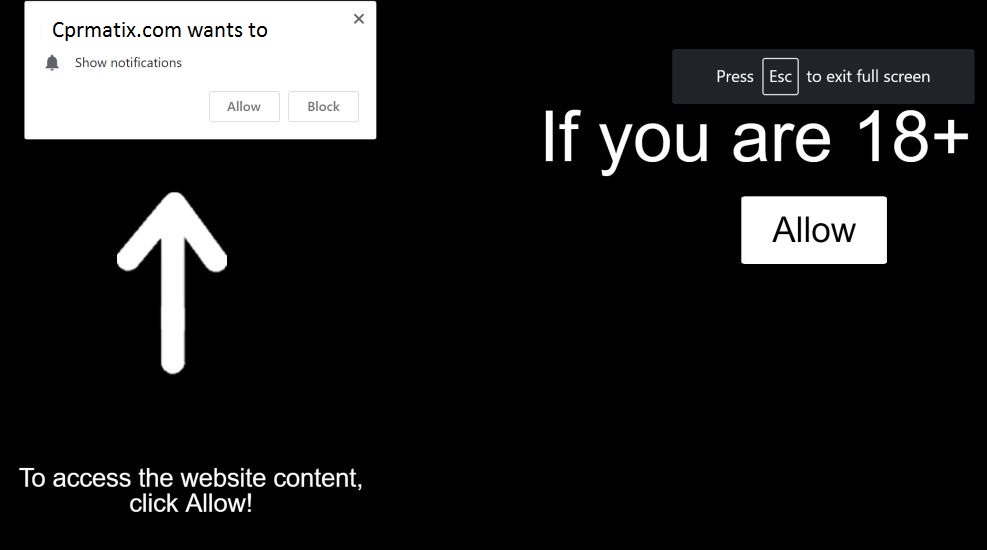
The article will help you to remove EverydayMemo totally. Follow the browser hijacker removal instructions provided at the end of the article. EverydayMemo.com is the main URL address that provides a direct download for a browser hijacker which is called…