Raccoon Infostealer: Introduction
There is a new information stealer in town. Dubbed Raccoon, the malware is gaining popularity as it is being sold as a MaaS (malware-as-a-service). Raccoon has already infected thousands of victims worldwide.
According to researchers, the Raccoon malware has contaminated hundreds of devices throughout the globe in just a couple of months, and has obtained card data and e-mail credentials from victims. The malware is already one of the top 10 most-mentioned malware tools in the underground community.
The malware is not excessively sophisticated or innovative, yet its malware-as-a-service (MaaS) model gives cybercriminals a quick-and-easy method to make money by compromising sensitive user details.
The Raccoon infostealer was discovered by Cybereason researchers, who say that “this strain of malware first emerged as recently as 2019, and has already established a strong following among cybercriminals. Its popularity, even with a limited feature set, signals the continuation of a growing trend of the commoditization of malware as they follow a MaaS (Malware-as-a-Service) model and evolve their efforts.”

Threat Summary
| Name | Raccoon Infostealer |
| Type | Infostealer, Malware |
| Removal Time | Less than 15 minutes (full-system scan) |
| Removal Tool |
See If Your System Has Been Affected by malware
Download
Malware Removal Tool
|
Raccoon Infostealer Variants
April 2020 Variant
These versions featured a change in the initial infection mechanism. The first action will be to trigger an initial installation script retrieving the actual malware from a Google Cloud Services repository. This is an important step, as most of the firewalls and other security solutions will consider it a safe and legitimate activity and not raise attention.
The new releases of the Raccoon infostealer malware were delivered via a phishing email campaign:
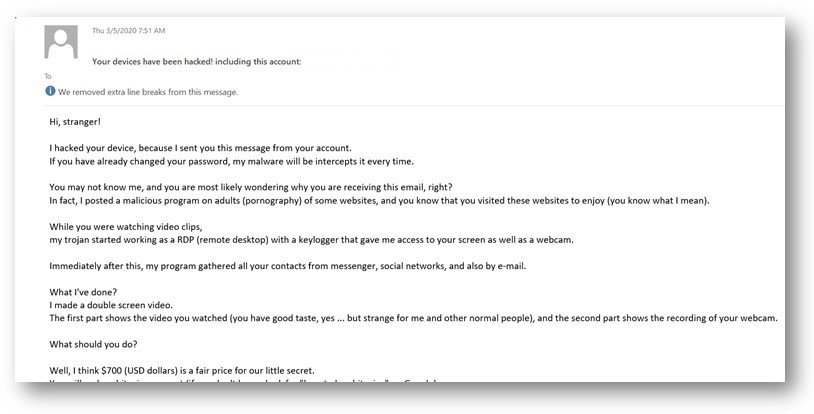
The recipients will be shown a message from a friend claiming that their inboxes have been compromised. Another typical scenario used to manipulate the intended victims is to send out warning messages claiming that their emails have been hacked. Various blackmail tactics will be used in order to manipulate the users into opening browser links or downloading attached files. Depending on the actual form of delivery the payload carrier may be a macro, an independent script, an executable file or another file type.
March 2020 Variant
The Raccoon malware was being spread in a sextortion phishing strategy. The criminals are sending email messages that contain nude images which include malicious scripts. The contents of these phishing emails also reveal that the criminal group behind it is called Red Skull. The premise of the emails is that the hackers have been able to compromise an acquaintance of the recipients and have found nude images of their naked girlfriends. They appear to be linked or attached directly to the email messages.
The malware was to be inserted in payload carrier files — the recipients will be instructed into enabling the built-in scripts — this is the case in macro-infected documents. They can be of all popular file types: presentations, databases, spreadsheets and text documents. The running of the macros will run a PowerShell initial infection script. This script will lead to the Raccoon malware installation.
Another extortion scam which is used by the criminals is the distribution of fake DocuSign documents. They are masked as legitimate files which when activated will download the malware.
Later Raccoon Versions
A dangerous feature found in some later versions of the malware is that it can also steal information from compromised devices which are using the TOR anonymous network. The information gathering module has been updated now to include software such as Mozilla Firefox, Google Chrome, Microsoft Edge and etc.
These versions could additionally steal credentials from any of the popular cryptocurrency wallets: Electrum, Ethereum, Jaxx, Exodus and Monero among others. This information stealing functionality is also extended to popular email clients such as Outlook, Foxmail and Mozilla Thunderbird. The attackers are probably using the Raccoon in order to acquire sensitive user data — the main goal is to intrude onto the target network. It is very possible that when this is done the virus may acquire administrative privileges.
The advanced functionality of the Raccoon allows it to execute a lot of malicious actions:
- Reconnaissance — The Trojan can take screenshots of the user activity and send them automatically to the hacker operators.
- Additional Infections — In many cases, these infections can be used to drop other malware to the hosts — ransomware, sabotage scripts, and etc.
