The Coronavirus has completely reshaped the way we use the Internet.
Remote work is on the rise, and historically, we’re processing more data than we have ever before. With this, hackers have fallen into great company. As we await defeating COVID-19, we will only create more data – influencing our growing concerns regarding backup, security, and privacy.
The best way to stay protected is to understand the history of backup and storage – dating back to its infancy. Let’s begin.
Where It All Began: Hardware & Software
Computer punch cards were the earliest form of digital data, developed in the 1900s. These cards were capable of storing up to 80-bits (10 bytes) of data. Today, most cellphones have the capacity to store 400 million – or more – of these computer punch cards into their internal drives.
In 1956, IBM created the first hard drive: RAMAC 305. A monumental development for its time, this magnetic disk drive measured over 16 feet tall, weighed over one ton, and stored 3.75 MB of data. Furthermore, this was the first storage device to allow random data access. This was game-changing since it eliminated the need to wait for drums or tape to progress to correct data points. After the release and success of IBM’s RAMAC 305, magnetic disk drives became the standard for data storage and backup by the 1960s.
In 1963, the world was introduced to Semiconductor Random Access Memory (RAM) for the very first time. The hardware was patented by Robert Norman & Fairchild Semiconductor; and over the next 5 years, RAM storage capacity grew by 32x. This boosted the hardware’s limits from 8 bits to 256 bits per chip.
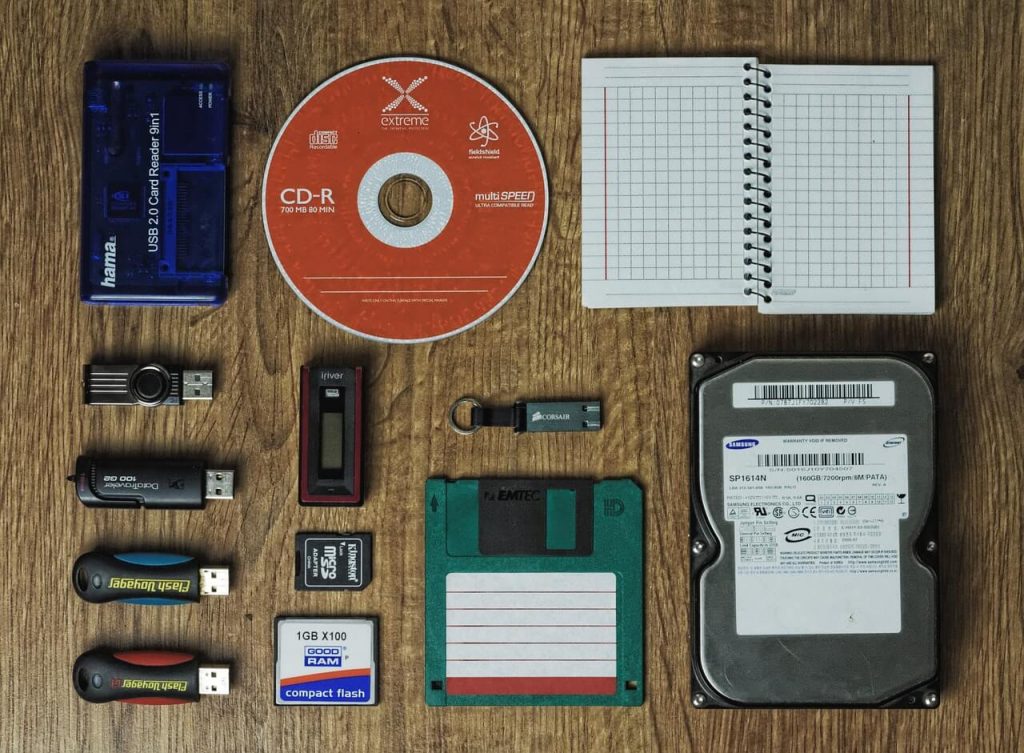
In 1967, IBM continued its success with its creation of the floppy disk. This allowed people to buy, load, and share data with one another – even before compact disks (CDs). By 1971, IBM was able to sell the world’s first 8-inch floppy disks, which went on to spark a new aftermarket in the software industry.
The Start of Computer Viruses
Named “Creeper,” the first computer virus was created in 1971. As is every other recipe for disaster, Creeper was only supposed to be used for experimentation. Although it was never used with any malicious intentions, it showed hackers how they can create viruses for evil. Thus and such, Creeper inspired a new era in security.
By 1978, technology began to replace paper in daily business operations. With this, many began to fear that power outages could have a huge impact on their businesses – causing them to lose data. As a solution, backup and disaster recovery solutions began flooding the software industry. In this year, the first backup hot site “Sungard Information Systems,” was invented, catering for this very concern.
Late 1980s: Desktop Backups Become a Thing
The ILLIAC-IV Supercomputer was the first computer to exclusively use semiconductor memory. Use of semiconductors allowed memory devices to shrink in size, all while operating at higher speeds. This paved the way for personal computers and sleeker desktops.
