iOS and macOS were long believed invincible but facts and statistics reveal another truth. According to a brand new research, there is a near 400% increase in cryptomining attacks against iPhones. This upsurge has been registered in the last two weeks of September, when attacks against the Safari browser also increased significantly, Check Point said. The attacks were delivering the infamous Coinhive malware.
Most Popular Malware for September 2018
Cryptomining Attacks Against Apple Devices on the Rise
According to Check Point’s findings, cryptomining continues to be a prevalent threat for global organizations. It should also be noted that the attacks on Apple devices haven’t adopted any new functionalities, despite the sudden surge. Researchers have not concluded why this is happening, and point out that the security of mobile devices is often disregarded in organizations. In order to prevent them from being the weak point in corporate security, mobile devices should be protected efficiently via threat prevention solutions, the report notes.
The Coinhive malware, in particular, is now affecting 19% of global organizations. Another piece of malicious software that has been widely deployed in attacks is the Dorkbot Trojan, which the report puts in second place in terms of global impact after Coinhive.
[wplinkpreview url=”https://sensorstechforum.com/dorkbot-malware-2012-resurfaces-becomes-major-threat/”]Dorkbot is in fact a 6-year-old banking malware that has resurfaced in the wild to become a major threat, security reports recently revealed.The Dorkbot banking malware started its malicious activity back in 2012 but now it seems that the malware has started attacking financial institutions once again.
Dorkbot is designed to drop multiple files, in the %AppData% and %Temp% directories, and among those files are worm infection files, that allow it to automatically spread across different machines. Dorkbot may also heavily modify the Windows registry sub-keys, as Microsoft report. The malware primarily attacks the Run and RunOnce sub-keys, where it creates registry entries for all of its executable files to automatically run upon launching Windows.
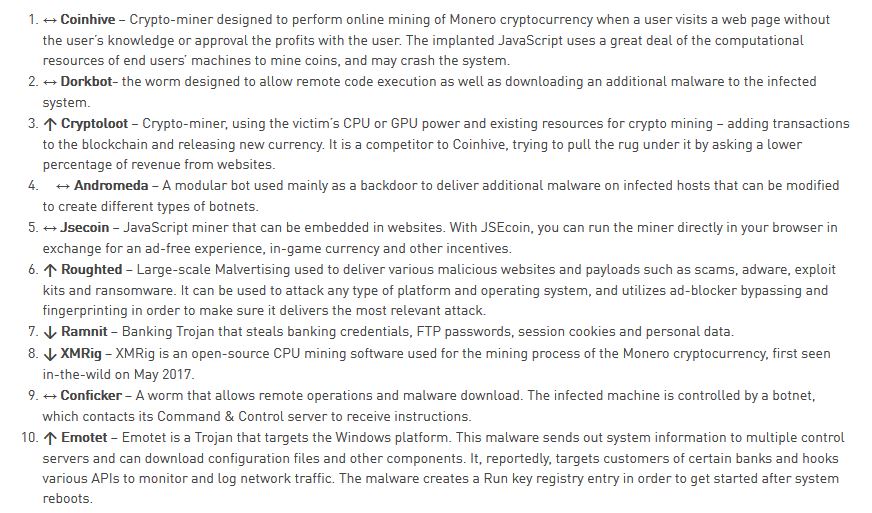
Other notable malware pieces that made in Check Point’s most recent malware analysis include [wplinkpreview url=”https://sensorstechforum.com/cryptoloot-coinhive-monero-miner-remove-pc/”]Cryptoloot, Andromeda, [wplinkpreview url=”https://sensorstechforum.com/millions-computers-infected-cryptocurrency-miners/”]Jsecoin, [wplinkpreview url=”https://sensorstechforum.com/roughted-malvertising-ad-blockers/”]Roughted, [wplinkpreview url=”https://sensorstechforum.com/german-nuclear-plant-hit-by-w32-ramnit-and-conficker-worms/”]Ramnit, [wplinkpreview url=”https://sensorstechforum.com/vmprotect-vmprotectss-exe-xmrig-monero-cpu-miner-remove/”]XMRig, Conficker, and [wplinkpreview url=”https://sensorstechforum.com/emotet-trojan-protection-guide/”]Emotet: