Since many of the users on our forum and on our complaint e-mails have reported to be victims of infections caused by .js files(JavaScript source code file format) we have decided to serve the need of knowledge our readers should have and educate them how to protect themselves from malicious execution of a JavaScript that may render their files equal to garbage and make them pay a hefty sum. Bear in mind, we will provide the best advices on our abilities, but even the best advise won’t protect you if you do not pay attention to what you are doing while browsing on a daily basis. Let us begin!
Since many of the users on our forum and on our complaint e-mails have reported to be victims of infections caused by .js files(JavaScript source code file format) we have decided to serve the need of knowledge our readers should have and educate them how to protect themselves from malicious execution of a JavaScript that may render their files equal to garbage and make them pay a hefty sum. Bear in mind, we will provide the best advices on our abilities, but even the best advise won’t protect you if you do not pay attention to what you are doing while browsing on a daily basis. Let us begin!

The E-mail
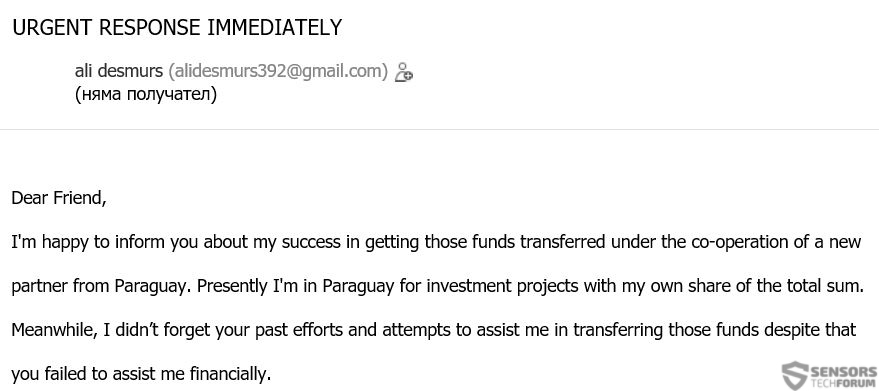
This segment is the most important piece of education you will ever receive if you are a beginner, because it will briefly teach you how to spot the difference between fake e-mail messages and actual e-mails. This is also due to the fact that the most often cause of infection by .js files viruses is via e-mail attachments. So when we are talking about .js files protection, we are also addressing spam e-mail protection as well.
The first step when receiving an e-mail and deciding whether or not to open a .js file in it is to have a system. Such system is very simple to memorize. If I could summarize it, I would definitely use this sentence:
The “top” is the subject of the e-mail that is sent to you and the source e-mail it is sent from. Here you can sort out the cheap e-mails which you can immediately delete even without having to open them. These are the so-called “promotion” and “important” e-mails that are not from organizations, but different individuals that you have never met before. Usually, people tend to write e-mail topics of something familiar to the user who they are sending the message to. Otherwise, why would have provided your e-mail address to specific people for contact, right?
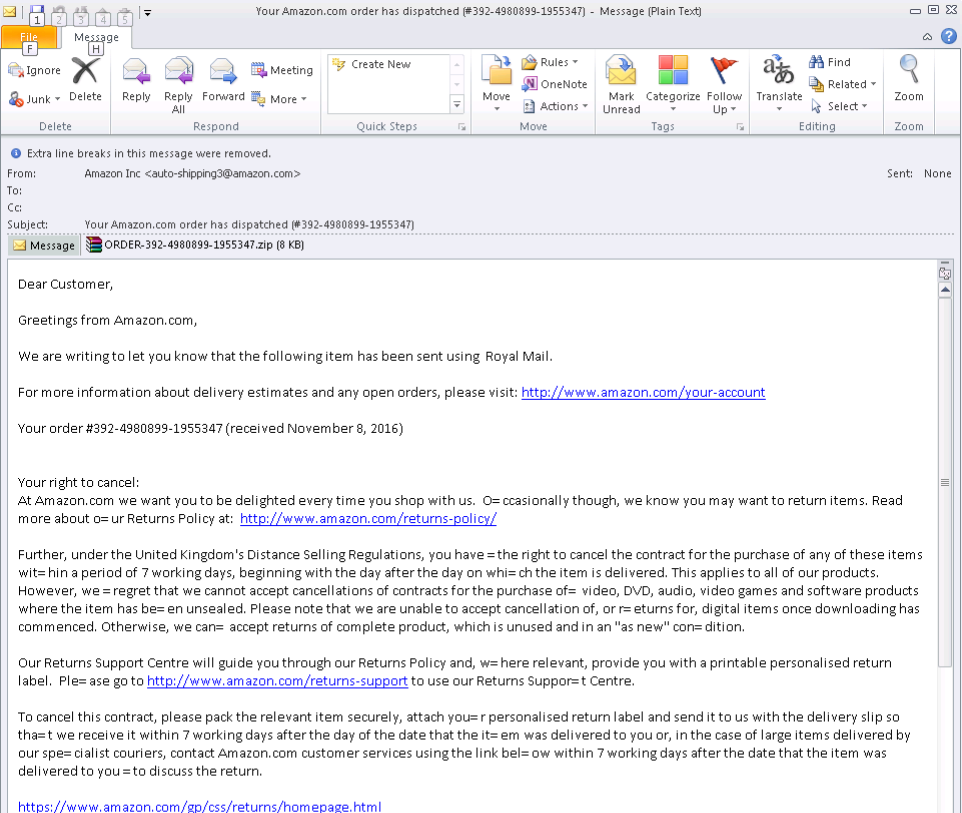
But then again, what if the message does not have a subject or what if it is sent by a company, like Amazon, for example (see the picture below). And what if the e-mail is saying that your PayPal account is suspended? The counter reaction to this in case you are not sure is to use a secure environment when opening the e-mail.Also, bear in mind of the obvious, and this is if a .js file is portrayed to you as a document in an e-mail, it may not be, because it is highly untypical for documents to be in JavaScript.
One solution is to use a sandbox application that “wraps” your web browser or e-mail client (Mozilla Thunderbird, Microsoft Outlook) in a secure encryption on which if the ransomware infection malware is activated, may immediately shut down because it will be stopped inside the program. One very good example for a sandbox application is a neat little app, called Sandboxie which we tested below. It even has the option to auto wrap every program you start in a sandbox automatically without affecting the performance of your computer even the slightest.
However, some sophisticated viruses and malware who run on .js to infect users may be coded and obfuscated with expensive obfuscators and exploit kits that may even go as far as through the sandbox application itself. Here is where you will need an advanced protection tool against these programs when you do your e-mailing – an advanced anti-malware tool is just the thing for you. Unlike traditional antivirus programs, most anti-malware programs are more frequently updated, and they are not just focused on .js malware, but on other suspicious files roaming around in spam e-mails carrying what may just be the lasts Locky or Cerber viruses.
There are a variety of anti-malware programs to choose from out there, and many would argue that the more well-known a security software is, the more it becomes a target for malware, because of the higher interest in it. This is why there should be a balance between a tool on which the hackers have little intelligence while at the same time is frequently maintained and updated. The best choice is a tool that will have a second-generation heuristic update system. This means that if the latest Locky hits in the U.S., the program on your computer should know about this and have the heuristics as fast as possible after this “zero patient” type of infection. One good example for such tool is Heimdal’s professional version, which we have kindly reviewed for you below and in case you do not seem to be fond of it it there are many other tools out there amongst which you can choose.