In 1981, IBM came back on the scene with a new product, a reseller challenger to expand the sales of the 5150 PC. Two years later in 1983, the Rivest-Shamir-Adleman Algorithm (RSA) was developed by MIT, which was the first patented cybersecurity technology in America. RSA used a type of public-key cryptography that formed the basis for data encryption, also enabling secure email and other online transactions.
In 1984, Apple II Computers fell into existence. These brought 5¼ inch floppy drives to consumers in a unique, never-seen-before style. The success of these devices went on for quite some time until new cybersecurity events called for a change in hardware.
The Rise of Cyber Threats
The Morris Worm (1988) and DR Popp Ransomeware (1989) shook things up toward the end of the 20th century. These both went on to influence the reshaping of the data backup markup.
The Morris Worm infected 1 in 10 computers connected to the Internet in its first 24-hours of release. Things went so far that many institutions completely wiped their systems, losing all of their data, in attempts to destroy the worm. Of course, data backup wasn’t widely available in 1988, so the cost of doing so was catastrophic. This malware sparked the creation of virus detection software, later inspiring a new generation of hackers.
DR Popp Ransomware was the first known form of ransomware, and was spread through infected floppy disks. Here’s how it worked: the floppy disk would remain dormant for 90 power cycles, then the malware would lock the infected computer and demand payment for a “software lease.” This cost the victim up to $378.
The Database Wars:
As malware rose, consumers, businesses, and educational leaders were losing some to all of their data. As a result, software and hardware companies began releasing database services.
In 1989, Network-Attached Storage (NAS) was a dedicated file-level storage server that used ethernet connections. This was created by Auspex, and just four years later, NetApp went on to make backup easier and more affordable.
In 1998, Brocade invented Storage Area Networks (SAN) to allow its users to connect devices and share files across servers and operating systems. Together, NAS and SAN made distance irrelevant to networked storage.
In 1998, IBM and Cisco teamed up to create the Internet Small Computer Systems Interface (iSCSI). This technology allowed access to stored data over an Internet connection, and made block storage cheaper and easier than it was through SAN.
The 21st Century: Data Backup Solutions
As technology became more widely available, tech giants like Amazon, Google, and Microsoft began adding cloud service. In 2006, Amazon Web Services (AWS) became the first cloud storage on the market, which was designed for software developers with innovative “pay per use” pricing.
In this same year, Managed Service Providers (MSP) was also one of the first cloud storage platforms made available. The difference? MSPs provide remote tech systems, often by subscription. Tech pioneers among the likes of Erick Simpson, Karl Palachuk, Amy Luby, etc. proposed the managed services business model that is still used today.
In mid-2010, ransomware went international. As strains including Reveton, WannaCry, CryptoLocker, Petya, and SamSam earned millions from targets around the world, some specifically targeted backup processes, and tools.
The following year, HANA, software created by SAP, allowed real-time processing for high-volume data. HANA integrated with cloud-based databases and custom applications.
Today’s Security Concerns
As databases grow larger, security concerns prompted an explosion of data compliance regulations designed to protect consumer data and privacy. For example, in 2017, Generative Adversarial Network (GAN) created deep fakes. GAN created adult films by superimposing celebrities’ faces, and the same technology was used a few months later to create a fake video of Donald Trump giving a positive speech on how we can stop climate change in Belgium.
Although these instances are fake, these films were convincing enough to raise impactful concerns over how to determine data’s authenticity. This is why businesses are training employees in phishing prevention. In other words, employees are a business’ primary asset in avoiding cybersecurity attacks and phishing attempts.
The Future of Data Protection & Cybersecurity
As always, new technology will present new risks. For example, as artificial intelligence and machine learning increase the value of big data, more opportunities for data breaches will present themselves. Furthermore, 5G networks will rely on software updates to maintain security, and even a single unsecured IoT device can compromise an entire network.
By 2025, we will be storing 175 zettabytes of data across the globe. Mostly through cloud-based data centers, 41.6 billion IoT devices will generate nearly 80 zettabytes of data, and 1 in 5 wireless connections will use 5G.
As technology advances, integrated security will become even more essential. Technology like Acronis, invented in 2019, can help you integrate data protection and cybersecurity technologies to create cyber protection.
The infographic below can provide you with a visual of this information, on a more-indepth level.
About the Author: Demetrius Harrison
 Demetrius has been a tech-lover since 2013. Demetrius currently writes tech news for Robotics Business Review & 21stCenTech, and has also conducted hands-on ISEF research from 2013-2016. Recently, Demetrius found an interest in SEO tech and halfway through completing his undergraduate’s degree. In the meantime, he is the Jr. Promotions Specialist at NowSourcing, Inc- an premier, award-winning design agency. Connect with Demetrius @demeharrison on social sites. Follow him @demeharrison
Demetrius has been a tech-lover since 2013. Demetrius currently writes tech news for Robotics Business Review & 21stCenTech, and has also conducted hands-on ISEF research from 2013-2016. Recently, Demetrius found an interest in SEO tech and halfway through completing his undergraduate’s degree. In the meantime, he is the Jr. Promotions Specialist at NowSourcing, Inc- an premier, award-winning design agency. Connect with Demetrius @demeharrison on social sites. Follow him @demeharrison