- System Reconfiguration — Raccoon infections can be used to drastically reconfigure the system — changes can be made to the Windows Registry, configuration files, and etc.
Raccoon samples appear to be created as part of a global RaaS (ransomware-as-a-service) operation — this means that the original developers of the malware offer customization options to prospective buyers. There may be different price plans and options which can be ordered from the developers, as well as custom orders.
Raccoon Infostealer Malware — Technical Overview
First of all, it is important to note that Raccoon is written in C++ and is designed to work on both 32-bit and 64-bit operating systems. Though it was originally classified as a password stealer by many AV companies, the infosec community has observed it leverage broader capabilities. Thus, it has been categorized as an information stealer (infostealer).
The analysis of the inforstealer shows that it was developed by a Russian cybercrime group. The malware is capable of obtaining a large set of information, despite the lack of sophistication – it can infect victims using various techniques, and can steal plenty of sensitive information, such as credit card data, cryptocurrency wallets, browser data, and e-mail credentials.
The Raccoon malware is swiftly getting grip of new threat actors, eager to use it in their campaigns. It has already become one of the top 10 most-referenced malware pieces on underground marketplaces, infecting numerous endpoints internationally across both organizations and individuals in North America, Europe, and Asia.
Raccoon follows a malware-as-a-service model, allowing people a quick-and-easy way to make money by stealing sensitive data without a big financial investment or technical know-how.
It also appears that the cybercrime team behind Raccoon is admired in the underground community for their level of service, support, and user experience, but has faced a number of bouts of public feuds and inner conflicts, the official report says.
Raccoon Infostealer Distribution Methods
Exploit kits. The Raccoon infostealer is leveraging several ways for distribution across devices, but it mostly relies on exploit kits, phishing attacks, and bundled malware. Cybercriminals are specifically using the Fallout EK to generate a PowerShell instance from Internet Explorer and then download the main payload of the malware.
Phishing. The phishing campaigns carrying the inforstealer are based on email messages that have an attached Word document. When the potential victim opens the Word document and enables macros, the macro code creates a connection to a malicious domain to download the malicious payload.
Bundled malware. The attackers are also leveraging the bundling method, where Raccoon is bundled with legitimate software. If a user downloads an infected installer, the malware will install itself silently, and the user will not notice it.
Raccoon Infostealer – Removal
In order to fully remove the Raccoon infostealer from your computer system, we recommend that you follow the removal instructions underneath this article. If the first two manual removal steps do not seem to work, we suggest what most security experts advise – to download and run a scan of your computer with a reputable anti-malware program.
Downloading this software will not only save you some time, but will remove all of Raccoon malware files and programs related to it and will protect your computer against such intrusive apps and malware in the future.
Preparation before removing Raccoon Infostealer.
Before starting the actual removal process, we recommend that you do the following preparation steps.
- Make sure you have these instructions always open and in front of your eyes.
- Do a backup of all of your files, even if they could be damaged. You should back up your data with a cloud backup solution and insure your files against any type of loss, even from the most severe threats.
- Be patient as this could take a while.
- Scan for Malware
- Fix Registries
- Remove Virus Files
Step 1: Scan for Raccoon Infostealer with SpyHunter Anti-Malware Tool



Step 2: Clean any registries, created by Raccoon Infostealer on your computer.
The usually targeted registries of Windows machines are the following:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
You can access them by opening the Windows registry editor and deleting any values, created by Raccoon Infostealer there. This can happen by following the steps underneath:


 Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.Step 3: Find virus files created by Raccoon Infostealer on your PC.
1.For Windows 8, 8.1 and 10.
For Newer Windows Operating Systems
1: On your keyboard press + R and write explorer.exe in the Run text box and then click on the Ok button.

2: Click on your PC from the quick access bar. This is usually an icon with a monitor and its name is either “My Computer”, “My PC” or “This PC” or whatever you have named it.

3: Navigate to the search box in the top-right of your PC's screen and type “fileextension:” and after which type the file extension. If you are looking for malicious executables, an example may be "fileextension:exe". After doing that, leave a space and type the file name you believe the malware has created. Here is how it may appear if your file has been found:

N.B. We recommend to wait for the green loading bar in the navigation box to fill up in case the PC is looking for the file and hasn't found it yet.
2.For Windows XP, Vista, and 7.
For Older Windows Operating Systems
In older Windows OS's the conventional approach should be the effective one:
1: Click on the Start Menu icon (usually on your bottom-left) and then choose the Search preference.

2: After the search window appears, choose More Advanced Options from the search assistant box. Another way is by clicking on All Files and Folders.

3: After that type the name of the file you are looking for and click on the Search button. This might take some time after which results will appear. If you have found the malicious file, you may copy or open its location by right-clicking on it.
Now you should be able to discover any file on Windows as long as it is on your hard drive and is not concealed via special software.
Raccoon Infostealer FAQ
What Does Raccoon Infostealer Trojan Do?
The Raccoon Infostealer Trojan is a malicious computer program designed to disrupt, damage, or gain unauthorized access to a computer system. It can be used to steal sensitive data, gain control over a system, or launch other malicious activities.
Can Trojans Steal Passwords?
Yes, Trojans, like Raccoon Infostealer, can steal passwords. These malicious programs are designed to gain access to a user's computer, spy on victims and steal sensitive information such as banking details and passwords.
Can Raccoon Infostealer Trojan Hide Itself?
Yes, it can. A Trojan can use various techniques to mask itself, including rootkits, encryption, and obfuscation, to hide from security scanners and evade detection.
Can a Trojan be Removed by Factory Reset?
Yes, a Trojan can be removed by factory resetting your device. This is because it will restore the device to its original state, eliminating any malicious software that may have been installed. Bear in mind that there are more sophisticated Trojans that leave backdoors and reinfect even after a factory reset.
Can Raccoon Infostealer Trojan Infect WiFi?
Yes, it is possible for a Trojan to infect WiFi networks. When a user connects to the infected network, the Trojan can spread to other connected devices and can access sensitive information on the network.
Can Trojans Be Deleted?
Yes, Trojans can be deleted. This is typically done by running a powerful anti-virus or anti-malware program that is designed to detect and remove malicious files. In some cases, manual deletion of the Trojan may also be necessary.
Can Trojans Steal Files?
Yes, Trojans can steal files if they are installed on a computer. This is done by allowing the malware author or user to gain access to the computer and then steal the files stored on it.
Which Anti-Malware Can Remove Trojans?
Anti-malware programs such as SpyHunter are capable of scanning for and removing Trojans from your computer. It is important to keep your anti-malware up to date and regularly scan your system for any malicious software.
Can Trojans Infect USB?
Yes, Trojans can infect USB devices. USB Trojans typically spread through malicious files downloaded from the internet or shared via email, allowing the hacker to gain access to a user's confidential data.
About the Raccoon Infostealer Research
The content we publish on SensorsTechForum.com, this Raccoon Infostealer how-to removal guide included, is the outcome of extensive research, hard work and our team’s devotion to help you remove the specific trojan problem.
How did we conduct the research on Raccoon Infostealer?
Please note that our research is based on an independent investigation. We are in contact with independent security researchers, thanks to which we receive daily updates on the latest malware definitions, including the various types of trojans (backdoor, downloader, infostealer, ransom, etc.)
Furthermore, the research behind the Raccoon Infostealer threat is backed with VirusTotal.
To better understand the threat posed by trojans, please refer to the following articles which provide knowledgeable details.