What If I Don’t Have the Time or Experience To Check Every E-mail?
In case the situation is that dire, or you are going to be educating someone who is systematically becoming infected via e-mail and via JavaScript and other types of files, do not worry. Explaining the situation to the inexperienced user may not be successful even if you repeat It over and over again. This is why we have a brilliant idea which can help protect your daily e-mailing if you are running a Windows OS and this is to use a virtual Android OS straight on your Windows device. Craftily, right?
The idea for this unexpectedly smart solution is that most spam e-mails are designed to trick Windows users into becoming infecting with malware. Surely, there is a lot of malware written for Android, but provided a little education and malware writers prefer malicious URLs via fake advertisements or suspicious apps to infect Android users, not e-mail. More to it than that, Android devices can also be additionally secured from .js files infection with an antivirus software and other utilities and app monitors, which is great. One app that is the leader and is very simple to use (install and start) is called Nox App Player, and after using it, we felt convinced in its stability as well as security

What about Malicious URLs?
Malicious URLs are a very sophisticated method of infection and very effective as well. This is why if the proper script is written to counter your defenses, neither of the tools above may save you. Here is where we talk about direct protection against any form of malicious JavaScript files. To secure your computer, this way, especially if you are using a browser instead of an e-mail client is to educate yourself in scanning URLs manually before opening. I know, it looks complicated at the start, but bear in mind that it can be significantly simplified with free browser add-ons, like VTzilla, VirusTotal.com’s web browser add-on. Need I remind you that VIrusTotal is most likely the one of the largest (if not, the largest) web database for malware and it not only uses the combination of a wide database of malicious .js files being detected 24/7 but it also learns to detect any URL’s and malicious JavaScripts before you even opened them. All it takes to right click on the URL before opening and scan it.

What If the Inevitable Happens?
If you are using any of those beginner tools, regularly updating your operating system, etc. and still manage to become infected somehow with a .js files attack, good data management is crucial to your survival from the devastation. Below, you may find more information on how to safely store your important files and protect them from .js files viruses.
Since a lot of malware including ransomware, now may not only slither other viruses on your computer if it becomes its victim, but it may also spread worms or make the computer a part of a botnet (bot network). This makes all of the other computers connected to the same network endangered, and they may not have such defensive tools. This is why, before all, your first deal of business is to disconnect the computer from the internet “the hardware way”. This will prevent any malicious packets to travel on your LAN and infect the other devices in it. From there, you can begin coping with the situation.
Preparation before removing .js Files.
Before starting the actual removal process, we recommend that you do the following preparation steps.
- Make sure you have these instructions always open and in front of your eyes.
- Do a backup of all of your files, even if they could be damaged. You should back up your data with a cloud backup solution and insure your files against any type of loss, even from the most severe threats.
- Be patient as this could take a while.
- Scan for Malware
- Fix Registries
- Remove Virus Files
Step 1: Scan for .js Files with SpyHunter Anti-Malware Tool



Step 2: Clean any registries, created by .js Files on your computer.
The usually targeted registries of Windows machines are the following:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
You can access them by opening the Windows registry editor and deleting any values, created by .js Files there. This can happen by following the steps underneath:


 Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.
Tip: To find a virus-created value, you can right-click on it and click "Modify" to see which file it is set to run. If this is the virus file location, remove the value.Step 3: Find virus files created by .js Files on your PC.
1.For Windows 8, 8.1 and 10.
For Newer Windows Operating Systems
1: On your keyboard press + R and write explorer.exe in the Run text box and then click on the Ok button.

2: Click on your PC from the quick access bar. This is usually an icon with a monitor and its name is either “My Computer”, “My PC” or “This PC” or whatever you have named it.

3: Navigate to the search box in the top-right of your PC's screen and type “fileextension:” and after which type the file extension. If you are looking for malicious executables, an example may be "fileextension:exe". After doing that, leave a space and type the file name you believe the malware has created. Here is how it may appear if your file has been found:

N.B. We recommend to wait for the green loading bar in the navigation box to fill up in case the PC is looking for the file and hasn't found it yet.
2.For Windows XP, Vista, and 7.
For Older Windows Operating Systems
In older Windows OS's the conventional approach should be the effective one:
1: Click on the Start Menu icon (usually on your bottom-left) and then choose the Search preference.

2: After the search window appears, choose More Advanced Options from the search assistant box. Another way is by clicking on All Files and Folders.

3: After that type the name of the file you are looking for and click on the Search button. This might take some time after which results will appear. If you have found the malicious file, you may copy or open its location by right-clicking on it.
Now you should be able to discover any file on Windows as long as it is on your hard drive and is not concealed via special software.
.js Files FAQ
What Does .js Files Trojan Do?
The .js Files Trojan is a malicious computer program designed to disrupt, damage, or gain unauthorized access to a computer system. It can be used to steal sensitive data, gain control over a system, or launch other malicious activities.
Can Trojans Steal Passwords?
Yes, Trojans, like .js Files, can steal passwords. These malicious programs are designed to gain access to a user's computer, spy on victims and steal sensitive information such as banking details and passwords.
Can .js Files Trojan Hide Itself?
Yes, it can. A Trojan can use various techniques to mask itself, including rootkits, encryption, and obfuscation, to hide from security scanners and evade detection.
Can a Trojan be Removed by Factory Reset?
Yes, a Trojan can be removed by factory resetting your device. This is because it will restore the device to its original state, eliminating any malicious software that may have been installed. Bear in mind that there are more sophisticated Trojans that leave backdoors and reinfect even after a factory reset.
Can .js Files Trojan Infect WiFi?
Yes, it is possible for a Trojan to infect WiFi networks. When a user connects to the infected network, the Trojan can spread to other connected devices and can access sensitive information on the network.
Can Trojans Be Deleted?
Yes, Trojans can be deleted. This is typically done by running a powerful anti-virus or anti-malware program that is designed to detect and remove malicious files. In some cases, manual deletion of the Trojan may also be necessary.
Can Trojans Steal Files?
Yes, Trojans can steal files if they are installed on a computer. This is done by allowing the malware author or user to gain access to the computer and then steal the files stored on it.
Which Anti-Malware Can Remove Trojans?
Anti-malware programs such as SpyHunter are capable of scanning for and removing Trojans from your computer. It is important to keep your anti-malware up to date and regularly scan your system for any malicious software.
Can Trojans Infect USB?
Yes, Trojans can infect USB devices. USB Trojans typically spread through malicious files downloaded from the internet or shared via email, allowing the hacker to gain access to a user's confidential data.
About the .js Files Research
The content we publish on SensorsTechForum.com, this .js Files how-to removal guide included, is the outcome of extensive research, hard work and our team’s devotion to help you remove the specific trojan problem.
How did we conduct the research on .js Files?
Please note that our research is based on an independent investigation. We are in contact with independent security researchers, thanks to which we receive daily updates on the latest malware definitions, including the various types of trojans (backdoor, downloader, infostealer, ransom, etc.)
Furthermore, the research behind the .js Files threat is backed with VirusTotal.
To better understand the threat posed by trojans, please refer to the following articles which provide knowledgeable details.